If you are seeing microsoft teams permission denied, the short answer is yes: it is a real access-control failure—but it can originate from multiple layers (Teams policy, Entra ID, device compliance, app consent, or even a mis-scoped integration token) that all look “the same” to users.
In practical Microsoft Teams Troubleshooting, the fastest wins come from separating who is denied (user vs guest vs app), where the denial happens (client, Teams service, Graph/API gateway, or tenant policy), and what resource is blocked (channel post, file attachment, meeting artifact, webhook callback, bot action).
Next, you need a repeatable diagnostic path that avoids random trial-and-error: capture the exact action, error surface (UI vs API), and correlation context, then confirm whether the denial is caused by role/policy mismatch, conditional access, missing consent, or token scope drift.
To move from symptoms to root cause, Giới thiệu ý mới: the sections below map common “permission denied” patterns to the right fix, including tenant controls, app permissions, and integration hardening that prevents the same denial from returning.
What does “Microsoft Teams permission denied” actually mean in practice?
Yes—“permission denied” means Teams (or a dependency) evaluated your request and concluded you are not allowed to perform that specific operation, typically because your identity, token, role, or policy does not satisfy an authorization rule.
To connect the symptom to the correct remedy, the key is to treat this error as an authorization decision, not a generic failure. In Teams, authorization can be evaluated by multiple components: the Teams service itself (policy and membership), Microsoft Entra ID (identity, sign-in risk, conditional access), SharePoint/OneDrive (file and folder ACLs), or Microsoft Graph (application vs delegated scopes).

Concretely, “permission denied” usually collapses several distinct realities into one message:
- Membership denied: you are not a member/owner of the team, private channel, or chat context required for the action.
- Policy denied: a Teams policy (messaging, meeting, app permission policy, information barrier, etc.) blocks the feature.
- Tenant security denied: conditional access, device compliance, location restrictions, or risk policies block the sign-in or session.
- App consent denied: the integration/app lacks admin consent or correct scopes, so Graph returns 401/403.
- Storage denied: posting succeeds but attachments fail because the underlying SharePoint/OneDrive permission is missing.
To keep expectations realistic, “permission denied” can also be secondary: the user sees a denial, but the true issue is an upstream token or resource reference that no longer exists, which then triggers a protective “deny” response at the gateway layer.
The fastest proof point is to reproduce the same action with a known-good identity (a Teams owner/admin) and compare: if the action works for the owner but fails for a specific user, you likely have a membership/policy issue; if it fails for everyone, the tenant/app configuration is the prime suspect.
The business impact is non-trivial: authorization friction blocks collaboration throughput and creates invisible workarounds (shadow chat tools, file sharing outside governed channels). Theo nghiên cứu của Forrester Consulting từ Total Economic Impact™ practice, vào 04/2019, một tổ chức tổng hợp ghi nhận ROI 832% và thời gian hoàn vốn < 6 tháng khi triển khai Microsoft Teams, cho thấy các “blockers” về quyền truy cập có thể ảnh hưởng trực tiếp đến giá trị khai thác nền tảng.
Which layer is denying access: Teams policy, Entra ID, or the resource itself?
There are three primary denial layers—Teams authorization, Entra ID session controls, and downstream resource ACLs—and you identify the correct layer by matching the denied action to the owning service.
To avoid misdiagnosis, the important move is to map the operation to the service of record. Then you can inspect the correct controls instead of “fixing” the wrong place. After that, you can validate whether the denial is consistent across devices and clients, which often reveals whether the block is policy-driven or token/session-driven.

Use this quick mental model:
- Teams-layer (authorization inside Teams): posting messages, creating channels, adding apps, creating meetings, managing team settings, messaging extensions, certain admin-only operations.
- Entra ID-layer (identity and session): login blocked, MFA required but failing, device compliance required, sign-in risk policies, token issuance issues, conditional access restrictions.
- Resource-layer (SharePoint/OneDrive/Exchange): file attachments, tabs that are SharePoint pages, meeting recordings/transcripts storage, channel file libraries, Planner/Loop/Whiteboard artifacts.
To make this actionable, here is a compact “symptom-to-layer” mapping. This table helps you identify which control surface to check first, so you can cut time-to-fix and avoid random changes.
| Symptom | Most likely denial layer | Fast verification | Typical fix direction |
|---|---|---|---|
| Cannot post in a specific channel; other channels OK | Teams membership / channel policy | Check if channel is private/shared; confirm membership | Add member; adjust channel moderation; review messaging policy |
| Sign-in succeeds, but actions fail after “something changed” | Entra ID session / conditional access | Compare web vs desktop; check if device compliance required | Update CA policy; ensure compliant device; reauthenticate |
| Messages post, but attachments fail | Resource ACL (SharePoint/OneDrive) | Try uploading in Files tab / SharePoint site directly | Fix SharePoint permissions; ensure site provisioning; storage policy |
| Integration/bot returns 403/401; users see “denied” | App consent / Graph scopes | Inspect token scopes; reproduce via Graph Explorer (admin) | Grant admin consent; correct delegated/app permissions |
When you treat “denied” as a layer problem, you can also spot compound failures: for example, a Teams policy allows posting, but an information protection policy prevents sharing a file, which users interpret as “Teams blocked me,” even though Teams is not the denying party.
As an operational guideline, define an internal escalation rule: if denial is limited to one team/channel, start with membership and channel settings; if it spans multiple teams, go straight to policy/Entra ID; if it is attachment-only, pivot to SharePoint/OneDrive permissions.
The ROI story reinforces why this matters: the platform value depends on consistent access and predictable controls. Theo nghiên cứu của Forrester Consulting từ Total Economic Impact™ practice, vào 04/2019, một tổ chức tổng hợp ghi nhận NPV 27.1M và ROI 832% khi triển khai Microsoft Teams—nhưng các gián đoạn do quyền truy cập có thể làm “rò rỉ” lợi ích theo thời gian.
How do you troubleshoot permission denied in under 15 minutes?
The fastest troubleshooting approach is a 6-step triage: capture the exact action, reproduce in another client, classify the denial layer, verify identity context, check policy/role, then validate token/scope if an integration is involved.
To keep your investigation tight, you must collect the minimum data that uniquely identifies the denial. Then, you can follow a deterministic path that narrows the cause without changing settings prematurely. After that, you can fix once—and fix correctly.
- Step 1: Pin down the action. What exactly was attempted (post message, upload file, create meeting, add app, trigger webhook callback)? “It doesn’t work” is not debuggable.
- Step 2: Capture the surface. Does it fail in desktop, web, and mobile equally? Web-only failures often implicate browser session controls; desktop-only failures can implicate cached tokens or device compliance posture.
- Step 3: Compare with a control identity. Test with a Teams owner or a known-good admin. If only one user fails, you likely have a membership/policy assignment issue.
- Step 4: Check the “where”. Is it a private/shared channel? Is the user a guest? Are you posting into a channel with moderation? Each of these changes the authorization rules.
- Step 5: Check policy/role alignment. Confirm the user’s Teams policies (messaging/meeting/app) and role (member vs owner). For admin actions, confirm the admin role assignments are correct.
- Step 6: If an integration is involved, inspect token and scopes. If you see 401/403 at the API boundary, it is usually missing consent, wrong permission type (application vs delegated), or an expired/rotated credential.
For teams that run automations, document a “deny packet” you can request from operators: timestamp, user UPN, tenant, client type, target team/channel ID, and the integration name if relevant. This becomes your repeatable evidence bundle, not an anecdotal complaint.
Also, do not ignore “nearby” symptoms. In real-world cases, you will see correlated issues like posts succeed but metadata is missing, or webhooks fire but payload fields are empty, which can lead teams to chase the wrong error class. This is where disciplined troubleshooting protects your time.
To ground the importance of a fast, repeatable method: Theo nghiên cứu của Forrester Consulting từ Total Economic Impact™ practice, vào 07/2025, ROI dự phóng 122%–408% cho Microsoft Teams cùng Microsoft 365 Copilot cho thấy tốc độ “unblock” người dùng và giảm ma sát quy trình có thể ảnh hưởng trực tiếp đến lợi ích kỳ vọng khi mở rộng sử dụng.
How to fix permission denied for end users in the Teams client?
Fixing end-user permission denied usually means correcting membership/role, resolving client token state, or addressing a policy that blocks the specific feature—and you can confirm which one applies by testing the same action in Teams web and by comparing with a team owner.
To begin, treat user-facing fixes as “least invasive first.” Then, if the denial persists, you move to policy assignments and channel settings that structurally block the feature. After that, you validate storage and attachments because users often report those as “Teams denied” even when the underlying issue is file ACLs.

Is the user actually allowed in that context (team, channel, chat)?
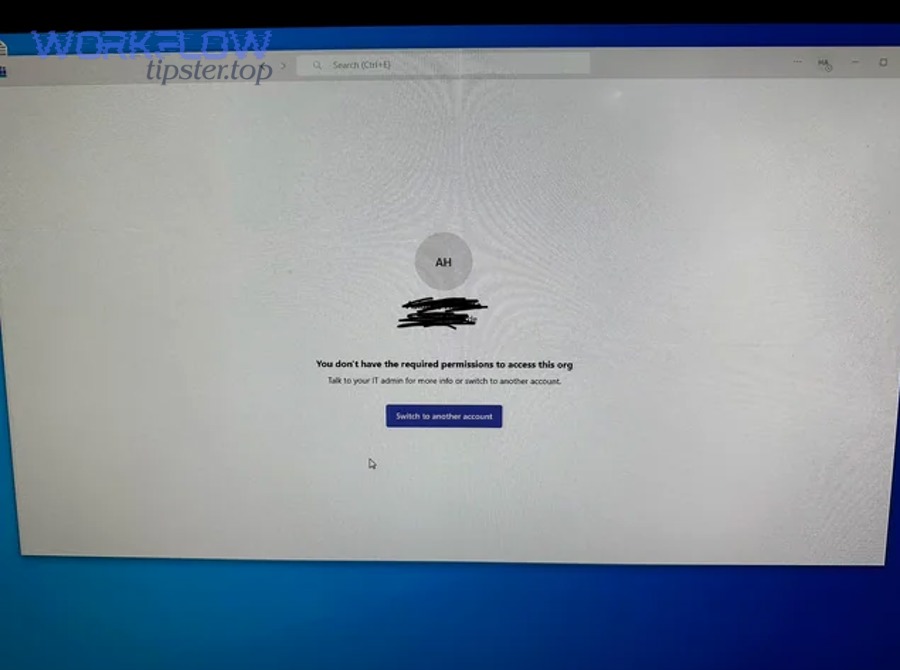
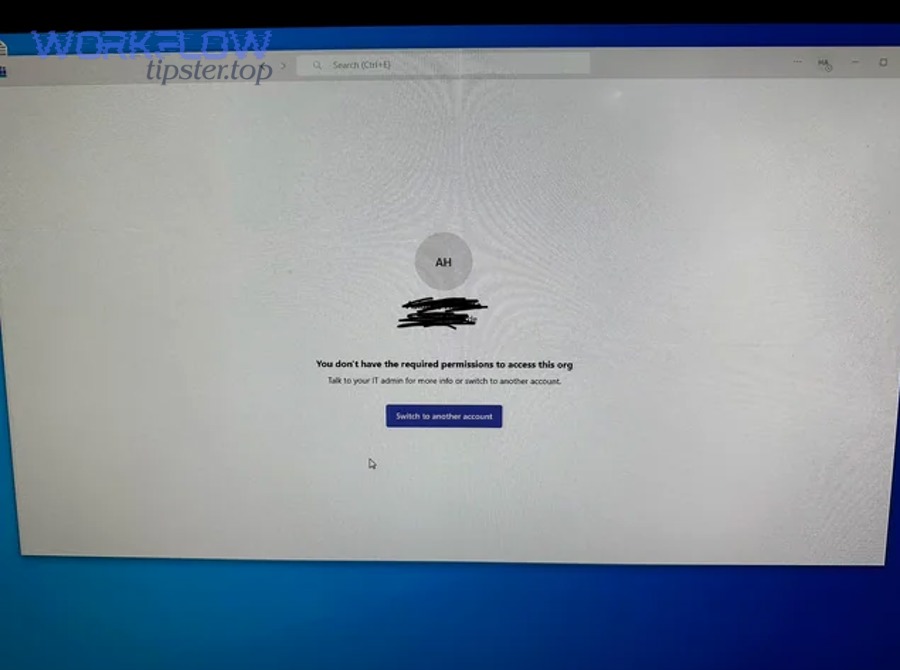
No, not always: users can be signed into Teams successfully and still be denied inside a specific team, private channel, or shared channel because membership is scoped at the container level.
Specifically, private channels have separate membership from the parent team, and shared channels can involve cross-tenant rules that differ from standard team membership. To move forward, confirm:
- User is a member of the team (not removed or pending).
- User is explicitly added to the private channel if applicable.
- User role (member vs owner) matches the action (e.g., only owners can change some settings).
Next, if membership is correct but posting is denied, examine channel moderation: moderated channels can restrict who can start new posts or reply. That often surfaces as “permission denied” to non-moderators.
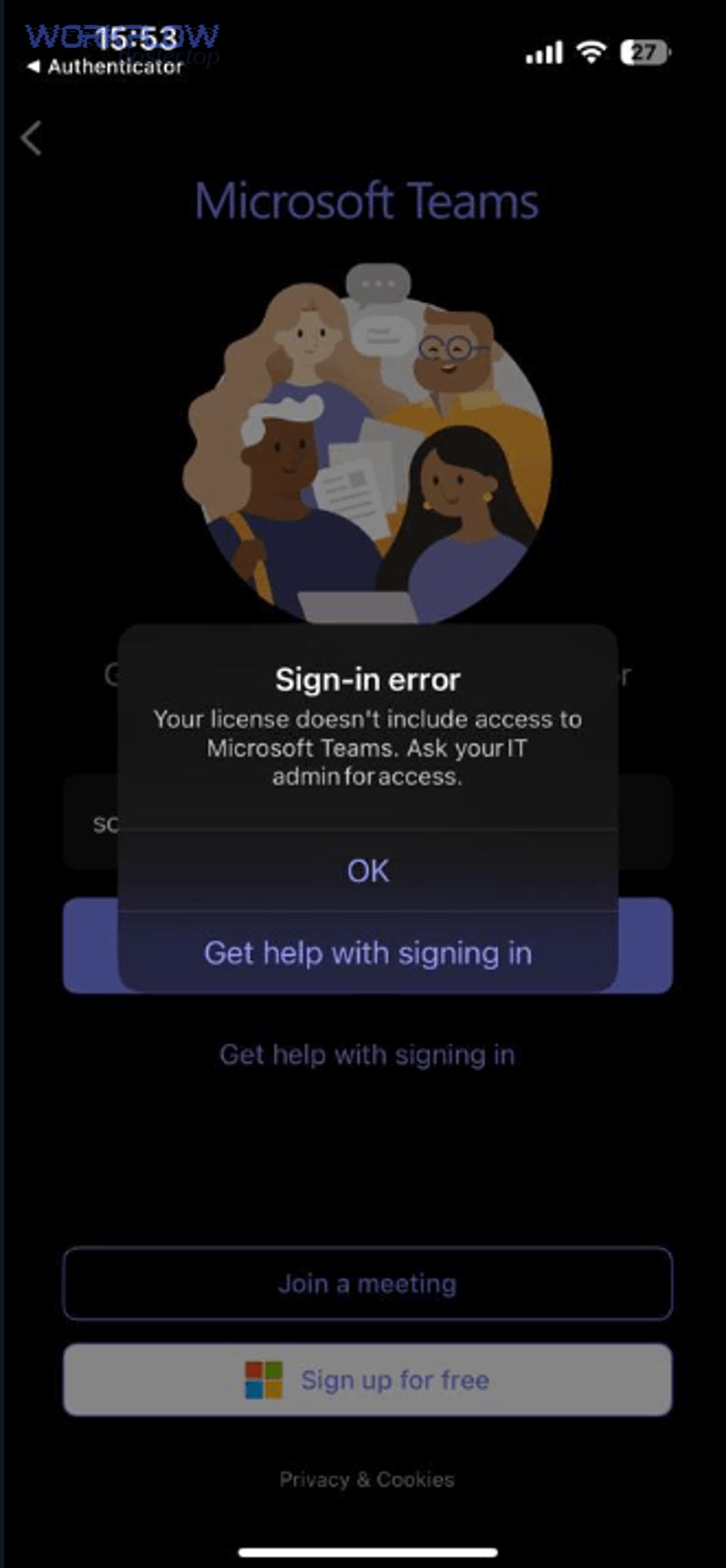
Could cached tokens or client state be the culprit?
Yes: client token drift can produce denial-like behavior, especially after password changes, MFA policy updates, or tenant security changes.
To isolate this quickly, compare Teams web vs desktop. If web works but desktop fails, you likely have a cached credential/session issue. The pragmatic fix sequence is:
- Sign out of Teams, close the client, and sign back in.
- Try Teams web in a private/incognito session to bypass cached cookies.
- If the tenant recently changed security posture, ensure the user completes any new MFA prompts and device registration steps.
Then, if only one device fails, treat it as a device posture problem rather than a Teams membership issue.
Are attachments failing even when messaging works?
Yes, attachments can be denied even when chat posting is allowed because files are governed by SharePoint/OneDrive permissions and provisioning status.
To verify, try uploading the same file through the channel’s Files tab. If that fails, the denial is likely in the SharePoint site/library permissions or in the site provisioning workflow. To resolve, ensure the user has appropriate permissions to the underlying document library and that the team’s SharePoint site exists and is healthy.
Finally, keep a user-facing script that explains the difference between “I can open Teams” and “I can perform this action,” because it reduces repeated tickets. Theo nghiên cứu của Forrester Consulting từ Total Economic Impact™ practice, vào 04/2019, thời gian hoàn vốn < 6 tháng cho thấy việc giảm thời gian gián đoạn do lỗi quyền truy cập là một đòn bẩy thực tế để bảo toàn lợi ích triển khai.
How to fix permission denied for admins: roles, policies, and Conditional Access
Admin-facing permission denied is most often caused by missing or mis-scoped administrative roles, policy assignment conflicts, or Conditional Access controls that block privileged actions.
To diagnose correctly, you must separate “admin of Teams” from “admin of identity.” Then, you can validate whether the denial is tied to an admin center operation, a policy write, or a protected API call. After that, you can decide whether the fix is role assignment, policy scope correction, or session control adjustment.
Are you using the correct admin role for the operation?
No, not by default: modern Microsoft 365 administration is role-scoped, and different Teams admin actions require different roles or privileges.
To move forward, align the operation to the role:
- Teams administration: managing Teams policies, meetings policies, calling policies, app policies often requires Teams admin roles (or broader Microsoft 365 roles depending on tenant design).
- Identity and access: app consent, Conditional Access, token policies require Entra ID roles with appropriate privileges.
- Compliance and protection: information barriers, retention policies, sensitivity labels may require security/compliance roles beyond Teams.
Next, if you can read settings but cannot save changes, that is a strong signal of role mismatch rather than a transient service error.
Are policies conflicting or assigned at the wrong scope?
Yes: Teams policies can be assigned directly to users, inherited through groups, or overridden by higher-priority assignments, resulting in “allowed here, denied there” behavior.
To troubleshoot, confirm the effective policy for the user (messaging, meeting, app permission policy) and ensure it matches the expected feature set. Then, verify whether a policy blocks actions like:
- Posting in certain contexts (messaging policy settings).
- Creating private channels or shared channels (team/channel configuration limits).
- Installing or using specific apps (Teams app permission policy).
Could Conditional Access be blocking privileged operations?
Yes: conditional access can block sign-in, require compliant devices, require MFA, or restrict locations—often affecting admin operations more than standard user operations because admins operate from different devices and contexts.
To validate, check whether the denial happens only on unmanaged devices, only off-network, or only in certain geographies. Then, adjust the policy with a least-privilege mindset: restrict where needed, but ensure admin workflows have a compliant, supported path.
In many organizations, the “fix” is not to weaken security, but to document the supported admin operating model (compliant device, enforced MFA, approved locations) so admins stop encountering “surprise denials.” Theo nghiên cứu của Forrester Consulting từ Total Economic Impact™ practice, vào 07/2025, ROI dự phóng 122%–408% cho Teams cùng Copilot nhấn mạnh rằng quản trị ổn định và an toàn là tiền đề để mở rộng năng suất mà không bị nghẽn bởi lỗi quyền.
How to fix permission denied for webhooks, bots, and Graph-based integrations
Integration permission denied is usually caused by missing consent, incorrect permission type (application vs delegated), token scope mismatch, or an expired credential—so the fix is to re-align identity, scopes, and callback security end-to-end.
To start, treat every integration as a security contract: who is calling, what scopes are granted, what resource is targeted, and what authentication the endpoint expects. Next, validate the authorization story from both sides—Teams/Graph and your endpoint. After that, you can harden the integration to reduce future denials.
![]()
Are you using the correct authentication model for the job?
Yes, it matters: a bot posting as itself, an app posting on behalf of a user, and a service posting via application permissions are three different authorization models with different constraints.
To clarify quickly:
- Delegated permissions: the app acts as the signed-in user. If the user is denied, the app is denied. This is common for user-triggered flows.
- Application permissions: the app acts as the app (no user). This requires admin consent and careful scoping, but can avoid user-by-user permission drift.
- Webhook callbacks: Teams calls your endpoint; your endpoint must validate signatures/tokens and respond within expected timeouts.
Do you have the right scopes and admin consent?
Not always: “permission denied” in integrations is often a quiet 403/401 at Graph or a denial returned by the Teams bot framework because the app lacks consent for the specific resource.
To fix, confirm:
- The app registration includes only the scopes you truly need (least privilege).
- Admin consent is granted for organization-wide scopes where required.
- The token you use at runtime actually contains the expected scopes/roles (do not assume; verify).
Then, rotate credentials deliberately: if you changed a client secret/certificate, ensure every environment updated. Expired credentials frequently present as “denied” when the platform refuses to honor the token request.
Are you mixing denial with transport errors (500s, slow runs, retries)?
Yes: operational failures can masquerade as authorization failures when systems apply protective behavior (fail closed) after repeated timeouts or invalid requests.
To illustrate, teams sometimes conflate a backend crash or transient platform issue with “permission denied,” especially when an automation retries and eventually returns a generic message. If your logs show server-side exceptions, you may be chasing the wrong issue. In integration operations, you may also see adjacent error narratives like microsoft teams webhook 500 server error even though the original trigger was an authorization/consent issue that caused an unexpected code path downstream.
Similarly, if your automation platform reports empty fields or missing properties, the issue may not be permission at all. You can see sequences where Teams events arrive, but the downstream mapping is wrong, leading operators to “fix permissions” when the real problem is data shape. This confusion is common enough that many teams maintain a dedicated internal page titled “Microsoft Teams Troubleshooting” to separate authorization failures from payload and mapping failures.
If you operate at scale, embed one authoritative video reference in your runbook for consistent admin practices and integration governance:
To anchor the value of “getting integration auth right,” consider the productivity multiplier: automations amplify both success and failure. Theo nghiên cứu của Forrester Consulting từ Total Economic Impact™ practice, vào 04/2019, ROI 832% cho Teams cho thấy các luồng tích hợp chạy ổn định có thể đóng góp đáng kể vào lợi ích hợp nhất công cụ—nhưng nếu bị “denied” lặp lại, bạn sẽ mất lợi ích theo cấp số nhân.
How to prevent permission denied from returning: governance and observability
Prevention comes from three controls: least-privilege design, change-managed policy assignment, and observability that distinguishes authorization denials from operational errors.
To reduce recurring tickets, you must stop treating permission denied as an incident-only problem. Next, you formalize a governance baseline: who gets what policy, how exceptions are handled, and how integrations are onboarded. After that, you build observability so denials are detected early and attributed correctly.
Build a least-privilege baseline that matches real job functions
Yes: the fastest way to reduce denials is to make default policies fit the majority of roles, then handle edge cases explicitly instead of ad hoc.
Practically, define role-based bundles (for example: frontline, standard knowledge worker, external collaborator, automation operator). Then, assign Teams messaging/meeting/app policies consistently via groups so policy drift is reduced.
Implement controlled change for security and collaboration policies
Yes: many denial spikes are self-inflicted during policy changes (Conditional Access tightening, app policy updates, guest restrictions), especially when change communication is weak.
To prevent this, require a simple change checklist:
- Test with representative users (including guests and mobile users).
- Validate web and desktop clients.
- Confirm integration service accounts still obtain tokens and can post/callback.
- Document the rollback path and known side effects.
Instrument denial telemetry and classify it automatically
Yes: the practical difference between fast recovery and repeated churn is whether you can classify the denial at the time it happens.
For example, tag events by category:
- Identity/session: sign-in blocked, MFA issues, device compliance errors.
- Teams authorization: membership, channel moderation, policy restrictions.
- Resource: SharePoint/OneDrive ACL failures, site provisioning issues.
- Integration: token scope mismatch, consent missing, endpoint auth failures.
Then, route each category to the right owner (identity team vs Teams admins vs app owners). This reduces “ping-pong” troubleshooting and keeps your operational response consistent.
To close the loop, schedule periodic audits for app permissions and policy assignments, and explicitly deprecate old runbooks that assume legacy controls. Theo nghiên cứu của Forrester Consulting từ Total Economic Impact™ practice, vào 07/2025, ROI dự phóng 122%–408% cho Teams cùng Copilot nhấn mạnh rằng vận hành bền vững và kiểm soát tốt quyền truy cập là điều kiện cần để khai thác lợi ích ở quy mô lớn.
Rare denial patterns: cross-tenant guests, “empty payload” confusion, and misleading symptoms
Rare patterns exist where the user perceives permission denied, but the true root cause is cross-tenant governance, guest restrictions, or data-shape failures that mimic denial.
To navigate these edge cases, you must apply a “contextual border”: if your earlier steps confirmed membership, correct policies, and valid consent, then you move to cross-tenant rules, guest posture, and payload diagnostics. After that, you can eliminate false positives and avoid weakening security unnecessarily.

Is the denial caused by guest/B2B governance rather than Teams permissions?
Yes: guest access and cross-tenant collaboration can impose constraints that do not apply to internal users, especially in shared channels or when external identities are subject to different sign-in controls.
To diagnose, compare an internal user vs the same guest flow, and confirm whether the denial happens only for external identities. Then, review tenant-to-tenant collaboration settings and guest policies that restrict messaging, file access, or app usage.
Can missing fields create a false “permission denied” diagnosis?
Yes: in automation pipelines, missing data can look like a denial when a downstream module refuses to write due to validation rules or schema mismatch.
For example, operators might report “Teams denied the post,” but the true issue is microsoft teams missing fields empty payload coming from an event that lacks required properties, causing a mapping failure. To avoid this, validate the raw event payload before blaming authorization, and confirm whether the failing component is Teams or the automation platform’s data validation.
Do “attachments missing” cases actually point to storage ACLs?
Often, yes: the message may succeed while the attachment fails because Teams hands file storage to SharePoint/OneDrive, which can deny access independently.
To confirm, test file upload directly in the channel’s Files tab and check whether the user can access the underlying library. If not, fix resource permissions rather than changing Teams messaging controls.
When should you treat the denial as a true platform incident?
When the denial is global, sudden, and reproducible across roles and clients, you should suspect a broader service-side condition rather than a local configuration issue.
In those cases, do not “randomly grant more access.” Instead, freeze changes, capture correlation evidence, and validate whether the issue is a transient platform behavior or a widespread policy rollout. If your logs also show operational errors (timeouts, retries, 500 responses), remember that incidents can cascade into perceived authorization failures—especially when systems fail closed under load.
By keeping these edge cases separate, you protect security posture while improving mean time to resolution. Theo nghiên cứu của Forrester Consulting từ Total Economic Impact™ practice, vào 04/2019, payback < 6 tháng cho Teams nhấn mạnh rằng giảm “thời gian chết” do lỗi truy cập là một đòn bẩy hiệu quả để bảo toàn giá trị triển khai theo thời gian.

