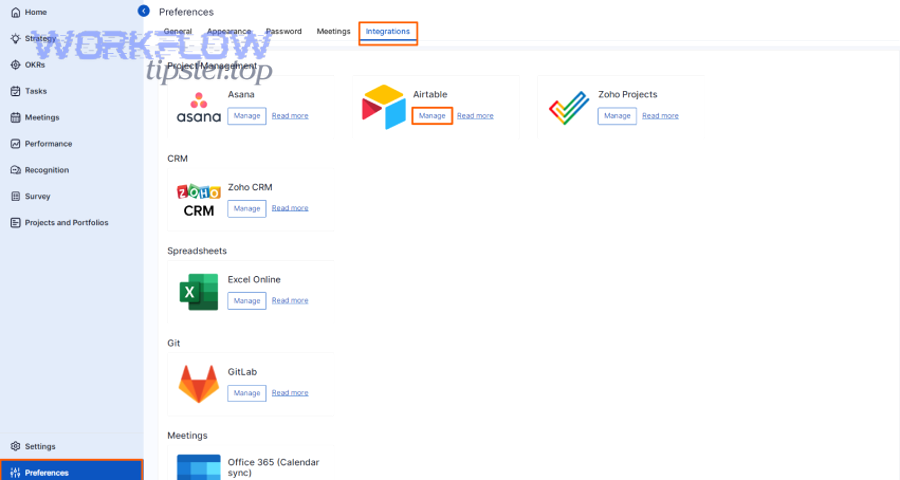
To connect Airtable to GitLab, you set up an integration that links Airtable records to GitLab work items (especially issues) and optionally logs commits, so updates flow automatically instead of being copied by hand.
Next, you’ll choose whether you need simple one-way automation (Airtable creates GitLab issues) or true sync (GitLab updates also change Airtable records), because that choice determines your tooling, data model, and maintenance effort.
Then, you’ll design the right method—Zapier/Make for quick no-code workflows, n8n for controlled engineering-grade automation, Unito-style two-way sync when you need bi-directional updates, or GitLab webhooks/API for custom behavior.
Introduce a new idea: once the integration path is clear, you can structure your Airtable base, select GitLab triggers, map stable identifiers, and add security plus troubleshooting practices so the workflow stays reliable as your team and volume grow.
What does it mean to “connect Airtable to GitLab” for dev teams (integration vs sync)?
Connecting Airtable to GitLab is the practice of linking Airtable records (a lightweight database) with GitLab work objects (like issues and commits) so information is created, updated, and tracked automatically across both systems.
To better understand the difference, start by separating two concepts that teams often mix: integration and sync. An integration usually means one system triggers actions in another system, often one-way. A sync implies continuous reconciliation—updates in either system can reflect in the other, based on explicit rules. That distinction matters because it affects everything: how you design fields, how you prevent duplicates, and how you handle conflicts when two people update different places.

Is “integration” the same as “sync” in Airtable ↔ GitLab workflows?
No—“integration” and “sync” are related (they can be synonyms in casual speech), but in Airtable ↔ GitLab workflows, sync usually means bi-directional updates with conflict rules, while integration often means one-way automation with simpler ownership.
Specifically, most teams start with integration because it is easier to reason about. You might say, “When a new Airtable record enters the ‘Ready for Dev’ view, create a GitLab issue.” That is integration: a trigger plus an action. Sync adds an additional promise: when the GitLab issue changes (status, assignee, labels), Airtable updates too. The moment you promise bi-directional behavior, you must define what happens when two values disagree.
In practice, a safe mental model is:
- Integration = event-driven automation with a clear source of truth (often GitLab for engineering execution).
- Sync = ongoing data consistency between two systems, requiring rules for conflicts, missing events, and replays.
- Hybrid = one-way automation plus “read-back” updates for a few critical fields (commonly status and assignee).
Next, keep the terminology consistent in your team documentation: if the workflow is one-way, call it an integration. If you truly allow edits in both places, call it a sync and document conflict resolution.
Which GitLab items are most commonly connected to Airtable records (issues, commits, merge requests)?
There are three main GitLab items commonly connected to Airtable records: issues (work tracking), commits (activity logging), and merge requests (review and release control), based on how dev teams plan, execute, and report progress.
Then choose which objects you connect by starting with the question: “What decision will this data support?” Airtable excels at portfolio views, cross-team planning, and structured metadata. GitLab excels at execution, discussions, code, and lifecycle events.
- Issues: best for intake, triage, sprint planning, and tracking progress through statuses. Airtable records become “work requests” or “epics-lite,” while GitLab issues become the execution unit.
- Commits: best for activity traces. Teams log commits into Airtable when they need reporting like “Which client deliverables were touched this week?” or “Which features had code changes but no issue movement?”
- Merge requests: best for review gates and release readiness. Airtable can track review status, QA sign-off, and release checklist items tied to each merge request.
To begin, most teams should connect Airtable records to GitLab issues first, then add commits or merge requests only if you have a concrete reporting or compliance need.
Do you need Airtable ↔ GitLab integration, sync, or both?
Yes, you can benefit from Airtable ↔ GitLab automation, but you should choose integration, sync, or both based on three reasons: the direction your data needs to flow, how often fields change, and how much governance your team can maintain.
Moreover, the best choice is the one that reduces manual work without creating a “mystery machine” no one wants to own. A lightweight integration can eliminate copy-paste and keep stakeholders informed. A full sync can make dashboards trustworthy, but it also introduces conflict risk and requires careful mapping.
Use this quick decision framework:
- Choose one-way integration if you mainly want Airtable to create issues (or tasks) in GitLab and keep GitLab as the source of truth.
- Choose “integration + read-back” if you need GitLab status and assignee reflected in Airtable for reporting, but you do not want edits in Airtable to overwrite GitLab.
- Choose two-way sync if non-engineering stakeholders must safely update specific fields (like priority or due date) and those updates must reflect in GitLab with clear rules.
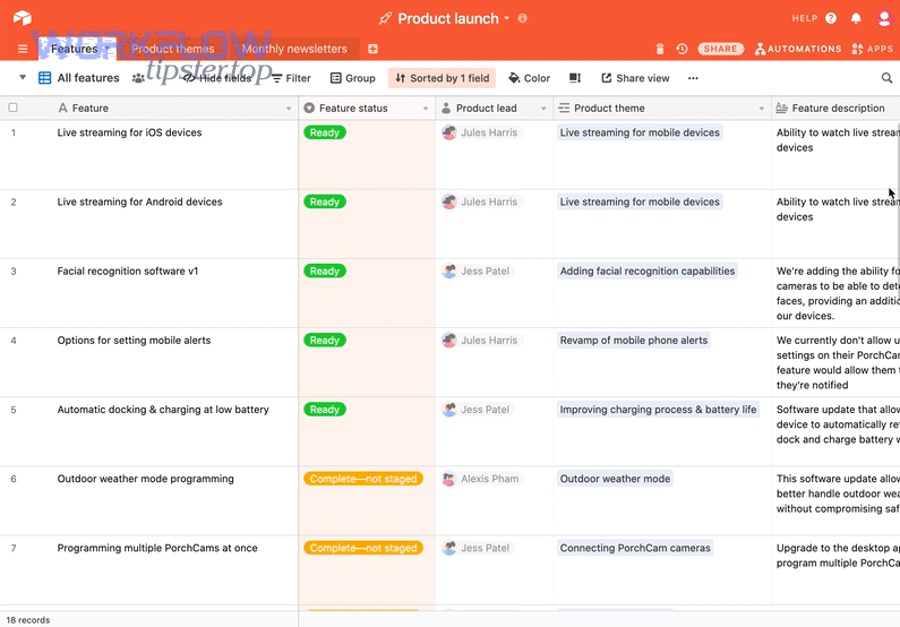
Do you want Airtable to create GitLab issues automatically?
Yes—Airtable can create GitLab issues automatically for at least three reasons: it standardizes intake, speeds up triage, and prevents work from being lost across chat threads or email.
Then, treat Airtable as your structured “request form” and GitLab as your execution system. The most important success factor is a clean minimum dataset so issues are created with enough context to be actionable.
A practical “minimum issue payload” from Airtable usually includes:
- Title (short and specific)
- Description (problem, expected outcome, acceptance criteria)
- Requester (name or team)
- Priority (single select) and Due date (optional)
- Labels mapped from Airtable categories
- Link back to the Airtable record URL for full context
To illustrate, a “Bug report” table in Airtable can feed GitLab issues with consistent templates, so developers start with the same structure every time.
Do you need GitLab updates to automatically update Airtable records?
Yes—GitLab updates can automatically update Airtable records for at least three reasons: stakeholders get real-time visibility, reporting becomes accurate, and status meetings shrink because dashboards reflect reality.
However, the most important decision is which fields should flow back from GitLab. Start small: status, assignee, and “last activity.” If you sync everything, you increase the odds of conflicts and noisy changes.
Typical “read-back” fields from GitLab into Airtable include:
- Issue state/status (opened/closed plus label-based workflow stage)
- Assignee (who owns execution)
- Milestone
- Labels (category, severity, team)
- Last updated timestamp for freshness checks
According to a study by the University of California, Irvine from the Department of Informatics, in 2008, interruptions and task switching increased stress and frustration even when people tried to compensate by working faster—an effect teams often see when they rely on manual status updates instead of dependable automation.
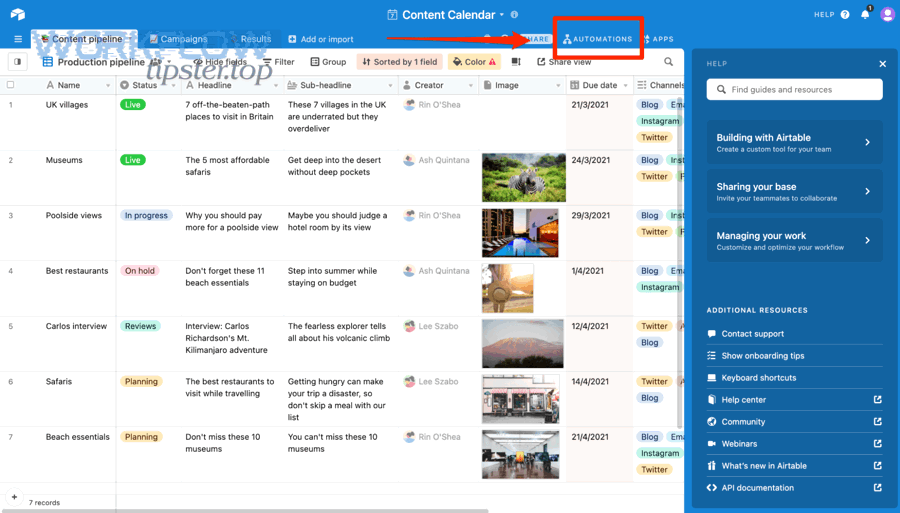
What are the best ways to connect Airtable to GitLab (Zapier, Make, n8n, Unito, or webhooks/API)?
Airtable ↔ GitLab connectivity has five main methods—Zapier, Make, n8n, two-way sync platforms (such as Unito-style tools), and custom GitLab webhooks/API—based on the criterion of speed-to-setup versus control and reliability.
Next, anchor your choice in the workflow you actually need. If your goal is “create an issue when a record changes,” a no-code tool is usually enough. If your goal is “maintain consistent records across two systems with conflict rules,” you’ll need either a dedicated sync tool or an engineered integration using webhooks and idempotency.
This table contains the most practical selection criteria and helps you choose a method that fits your team’s constraints.
| Method | Best for | Strength | Main risk |
|---|---|---|---|
| Zapier | Fast, template-driven automation | Speed and simplicity | Complex branching can get expensive or limited |
| Make | Visual multi-step scenarios | Flexible mapping and routing | Operational complexity if scenarios sprawl |
| n8n | Engineering-owned workflows | Control, self-hosting, custom logic | Requires maintenance and monitoring |
| Two-way sync platform | Bi-directional issue ↔ record sync | Purpose-built conflict handling | May limit customization beyond supported objects |
| GitLab Webhooks + API | Custom, scalable integrations | Maximum control and precision | Engineering time, reliability engineering required |

Which method is best for no-code automation (templates and quick setup)?
Zapier wins in speed-to-launch, Make is best for richer visual scenarios, and templates are optimal for teams that want results quickly without engineering effort.
Specifically, no-code is strongest when the workflow can be described as “When X happens, do Y, then notify Z.” It is also the simplest way to prototype before committing to a more engineered approach.
- Choose Zapier if you want a straightforward trigger/action flow and value quick setup.
- Choose Make if you expect multi-step routing (e.g., different projects based on category) and complex field mapping.
- Choose templates when you want common automations like “new record → create issue” or “new commit → create record” without designing from scratch.
Then, if your organization already uses Automation Integrations across apps, keep Airtable ↔ GitLab consistent with your existing conventions: naming, error notifications, and ownership.
Which method is best for two-way sync between records and issues?
A dedicated two-way sync platform wins for ongoing record ↔ issue consistency, while custom webhook/API sync is best when you need strict control over conflict rules and advanced mapping.
More specifically, two-way sync is not “more automation.” It is a data consistency promise. That means you must decide:
- Which fields are allowed to sync both ways (for example, priority and due date might be editable in Airtable, while status might be owned by GitLab).
- What happens on conflict (last-write-wins, GitLab-wins, Airtable-wins, or merge rules).
- How you detect stale records (timestamps and “last synced” fields).
If your team is also comparing other business automations such as airtable to freshbooks, the lesson is similar: bi-directional sync is powerful, but the governance cost is higher than one-way automation.
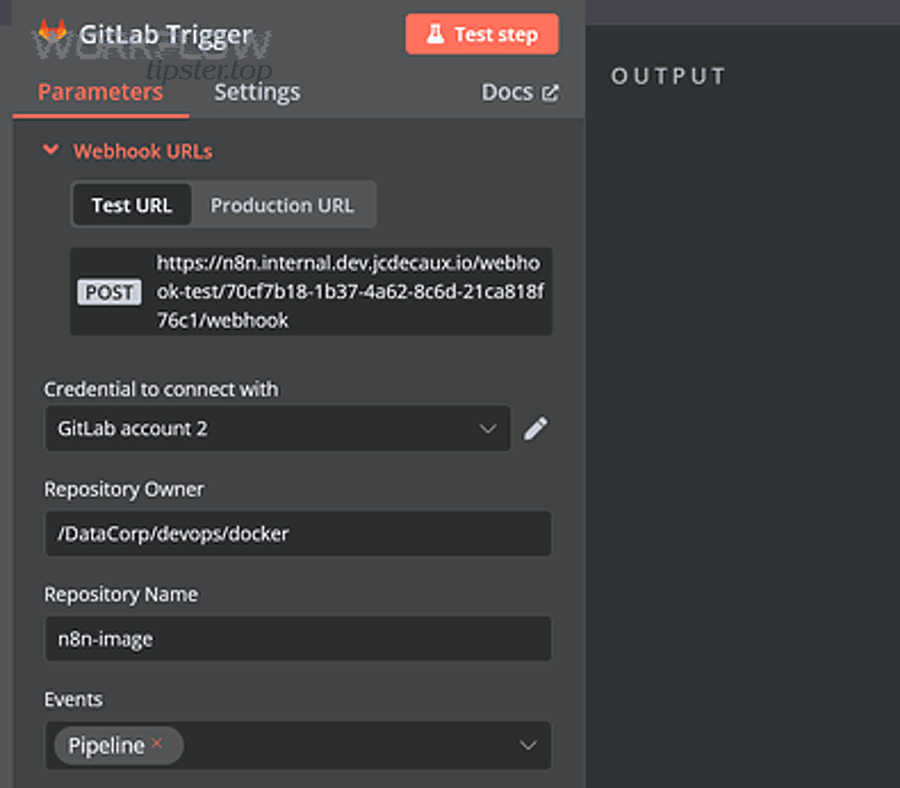
Which method is best for engineering teams that need control (self-hosted workflow + webhooks)?
n8n plus GitLab webhooks and the GitLab API is best for engineering teams because it offers at least three benefits: self-hosted control over data, programmable logic for edge cases, and reliability patterns like retries and idempotency.
Moreover, engineering-owned workflows become maintainable when you build them like software: version your workflows, add run logs, define error handling, and assign ownership. A self-hosted approach also helps when you must operate behind strict security policies or need consistent behavior across many projects.
Use a self-hosted workflow engine when you need to:
- Route events across many GitLab projects with consistent logic
- Enforce data standards (labels, titles, templates)
- Implement “upsert” behavior (update if exists, otherwise create)
- Support custom mapping (linked records, multiple tables, calculated fields)
In addition, if you already maintain cross-tool documentation flows like google docs to miro or clickup to google docs, an engineering-owned integration can keep your “source-of-truth” rules consistent across the whole stack.
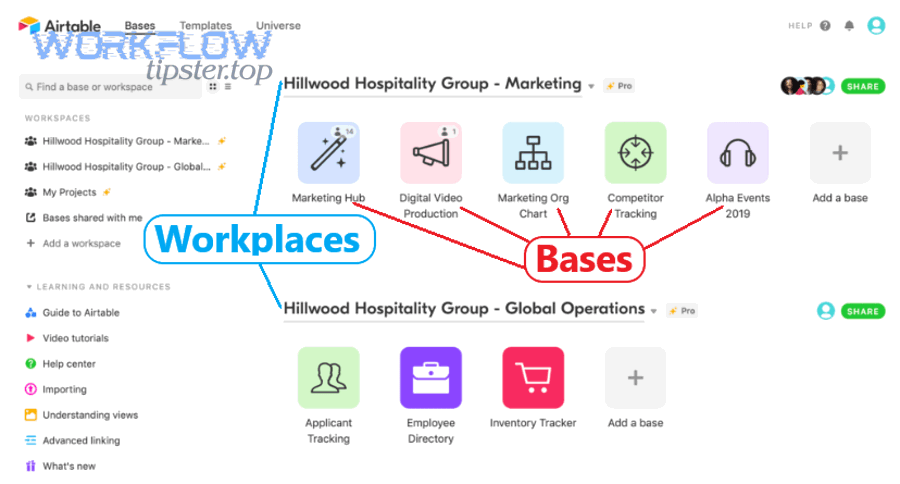
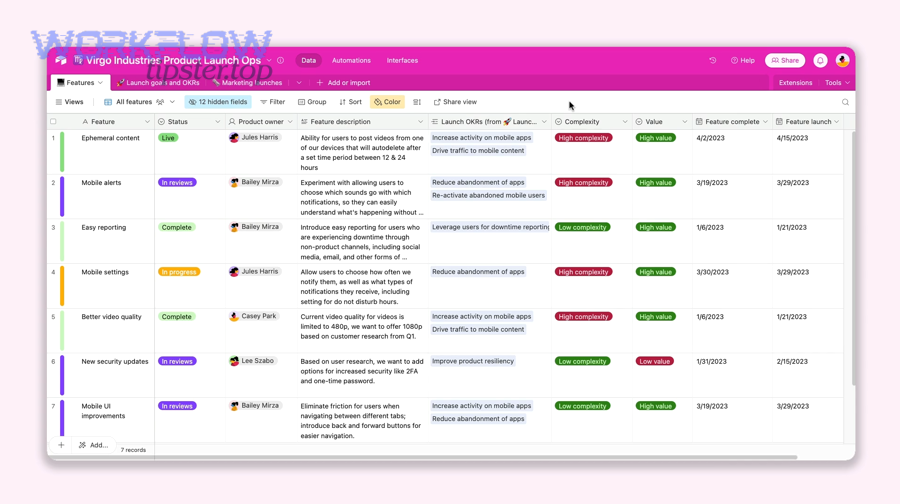
What should your Airtable base look like to track GitLab work correctly?
Your Airtable base should be a structured tracking system with clear tables, stable identifiers, and a defined status model, designed so GitLab issues map cleanly to records and dashboards stay trustworthy.
To begin, think in two layers: a “work request” layer that stakeholders understand, and an “execution” layer that maps precisely to GitLab. Airtable is excellent at relationships, so you can link projects, teams, and releases without forcing developers to manage those relationships manually in GitLab.
A typical base for dev teams includes:
- Requests (intake records that may become issues)
- GitLab Issues (or a single table where each record is an issue-backed item)
- Releases/Milestones (dates, scope, readiness)
- Owners/Teams (assignees, stakeholders, service areas)
Which Airtable fields should you create to map GitLab issues cleanly?
There are 10 core Airtable fields you should create to map GitLab issues cleanly: Issue IID, Issue URL, Project ID, Title, Description, Status, Assignee, Labels, Milestone, and Last Synced At, based on the criterion of stable linkage and reliable reporting.
Then add a few “integration health” fields so you can debug without guesswork:
- Source (Created in Airtable vs created in GitLab)
- Sync Direction (One-way, Read-back, Two-way)
- Sync Error (last error message, if any)
Finally, keep your “Issue URL” prominently visible. When stakeholders click through to GitLab, the integration earns trust because it reduces friction instead of adding another layer.
How should you model issue status in Airtable to avoid mismatches?
You should model issue status in Airtable as a canonical, limited set of stages mapped to GitLab states and/or labels, so every stage has a single meaning and dashboards do not contradict GitLab.
Specifically, GitLab’s basic state is often “opened/closed,” but real workflows use labels like “To Do,” “Doing,” “Blocked,” “In Review,” and “Done.” If you mirror every label, your Airtable status becomes noisy. Instead, define a small set of stages that represent decisions stakeholders care about.
A practical approach is:
- Airtable Stage: a single select with 6–8 stages max
- GitLab Mapping: one or more labels that correspond to each stage
- Rule: GitLab drives stage changes after the issue is created
Then, when GitLab labels change, your integration updates the Airtable Stage, keeping reporting aligned with execution.
What GitLab triggers and events should you use (issues, commits, merge requests, pipelines)?
There are four main GitLab event categories you should use—issue events, push/commit events, merge request events, and pipeline events—based on the criterion of what you want Airtable to track: work state, code activity, review gates, or release health.
Next, minimize event noise by starting with the smallest set of triggers that supports your reporting needs. If everything becomes an event, your Airtable base turns into a noisy log instead of an operational dashboard.
Which GitLab events are best to sync issue lifecycle updates back to Airtable?
There are three best GitLab event patterns to sync issue lifecycle updates back to Airtable: issue created/updated events, label changes, and assignment changes, based on the criterion of decision-relevant progress signals.
Then map each event to an Airtable field change that stakeholders recognize. For example:
- Issue state change → Airtable Stage becomes “Done” (or “Closed”)
- Assignee change → Airtable Owner updates
- Label change → Airtable Category/Team/Stage updates
To illustrate, if a developer adds a “Blocked” label in GitLab, Airtable can surface “Blocked” as a stage and automatically notify the stakeholder owner.
Which GitLab events are best to log commits in Airtable without duplicates?
There are two best GitLab commit logging strategies to avoid duplicates: log commits by unique commit SHA and filter by branch or path, based on the criterion of stable identity and meaningful signal.
More specifically, duplicates happen when the same commit appears in multiple event streams (rebases, merges, mirrored repositories). The fix is a stable key:
- Use commit SHA as the unique ID in Airtable.
- Upsert (update if SHA exists, otherwise create).
- Filter to only the branches you care about (often default branch) or only the repository paths linked to deliverables.
Then, if your team’s goal is stakeholder visibility rather than a full audit trail, consider logging only “deploy commits” or “release-tag commits” to keep Airtable actionable.
How do you map data between Airtable and GitLab so the workflow stays stable?
You map data between Airtable and GitLab by defining stable identifiers, consistent field transformations, and clear source-of-truth rules, so records and issues stay linked even when titles, labels, and owners change.
To better understand stability, focus on what changes frequently versus what should never change. Titles and descriptions evolve. Labels can be reorganized. People can change. Your workflow stays stable when the linking key and reconciliation logic do not depend on unstable fields.
Which identifiers should you store to link Airtable records to GitLab objects (Issue IID vs URL vs internal ID)?
Issue IID wins for human-friendly linking, internal ID is best for API precision, and URL is optimal for navigation, so the most stable practice is to store all three where possible: IID for display, internal ID for operations, and URL for usability.
Specifically, treat identifiers as layers:
- GitLab internal ID (best for API updates and unambiguous identity)
- Issue IID (best for humans and cross-references)
- Issue URL (best for click-through workflows)
Then, in Airtable, store these identifiers in dedicated fields and never overwrite them from user-edited fields. This approach prevents a common failure mode where a user accidentally edits a “link” field and breaks the integration.
How do you prevent duplicate issues or duplicate commit rows when automating?
You prevent duplicates by using at least three practices: upsert logic, idempotency keys, and a “lookup-before-create” step, so the integration updates existing objects instead of creating new ones repeatedly.
Moreover, duplicates are rarely caused by “bad tools.” They are usually caused by unclear uniqueness rules. Fix the rules and your automation becomes predictable.
- Upsert: if a record already has a GitLab issue ID, update that issue instead of creating a new one.
- Idempotency key: use a stable key (Issue internal ID, commit SHA) that never changes; store it in Airtable.
- Lookup-before-create: search GitLab by a unique signature (e.g., an Airtable record URL embedded in the issue description) before creating a new issue.
Then add a “Created By Integration” label in GitLab, so you can filter and audit what automation produced.
Can you connect Airtable to GitLab securely (tokens, permissions, and access control)?
Yes—you can connect Airtable to GitLab securely for at least three reasons: GitLab supports scoped access tokens, Airtable can restrict base permissions, and modern automation platforms support secret storage so credentials are not exposed to end users.
Next, security becomes much easier when you define ownership and boundaries. Decide who “owns” the integration (DevOps, platform engineering, or a designated ops admin), and document who can edit workflows, rotate tokens, and view run logs.
What permissions/scopes should you use for GitLab tokens to minimize risk?
You should use the minimum GitLab token permissions needed for your workflow, ideally limited to a single project or group and restricted to the exact actions required (create/update issues, read events), so a leaked token cannot escalate into broader access.
Specifically, apply the least-privilege checklist:
- Scope tokens to a project or group rather than personal, all-access tokens.
- Use read-only permissions where possible for “read-back” integrations.
- Rotate tokens regularly and after role changes.
- Store secrets in a secure vault or the automation tool’s secret manager, not in plain text fields.
Then, mirror the same discipline on the Airtable side: restrict who can edit the base schema and who can edit the “integration fields” that hold IDs and sync metadata.
Should you allow bi-directional edits, or keep GitLab as the source of truth?
GitLab wins as the source of truth for execution accuracy, Airtable is best for planning visibility, and a controlled hybrid is optimal for collaboration—so most dev teams should keep GitLab authoritative for status while allowing limited Airtable edits for priority or metadata.
However, if you let Airtable overwrite GitLab status freely, you create the risk of “dashboard-driven fiction,” where the dashboard looks good but the repo reality does not match.
A stable governance pattern is:
- GitLab owns: status, assignee, labels related to execution, links to code, merge request state.
- Airtable owns: stakeholder priority, business impact, portfolio grouping, optional due dates (if your team accepts them).
- Shared with rules: titles (optional), descriptions (optional), and tags only if you define strict mapping.
According to a study by The Ohio State University from the Graduate Program in Computer Science and Engineering, in 2014, empirical analysis in an enterprise setting found that Continuous Integration maturity correlated with fewer production defects and improved productivity—supporting the idea that stable automation and consistent workflows reduce downstream quality costs.
How do you troubleshoot common Airtable ↔ GitLab integration failures (missed updates, rate limits, mapping errors)?
You troubleshoot Airtable ↔ GitLab integration failures by checking three core areas first: trigger conditions, authentication/permissions, and data mapping, because most “missed updates” come from filters, token issues, or inconsistent field transforms.
Then move from symptom to root cause using a consistent checklist. This prevents a common problem: teams “fix” the workflow by adding more steps, which increases complexity while the root issue remains.
Start with these fast diagnostics:
- Did the event trigger? Check the integration run log and the Airtable view condition.
- Did GitLab accept the request? Look for HTTP errors (401/403 auth, 429 rate limiting, 5xx server errors).
- Did mapping succeed? Validate required fields (title, project), and confirm the expected data type (single select vs text).
Why do updates fail or arrive late, and how do you diagnose the cause?
Updates fail or arrive late because of at least three common causes: filtered triggers that never fire, token or permission errors that block actions, and rate limits or queue backlogs that delay processing.
Specifically, diagnose in this order:
- Trigger filters: Airtable “view-based” triggers only fire when records enter or change inside that view; a record can be updated but still not meet view criteria.
- Permissions: a token can read issues but not create or update them; a base can be readable but not editable by the automation user.
- Volume and limits: bursts of commits or issue updates can overwhelm a workflow; delays show up as queued runs.
Next, add observability fields like “Last Synced At” and “Sync Error” in Airtable so you can spot stale records immediately.
What’s the best way to handle retries and prevent “update storms”?
The best way to handle retries and prevent update storms is to use at least three practices: exponential backoff retries, batching or rate-limiting updates, and idempotent processing, so temporary failures recover without spamming both systems.
Moreover, “update storms” often happen when a sync writes a field, triggers itself again, and loops. Break the loop with explicit controls:
- Backoff retries: wait longer between retries after failures, especially on 429 rate limits.
- Batching: group updates (for example, sync every 2–5 minutes) when real-time is not required.
- Idempotency: ensure the same event processed twice produces the same final state, not duplicates.
- Loop guards: write a “Synced By” marker so your trigger can ignore changes made by the integration itself.
To sum up, reliability is not about adding more steps—it’s about adding the right control points so the integration behaves predictably under stress.
What advanced patterns make Airtable ↔ GitLab sync more reliable at scale (and what are the trade-offs)?
Advanced reliability comes from at least three patterns—idempotent upserts, conflict-resolution rules, and environment-aware security controls—because scale amplifies every small inconsistency into a recurring operational problem.
In addition, this is where micro-semantics matters: the integration is no longer just “create an issue.” It becomes a system that must handle retries, duplicates, partial failures, and human behavior across teams. The trade-off is clear: you gain trustable dashboards and less manual effort, but you pay with governance, monitoring, and a higher standard of documentation.
How do you design idempotency and de-duplication rules for commits and issue updates?
You design idempotency and de-duplication by selecting one stable key per object (commit SHA for commits, internal issue ID for issues) and enforcing an upsert rule so reprocessing events never creates extra rows or extra issues.
Specifically, implement the “same input, same outcome” rule:
- Commits: commit SHA is your primary key; if SHA exists, update fields like author, message, and timestamp rather than inserting again.
- Issues: store GitLab internal ID and use it to update; avoid searching by title, which can change.
- Event replay: assume webhooks can be delivered more than once and design accordingly.
Then, keep “last processed event” metadata to detect gaps and validate the integration’s health over time.
How do you handle conflicts in two-way sync (last-write-wins vs source-of-truth vs merge rules)?
Last-write-wins is simplest, source-of-truth is safest, and merge rules are optimal for mature teams—so choose last-write-wins only for low-risk fields, keep GitLab as source-of-truth for execution fields, and use merge rules when you need predictable collaboration.
However, conflict handling is only as good as your field boundaries. Set boundaries first, then apply a rule:
- Last-write-wins: acceptable for non-critical metadata like “Notes” or “Stakeholder comments.”
- Source-of-truth: best for status, assignee, and execution labels; choose GitLab for those fields.
- Merge rules: best for multi-value fields like tags, where you want union behavior rather than overwrite.
Next, document your rules inside the Airtable base (e.g., a “Sync Rules” table) so new team members understand what automation will do.
What changes if you use self-managed GitLab or strict network/security controls?
Self-managed GitLab and strict network controls change the integration because webhook delivery, token governance, and connectivity constraints become first-class requirements, not afterthoughts.
Specifically, plan for:
- Webhook reachability: your endpoint may need allowlisting, VPN access, or internal routing.
- Secrets management: tokens should be stored in an approved secret manager; auditing may be required.
- Environment separation: dev/staging/prod integrations should not share tokens or endpoints.
Then, add a controlled rollout process: test in staging, validate event volume, and only then move to production with monitoring enabled.
When should you not integrate Airtable with GitLab and keep updates human-driven?
Yes—sometimes you should avoid integration and keep a manual workflow for at least three reasons: the workflow changes too often, the data is too sensitive or regulated for automation, or the team lacks ownership to maintain the integration.
Meanwhile, the antonym of automation is intentional manual control. Manual workflows can be healthier when they reduce operational risk. Choose manual when:
- Requirements churn weekly and your mapping rules would break constantly.
- Only a handful of items exist and the automation cost outweighs the time saved.
- Compliance demands strict review of every change, making automated updates risky.
In short, integrate when it creates stable, repeatable value; stay manual when automation would add complexity without trust.

