If you see make oauth token expired in Make, it means the connection credential that authorizes your scenario to call an external app is no longer valid, so the module can’t authenticate and the run fails until you refresh or re-authorize.
In practical Make Troubleshooting, the fastest path is to confirm whether the failure is a true token expiration (time-based) or a token invalidation (revoked/rotated permissions), because each requires a different recovery action inside the connection.
Beyond the immediate fix, you also want to prevent repeat outages by designing around token lifecycles: refresh-token availability, scoped permissions, shared connections, and alerting when re-authorization is needed before your automations go dark.
Giới thiệu ý mới: below is a step-by-step, root-cause-first guide that moves from definition to diagnosis to durable prevention, so you can restore scenarios quickly and keep them stable at scale.
What does “make oauth token expired” mean in Make connections?
It means Make attempted to use an OAuth access token that is no longer accepted by the target service, so the API call is rejected and the module stops until the connection is refreshed or re-authorized.
Tiếp theo, it helps to map the message to what OAuth actually does inside Make. In most Make integrations, a connection stores OAuth credentials (typically an access token and—if the provider supports it—a refresh token). Make attaches the access token to API requests. When that token is expired, the provider returns an authentication failure (often HTTP 401 or 403), and Make surfaces it as an “OAuth token expired” class of error.
Cụ thể, there are two common interpretations that look similar in logs but differ operationally:
- Expired (time-based): the access token’s lifetime ended. If a refresh token exists and is still valid, Make can often refresh automatically or you can trigger a manual reconnect.
- Invalidated (event-based): the provider revoked the token, the user changed password, an admin removed the app, consent was withdrawn, scopes changed, or the provider rotated secrets. Refresh may fail, forcing a full re-authorization.
Để minh họa, imagine your scenario calling a CRM module every 5 minutes. If the provider issues 60-minute access tokens, Make will eventually need to refresh. If refresh is blocked (no refresh token, offline access not granted, or the refresh token was revoked), the scenario fails with a token error until you re-consent.
The key operational point is that “expired” is not always “wait and retry.” Most providers require a new token issuance flow; retries without re-auth will keep failing and may create noise, delays, or downstream backlogs.
Why do OAuth tokens expire or get revoked in Make scenarios?
They expire because access tokens are designed to be short-lived, and they get revoked when the user, admin, or provider invalidates authorization for security or policy reasons.
Sau đây is a grouped view of root causes that directly affect Make reliability. Treat each group like a checklist so you can diagnose without guessing.

Group 1: Normal expiry and refresh behavior
Access tokens typically have a limited lifetime, so your scenario will eventually need a refresh; if refresh is available and configured correctly, the outage risk is low.
Cụ thể hơn, providers issue short-lived tokens to reduce blast radius if credentials leak. If your Make connection includes a refresh token, Make can request a new access token when the old one expires. If no refresh token exists, you are effectively running on “single-use authorization,” which is fragile for long-running automations.
Group 2: Consent and permission changes
Tokens often fail after scope changes, consent withdrawal, or app access changes, because the provider no longer recognizes the authorization grant behind the token.
Để bắt đầu, check whether anyone changed the app’s permission scopes, reconfigured the OAuth client, switched from “testing” to “production,” or modified domain/redirect rules. Any of these can invalidate existing grants and cause Make to throw token expiry-like errors even if time-based expiry is not the trigger.
Group 3: Security events and account hygiene
Password resets, MFA enforcement, suspicious-login flags, or admin security policies can revoke tokens and refresh tokens, forcing re-authorization.
Ngoài ra, some providers automatically revoke refresh tokens when a user changes password or when a session is deemed risky. In those cases, Make cannot recover automatically; you must reconnect the account inside Make.
Group 4: Provider-side policy limits
Providers can limit the number of active refresh tokens per user/app or expire refresh tokens after inactivity, which turns a stable scenario into a periodic “needs reconnection” workflow.
Quan trọng hơn, if your team repeatedly “creates new connections” instead of reusing one, you can hit token issuance limits or silently invalidate older refresh tokens. That pattern frequently appears in multi-scenario Make workspaces.
To keep the flow practical, the next section converts these causes into a fast recovery playbook you can follow during an incident.
How do you fix an expired OAuth token in Make in under 10 minutes?
Use a three-step method: confirm it’s authentication, refresh/reconnect the connection, then validate with a controlled test run before re-enabling normal scheduling.
Để hiểu rõ hơn, your goal is to restore authorization with the least disruptive action, while avoiding duplicate writes or partial processing.

Step 1: Confirm the error is truly OAuth authentication
Check the failed module’s response: a token problem will typically surface as unauthorized/forbidden, invalid token, or an authentication-required message rather than a data validation error.
Cụ thể, isolate the first module that touches the provider. If the first call fails with an auth error, the connection is suspect. If auth succeeds but a later module fails, you may be dealing with permissions on a specific endpoint or object.
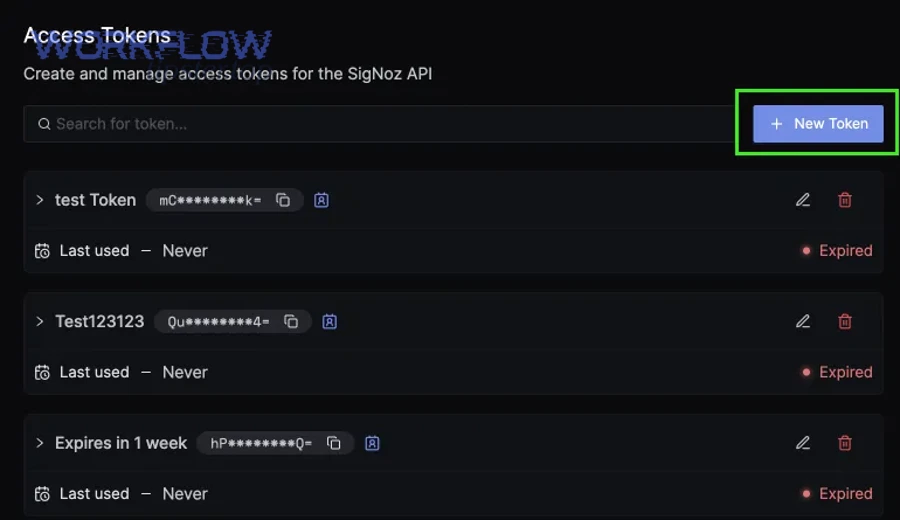
Step 2: Refresh or re-authorize the Make connection
If refresh is available, reconnecting the existing connection is the fastest fix; if refresh is not available or fails, remove and re-add authorization for that connection.
Dưới đây is a practical sequence that usually minimizes side effects:
- Open the scenario run log and identify the connection name used by the failing module.
- Open the connection settings for that app and attempt a Reconnect (or equivalent re-auth action).
- If reconnect fails, create a new connection using the same account, then rebind the module(s) to the new connection.
- If the provider is multi-tenant (teams, workspaces, organizations), confirm you are authorizing the correct tenant.
Ví dụ, if a shared Gmail/Drive connection was authorized by a user who left the company, the token may be revoked. Re-authorize with a service account or a stable admin identity where policy allows it.
Step 3: Validate safely to prevent duplicates
Run a controlled test (single cycle) and verify outputs before turning the schedule back on, especially for “create/update” actions.
Tiếp theo, use these safeguards during validation:
- Idempotency check: confirm the target system won’t create duplicates if the previous run partially succeeded.
- Small replay window: re-run with minimal input data (one record) to confirm authorization and mapping.
- Commit awareness: for multi-step writes, ensure earlier steps didn’t already commit changes before the token failure.
To avoid re-learning this during the next outage, the next section shows how to diagnose faster using a structured make troubleshooting lens.
How does make troubleshooting isolate whether the failure is in Make, the app, or your network?
It isolates by testing authentication boundaries: first confirm the provider is reachable, then confirm the connection can obtain or refresh tokens, and finally confirm the specific API scope/endpoint is permitted.
Để bắt đầu, treat your scenario like a layered system. Token errors sit at the boundary between Make and the provider, but symptoms can be amplified by timeouts, retries, and partial runs.

Layer 1: Provider availability vs credential validity
If the provider is down or rate-limiting, you may see intermittent authentication-like errors; a quick check is whether other tools (or the provider’s status page) show outages at the same time.
Trong khi đó, if every run fails consistently for the same connection across scenarios, credential validity is the leading hypothesis.
Layer 2: Refresh-token pathway health
If Make cannot refresh tokens, you’ll see failures start at the moment the access token expires and continue until a user re-authorizes.
Cụ thể hơn, look for a pattern: runs succeed for hours/days, then suddenly all fail with auth until someone reconnects. That pattern indicates a refresh token problem, missing offline access, or a revoked refresh grant.
Layer 3: Endpoint scope and tenant alignment
If only certain modules fail (but others in the same scenario succeed), you may have insufficient scopes or you are authorized to the wrong tenant/workspace.
Để minh họa, you might have access to “read contacts” but not “write deals” in a CRM. The provider can respond with permission errors that Make may surface near “token expired” messages. Confirm that the consent screen includes the needed scopes and that you are using the correct org/workspace within the provider.
Layer 4: Scenario design signals
If token errors appear after long delays, your design might be triggering extended processing windows that collide with token lifetimes or provider session constraints.
Hơn nữa, heavy scenarios with many sequential API calls can hit rate limits and receive defensive responses that look like auth failures. In that case, adding backoff, batching, and checkpoints reduces the probability that a token refresh is requested under stress.
Once you can isolate the layer, you can design prevention that targets the real failure mode rather than applying repeated reconnects as a ritual.
How can you prevent token expiry from breaking scenarios again?
You prevent it by designing for token lifecycles: stable account ownership, refresh-token continuity, proactive monitoring, and workflow patterns that minimize long, brittle runs.
Sau đây are prevention controls that map directly to the root causes you already identified.
Control 1: Use stable authorization identities
Authorize connections with accounts that won’t disappear, change roles frequently, or be subject to personal security resets that revoke tokens unexpectedly.
Cụ thể, prefer a dedicated integration user (or an admin-managed account) where provider terms allow it. If your organization uses SSO, coordinate with IT so policy changes do not silently invalidate refresh tokens.
Control 2: Minimize “connection sprawl”
Reusing a small number of well-governed connections reduces refresh token churn and makes reconnection events predictable.
Ngoài ra, document which scenarios use which connections. When token issues arise, you can re-authorize once and restore multiple scenarios, rather than hunting across a workspace.
Control 3: Add alerting before business impact
Detect and notify on authentication failures immediately, so you re-authorize before downstream queues, missed SLAs, or data drift accumulate.
Để bắt đầu, route errors to email/chat and include the connection name, scenario name, first failing module, and timestamp. That transforms an “unknown outage” into a one-click reconnection task.
Control 4: Make scenarios idempotent and restartable
When you must reconnect and replay, idempotent design prevents duplicates and enables safe retries.
Ví dụ, store last-processed IDs, use provider-side upserts, or check for existing records before creating new ones. This is especially important when an expired token occurs mid-run after some actions have already succeeded.
Tóm lại, prevention is not just about tokens; it is about building runs that can pause, resume, and prove correctness when authentication is restored.
How do refresh tokens, offline access, and consent settings affect Make reliability?
They determine whether Make can recover automatically: refresh tokens and offline access enable silent renewal, while restrictive consent settings force manual re-authorization and increase downtime risk.
Để hiểu rõ hơn, treat these as the “durability attributes” of your connection. Two scenarios can call the same API, yet one is resilient and the other is fragile because of how authorization was granted.

Refresh token present vs absent
If a refresh token exists and remains valid, Make can request new access tokens without human involvement; without it, every access-token expiry becomes an incident.
Cụ thể, some providers only issue refresh tokens under specific conditions (first-time consent, offline access, specific grant types, or when prompt/consent parameters force a refresh token). If you authorized years ago under different policies, you may be missing a refresh token even though the connection appears normal.
Offline access and “long-lived authorization”
Offline access (or its equivalent) signals that the app should maintain access when the user is not actively present, which is essential for scheduled Make scenarios.
Trong khi đó, some providers treat scheduled automation as higher risk and require stronger consent or admin approval. If offline access was not granted, refresh token issuance may be blocked, leading to recurring “token expired” failures.
Consent screen configuration and scope hygiene
Broader scopes can increase approval friction and revocation risk, while too-narrow scopes can break specific modules and produce confusing auth-like errors.
Quan trọng hơn, keep scopes minimal but sufficient. When you must expand scopes, expect existing grants to require re-consent. Plan that change like a deployment: schedule it, notify stakeholders, and validate after re-authorization.
Như vậy, Make reliability improves when you deliberately choose authorization settings that support unattended operation and controlled change.
What are the most common “false positives” that look like token expiry?
They are errors that surface as authentication failures but are actually caused by permissions, tenant mismatch, clock skew, or provider-side defenses like rate limiting.
Tiếp theo, use this grouping to avoid burning time on reconnect loops when the token is not the real problem.

Permission denied on a specific object or endpoint
If only certain actions fail, your token may be valid but not authorized for that endpoint or resource type.
Cụ thể, check user role changes in the provider and whether the connection’s consent includes the needed scopes. A role downgrade can break write actions while read actions still succeed, mimicking “token expired” from the perspective of a single module.
Wrong workspace, organization, or tenant
Authorization can be valid but pointing to the wrong tenant, causing access checks to fail even though the token itself is fine.
Để minh họa, a user might have access to multiple workspaces and accidentally authorizes the connection against a personal workspace rather than the company workspace that holds the data.
Rate limiting and anti-abuse defenses
Under heavy load, providers may respond with defensive auth-like failures, especially when requests are bursty or come from unusual IP patterns.
Ngoài ra, long chains of API calls can trigger throttling that looks like intermittent authentication errors. In that case, improving batching and pacing often “fixes” the issue without changing tokens.
Time synchronization and clock-related validation
Some token validations depend on accurate time; if your system or provider has time drift, tokens can appear “not yet valid” or “already expired.”
Quan trọng hơn, when you see sudden token failures across multiple services at the same time, consider environment-level time drift or proxy/CDN behavior before rebuilding every connection.
Tổng kết lại, false positives are best handled by checking scope/tenant/load signals first, then reconnecting only when you confirm the credential path is broken.
When should you rotate credentials, rebuild the connection, or contact the app vendor?
You should rebuild or escalate when reconnect attempts fail consistently, refresh is revoked, or provider policy changes block unattended authorization; rotating credentials is appropriate when security or compliance requires revocation and re-issuance.
Để bắt đầu, decide based on which action reduces risk and time-to-recovery, not which action feels familiar.

Rebuild the connection when the refresh grant is broken
If reconnect fails or immediately re-fails, the refresh token may be revoked or the OAuth client configuration may have changed, so a full re-authorization is the correct move.
Cụ thể, rebuild is also appropriate after major consent/scope changes, provider migrations, or changes from “testing” to “production” OAuth configuration that invalidate prior grants.
Rotate credentials when you suspect compromise or policy mandates
If a token leak is possible or your organization requires periodic credential rotation, revoke existing grants and re-authorize with updated scopes and controls.
Ngoài ra, rotation should be planned: identify all scenarios that use the connection, switch them to the new connection in a controlled window, and validate outputs to avoid silent data gaps.
Contact the vendor when failures are provider-side or undocumented
If tokens expire unusually quickly, refresh tokens vanish, or the provider returns inconsistent errors across identical calls, vendor support can confirm policy limits or outages.
Để minh họa, some providers impose limits on how many refresh tokens an app can hold per user, or they enforce inactivity expiration on refresh tokens. When those constraints are not visible in Make, vendor confirmation prevents repeated trial-and-error changes.
Như vậy, the “right” escalation step is the one that aligns with the underlying invalidation mechanism, not simply the error label.
At this point, you have the core incident playbook. Bên cạnh đó, the next section focuses on edge cases that commonly affect production automations: shared connections, partial replays, and run-behavior pitfalls that amplify authentication incidents.
Edge Cases and FAQ for OAuth expiry in Make
This section covers uncommon but high-impact scenarios where token failures cascade: shared connections, replay safety, and performance patterns that make token refresh more fragile.

Can you auto-reconnect without user interaction?
Sometimes yes, but only if the provider issues a durable refresh token and allows offline access; otherwise, Make cannot legally or technically re-consent on behalf of a user.
Cụ thể, many providers require an interactive login when refresh tokens are revoked, when scopes expand, or when an admin demands re-approval. If your operations depend on unattended reconnect, choose providers and authorization models that support it, and avoid user accounts that trigger frequent security resets.
What if multiple scenarios share one connection?
Shared connections are efficient, but a single token invalidation can take down many scenarios at once, so you must pair sharing with monitoring and ownership controls.
Tiếp theo, document the blast radius: list which scenarios use the shared connection, and define who is responsible for re-authorization. In incident response, fix the shared connection first, then validate each scenario’s output behavior to ensure no silent partial failures remain.
How do you avoid partial replays and missing data after reconnect?
You avoid them by storing checkpoints (last processed IDs/timestamps), using idempotent writes, and replaying only the minimal safe window after authentication is restored.
Dưới đây is a table that helps you choose a replay strategy based on where the token expired; it reduces duplicates and closes gaps.
This table contains replay decisions by failure point so you can restart safely without guessing which steps already committed changes.
|
Failure point |
Risk |
Recommended replay approach |
|---|---|---|
|
Before first read/search module |
Low duplication risk |
Reconnect, re-run normally, verify first batch |
|
Mid-run after some creates/updates |
High duplication risk |
Replay minimal window, use upsert/idempotency keys, verify targets |
|
After writing but before logging/confirmation |
Hidden success risk |
Audit target system first, then replay only missing confirmations |
In advanced operations, teams often describe these symptoms as make pagination missing records after an auth incident because the replay window is too small or the cursor state isn’t persisted across reconnects. The fix is not “more retries,” but deterministic checkpoints and cursor-safe paging.
How do you reduce token failures caused by long processing windows?
You reduce them by shortening critical paths, batching requests, adding backoff, and avoiding long uninterrupted runs that stress provider limits and make refresh operations more likely to fail under load.
Quan trọng hơn, if your workspace repeatedly experiences slow, high-latency execution, the pattern is often discussed as make timeouts and slow runs in operations reviews. The mitigation is architectural: split scenarios, queue work, and move heavy transforms to dedicated compute so that OAuth refresh happens in a stable, predictable window.
FAQ (quick answers)
-
Will reconnecting delete my scenario data? No, it changes authorization for API calls; your scenario configuration remains, but you must validate outputs to prevent duplicates.
-
Should I create a new connection every time? Not by default; reuse stable connections unless you need rotation, scope changes, or the refresh grant is irreparably broken.
-
Why does it work manually but fail on schedule? Scheduled runs depend on unattended authorization; missing offline access or revoked refresh tokens can make manual tests succeed while scheduled runs fail later.
-
What’s the fastest “first move” during an incident? Identify the failing connection name, reconnect it once, then run a single controlled test to confirm recovery before restarting full schedules.

