A “google chat oauth token expired” error usually means your integration is trying to use an access token or refresh token that is no longer valid, so Google refuses the request and your app can’t post messages, read spaces, or act on behalf of the user.
Next, you need to identify whether the failure is truly token expiration (normal lifecycle) or token invalidation (revoked consent, changed app status, rotated credentials), because the fix changes depending on which one happened.
Then, you should apply a repeatable repair workflow: confirm the exact error type, confirm which token is failing, re-authorize if needed, and harden your refresh-and-retry logic so the issue doesn’t come back.
Introduce a new idea: once the core OAuth problem is fixed, you can speed up google chat troubleshooting by separating “auth failures” from “webhook and trigger failures,” which often look similar in logs but require different actions.
What does “Google Chat OAuth token expired” mean?
“Google Chat OAuth token expired” is an authentication failure where a Google Chat API request is rejected because the token presented is no longer valid for authorization, typically due to expiration, revocation, or a misconfigured OAuth lifecycle in the client.
To better understand why the error appears, it helps to separate the token types and their jobs in a Google Chat integration.
What is the difference between an access token and a refresh token in Google Chat OAuth?
An access token is the short-lived credential your integration sends to the Google Chat API, while a refresh token is the long-lived credential your app uses to obtain a new access token without asking the user to sign in again.
Specifically, the access token is what your HTTP requests carry (usually in an Authorization header), so when it expires your API calls start returning authorization errors.
For example, the refresh token never “calls Google Chat” directly; it calls the token endpoint to get a new access token, and then your app retries the Google Chat request using the fresh access token.
- Access token: used on every Google Chat API call; expires relatively quickly.
- Refresh token: used only to mint new access tokens; may be invalidated by policy, consent changes, or app configuration.
- Scope: limits what the tokens can do (which Chat resources/actions your app may access).
What does “invalid_grant: Token has been expired or revoked” mean in practice?
“invalid_grant: Token has been expired or revoked” means the token exchange step failed, so your app cannot refresh and must treat the stored token as unusable until it re-authorizes or fixes the underlying configuration.
More specifically, you’ll usually see it when your code attempts a refresh-token exchange and Google refuses to issue a new access token.
In practice, the fastest way to interpret it is: the token you’re holding is not acceptable anymore—either because it naturally expired under a special policy, or because it was revoked/invalidated.
When does Google Chat OAuth “expire” versus “get revoked”?
OAuth “expires” when the token lifecycle reaches its time limit, while OAuth “gets revoked” when consent or credentials are invalidated by a user action or administrative/configuration change.
Next, you can map this to real situations that developers commonly hit:
- Expired: access token timed out and your app didn’t refresh; or refresh token expired due to a testing/publishing status policy.
- Revoked: user removed app access; admin blocked the app; scopes changed and old consent is no longer valid; credentials were rotated in a way that breaks refresh.
- Invalid: redirect URI mismatch, wrong client, or a token stored/used for the wrong environment.
Is your Google Chat integration failing because the OAuth token expired?
Yes—if your logs show authentication errors immediately after an access token’s lifetime ends and the failures stop after a successful refresh or re-authorization, your Google Chat integration is failing because the OAuth token expired (or your refresh process failed) for at least three common reasons: missing refresh logic, bad token storage, or revoked/invalid refresh tokens.

Below, you can confirm it quickly by matching symptoms to the stage where your integration breaks.
Are you seeing HTTP 401/403 responses from the Google Chat API right after a period of inactivity?
Yes, that pattern strongly suggests an expired access token or a refresh token that can’t be used after inactivity, especially if the integration works again right after re-login.
Then, check the timing: if failures start around the same interval after the last successful call, you’re likely holding an access token too long or failing to refresh before calling Chat.
- Likely cause: access token expired and your app did not refresh before calling the API.
- Common log hints: “Unauthorized”, “Invalid Credentials”, “Request had invalid authentication credentials”.
Is your refresh step failing with “invalid_grant” even though your code hasn’t changed?
Yes, and that usually means the refresh token is no longer valid, not just the access token.
However, the key nuance is why it’s no longer valid: it might be revoked by the user, or it might be subject to a policy that forces it to expire (for example, certain testing configurations in Google Cloud projects can cause refresh tokens to stop working after a short period).
According to guidance published by Google for Developers (Google Ads API “Common Errors”), a project with an external OAuth consent screen in Testing status can receive refresh tokens that expire in 7 days, leading to “invalid_grant” until the publishing status changes.
Are you mixing tokens across environments (dev/staging/prod) or users?
Yes—token mix-ups are one of the fastest ways to create “expired” errors that are actually “wrong token” errors.
Next, verify that the stored refresh token is bound to the correct OAuth client, the correct redirect URI configuration, the correct user identity, and the correct scope set for the Google Chat actions you’re performing.
- Dev/prod mismatch: tokens minted in dev can’t reliably be used in prod if client IDs differ.
- User mismatch: a token for User A won’t authorize actions for User B’s resources.
- Scope mismatch: the token may be “valid” but not authorized for the specific Chat API endpoint.
What are the most common causes of Google Chat OAuth token expired errors?
There are 6 main causes of Google Chat OAuth token expired errors: access token not refreshed, refresh token invalidated, consent screen testing policy, scope changes, clock/time skew, and incorrect OAuth client/redirect configuration.

To illustrate which cause matches your symptoms, use the table below as a quick diagnostic map.
This table contains the most common symptoms developers see and the most likely underlying cause, helping you pick the correct fix instead of re-authorizing blindly.
| Symptom in logs | Most likely cause | Fastest confirmation | First fix to try |
|---|---|---|---|
| 401 Unauthorized after token age threshold | Access token expired; no refresh before call | Check whether refresh endpoint was called | Add refresh-before-call and retry-on-401 |
| invalid_grant on refresh_token exchange | Refresh token revoked/expired | Re-authorize once; see if it resolves | Force re-consent; store new refresh token |
| Works for 7 days, then always fails | Testing-mode policy on refresh tokens | Check OAuth consent screen publishing status | Move app to production / verification path |
| Fails after changing scopes | Old consent no longer matches scope set | Compare stored scopes vs requested scopes | Re-authorize with updated scopes |
| invalid_grant intermittently across servers | Clock skew / incorrect time handling | Compare server time vs reliable NTP | Fix time sync; refresh earlier |
| redirect_uri_mismatch or client mismatch | Wrong OAuth client/redirect configuration | Compare configured redirect URIs | Fix client config; re-authorize |
Is your app failing to refresh the access token before calling Google Chat?
Yes, this is the #1 cause: your app keeps using an old access token until Google rejects it, and only then you realize refresh logic isn’t running or isn’t wired into the request pipeline.
Next, ensure your code treats access tokens as disposable and refreshes them proactively, not reactively.
- Store expires_at (absolute time) rather than only expires_in.
- Refresh early (for example, 2–5 minutes before expiry) to avoid race conditions.
- On a 401, refresh once and retry the API call exactly once to avoid infinite loops.
Did the user revoke consent or did an admin block the app?
Yes, revocation is common in real organizations: users remove access during cleanup, admins disable an app, or security policy changes invalidate refresh tokens.
Then, your integration must respond by prompting a clean re-authorization rather than repeatedly retrying refresh.
- User-driven: “Remove access” in Google Account permissions.
- Admin-driven: app blocked in Workspace admin settings or restricted scopes.
- Security-driven: suspicious activity triggers token invalidation.
Is your OAuth consent screen in “Testing,” causing refresh tokens to expire quickly?
Yes—this specific configuration can make a problem look like random expiration when it’s actually a predictable policy.
Next, if your integration reliably breaks after a short window (often measured in days rather than minutes/hours), check your Google Cloud project’s consent screen status and whether your app is still treated as unverified/testing.
Did you change scopes or the Chat permissions after users already connected?
Yes—scope changes commonly break existing tokens because the stored consent no longer matches what your app now requests.
Then, you should treat the change as a new authorization contract: re-run consent, store the new refresh token, and version your scopes so you can migrate users safely.
How do you fix a Google Chat OAuth token expired error step-by-step?
The fastest fix is a 7-step workflow: capture the exact error, confirm which token failed, verify consent screen status, re-authorize if needed, repair token storage, implement refresh-and-retry logic, and validate with controlled tests against the Google Chat API.

Let’s explore the steps in the same order your integration actually executes them.
Step 1: What is the exact error and where does it occur in the flow?
The exact error text and the failing step (API call vs token refresh exchange) determines whether you should refresh, re-authorize, or fix configuration.
Next, separate the two failure zones:
- Zone A (API call): Google Chat endpoint returns 401/403 because the access token is expired/invalid.
- Zone B (token refresh): token endpoint returns invalid_grant because the refresh token is expired/revoked/invalid.
Step 2: Are you storing tokens correctly and securely?
You fix recurring “expired” errors by storing the refresh token durably and storing the access token’s expiry metadata accurately, so your app can refresh before making a Chat request.
Then, apply storage rules that prevent silent corruption:
- Persist refresh tokens in a durable store (not in-memory only).
- Encrypt at rest and restrict access to the minimum runtime component.
- Store token records keyed by user + workspace/domain + environment to prevent cross-tenant mix-ups.
Step 3: If refresh fails, should you re-authorize the user immediately?
Yes—if the refresh exchange returns invalid_grant, you should re-authorize immediately because retries will not resurrect a revoked/expired refresh token.
However, do it cleanly: show a clear “Reconnect Google Chat” action, explain that access expired, and avoid forcing re-consent loops if the real issue is misconfiguration.
Step 4: Are you using a safe retry pattern for Chat API calls?
Yes—use a single refresh attempt plus a single retry of the original request, because repeated refresh calls can create rate-limit pressure and confusing logs.
Next, apply a strict rule set:
- On 401: refresh once, retry once, then fail with a “Reconnect” path if it still fails.
- On 403: do not blindly refresh; first verify scopes and permissions.
- On repeated failures: open a circuit breaker to prevent hammering the token endpoint.
Step 5: Are you validating with a controlled test user and fresh consent?
Yes—controlled validation isolates token lifecycle issues from unrelated integration bugs.
Then, test with a single user account you can re-consent quickly, and confirm that the integration survives an access-token expiry window by refreshing automatically without human action.
According to a study by The Chinese University of Hong Kong from the Department of Information Engineering, in 2016, researchers tested OAuth-based deployments across hundreds of top-ranked websites and found that implementation mistakes are common and can create real security and reliability failures—so validating your implementation under controlled conditions is not optional for production integrations.
Should you switch from user OAuth to service accounts or domain-wide delegation for Google Chat?
User OAuth is best for user-scoped actions in Google Chat, while domain-wide delegation (where allowed by your environment and policies) can be better for admin-approved, organization-wide automation—so the right choice depends on whether you need per-user consent or centralized admin control.

However, the crucial link to your “token expired” problem is this: the more your integration depends on individual user consent and tokens, the more you must handle churn, revocation, and re-authorization gracefully.
Is user OAuth the best choice for posting messages “as the user” in Google Chat?
Yes—user OAuth is the best choice when you need actions tied to a specific user identity, because it aligns permissions with that user’s consent and provides an auditable, user-scoped authorization model.
Next, match this to typical Chat use cases:
- Posting messages that should reflect a user’s permissions and access level.
- Reading space membership or messages only where the user has access.
- Integrations that must respect per-user opt-in and opt-out.
Is a centralized “bot-style” integration better for reducing token churn?
Yes, a centralized integration can reduce churn because it minimizes the number of unique token holders, but it increases the importance of administrative governance and secure storage since one credential becomes highly privileged.
Then, evaluate the operational trade-off:
- Fewer tokens to rotate and monitor.
- Clearer ownership (admin-managed) and better continuity when employees leave.
- Higher blast radius if credentials are mishandled.
Comparison: Which approach fits “developers building automated workflows” best?
User OAuth wins in fine-grained, user-specific permissions, while centralized automation wins in operational stability and reduced per-user reconnection work, and a hybrid approach is optimal when you need both.
Meanwhile, your choice should be guided by three criteria:
- Identity requirement: must the action be attributable to a user, or can it be attributed to a bot/app?
- Governance: can admins approve and manage the integration centrally?
- Lifecycle cost: how expensive is it for users to reconnect when tokens expire or are revoked?
Does formal OAuth research suggest you should avoid weaker patterns?
Yes—research on OAuth has repeatedly shown that incorrect flows and sloppy validation cause vulnerabilities, so you should prefer modern best practices (such as strong redirect validation and safer flows) rather than “quick fixes” that bypass consent or weaken checks.
According to a study by the University of Trier from its academic security research work, in 2016, researchers formally analyzed OAuth 2.0 and identified multiple practical attacks when best practices are not followed, reinforcing that “making it work” must not come at the cost of weakening the authorization model.
How do you prevent Google Chat OAuth token expired errors from happening again?
You prevent recurring Google Chat OAuth token expired errors by implementing proactive refresh, resilient retries, clear re-authorization UX, token hygiene (rotation and revocation handling), and monitoring that distinguishes auth failures from API and webhook failures.

Next, turn prevention into specific engineering controls you can ship and measure.
What token lifecycle rules should your integration enforce?
Your integration should enforce rules that refresh early, retry safely, and fail loudly with a re-connect path when refresh is impossible.
Specifically, implement the following:
- Early refresh: refresh before expiry to avoid race conditions.
- Single refresh attempt on 401: refresh once, retry once.
- Cache discipline: never share tokens across users or tenants.
- Scope versioning: treat scope changes as a breaking change requiring re-consent.
How do you monitor and alert on token failures without drowning in noise?
You monitor token failures by tracking a few high-signal metrics that pinpoint whether the failure is access-token expiry, refresh-token invalidation, or misconfiguration.
Then, instrument these counters:
- 401 rate on Google Chat API calls (by endpoint, by tenant).
- invalid_grant rate on token refresh exchanges (by OAuth client, by environment).
- Re-auth success rate .
- Time-to-recover .
How do you build a user-friendly reconnect experience?
You build a user-friendly reconnect experience by explaining what happened, preserving context, and making reconnection a single-click action rather than a support ticket.
Next, include practical UX details:
- Show which workspace/space is affected and what the integration was trying to do.
- Explain the exact action: “Reconnect Google Chat to restore permission.”
- After reconnect, re-run the failed job once (idempotently) and confirm success.
How do you reduce “expired token” incidents caused by deployment and configuration changes?
You reduce incidents by treating OAuth settings as versioned infrastructure: validate redirect URIs, keep dev/staging/prod isolated, and automate configuration checks in CI/CD.
Then, harden operations with a checklist:
- Lock down redirect URIs and disallow wildcards unless strictly required.
- Ensure server time is synchronized to a reliable source to avoid skew-based failures.
- Keep separate OAuth clients per environment to avoid token cross-contamination.
Contextual border: up to this point, you have the complete “fix + prevent” playbook for the primary intent (expired/invalid tokens). Next, the content expands into closely related Google Chat failures that often masquerade as OAuth expiration in logs and dashboards.
What other Google Chat auth and webhook issues look similar to OAuth token expired (401 vs 403 vs 429)?
Several issues can look like “token expired” in practice—especially 401 unauthorized webhooks, permission-related 403 responses, and rate-limited 429 bursts—so you should classify the failure by HTTP code, endpoint type (API vs webhook), and whether the failure happens before or after token refresh.

Below are the most common “look-alikes” and how to separate them fast.
Is “google chat webhook 401 unauthorized” always an OAuth token problem?
No—google chat webhook 401 unauthorized often indicates a signature/verification or audience mismatch in the webhook delivery pipeline, not necessarily an OAuth token issue.
However, it can still be auth-adjacent: if your webhook handler calls back into Google Chat using a bad access token, the downstream call may return 401 even though the webhook itself arrived correctly.
- Webhook-layer 401: verify endpoint verification, headers, and identity expectations.
- Callback-layer 401: verify access token freshness and refresh logic.
Why does “google chat trigger not firing” get mistaken for token expiry?
google chat trigger not firing is commonly mistaken for token expiry because the visible symptom is “nothing happens,” but the root cause may be event configuration, permissions, or delivery failures rather than token lifecycle.
Next, separate “no event delivered” from “event delivered but action failed”:
- No event delivered: check subscription/configuration, filters, and whether the event source is enabled.
- Event delivered but action failed: check your handler logs for auth errors, including token refresh failures.
Comparison: How do you distinguish OAuth failures from rate limits and platform errors?
OAuth failures usually produce consistent 401/invalid_grant patterns tied to token age or consent state, while rate limits produce 429 bursts tied to volume, and platform errors produce 5xx responses that correlate with service incidents rather than your token store.
Meanwhile, use a practical decision rule:
- 401 + refresh succeeds: access token expiry handled correctly.
- 401 + refresh fails (invalid_grant): refresh token invalid → reconnect required.
- 429: throttle/backoff; do not re-authorize.
- 5xx: retry with exponential backoff; do not rotate tokens.
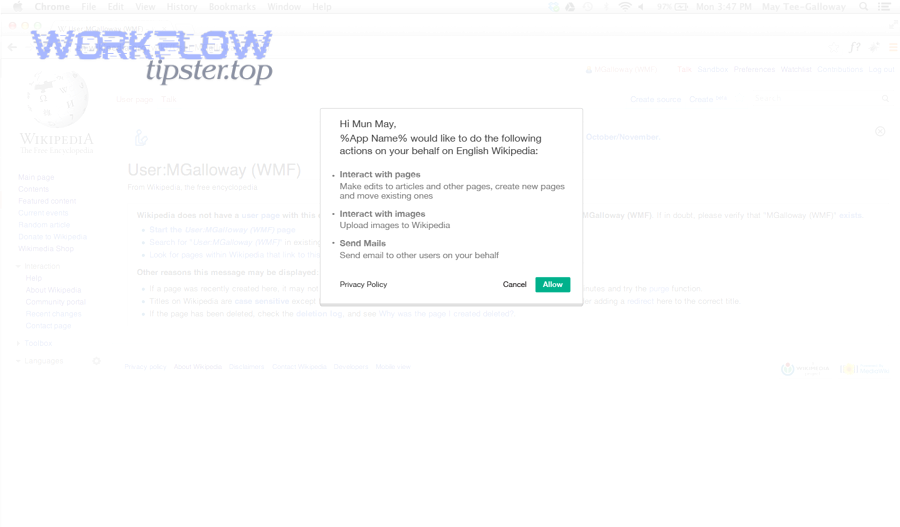
How can Workflow Tipster-style runbooks speed up Google Chat troubleshooting?
A Workflow Tipster-style runbook speeds up resolution by turning confusing symptoms into a short checklist: identify the failing zone, classify the HTTP code, verify token freshness, and only then escalate to consent or configuration changes.
Next, if you operationalize that runbook, your team stops “reconnecting users” as the default response and instead fixes the actual failure mode—OAuth lifecycle, webhook verification, event delivery, or rate-limit handling—on the first pass.

