If you want contracts to move faster without losing control, the most reliable path is to automate a single “source-of-truth” workflow where Airtable drives the process, DocSend manages controlled sharing, Box governs storage, and DocuSign executes signatures end-to-end.
Next, you’ll learn what this workflow actually is in practice, what must exist before you build it, and how to choose an integration approach that won’t collapse the moment your team scales from 10 envelopes a week to 200.
Then, you’ll design a stable Airtable schema for signing, map your data into recipients and fields, and build a repeatable flow that creates an envelope, tracks its status, and writes everything back to Airtable in a way Ops & RevOps can trust.
Introduce a new idea: once the core system works, you’ll harden it—handling permissions, failures, audit trails, retention, and the “DocSend vs DocuSign” boundary so your signing pipeline stays fast, compliant, and predictable.
What is an Airtable → DocSend → Box → DocuSign eSignature workflow?
An Airtable → DocSend → Box → DocuSign eSignature workflow is an automated contract execution pipeline where Airtable triggers document preparation, DocSend controls secure sharing, Box stores governed files, and DocuSign collects signatures while syncing status back to Airtable.
Specifically, the point of this workflow is not “using four tools,” but creating one continuous chain that prevents the usual breakpoints: missing signer emails, outdated attachments, duplicate envelopes, and lost final PDFs.
In a mature setup, Airtable holds the deal context (who, what, when, and what’s approved), DocSend handles controlled access when you want a review step or engagement signals, Box holds your authoritative file structure and retention rules, and DocuSign acts as the execution engine with timestamps and completion artifacts.
When those roles are clear, you stop arguing about which copy is “the real one.” You always know:
- Which record launched the signing
- Which file version was signed
- Which envelope is active
- Where the executed PDF is stored
- Which status should trigger the next operational step (billing, provisioning, onboarding)
What does “automation” mean in this workflow (and what steps stay manual)?
Automation in this workflow means the system creates, routes, tracks, and stores signing actions automatically once a human confirms readiness—while manual steps remain where humans add value: approvals, exceptions, and non-standard negotiations.
More specifically, you should treat automation as a guarded conveyor belt, not a runaway robot. The workflow can automatically:
- Validate required Airtable fields
- Generate or select the correct document version
- Place the file into the right Box folder
- Create and send a DocuSign envelope
- Record envelope ID + status into Airtable
- Retrieve the signed copy and file it correctly
But you often keep these manual (or semi-automated) on purpose:
- Final deal approval (especially when terms vary)
- Legal review gates (high-value or regulated deals)
- Non-standard signer logic (substitutions, delegates, external counsel)
- Exceptions (missing data, bounced emails, redlines still open)
The practical model is “human approves the start; automation runs the middle; humans intervene only on exceptions.”
Is this workflow the right fit for Ops & RevOps teams?
Yes—this workflow is a strong fit for Ops & RevOps teams because it (1) reduces signing cycle time, (2) makes pipeline execution measurable, and (3) standardizes storage and auditability across every agreement.
Then, to confirm you’re the right audience, check the three most common “yes” indicators:
- You handle repeatable agreements (MSAs, order forms, renewals, NDAs, onboarding packs)
- You track stages in a system (deal stage, provisioning stage, onboarding stage)
- You need reliable execution artifacts (final PDFs, timestamps, audit trails, and retention)
If your team sends a few one-off contracts a month, the setup might feel heavy. But if you’re consistently pushing volume through a pipeline, this is exactly the kind of operational leverage Ops & RevOps are built to create.
What are the core components you need before building the automation?
There are 6 core components you need before building the automation: (1) a stable Airtable data model, (2) document templates and version rules, (3) signer roles and routing logic, (4) a Box folder taxonomy, (5) permissions and authentication, and (6) an integration method to connect everything reliably.
Next, once you see these components as “requirements,” you’ll stop treating failed envelopes as mysterious bugs and start treating them as predictable gaps.
Here’s why each component matters:
- Airtable data model
Airtable is your control plane. If the record can’t describe “who signs what,” automation has nothing to execute. - Templates + version rules
If templates are inconsistent, you’ll send the wrong terms or lose field alignment. Your workflow must decide: which template, which clauses, which version. - Signer roles + routing logic
Signing is not “send to email.” It’s a role system: signer, approver, CC, internal witness, counter-signer, conditional recipient. - Box folder taxonomy
Without an agreed folder structure and naming convention, you’ll store executed agreements in random places and break retrieval later. - Permissions + authentication
Signing workflows are access-control problems. If an integration account can’t read a folder, envelopes fail. If a reviewer can’t access a link, deals stall. - Integration method
You must pick the right “glue”: native connectors, a no-code automation layer, or a custom API flow.
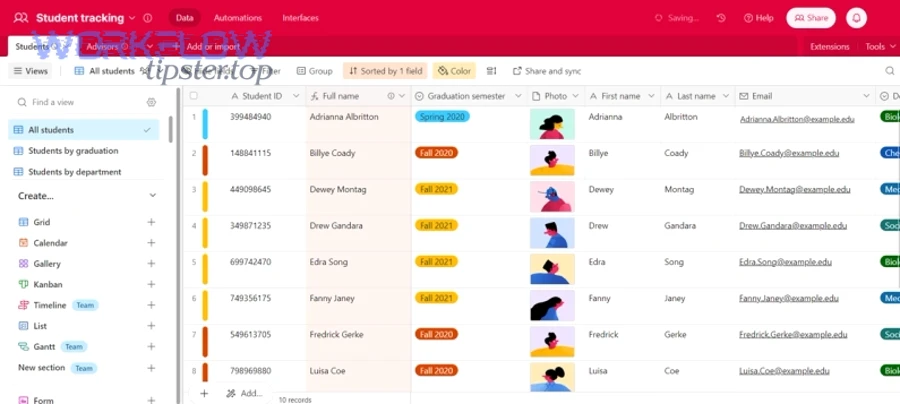
What data should Airtable store to generate and route documents correctly?
Airtable should store the minimum signing dataset: document identity, signer identity, routing logic, and execution tracking—because those four groups prevent 80% of operational failures.
Then, to make it actionable, group your fields like this:
A) Document identity fields
- Document type (MSA, order form, NDA, renewal)
- Template/version (v1.2, 2026 terms, region-specific)
- Document location link (Box file URL or file ID)
- DocSend link/package ID (if used for pre-sign review)
B) Signer identity fields
- Primary signer name + email
- Counter-signer name + email (your side)
- Signer role (client signer, legal, finance, executive)
- Signer constraints (needs SMS verification, must sign last)
C) Routing logic fields
- Routing order (sequential vs parallel)
- Conditional routing flags (if deal size > X, add approver)
- Internal approval status (approved / blocked / needs review)
D) Execution tracking fields
- Envelope ID (DocuSign)
- Envelope status (created/sent/viewed/completed/voided/failed)
- Sent timestamp, completed timestamp
- Executed PDF link (Box final file link)
- Error log field (last failure + reason)
If you store these consistently, you can automate confidently and debug fast when something breaks.
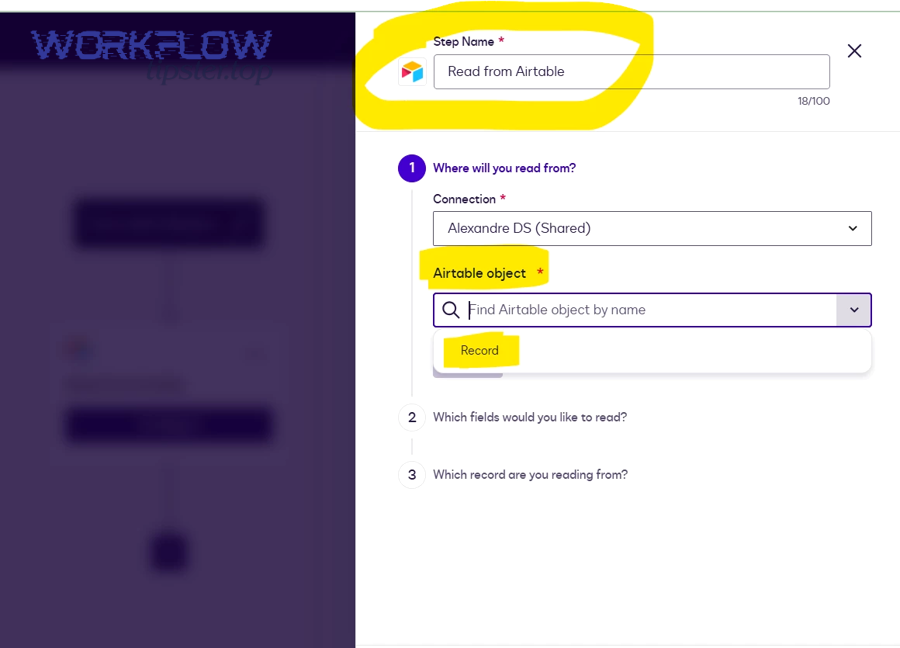
Which integration approach should you use (native, Zapier/Make, or custom API)?
Native connectors win for speed, Zapier/Make win for flexibility at moderate complexity, and a custom API wins for control and scale—so the best approach depends on volume, compliance needs, and how many exceptions you must support.
Next, use this practical comparison to decide:
| Approach | Best for | Strength | Weak point |
|---|---|---|---|
| Native connectors | Simple workflows | Fast setup, fewer moving parts | Limited logic + edge cases |
| Zapier/Make (no-code) | Ops-led automation | Great branching, easier iteration | Can get fragile at high volume |
| Custom API (engineering) | High scale + strict governance | Full control, better observability | Slower build, ongoing maintenance |
If Ops & RevOps are building and owning the workflow, no-code is often the sweet spot—until compliance, volume, or complex routing forces an API build.
How do you design the Airtable base schema to support document signing automation?
You design the Airtable base schema with 3 structural layers—(1) canonical records, (2) signing transactions, and (3) audit + exceptions—so your automation can run repeatedly without corrupting data or losing traceability.
Then, the key is to stop storing “signing” as a single checkbox and store it as a lifecycle with history.
A durable schema usually includes these tables:
- Deals / Requests (canonical table)
One row = one business context (deal, onboarding, vendor contract request). - Contacts / Signers
Signer info is reusable and should not be duplicated across deals. - Documents
One deal can have multiple documents (MSA + order form + DPA). Store document versions and canonical file links here. - Envelopes / Signing Transactions
This is the engine table. One envelope per signing event, with statuses and timestamps. - Approvals / Exceptions (optional but powerful)
A small table that captures manual gates and error handling.
To make this schema concrete, here’s a field map you can copy. This table contains the minimum field set needed to trigger signing, track completion, and file the executed PDF without losing context.
| Table | Field | Purpose |
|---|---|---|
| Deals | Deal ID / Request ID | Primary key for everything |
| Deals | Status stage | Controls “ready to send” gating |
| Documents | Template/version | Prevents wrong terms |
| Documents | Box file link / ID | Authoritative file pointer |
| Envelopes | Envelope ID | Required to fetch status + final PDF |
| Envelopes | Envelope status | Drives downstream automations |
| Envelopes | Completed timestamp | Proof + SLA tracking |
| Envelopes | Executed PDF link (Box) | Retrieval + compliance |
| Envelopes | Error message | Debugging + retry logic |
What are the best-practice status stages for tracking signing from start to finish?
There are 8 best-practice status stages for tracking signing from start to finish: Draft, Ready for Review, Approved, Sent for Signature, Viewed, Completed, Archived, and Failed/Needs Fix—based on whether the document is prepared, authorized, executed, and safely stored.
Next, the reason this matters is simple: status stages are your automation guardrails. If you collapse everything into “sent/not sent,” you create duplicate sends, missing files, and unclear ownership.
A strong stage design also lets Ops & RevOps measure cycle time:
- Approval SLA (Ready for Review → Approved)
- Signing SLA (Sent → Completed)
- Filing SLA (Completed → Archived)
And it makes exception handling explicit:
- Failed/Needs Fix means your workflow stops and requires a fix before retrying.
Should you use a button-driven trigger or an event-driven trigger in Airtable?
Yes, you should usually start with a button-driven trigger because it (1) prevents accidental sends, (2) forces a final human readiness check, and (3) creates a clean audit moment—then shift to event-driven triggers only when your data quality and governance are consistently strong.
Then, the transition from button-driven to event-driven should be earned, not assumed.
Button-driven trigger (recommended default)
- Best when you need control
- Best when approvals are real
- Best when mistakes are costly
Event-driven trigger (advanced)
- Best when inputs are validated automatically
- Best when contracts are standardized and low-risk
- Best when you need high throughput
A practical compromise is a hybrid:
- Event-driven validation + preparation
- Button-driven “Send for signature”
That gives you speed without risking uncontrolled execution.
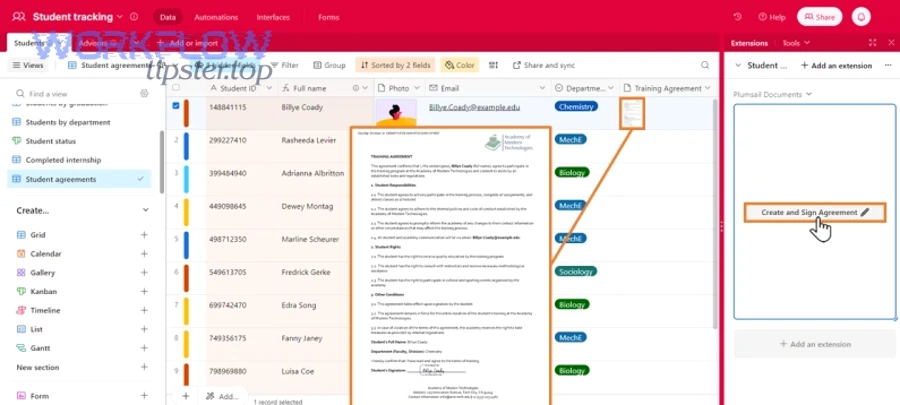
How do you build the automation flow from Airtable to DocuSign (with DocSend and Box in the middle)?
You build the automation flow using a 7-step chain—validate → prepare → share → store → send → sync → archive—so Airtable triggers DocSend sharing when needed, Box stores the authoritative file, and DocuSign executes signatures while writing every state change back to Airtable.
Next, the only way to keep this chain stable is to define “source of truth” at each step: Airtable for status, Box for files, DocuSign for signing events, and DocSend for controlled review signals.
Here’s the practical flow (Ops-friendly and automation-ready):
Step 1: Validate the Airtable record
Before anything is sent, confirm required fields exist:
- signer emails present
- correct template/version selected
- Box folder exists (or can be created)
- approvals complete (if required)
Step 2: Prepare the document
Preparation can mean:
- selecting an approved PDF from Box
- generating a document from a template (outside scope here)
- ensuring the file name and version are correct
Step 3: (Optional) Create a DocSend share for review
This step is useful when you want a controlled pre-sign review:
- internal stakeholders review before signature
- you want engagement signals (viewed/not viewed)
- you want a single controlled link
Step 4: Place the document in the correct Box folder
This is where your file governance becomes real:
- deal folder
- contract type folder
- “Draft” vs “Executed” subfolders
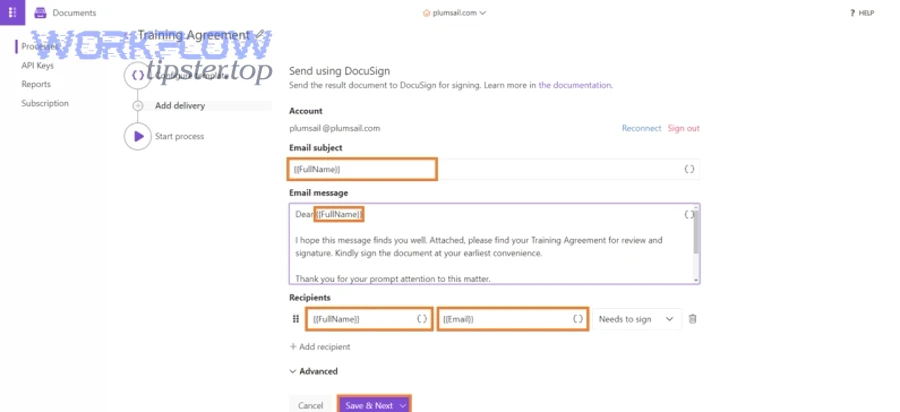
Step 5: Create and send the DocuSign envelope
The envelope should include:
- the correct document (from Box link or attachment)
- the recipients in correct order
- tabs/fields aligned to roles
- custom fields for tracking (deal ID, doc type)
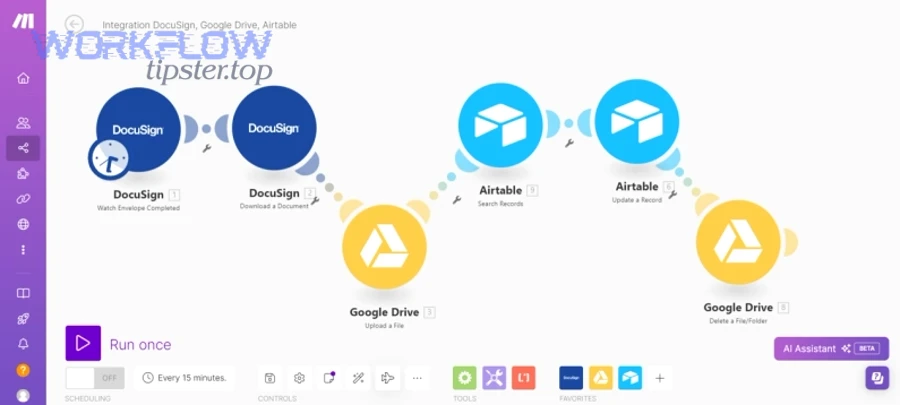
Step 6: Sync envelope ID + status back to Airtable
Write back immediately:
- envelope ID
- sent timestamp
- current status
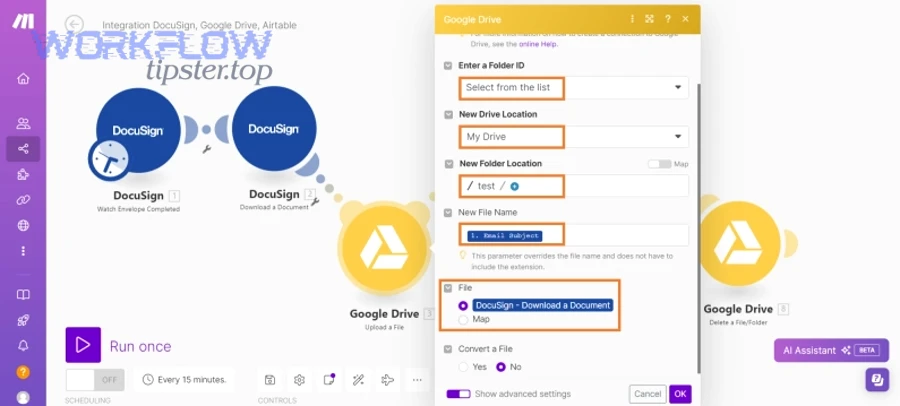
Step 7: On completion, archive the executed copy to Box and update Airtable
Store the executed PDF and update:
- completed timestamp
- executed file link (Box)
- final status (Completed → Archived)
A real-world note: this same flow pattern is how many teams scale other chains too, like google forms to hubspot to google sheets to slack lead capture—validate inputs, route to system-of-record, notify, and store outcome—so the logic is transferable even when the tools change.
How do you package and share the document in DocSend without breaking the signing process?
You package and share the document in DocSend safely by using DocSend for controlled review and visibility while keeping DocuSign as the single signing surface, because splitting signing across tools creates version confusion and execution disputes.
Then, to keep it clean, choose one of these two patterns:
Pattern A: DocSend for review → DocuSign for signature (recommended)
- DocSend link is used to review a “ready” draft
- Once approved, the workflow sends the final signing version through DocuSign
- Airtable stores both the DocSend link (review) and the DocuSign envelope ID (execution)
Pattern B: DocSend eSignature for lightweight use cases
- Use only when your signing complexity is minimal
- Use only when template/routing needs are simple
- Avoid when you need advanced routing, strict controls, or deep template systems
DocSend’s own documentation emphasizes that signable documents produce a certificate/audit history capturing signing events and related metadata. (help.dropbox.com)
That’s valuable—but the key is to decide whether that audit depth is sufficient for your contract category.
How do you store, name, and route files in Box so signed copies are always retrievable?
You store, name, and route files in Box reliably by applying 3 rules: (1) one deal folder structure, (2) one naming convention tied to Airtable IDs, and (3) a strict separation between drafts and executed copies.
Next, if you want retrieval to be instant (not a scavenger hunt), file structure must be designed for the future you—months after the deal closes.
A practical Box folder pattern:
- /Accounts/{AccountName}/Deals/{DealID}/
- /Draft/
- /For-Signature/
- /Executed/
- /Supporting/
File naming convention (examples):
- {DealID}_MSA_v1.2_FOR-SIGNATURE.pdf
- {DealID}_OrderForm_{YYYY-MM-DD}_FOR-SIGNATURE.pdf
- {DealID}_MSA_EXECUTED_{YYYY-MM-DD}.pdf
Routing rule:
- Only one file is eligible for signing at a time (“FOR-SIGNATURE”)
- Only executed files enter “Executed”
- Airtable must store the Box link to the executed copy, not just the folder
Box’s integration guidance explicitly describes sending documents stored in Box for signature and saving them back to Box for secure storage and sharing. (support.box.com)
How do you set up DocuSign envelopes so signatures are accurate and status syncs back to Airtable?
You set up DocuSign envelopes accurately by using templates and role-based mapping so Airtable fields populate recipients and tabs consistently, while the envelope ID and status events write back to Airtable for tracking, SLAs, and downstream automation.
Then, the operational truth is this: most envelope errors come from messy mapping (wrong recipient, wrong routing order, wrong document version), not from DocuSign itself.
Your envelope design should cover four layers:
- Recipients and routing
- signer vs approver vs CC
- sequential vs parallel routing
- conditional routing (if needed)
- Document alignment
- correct version
- fields anchored to the right places
- no missing tabs for required signatures
- Tracking fields
- envelope custom fields: deal ID, document type, requester, renewal flag
- Sync strategy
- write envelope ID to Airtable immediately
- update status on key events (sent, delivered/viewed, completed, voided)
If you’re new to templates, this short walkthrough can help clarify how template-driven envelopes reduce errors:
What is the difference between DocuSign templates and ad-hoc envelopes for this workflow?
DocuSign templates win in consistency and scale, ad-hoc envelopes are best for flexibility, and a hybrid approach is optimal when you need standardized agreements with occasional exceptions.
Then, decide based on three criteria:
Criterion 1: Error rate
- Templates reduce “missing field” and “wrong tab” mistakes
- Ad-hoc sends rely on human memory and manual placement
Criterion 2: Speed
- Templates send faster because roles and tabs are pre-defined
- Ad-hoc sends slow down as complexity increases
Criterion 3: Governance
- Templates enforce approved language and structure
- Ad-hoc sends make it easier to drift into unofficial variants
For Ops & RevOps, templates are usually the foundation because they create repeatability, and repeatability is what automation needs.
How do you map Airtable fields to DocuSign recipients, roles, and tabs?
You map Airtable fields to DocuSign recipients, roles, and tabs by using a consistent “role dictionary” and validating required fields before envelope creation, so each envelope receives correct signer data and each signer sees only the fields they must complete.
Next, follow this mapping checklist (this prevents most execution failures):
A) Build a role dictionary (one-time setup)
- Client Signer (Role:
client_signer) - Internal Counter-Signer (Role:
company_signer) - Approver (Role:
internal_approver) - CC (Role:
cc)
B) Map Airtable → DocuSign recipients
- Airtable
Client signer email→ DocuSignclient_signer.email - Airtable
Client signer name→ DocuSignclient_signer.name - Airtable
Counter signer email→ DocuSigncompany_signer.email - Airtable
Routing order→ DocuSign recipient order
C) Map Airtable → DocuSign tabs
- Airtable
Effective date→ DocuSign Date Signed tab (or custom date tab) - Airtable
Legal entity name→ Text tab (read-only, if needed) - Airtable
Amount/term→ Text tabs (if included)
D) Validate before sending
- If signer email is missing: stop and mark record “Failed/Needs Fix”
- If the document version is not approved: stop
- If Box file link is missing: stop
Finally, once you create the envelope, write back:
- Envelope ID
- Status = Sent for Signature
- Sent timestamp
That write-back is what makes the workflow trackable and operationally useful.
How do you monitor, troubleshoot, and harden the workflow to prevent failed sends or missing documents?
You monitor, troubleshoot, and harden the workflow by adding validation, logging, retries, permission checks, and a clear exception path—because reliability comes from catching failures early, recording why they happened, and preventing duplicate or partial execution.
Then, treat your workflow like an operational system, not a one-time integration: every automated step should either succeed cleanly or fail loudly with a reason.
To harden the chain, build these safeguards:
1) Pre-flight validation (before any send)
- required fields present
- approvals complete
- document version locked
- Box folder reachable
- signer emails valid format
2) Unique execution keys
- one envelope per deal per document version
- store a unique key in Airtable like
{DealID}-{DocType}-{Version} - block sends if a key already has an active envelope
3) Logging you can actually use
- record the last automation run time
- record the last step completed
- store error message and error code (if available)
- store link to run log (if your automation tool supports it)
4) Retry strategy
- retry only safe steps (fetch status, file copy)
- never retry “send envelope” automatically unless you guarantee idempotency
5) Post-completion verification
- confirm executed PDF stored in Box
- confirm Airtable has executed link
- confirm status moved to Archived
What are the most common failure points in Airtable → DocSend → Box → DocuSign automation workflows?
There are 6 common failure points in Airtable → DocSend → Box → DocuSign automation workflows: permissions/auth failures, missing required fields, wrong template/version, folder path mismatches, rate limits/timeouts, and webhook/event sync gaps.
Next, here’s how each failure typically shows up and how to fix it:
- Permissions/auth failures
- Symptom: cannot access Box file or cannot create envelope
- Fix: audit integration account access; apply least privilege but ensure required scopes
- Missing required fields
- Symptom: envelope created with wrong recipient or fails validation
- Fix: enforce required field rules in Airtable; block sends until complete
- Wrong template/version
- Symptom: signer sees wrong terms or fields don’t align
- Fix: lock template selection based on deal type; store template IDs, not names
- Folder path mismatches
- Symptom: executed file stored in wrong place or not stored at all
- Fix: create folder programmatically and store folder IDs; avoid free-text paths
- Rate limits/timeouts
- Symptom: intermittent failures at volume
- Fix: queue sends; add backoff; reduce unnecessary API calls
- Webhook/event sync gaps
- Symptom: DocuSign completed but Airtable still says “Sent”
- Fix: add periodic status reconciliation (“polling fallback”) and confirm event subscriptions
Can you make this workflow secure and compliant without slowing teams down?
Yes, you can make this workflow secure and compliant without slowing teams down because (1) role-based access reduces exposure, (2) retention rules automate compliance, and (3) audit trails provide defensible evidence—while automation removes manual handoffs that usually cause delays.
Then, instead of adding friction, you add guardrails:
- Least privilege integration accounts (only the folders and actions needed)
- Approval gates based on risk (deal size, non-standard clauses)
- Retention rules in Box (executed agreements retained appropriately)
- Audit trails from signing events (who signed, when, from where, and what changed)
A university example illustrates the scale impact: a University of Virginia case study reported that automation around eSignature processes saved 10,000 hours in 2022. (internet2.edu)
Evidence: According to a guide by The Ohio State University from the Office of Business and Finance and the Office of the Chief Information Officer, issued in 2015, electronic signatures can reduce processes from “days or weeks” to “minutes or hours” by removing travel delays and multi-signer paper handling. (busfin.osu.edu)
Contextual Border: You now have the full macro workflow—definition, prerequisites, schema design, end-to-end execution, envelope setup, and hardening. Next, we shift into micro decisions that expand semantic coverage: tool overlap, governance depth, audit tactics, and when not to automate.
What advanced considerations help you optimize (or safely limit) Airtable → DocSend → Box → DocuSign document signing?
There are 4 advanced considerations that help you optimize (or safely limit) this workflow: choosing the right signing engine boundary, tightening Box governance, strengthening audit/webhook integrity, and deciding where manual approvals should override full automation.
Next, these considerations are what separate a “working integration” from a trustworthy operational system.
To illustrate, many teams eventually manage multiple signing chains—sometimes even adjacent variants like airtable to docsend to box to pandadoc document signing—and the real skill is governing the pattern, not just wiring one instance.
How is DocSend eSignature different from DocuSign eSignature for contract execution?
DocSend eSignature is best for simpler, share-first signing experiences, while DocuSign eSignature is best for robust enterprise execution—because DocuSign generally supports deeper template systems, routing complexity, and organization-wide governance patterns.
Then, think of the difference like this:
- DocSend is often “share + track + sign”
- DocuSign is “execute + control + audit at scale”
DocSend highlights that signable documents produce a certificate/audit history capturing signing events and related metadata. (help.dropbox.com)
That’s powerful for speed, but for higher-risk agreements, many Ops & RevOps teams still prefer DocuSign as the execution backbone because the surrounding controls are designed for operational scale.
Which Box governance and retention settings matter most for signed agreements?
The Box governance and retention settings that matter most are retention policies, controlled sharing, version history, and metadata consistency—because those controls determine whether your executed agreements remain discoverable, defensible, and compliant over time.
Next, apply these practical governance moves:
- Retention rules: executed agreements retained per policy (by contract type if needed)
- Folder permission model: restrict “Executed” to the smallest set of editors
- Shared link discipline: avoid open links for executed agreements; prefer authenticated access
- Version history rules: keep the executed copy immutable; store redlines elsewhere
- Metadata standards: ensure Deal ID and document type are searchable
And remember the integration promise: Box’s own integration overview describes saving signed documents back to Box for secure storage and sharing. (support.box.com)
What webhook and audit-trail practices reduce disputes and “missing signature” incidents?
The webhook and audit-trail practices that reduce disputes most are event redundancy, immutable envelope IDs, and complete signer metadata capture—because disputes happen when you can’t prove who signed what, when, and from where.
Then, implement these micro-level practices:
1) Store immutable identifiers
- envelope ID
- document version ID
- executed file ID (not just link)
2) Capture key lifecycle timestamps
- sent, delivered/viewed, completed, voided
- store them in Airtable so Ops can run SLAs
3) Build an event redundancy strategy
- primary: webhook/event update
- fallback: scheduled reconciliation (polling)
This prevents “status stuck” situations when a webhook fails.
4) Preserve audit metadata
DocSend’s help content describes audit events that can include timestamped history and details such as IP address and user agent in the certificate history. (help.docsend.com)
That kind of metadata becomes your operational “receipt” when someone claims they never signed or the wrong person completed the action.
When should you choose a manual approval step instead of full automation?
You should choose a manual approval step instead of full automation when (1) the document is non-standard, (2) the risk is high (money, regulation, brand/legal exposure), or (3) the signer routing is unusual—because approvals prevent irreversible mistakes that automation can’t safely infer.
Then, use this simple decision rule:
Use full automation when
- templates are standardized
- pricing/terms are within defined bounds
- signer roles are predictable
Insert manual approval when
- redlines exist or clauses are custom
- deal size crosses a risk threshold
- jurisdiction or compliance requirements change the terms
- the signing path requires exceptions (alternate signer, delegated authority)
This is also where you keep operational consistency across your broader automation workflows portfolio—so the same governance logic can apply whether you’re orchestrating contract execution or chains like calendly to google calendar to google meet to trello scheduling where timing, ownership, and exceptions determine success.

