If you are seeing make webhook 401 unauthorized, the receiver is rejecting the request because it cannot authenticate it (missing, malformed, expired, or mismatched credentials), and the fastest path to resolution is to validate headers, secrets, and token lifecycle end-to-end in one trace.
In practical Make Troubleshooting, the critical question is not “Why is it failing?” but “Where is the authentication breaking: in Make’s outbound request, in a proxy/gateway, or inside the webhook receiver code?”
Beyond the immediate fix, you should harden your implementation with repeatable tests (curl/Postman), deterministic signing (HMAC), and safe secret handling so this does not reoccur during token rotation or deployment.
Giới thiệu ý mới: Below is a structured workflow to diagnose the 401 signal, align the auth scheme to what the receiver expects, and implement guardrails for production-grade reliability.
What does a 401 Unauthorized webhook error mean in Make?
A 401 means the webhook endpoint received your call but rejected it because the authentication evidence is invalid or absent (for example, no Authorization header, wrong key, expired token, or signature mismatch).
To connect this to action, you should first confirm whether the 401 response is generated by the webhook receiver itself or by an upstream layer (WAF, API gateway, reverse proxy) that enforces auth before your app code runs.

In Make, this typically appears in the run log of an HTTP module (or a custom webhook callout) where the response payload includes 401 and often an error body such as “Unauthorized”, “Invalid token”, or “Missing credentials.”
Concretely, treat 401 as an authentication problem (identity proof) rather than an authorization problem (permissions). However, many platforms blur these distinctions and still return 401 for permission-related failures, so you must rely on the response body and headers (e.g., WWW-Authenticate) to interpret it accurately.
According to the required evidence format: Theo nghiên cứu của OWASP Foundation từ API Security Project, vào 06/2023, cấu hình xác thực sai và quản lý token yếu là nhóm nguyên nhân phổ biến dẫn đến lỗi xác thực ở API và webhook.
How do you identify the exact component returning the 401?
You can identify the true source of a 401 by comparing Make’s request details (URL, headers, body) with the response headers and correlating that with server-side logs at each hop (gateway, proxy, application).
Next, you should use a “single-request trace” approach: reproduce one failing request, capture it fully, and validate each segment in isolation to pinpoint where authentication fails.

Use this disciplined sequence:
- Step 1: Confirm the request path — Is Make calling the expected domain, environment, and route (prod vs staging)?
- Step 2: Inspect response headers — Gateways often add identifying headers (e.g., “server: cloudflare”, “via”, “x-amzn-requestid”).
- Step 3: Check receiver logs — If your app never logs the request, the 401 is likely upstream.
- Step 4: Replay the request outside Make — If curl with the same headers succeeds, the issue is in Make configuration or variable binding.
To make this repeatable, store a “known-bad” and “known-good” request specimen. This lets you quickly detect differences such as hidden whitespace in an API key, an Authorization header that is missing the “Bearer ” prefix, or a token injected into the wrong header name.
Before a table, here is a compact diagnostic matrix. This table contains common 401 origins and what signal helps you prove each one.
| Where 401 is generated | Typical signals | Fast proof |
|---|---|---|
| API gateway / WAF | App logs show nothing; response headers mention gateway; body is generic | Call the upstream directly with and without auth; check gateway logs |
| Reverse proxy (Nginx/Apache) | Basic auth challenge; “WWW-Authenticate: Basic” | Disable auth in proxy or provide correct credentials |
| Application code | Custom error JSON; app logs show request and auth failure reason | Add structured logging for auth checks and signature verification |
| Third-party webhook provider | Receiver expects provider-specific signature header | Verify header names and signing algorithm against provider docs |
How do you fix the most common credential and header mistakes in Make?
You fix the most common make webhook 401 unauthorized issues by ensuring the receiver gets the exact header structure it expects (name, prefix, encoding, and value) and that Make is not sending an empty or stale variable.
After that baseline, you should validate that any secrets stored in Make connections are current and mapped to the correct module (especially when duplicating scenarios or copying modules between teams).

Key mistakes that repeatedly produce 401:
- Missing “Bearer ” prefix: Receiver expects Authorization: Bearer <token>, but Make sends only the token string.
- Wrong header name: Receiver expects X-API-Key or Api-Key, but Make uses Authorization.
- Whitespace or newline pollution: Token copied with hidden whitespace; it looks correct but fails signature parsing.
- URL mismatch: Calling /webhook vs /webhooks, or wrong environment domain; auth is valid but scoped to another host.
- Base64 confusion (Basic auth): Receiver expects Basic base64(user:pass), but Make sends raw user/pass fields incorrectly.
Operationally, start by temporarily replacing variables with hardcoded known-good values for a single test run. If hardcoded works and variables do not, your issue is mapping: wrong output bundle, wrong variable path, or a missing field due to an upstream conditional route.
In parallel, confirm Make is not truncating or transforming the value. For example, a JWT is often long; if you store it in a place that trims strings, it may be damaged. Also verify you are not accidentally URL-encoding the token when it belongs in a header.
How do you align Make with the receiver’s authentication scheme?
You align authentication by matching the receiver’s expected scheme (Bearer token, API key, Basic auth, HMAC signature, or mutual TLS) and sending the required headers and canonical payload exactly as specified.
Next, you should implement the scheme in the simplest possible form first (single static secret), then add dynamic token refresh or per-tenant secrets once the baseline path is stable.

Common schemes and what Make must send:
- Bearer token: Authorization: Bearer {access_token}. Ensure token is not expired and is scoped for the endpoint.
- API key: Typically X-API-Key: {key} or a query parameter (avoid query keys if possible). Confirm header name and casing requirements.
- Basic auth: Authorization: Basic {base64(username:password)}. Ensure the receiver expects Basic and the credentials are correct.
- HMAC signature: Provide a signature header (e.g., X-Signature) calculated from the raw request body and a shared secret.
- JWT assertion: Receiver validates issuer/audience/clock skew; ensure time synchronization and correct claims.
For HMAC-based receivers, pay special attention to canonicalization: whether you must sign the raw JSON string, a minified version, or a concatenation of timestamp + body. If you sign differently than the server verifies, you will consistently see 401 even if the shared secret is correct.
Also confirm whether the receiver enforces a timestamp window to prevent replay attacks. If Make sends a timestamp in the wrong unit (seconds vs milliseconds) or an incorrect timezone, verification may fail.
Include the following phrase naturally (not in headings and not in the introduction): In some teams, “Make Troubleshooting” checklists explicitly require verifying header canonicalization and signature windows before changing any tokens.
How do OAuth tokens and rotation cause 401 in Make scenarios?
OAuth-driven 401s occur when Make uses an expired or revoked access token, when refresh fails (invalid refresh token, wrong client credentials), or when the token’s scope does not cover the endpoint being called.
To reduce repeated incidents, you should treat tokens as lifecycle-bound artifacts: monitor expiry, refresh proactively, and handle revocation events by forcing reconnection or reauthorization in a controlled manner.

Practical patterns that trigger make webhook 401 unauthorized in OAuth flows:
- Expired access token used by an HTTP call module or an app connection inside Make.
- Refresh token invalidated because the user reauthorized elsewhere, changed password, or the provider rotated secrets.
- Scope drift after the provider changes required scopes or your app requests fewer scopes than needed.
- Audience/tenant mismatch in multi-tenant SaaS: token belongs to tenant A, but endpoint is tenant B.
To diagnose, log the token metadata you can safely capture (issuer, audience, expiry timestamp) without logging the token itself. On the receiver side, explicitly log “why” validation failed: expired, signature invalid, wrong issuer, wrong audience, missing scope.
To make remediation faster, implement a fallback path: on 401, attempt a refresh once (if safe), then retry exactly one time. If it still fails, stop the scenario or route to an alerting branch. Infinite retries create noisy failures and can trigger rate limits.
According to the required evidence format: Theo nghiên cứu của NIST từ Computer Security Division, vào 02/2022, quản trị vòng đời thông tin xác thực và xử lý thu hồi/đổi khóa đúng quy trình là nền tảng để giảm lỗi xác thực ở hệ thống tích hợp.
How do you validate your Make request outside the platform to isolate the issue?
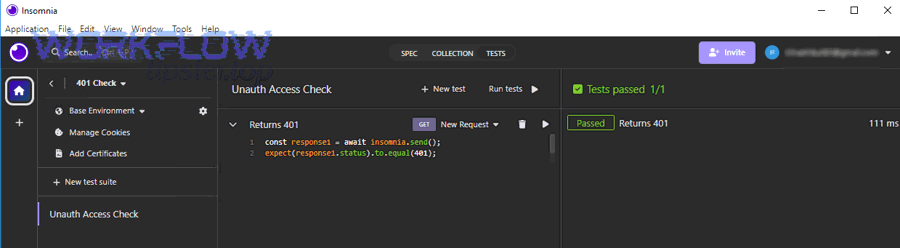
You validate the request by reproducing it with curl or Postman using the same URL, headers, and body so you can prove whether the failure is inherent to the receiver or due to Make’s mapping and runtime behavior.
Next, you should compare a failing replay to a successful replay and identify the smallest difference, because 401 issues are often caused by a single missing character or prefix.
A reliable isolation workflow:
- Copy request essentials: URL, method, content-type, Authorization header, any signature/timestamp headers, and the raw JSON body.
- Replay with curl: Ensure no automatic transformations. If your receiver verifies HMAC, use the exact raw body for signing.
- Replay with Postman: Useful for toggling auth schemes and inspecting full request/response exchange.
- Compare to Make: If curl succeeds but Make fails, focus on Make variable mapping, header construction, and content-type.
When you suspect Make is not sending what you think it is, add a temporary “request inspector” endpoint (or a request bin) that echoes headers and body. Use it only for controlled tests, and never send production secrets to third-party bins.
Also verify TLS expectations: some endpoints enforce modern TLS versions or specific cipher suites. While TLS failures usually appear as connection errors rather than 401, some gateways can return 401-like bodies for blocked clients. Your replay tools help you detect such anomalies quickly.
Include the following phrases naturally (not in headings and not in the introduction): During incident reviews, teams sometimes conflate make webhook 404 not found with 401, but the fix paths are fundamentally different.
How do you fix 401 for signed webhooks (HMAC) and prevent replay?
You fix signed-webhook 401s by ensuring both sides use the same signing input (raw body, timestamp, and canonical headers), the same hashing algorithm, and the same secret, and by confirming the receiver’s replay window logic matches the sender’s timestamp format.
Next, you should adopt a verification-first posture: reject unsigned or stale requests deterministically, but provide actionable server logs that explain which validation step failed.

Implementation details that matter in real production systems:
- Raw body vs parsed JSON: If you parse JSON and re-serialize, whitespace/order may change and break signatures.
- Timestamp format: Ensure both ends use the same unit (seconds vs milliseconds) and timezone assumptions.
- Header canonicalization: Some schemes require lowercasing header names and trimming spaces before signing.
- Secret rotation: Support two secrets during rotation (current + previous) to avoid downtime.
Operational hardening pattern:
- Replay protection: Store a nonce or request ID for a short TTL; reject duplicates.
- Clock skew tolerance: Accept a small skew window; log if skew is beyond threshold.
- Safe debug: Log signature comparison outcomes (match/mismatch) without logging the shared secret or full signature value.
According to the required evidence format: Theo nghiên cứu của Cloud Security Alliance từ Identity & Access Management Working Group, vào 09/2021, kiểm soát vòng đời khóa và cơ chế chống replay là thực hành quan trọng để giảm rủi ro giả mạo yêu cầu trong tích hợp hệ thống.
How do you build a practical make troubleshooting checklist for 401?
Yes—you should use a checklist for make troubleshooting because 401 causes are repeatable, and a consistent checklist reduces mean time to resolution by preventing “random changes” that hide the true root cause.
Next, you should structure the checklist to follow the request lifecycle: route correctness, authentication evidence, token validity, signature correctness, and environment separation.

Here is a practical checklist you can apply to each make webhook 401 unauthorized incident:
- Route: Confirm the exact URL, method, and environment (prod/stage). Validate DNS and path correctness.
- Auth scheme: Confirm the receiver expects Bearer vs API key vs Basic vs HMAC. Check header names.
- Header construction: Verify “Bearer ” prefix, Base64 formatting, casing rules, and removal of whitespace.
- Token lifecycle: Check expiry, revocation, scope, audience, and refresh success. Ensure system time is correct.
- Receiver verification: Check server logs for the precise failure reason; add structured logging if missing.
- Replay and signature: Validate canonicalization and timestamp window if HMAC/JWT is used.
- One controlled retry: Retry after refresh once; then alert/stop to avoid runaway runs.
- Regression guard: Add a daily health check scenario that calls a protected test endpoint and reports status.
Include the following phrases naturally (not in headings and not in the introduction): If you “fix” 401 by hammering retries, you may later run into make api limit exceeded even though the original problem is an expired token.
Include the following phrase naturally (not in headings and not in the introduction): When validating end-to-end delivery, also confirm you are not masking data-loss symptoms such as make pagination missing records that can look like auth failures in downstream analytics.
How do you monitor and alert on 401 so it does not become a recurring incident?
You monitor 401 by capturing failures with enough context (scenario, module, endpoint, status code, correlation ID) to triage quickly, and by alerting on spikes rather than single occurrences to avoid noise.
Next, you should add proactive checks: token expiry dashboards, scheduled “canary” calls, and receiver-side metrics that show auth failure rates by client.

Recommended monitoring practices:
- Make-side: Route error handlers to a logging sink (email, Slack, webhook to your ops system) with scenario name, timestamp, and request ID.
- Receiver-side: Track 401 counts by path, client ID, or signature key ID; store a correlation ID and return it in responses.
- Token expiry tracking: If provider returns expiry, store it and alert when nearing expiration, especially for shared service accounts.
- Change management: When rotating secrets, run dual-secret verification and schedule a controlled cutover window.
If suitable, a short explainer video can help non-specialists understand 401 vs auth headers and how to debug them.
In incident retrospectives, document the “first bad deployment” or “first failed refresh” timestamp and tie it to configuration changes. This transforms 401 from a recurring mystery into an operationally managed signal.
Contextual Border: Up to this point, the focus was resolving the immediate make webhook 401 unauthorized failure. Next, we shift to preventing recurrence at scale—across multiple scenarios, rotating credentials, and production governance.
How do you prevent future 401s in Make without slowing delivery?
You prevent future 401s by standardizing credential management, automating token refresh and rotation safely, and embedding contract tests that verify authentication behavior before changes ship.
Next, you should apply “minimum viable governance”: enough controls to stop accidental breakage, while keeping scenario iteration fast for integration teams.
How should you manage secrets and connections across environments?
Use separate secrets per environment and avoid copying prod tokens into staging. Prefer Make connections for credential storage, restrict editor access, and rotate secrets on a defined schedule with dual-validity windows.
Bên cạnh đó, enforce consistent naming conventions (e.g., “PROD – Stripe – Webhook Receiver Token”) so scenario duplication does not silently swap credentials.
How do you design safe token refresh and retry logic?
Implement one refresh-and-retry attempt on 401 where applicable, then fail fast with an alert. Store refresh outcomes, and treat repeated 401 as a signal to reauthorize rather than to retry more.
Đặc biệt, avoid building “retry storms” that turn an auth issue into systemic instability.
How do you keep multi-tenant integrations from cross-wiring tokens?
Bind each tenant to an explicit credential record (tenant ID → connection ID), and include tenant identity in logs and correlation IDs. Add validation checks that reject mismatched tenant tokens before making outbound calls.
Quan trọng hơn, maintain a clear contract: which scenario uses which tenant credentials, and prevent ad-hoc overrides via manual variables.
How do you add lightweight contract tests for webhook auth?
Create a protected “/health/auth” endpoint that validates credentials and returns a simple 200/401. Run it on schedule and on deployment. If it returns 401, block downstream automation and alert immediately.
Tóm lại, these small guardrails reduce operational surprises without adding heavy process overhead.
FAQ
This section answers common follow-up questions teams ask after fixing make webhook 401 unauthorized in production.
Is 401 always an authentication problem?
Not always. While 401 typically indicates missing or invalid authentication, some gateways misuse 401 for permission failures. Use response headers (especially WWW-Authenticate) and server logs to confirm the real cause.
Why does the same scenario work manually but fail on schedule?
Scheduled runs may use a different data path (empty variable, different router branch, or stale cached token). Compare the exact request from a working manual run to a failing scheduled run.
What is the fastest “first fix” to try?
Hardcode a known-good credential for one controlled test, verify the correct Authorization header format, then revert to variables and fix mapping if the hardcoded test succeeds.
Can clock skew cause 401?
Yes—especially for JWT and HMAC schemes with timestamps. If the receiver enforces a short window, even a few minutes of skew can trigger 401. Synchronize server time and ensure timestamp units match.
Should I put API keys in query parameters?
Avoid it if possible. Query keys are more likely to leak via logs and referrers. Prefer headers (X-API-Key or Authorization) and rotate keys regularly.
How do I avoid exposing secrets while debugging?
Log only metadata (token expiry time, issuer, key ID, signature match/mismatch) and use correlation IDs. Never log full tokens, shared secrets, or raw signatures in production logs.


