If you want to automate (not manual) eSignature document signing with Airtable → Google Docs → Box → Dropbox Sign, you can build a dependable workflow that generates a contract from record data, stores the file in Box, sends it to the right signer in Dropbox Sign, and writes signing status back to Airtable—without writing code.
The first priority is getting the minimum reliable setup right: the Airtable base must hold clean “source-of-truth” fields, the Google Docs template must be structured for mapping, Box must enforce consistent access, and Dropbox Sign must have a repeatable request pattern that never duplicates sends.
Next, you’ll want a practical way to reduce mistakes that break automation workflows—like placeholder mismatches, file version confusion, or permissions that block Box uploads—so the system stays “Not Manual” even when volume increases.
Introduce a new idea: once the core workflow is stable, you can layer in advanced controls—like conditional signer routing, webhook-based status updates, and governance policies—so the same automation can support both lightweight operations and compliance-heavy teams.
Is it possible to automate document signing from Airtable → Google Docs → Box → Dropbox Sign without coding?
Yes—airtable to google docs to box to dropbox sign document signing can be automated without coding because no-code connectors can (1) map Airtable fields into a Google Docs template, (2) store and permission the file in Box, and (3) send and track a Dropbox Sign signature request end-to-end.
To better understand why “Not Manual” is realistic, let’s explore what you must set up so the workflow behaves predictably every time.

What are the minimum requirements to make the workflow reliable?
A reliable workflow needs four non-negotiables: a clean Airtable schema, a stable Google Docs template, a controlled Box destination, and a deterministic Dropbox Sign sending pattern.
Start with Airtable as the system of record. At minimum, each “send for signature” record should store:
- Signer identity fields: full name, email, optional phone (if you later add SMS verification)
- Document variables: contract type, pricing/terms, effective date, address, identifiers
- Workflow control fields: status (Draft → Ready → Sent → Signed), lock flags, request ID
- File tracking fields: draft doc link, PDF link, Box file ID, signed PDF link
Then your Google Docs template must be “merge-ready.” That means you design predictable placeholders (like {{ClientName}}) and you avoid layouts that break when text expands (for example, inline placeholders inside tightly constrained table cells).
On the storage side, Box must have a destination folder strategy that answers two questions: Where is the authoritative version stored? and Who is allowed to see it before it’s signed? This avoids the silent failure mode where the automation “runs,” but users can’t access the result.
Finally, Dropbox Sign must be set up so sending can be repeated safely. The core rule is simple: every record should send at most one active signature request unless a controlled “resend” path is used.
When should you keep steps manual instead of automated?
Automation wins when the process is repeatable, but manual steps still make sense for exceptions—especially when legal review or custom negotiation changes document content in unpredictable ways.
A practical comparison looks like this:
- Automate (Not Manual) when the document is template-driven (NDA, onboarding form, standard agreement), signer routing is predictable, and the business cares about speed and traceability.
- Keep manual control when the contract is heavily negotiated, the signer list changes midstream, or attachments vary per deal in a way that would require frequent template redesign.
In other words, “Not Manual” should be your default for volume and repeatability, while manual should be your controlled exception path for high-variance documents.
What does an “end-to-end eSignature document signing workflow” mean in this tool chain?
An end-to-end eSignature document signing workflow is a repeatable, trackable process that starts from Airtable data, generates a document in Google Docs, stores it in Box, sends it via Dropbox Sign, and updates Airtable with status and signed outputs.
Next, let’s connect that definition to the exact lifecycle stages you must design so every step has a clear owner and a clear outcome.

Which data should live in Airtable to support document generation and signing?
Keep Airtable focused on structured, queryable truth—not long-form document content. The best rule is: if you need it to appear in the contract, it should exist as a field.
A strong field design typically includes:
- Record identifiers: contract ID, customer ID, internal reference
- Parties: signer name/email, counterparty name, internal owner
- Commercial terms: price, term length, renewal, effective date
- Operational terms: delivery scope, service level option, region
- Control flags: “Ready to send,” “Approved,” “Needs changes,” “Sent timestamp”
- Status timeline: Sent, Viewed, Signed, Declined, Expired
This structure matters because it turns Airtable into a workflow engine: every downstream step can be triggered from a precise status change, not from human memory.
What are the most common failure points in this workflow?
The most common failure points are template mismatch, file conversion issues, storage permissions, and missing status updates—and they usually come from one root cause: the workflow depends on an assumption that isn’t enforced by the system.
Typical breakdowns include:
- Placeholder mismatch: Google Docs expects
{{StartDate}}, Airtable field isStart Dateand mapping breaks - Empty fields: required variables (like address or signer email) are blank
- Wrong output type: a signature request needs a PDF, but you send a Docs link
- Box permission denial: the automation account can’t upload or share the file
- Status sync failure: the signature is completed, but Airtable never updates because the sync step is missing or misconfigured
To avoid these, treat every assumption as a validation rule: required fields must be required, file locations must be deterministic, and status transitions must be explicit.
How do you design the Airtable base so document signing can be automated cleanly?
You design the Airtable base cleanly by separating “source-of-truth data” from “workflow status,” standardizing signer records, and enforcing send-safe rules that prevent duplicates and missing fields.
Then, you make the design operational by deciding which fields humans can edit and which fields automation controls.

Which fields should be treated as “source of truth” vs “derived status”?
Source-of-truth fields are values that humans intentionally set because they represent business reality. Examples: signer email, contract start date, contract value, company name.
Derived status fields are values produced by the workflow to record what happened. Examples: “Sent at,” “Signed at,” “Dropbox Sign request ID,” “Box file ID,” “Signed PDF URL.”
The reason this separation matters is simple: if users can freely change derived status fields, the automation becomes unstable. If the workflow can overwrite source-of-truth fields, trust collapses.
A practical rule is:
- Humans edit source-of-truth fields before sending
- Automation writes derived status fields during and after sending
- A “lock” field prevents edits after the send step (except through a controlled revision workflow)
How do you prevent duplicate signature requests from the same record?
Duplicate sends usually happen when the workflow re-runs due to a retry, a user clicking “send” twice, or multiple triggers firing.
To stop this, implement a send-once contract:
- Add a field like
Signature Request ID(blank until first send). - Before sending, the automation checks: Is Request ID blank?
- If blank, send and write Request ID immediately.
- If not blank, block sending unless a controlled “Resend” flag is explicitly set.
Add a second guard: store a Send Hash (for example, signer email + record ID + template version). If the hash changes, you know the contract changed, and a new send may be valid.
This one design decision is what keeps your workflow “Not Manual” at scale—because you remove the need for humans to notice duplicates after damage is done.
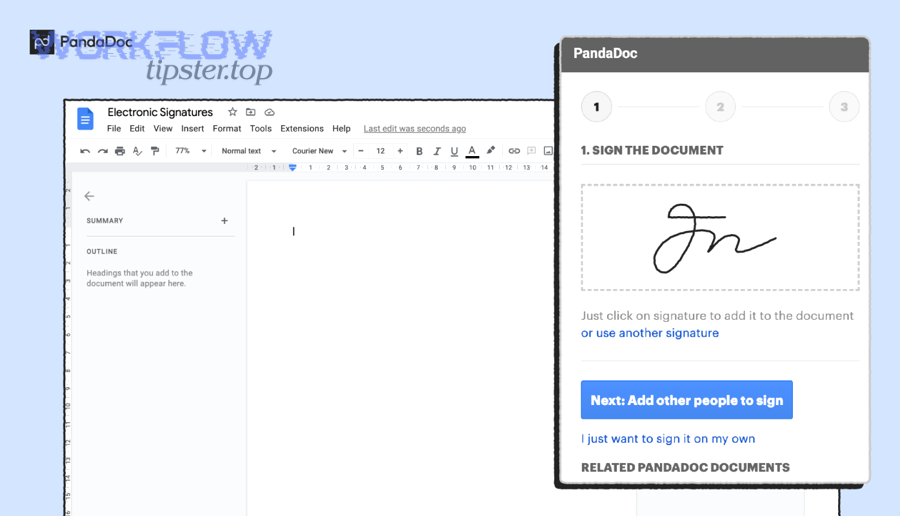
How do you generate a Google Docs document from Airtable data the right way?
Generate the Google Docs document the right way by using a stable template, mapping fields consistently, exporting a signature-ready PDF, and storing the result with a versioned name that ties back to the Airtable record.
To illustrate, the key is treating document generation as a repeatable manufacturing process, not a one-off craft task.

What is the best way to structure placeholders so mapping doesn’t break?
The best placeholder structure is predictable, unique, and formatting-safe.
Use these rules:
- Use a single placeholder style everywhere, e.g.
{{ClientName}}, not mixed styles - Keep placeholders case-consistent and avoid spaces inside braces
- For numeric fields, decide formatting rules early (currency, decimals)
- For dates, store a canonical date in Airtable and format it consistently on output
- Avoid placeholders in fragile layout zones (tight columns, tiny table cells)
A useful pattern is to keep a “Template Variables” table in Airtable listing:
- Placeholder name (e.g.,
ClientName) - Airtable field source (e.g.,
Company Name) - Required? (Yes/No)
- Example value (to test template rendering)
This makes template maintenance a controlled system instead of tribal knowledge.
Should you send the signature request on a Google Doc or a PDF export?
PDF export is typically best for signing consistency, while a Google Doc can be best for collaborative drafting before signing.
Here’s the practical comparison:
- PDF export wins when you want a fixed layout, predictable rendering, and a clear “final document” artifact for storage and audit.
- Google Doc wins during drafting because multiple stakeholders can edit and comment, and the latest version stays centralized.
For most teams, the stable approach is: draft in Docs → export to PDF → sign the PDF → store signed PDF in Box → link signed PDF back to Airtable.
This is also where “airtable to google docs to box to docusign document signing” is conceptually similar: the key difference is the eSignature provider, while the document manufacturing logic remains the same.
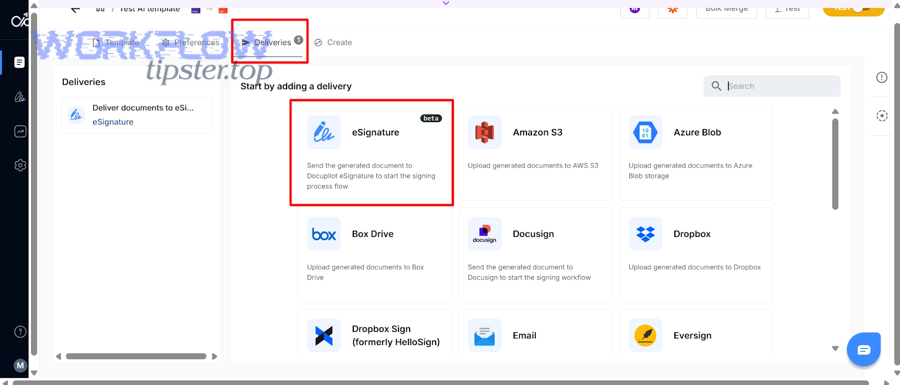
How do you store and manage the document in Box before and after signing?
Store and manage documents in Box by using a consistent folder taxonomy, controlled permissions, and a clear “draft vs final” file lifecycle so the signed PDF becomes the authoritative version.
Next, we’ll connect storage decisions directly to workflow reliability—because file chaos is one of the fastest ways to turn automation back into manual cleanup.
Which Box folder structure reduces confusion for No-Code Ops teams?
A low-confusion structure is one that answers “where do I find it?” in one click.
A simple model is:
/Customers/{CustomerName}/Agreements//Drafts//Signed//Supporting Docs/
Then standardize file naming, for example:
{ContractID} - {ContractType} - {CustomerName} - {YYYY-MM-DD}.pdf
This naming scheme creates three benefits:
- Searchability in Box
- Easy reconciliation with Airtable records
- Clear separation of drafts and finals
If you want to add more structure, do it with a single dimension (like year) rather than adding multiple nested categories that people won’t follow consistently.
How do you ensure the signed version becomes the “final” version in Box?
You ensure “final” status by making one storage rule non-negotiable: only one file location is considered final, and automation always updates it the same way.
Two common patterns:
- Replace pattern: signed PDF replaces the draft PDF (same filename, new version)
- Best when you want a single canonical file that always stays in one place
- Append pattern: signed PDF is saved as a new file in
/Signed/- Best when you want a clear separation and an immutable final artifact
Most compliance-aware teams choose the append pattern because it preserves an immutable signed copy while leaving the draft trail intact.
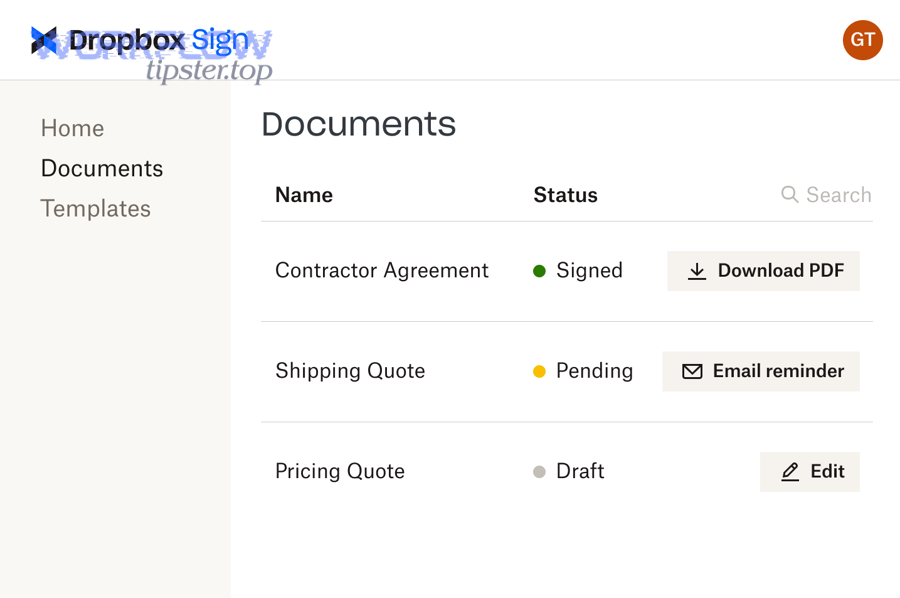
How do you send the document for signature in Dropbox Sign and track status back in Airtable?
Send the document for signature by creating one signature request per Airtable record, assigning correct roles and signing order, and writing request IDs plus status events back into Airtable so the record becomes your live tracking dashboard.
Then, you decide how “real-time” you need status tracking to be, because that choice changes the architecture.
What signing roles and routing options should you use (signer, CC, approver)?
You should choose roles based on who must act versus who must be informed.
Common patterns include:
- Single signer: one external party signs, internal team receives a copy
- Two-party signing: internal signer signs first (or second), then external signer
- Approval then signature: internal approver reviews first, signer executes second
- CC recipients: stakeholders receive final copies without being blockers
A practical routing rule is: minimize the number of people who must take an action, because every additional required signer increases cycle time and decreases completion rate.
If you have a “legal review” step, separate it from signing. Legal review is a gate, not a signer role, and treating it as a signer often introduces delays and confusion.
Should status updates use webhooks or scheduled checks?
Webhooks are best for near-real-time tracking, while scheduled checks are best for simpler setups that still need reliable updates.
- Webhook approach: Dropbox Sign sends an event when status changes; automation updates Airtable immediately.
- Pros: fast, reactive, fewer “status drift” issues
- Cons: requires careful configuration and a stable endpoint (or a platform that handles webhooks well)
- Scheduled checks (polling): a scheduled automation queries request status every X minutes/hours.
- Pros: easier to implement, resilient when webhooks are difficult
- Cons: delays updates and may increase API usage
If your operations team depends on status accuracy (e.g., “signed today triggers onboarding”), webhooks are usually worth the effort.
What is the simplest step-by-step automation blueprint for this workflow?
The simplest blueprint is a 7-step method—validate record → generate document → export PDF → store in Box → send via Dropbox Sign → write status back → archive signed PDF—so you get a repeatable signing outcome with minimal human touch.
Below is a concrete workflow you can implement with common no-code tools while keeping each step testable and reversible.

This table summarizes what each step does and what the output should be stored in Airtable:
| Step | Action | Output you should store in Airtable |
|---|---|---|
| 1 | Validate required fields | “Ready to Send” = true or error message |
| 2 | Create Google Doc from template | Draft doc link |
| 3 | Export to PDF | Draft PDF link |
| 4 | Upload PDF to Box | Box file ID + Box link |
| 5 | Send signature request in Dropbox Sign | Signature request ID |
| 6 | Track status updates | Status + timestamps |
| 7 | Save signed PDF back to Box | Signed PDF link + final status |
Now make it operational with two important principles:
- Write critical IDs immediately (Box file ID, signature request ID) so retries won’t duplicate work
- Lock the record after sending so edits don’t invalidate the signed document
Also, keep a “Manual Override” path: if something breaks, a human can set status back to Draft, fix the source fields, and re-run safely.
Which trigger is best: button-driven, schedule-based, or event-driven?
Button-driven triggers win for control, schedule-based triggers win for batching, and event-driven triggers win for speed.
- Button-driven is best for early adoption because it prevents accidental sends and lets humans confirm readiness.
- Schedule-based is best for back-office batches (e.g., send renewal agreements nightly).
- Event-driven is best for high-velocity pipelines but needs strong safeguards to prevent duplicates.
A useful analogy is other automation workflows: just like calendly to outlook calendar to zoom to asana scheduling works best when the calendar event rules are clear, document signing works best when record readiness rules are enforced before triggers fire.
What notifications should be added so humans only handle exceptions?
Add notifications that tell humans only when their judgment is needed.
The highest value notifications are:
- Validation failed (missing signer email, missing template version, missing price)
- Upload failed (Box permission or folder not found)
- Send failed (Dropbox Sign request rejected)
- Stuck in Viewed for too long (send reminder or escalate)
- Declined (route to revision workflow)
This keeps the system “Not Manual” because people stop checking dashboards and only respond to exceptions.
How do you troubleshoot when the workflow fails or produces the wrong output?
Troubleshoot by isolating the failing step, verifying inputs and permissions, and re-running safely using stored IDs so you don’t create duplicates or lose audit history.
More specifically, you should treat troubleshooting as a controlled diagnostic sequence, not a guessing game.
Why does the document generate with missing or incorrect fields?
Missing or incorrect fields usually come from template-variable misalignment rather than “random errors.”
Check these in order:
- Are required Airtable fields actually populated? A blank “Company Name” becomes a blank
{{ClientName}}. - Does the placeholder name exactly match the mapped variable?
{{StartDate}}≠{{Start Date}}. - Is the field formatting consistent with the template expectation? Currency fields should not contain extra text like “USD $”.
- Did the workflow pull the correct record? Triggers that fire from linked tables can sometimes reference a related record by mistake.
Fixing this becomes straightforward if you maintain a “Template Variables” reference and enforce required fields before generation.
Why does the signature request send but Airtable never updates?
When sending works but status tracking fails, the usual causes are missing request IDs, broken webhook/poll configuration, or field-type mismatch in Airtable.
Diagnose it like this:
- Confirm Airtable stored the signature request ID immediately after sending.
- Confirm the status update step can read that ID and query the request.
- Confirm status fields in Airtable accept the data type you write (single select vs text vs date).
- Confirm your automation has permission to update Airtable and is targeting the correct record.
If you use webhooks, also confirm the receiving system is reachable and is not dropping events.
According to a press release by Ruhr-Universität Bochum from the Horst Görtz Institute for IT Security, in 2020, researchers showed that content in digitally signed PDFs can still be changed unnoticed in many programs, which is why version control and “final artifact” storage are essential in signing workflows. (news.rub.de)
What advanced options make this eSignature workflow more secure and less manual in edge cases?
There are 4 advanced options that make this workflow more secure and less manual: (1) conditional routing, (2) webhook-first status tracking, (3) governance controls for retention and audit, and (4) duplicate-proof design with version locking—so edge cases don’t force humans to rebuild the process each time.
Moreover, these options matter because the “Not Manual” promise only holds if the workflow survives unusual inputs, strict policies, and high volume.
What is the difference between electronic signatures and digital signatures in real workflows?
Electronic signatures are a broad category of intent-to-sign methods (typed name, click-to-sign, drawn signature), while digital signatures are a specific cryptographic method designed to prove integrity and authenticity.
Operationally:
- eSignatures are often enough for standard agreements and faster completion
- digital signatures are used when cryptographic validation and integrity assurance are required
According to a study by the University of New South Wales from the School of Psychology, in 2020, digitally signed documents were perceived as conveying less social presence than handwritten signatures, which influenced trust-related judgments—so teams should pair digital convenience with clear identity and audit signals in signing flows. (researchgate.net)
How can you add conditional signer routing (if/then approvers) without breaking reliability?
Conditional routing works when you treat routing rules as data, not hard-coded logic.
A reliable approach is:
- Store routing conditions in Airtable fields (e.g.,
Contract Value,Region,Needs Legal Review) - Use explicit branches:
- If value > threshold → internal approval step → then external signature
- Else → direct external signature
To keep it stable:
- Write a “Routing Version” field so you know which logic path was used
- Always record the final signer list before sending
- Lock routing fields once the request is sent
This prevents midstream edits that create “mystery behavior.”
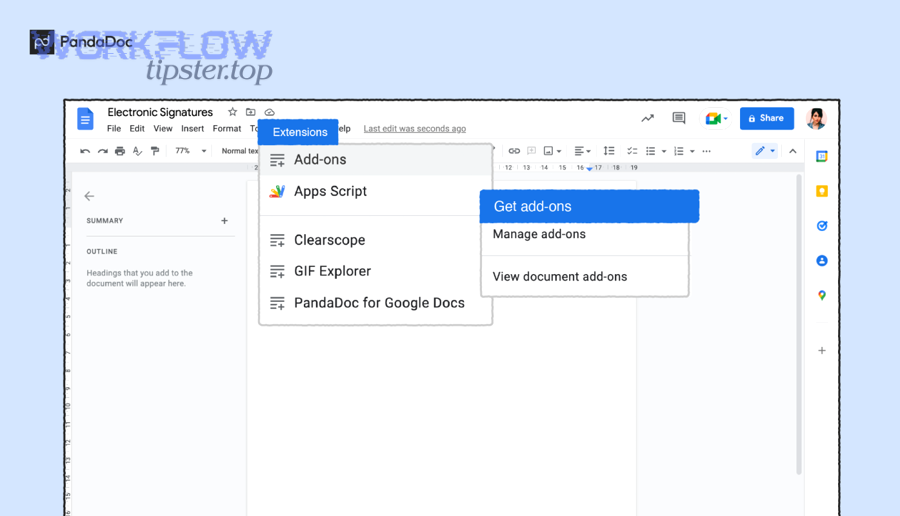
Which approach is better for teams: native features or an automation platform like Zapier / Make?
Native features win in simplicity, an automation platform wins in flexibility, and a hybrid approach is optimal for scaling teams.
- Native is best when you can do everything inside one ecosystem with limited branching and minimal transformation.
- Automation platforms are best when you need multi-step logic, branching, retries, and cross-tool logging.
- Hybrid is best when core steps are native but exceptions are handled by automation.
This is the same strategic decision teams face when building automation workflows across different domains: you keep simple flows native, and you use orchestration when complexity grows.
What rare governance controls matter for regulated teams (audit trail export, retention, signer authentication)?
Regulated teams care about controls that typical teams don’t think about until an audit happens.
The most important rare controls include:
- Audit trail export: prove who signed, when, and what version was signed
- Retention rules: keep signed documents for required durations and apply legal holds
- Signer authentication: stronger identity verification where appropriate
- Version locking: ensure the signed PDF is stored as an immutable final artifact
- Access review: restrict who can view drafts vs signed copies
According to a report by San Francisco State University’s Quality Assurance team (California State University system), in 2020, selected electronic signature use cases reduced average turnaround time by 73% versus manual processes, with 78% of transactions completed in under one week—showing why governance plus automation can improve both speed and consistency. (calstate.edu)

