Title analysis (Step 1.1):
– Main keyword (keyword focus): airtable to docsend to box to dropbox sign document signing
– Predicate (main verb/action): Automate
– Relations Lexical used: Antonym (Automated vs Manual), plus Meronymy (the workflow is made of parts: Airtable, DocSend, Box, Dropbox Sign)
If your goal is to stop chasing files, links, and signatures, yes—you can automate Airtable → DocSend → Box → Dropbox Sign document signing end-to-end by letting one “source of truth” record (Airtable) generate a shareable document experience (DocSend), store the master file (Box), and trigger a legally-auditable eSignature request (Dropbox Sign).
Next, you’ll want to be clear about what this chain actually means in real operations: Airtable is the control plane (data + status), DocSend is the secure “send + track + viewer experience,” Box is the long-term governed repository, and Dropbox Sign is the signature engine with signer workflow and completion artifacts. Dropbox’s own help center documents how DocSend supports signable documents and how the signing experience works from share link to completed, read-only final copy. (help.dropbox.com)
Then, you can build the automation as a repeatable pipeline—most teams start with a no-code orchestrator (Zapier/Make) because it’s faster to implement and easier to maintain than custom code for straightforward automation workflows, and Zapier explicitly supports Airtable ↔ Dropbox Sign workflows out of the box. (zapier.com)
Introduce a new idea: once you move beyond a single document type, the real win comes from designing the workflow like a system—templates, naming conventions, error handling, and audit requirements—so it keeps working when volume scales and stakeholders multiply.
Can you automate Airtable to DocSend to Box to Dropbox Sign document signing end-to-end?
Yes—Airtable to DocSend to Box to Dropbox Sign document signing can be automated end-to-end because (1) Airtable can reliably trigger the process, (2) DocSend and Box can standardize how files are shared and stored, and (3) Dropbox Sign can send trackable signature requests with completion artifacts.
To begin, the simplest way to think about the pipeline is: Airtable decides, DocSend shares, Box stores, and Dropbox Sign signs—so every step is deterministic instead of “who has the latest PDF?”
What are the minimum requirements before you automate this workflow?
You’ll get a stable workflow only if you set up four basics up front:
- Airtable base structure: one table for “Agreements” (or “Packets”), one record per document instance, with fields like Status, Doc Type, Primary Contact, Company, File URL, DocSend Link, Box Path, Sign Request ID, Signed File URL.
- A single “trigger rule”: e.g., when Status changes to Ready to Send, automation starts. This prevents accidental duplicates.
- Access model: which service account owns DocSend and Box actions, and which users should be recipients/signers.
- A canonical file source: decide where the “master PDF” lives before sending (often Box), even if DocSend is the distribution layer.
What are the 3 most common automation triggers in Airtable for document signing?
Most teams choose one of these triggers because they map cleanly to operational intent:
- Status-based trigger (recommended): Status → “Ready to Sign” starts the chain.
- Record-created trigger: a new record in a specific view starts the chain (useful for intake forms).
- Approval-based trigger: a checkbox or approver field gets set, then the chain starts.
If you’re orchestrating with Zapier, this aligns directly with its Airtable trigger pattern and Dropbox Sign action pattern (trigger in Airtable → action in Dropbox Sign). (zapier.com)
What can break end-to-end automation ?
The failures are predictable, so prevention is mostly design:
- Duplicate signature requests: prevent by writing the Sign Request ID back to Airtable and blocking reruns when it exists.
- Wrong file version: prevent by storing a single canonical file (Box) and always referencing that file for signature.
- Missing signer data: prevent by validating required fields (email/name/role) before the automation proceeds.
- Permissions drift: prevent by using dedicated service accounts and shared folders rather than personal drives.
Evidence: According to a 2017 report by the University of South Carolina (Faculty & Staff IT Advisory Committee, anchored by the Division of Information Technology), e-signature programs are pursued specifically to reduce lengthy processing times and operating costs, and the report notes market preference for cloud deployment models (citing Gartner research and adoption patterns). (sc.edu)
What does “Airtable to DocSend to Box to Dropbox Sign document signing” mean in practice?
“Airtable to DocSend to Box to Dropbox Sign document signing” is a document-signing automation pipeline where Airtable manages structured deal or operations data, DocSend provides a controlled document-sharing experience, Box stores governed files, and Dropbox Sign executes the signature ceremony with audit-friendly outputs.
Next, let’s translate that into a real operational story: the process isn’t “four apps,” it’s one lifecycle—draft → share → store → sign → archive—where each app is responsible for a specific part of the lifecycle.

What role does Airtable play in this workflow?
Airtable is the system of record and state machine.
- It holds the who/what/when (signers, document type, due date, amount, region).
- It holds the status (Drafting → Ready → Sent → Viewed → Signed → Archived).
- It becomes your reporting layer (cycle time, bottlenecks, signature completion rate).
If you don’t treat Airtable as the “truth,” you’ll end up with mismatched states: “signed in Dropbox Sign” but “pending in Airtable.”
What role does DocSend play (and why not skip it)?
DocSend is best used when you need controlled sharing + tracking as part of the workflow.
- It standardizes how recipients view documents (links, permissions, expiration).
- It supports “signable documents” in DocSend, including adding signer fields and managing multiple signers (up to a limit described in Dropbox’s help documentation). (help.dropbox.com)
In practice, DocSend becomes the “front door” for the recipient experience—especially useful when multiple stakeholders must view before signing.
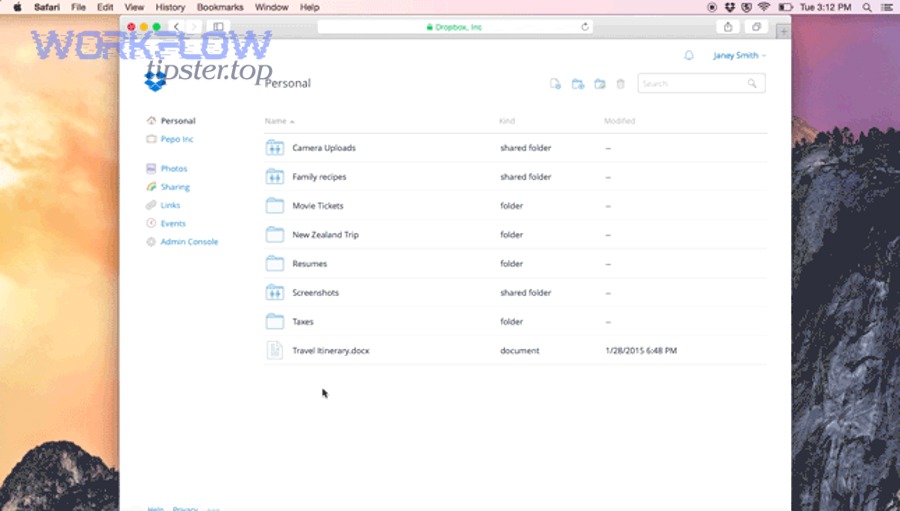
What role does Box play?
Box is your governed repository.
- It gives consistent folder structure and access controls (team ownership, retention policies).
- It reduces “file sprawl” by making one authoritative location for drafts and final signed artifacts.
A clean pattern is: Box stores the master; DocSend shares a controlled experience; Dropbox Sign produces the executed copy; Box stores the final.
What role does Dropbox Sign play?
Dropbox Sign is your signature engine:
- Sends signature requests, manages signer order, reminders, and completion.
- Produces a completed, signed document and audit trail artifacts depending on configuration.
If you’re using DocSend eSignature features, Dropbox notes that once all signers complete signing, the signable document becomes read-only and parties receive the signed copy. (help.dropbox.com)
How do you build the Airtable → DocSend → Box → Dropbox Sign automation workflow step by step?
Build this workflow with a no-code orchestrator in 5 steps—Airtable trigger, document preparation, DocSend link creation, Box storage, and Dropbox Sign request—so you consistently send the right file to the right signer and write status back to Airtable.
Then, you’ll refine the “happy path” into a reliable operational path by defining inputs/outputs at every hop.

Step 0: How do you prepare Airtable so automations don’t create duplicates?
Create (at minimum) these fields:
- Status (single select): Draft / Ready to Send / Sent / Signed / Error
- Doc Type (single select): NDA / MSA / SOW / Offer / Other
- Signer Name, Signer Email
- Box File Path (text or URL)
- DocSend Link (URL)
- Dropbox Sign Request ID (text)
- Signed File URL (URL)
- Last Automation Run (date/time)
Guardrail rule: If Dropbox Sign Request ID is not empty, do not send again.
Step 1: How do you generate or select the correct document for DocSend?
You have two practical patterns:
- Template-to-PDF pattern: generate a PDF from a template (Docs/Doc generator) and save it to Box first.
- Box-first pattern (simpler): require the user to attach/select the final PDF in Box, then your automation proceeds.
If your team already lives in Box, the Box-first pattern reduces complexity and prevents “signed the wrong draft.”
Step 2: How do you create a DocSend signable document link?
DocSend’s own docs describe how signable documents are configured in the Content library and how fields are placed and signers added. (help.dropbox.com)
Operationally, your automation should:
- Create or select the document in DocSend.
- Configure signing fields (if you do this dynamically).
- Generate a share link and write it back to Airtable (DocSend Link).
If you don’t need DocSend tracking, you can skip this and go straight to Dropbox Sign—but when tracking matters, DocSend is the “view layer.”
Step 3: How do you store the master file and the final signed copy in Box?
Use a deterministic folder scheme, for example:
/Agreements/{Company}/{Year}/{Doc Type}/- Filename:
{Company}-{DocType}-{RecordID}-vFinal.pdf
Automation should write the Box path into Airtable so humans can always locate the file—even if the no-code run fails midstream.
Step 4: How do you send the Dropbox Sign signature request automatically?
If you’re using Zapier, this is a standard pattern: Airtable trigger → Dropbox Sign action, and Zapier explicitly supports Airtable/Dropbox Sign integrations and templates. (zapier.com)
Core request settings to decide:
- Signer order: parallel vs sequential
- Reminders: on/off, cadence
- CCs / internal notification
- Return artifacts: signed PDF URL, status, timestamps
Write the resulting Signature Request ID and status back to Airtable immediately so the workflow becomes observable.
Step 5: How do you sync signing status back to Airtable?
Use a webhook/event trigger from Dropbox Sign (or polling if needed) to:
- Update Status → Signed
- Save Signed File URL
- Save completion timestamp
- Optionally copy the signed PDF into Box and store the Box link too
Optional: 1 video walkthrough
Evidence: According to a 2025 user-experience study published on arXiv, a controlled study with 20 participants found a strong preference for remote e-signature usability (e.g., majorities rating remote signatures more usable), reinforcing why automated, web-based signing flows reduce friction compared with hardware-heavy flows. (arxiv.org)
Which automation approach is best: Zapier vs Make vs native integrations vs custom code?
Zapier wins in speed-to-launch, Make is best for complex branching and data shaping, native integrations are best when you already pay for them and need fewer moving parts, and custom code is optimal for strict compliance, bespoke logic, or very high volume.
However, picking the “best” approach isn’t about brand—it’s about matching your workflow complexity, security model, and maintenance capacity.

What criteria should you use to choose the right approach?
Use these decision criteria (in this order):
- Reliability & observability: retries, error logs, replay ability
- Security/compliance: least privilege, audit trails, data residency
- Complexity handling: branching logic, loops, multi-step transforms
- Total cost of ownership: not just subscription—also maintenance time
- Time to implement: weeks vs days vs hours
Zapier vs Make: which is better for this exact chain?
- Zapier is usually best if your workflow is “mostly linear” and you want fast implementation with common triggers/actions. Airtable ↔ Dropbox Sign support is straightforward in Zapier’s ecosystem. (zapier.com)
- Make is usually best if you need heavy transformations, routers, iterators, and multi-path scenarios (e.g., multiple signers, conditional DocSend experiences, branching by doc type).
This is where “automation workflows” mature: you start linear, then add complexity only when required.
When should you use native integrations?
Use native integrations when:
- Your organization already standardizes on a vendor suite.
- You need fewer failure points.
- You want vendor-supported compliance and support SLAs.
But be careful: “native” often means less flexibility in multi-app chain orchestration.
When is custom code worth it?
Choose custom code if:
- You need strict policy enforcement (fine-grained permissions, encryption requirements).
- You must integrate internal systems not supported by no-code tools.
- You process high volumes where per-task pricing becomes expensive.
- You need deep audit logging and guaranteed idempotency.
If your organization also runs other operational chains like “calendly to calendly to microsoft teams to clickup scheduling” or “calendly to calendly to microsoft teams to trello scheduling”, you’ll recognize the same pattern: no-code is fast, but code wins when governance and scale dominate.
Evidence: According to a 2017 University of South Carolina report (Faculty/Staff IT Advisory Committee, including Division of Information Technology leadership), Gartner research cited in the report stated that 85% of clients chose SaaS deployment models for e-signature tools—one reason no-code/SaaS orchestration is often the default starting point. (sc.edu)
— Contextual Border (macro → micro): You now know what the workflow is and how to build it. Next, the focus shifts to micro-level execution details—naming rules, exceptions, monitoring, compliance, and troubleshooting—so the workflow keeps working under real operational pressure. —
How do you optimize and troubleshoot this document-signing workflow when it scales?
Optimize this workflow by adding four layers—standardized templates, status telemetry, error handling with retries, and governance controls—so higher volume doesn’t create higher chaos.
More importantly, scaling success is less about adding steps and more about making every step inspectable and recoverable.

How do you standardize templates so every record produces the right signing packet?
Standardization prevents 80% of operational mistakes:
- Doc type mapping: Airtable Doc Type → correct template or PDF source
- Signer mapping: Role-based signer fields (Legal, Finance, Customer)
- Field placement rules: consistent signature/date/title placement
- Naming conventions: predictable filenames and folder paths
If you use DocSend’s signable documents, follow Dropbox’s documented approach to configuring signers and fields so humans don’t reinvent setup every time. (help.dropbox.com)
How do you add monitoring and alerting (so failures don’t stay invisible)?
A “scaled” workflow is one where failures are caught automatically.
Minimum monitoring checklist:
- Airtable error field: write failure reason into a field like
Last Error - Retry counter: attempt up to N times for transient errors
- Alert channel: Slack/Teams message on failure (include Record URL)
- Daily reconciliation job: find records stuck in Sent > X days
If you also run engineering pipelines like “github to clickup to discord devops alerts”, borrow that same discipline: alerts should contain context, links, and a clear “next action.”
What are the most common troubleshooting cases (and the fastest fixes)?
- Signer never receives email → verify signer email, domain allowlists, resend logic
- Wrong file is signed → lock the canonical file source (Box-first pattern)
- Status mismatch → enforce “write-back” after each step, not only at the end
- DocSend link access issues → check link settings, expiration, permissions
- Duplicates → enforce idempotency with “Request ID exists” guardrail
How do you handle compliance and audit requirements without slowing the workflow?
Treat compliance as design constraints, not afterthoughts:
- Audit trail storage: store signed PDF + audit log artifact in Box
- Access controls: restrict who can edit templates and who can trigger signing
- Retention rules: define how long drafts vs signed contracts live
- Least privilege: service accounts with minimum scope
Dropbox’s help documentation emphasizes the signing experience lifecycle and final document handling (e.g., read-only completed state and distribution of signed copies). That is exactly the kind of predictable lifecycle auditors want. (help.dropbox.com)
Evidence: According to EDUCAUSE reporting on e-signature adoption in higher education, institutions have reported significant reductions in processing time when shifting to e-signatures—illustrating why scaling “paperless + automated signing” often produces measurable cycle-time gains. (er.educause.edu)

