An Airtable → DocSend → OneDrive → Dropbox Sign workflow is the fastest way for Operations teams to turn a “ready-to-send” record into a signed, archived agreement—by standardizing intake in Airtable, packaging the document experience in DocSend, controlling storage in OneDrive, and executing signatures in Dropbox Sign.
Next, you’ll see what each tool contributes to the chain and why this sequence helps you reduce rework: Airtable organizes demand, DocSend structures the document experience, OneDrive governs the file lifecycle, and Dropbox Sign enforces the signing step with a verifiable audit trail.
Then, we’ll break down the exact inputs you need (fields, roles, permissions, statuses) and show how to design a stage-based pipeline that prevents duplicates, avoids “stuck” requests, and keeps every signature request traceable back to one Airtable record.
Introduce a new idea: once you understand the workflow logic, the rest is execution—connecting accounts, mapping data, and building reliable automation workflows that keep signing on-track even when records change, signers drop off, or permissions fail.
What is an Airtable → DocSend → OneDrive → Dropbox Sign eSignature workflow?
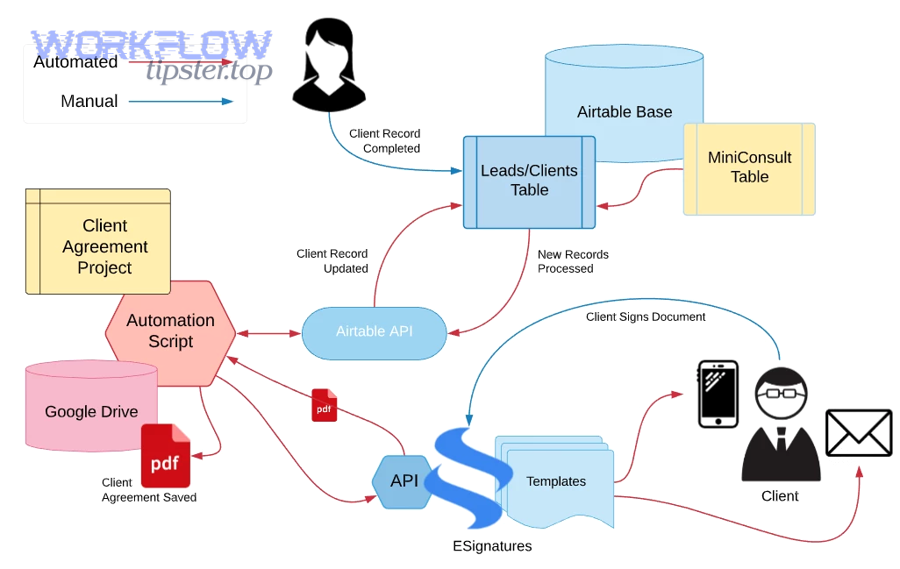
An Airtable → DocSend → OneDrive → Dropbox Sign eSignature workflow is an automation chain that captures signing requests in Airtable, prepares and shares documents through DocSend, stores and versions files in OneDrive, and sends signature requests via Dropbox Sign until a final signed PDF is archived and tracked.
To better understand why this matters, think of the workflow as a conveyor belt: each tool owns one stage so your team stops improvising the same steps for every agreement.

A practical version of this workflow usually looks like this:
- Intake (Airtable): a record becomes “Ready to Send” with signer data, due date, and document reference.
- Document experience (DocSend): the document is packaged into a controlled viewing/signing experience (especially helpful when multiple stakeholders need a consistent “front door”).
- Storage (OneDrive): the canonical file lives in a governed folder structure with consistent naming and access controls.
- Execution (Dropbox Sign): the signature request is created, routed, and completed with status events.
- Tracking (back to Airtable): the record updates as “Sent → Viewed → Signed/Declined/Failed,” with timestamps and links to the final artifact.
If you want a simple definition that stays true in every implementation: Airtable is the system of record; DocSend is the document experience layer; OneDrive is the storage spine; Dropbox Sign is the signing engine. When these roles stay stable, your process stays scalable.
According to a study by the University of California, Los Angeles from the Department of Urology (David Geffen School of Medicine), in 2020, digital signatures reduced median document completion time from 7 days to 3 days in a feasibility study comparing digital vs wet ink routing. (pmc.ncbi.nlm.nih.gov)
Do you need DocSend in the signing chain, or can you sign directly from OneDrive?
Yes—you may need DocSend in the signing chain if you want more control over the document experience, stronger link-based sharing governance, and clearer stakeholder engagement signals; no—you can sign directly from OneDrive if your priority is a simpler file-to-signature path with fewer moving parts.
Below is how to decide quickly, because this one choice determines how “clean” or “complex” your automation workflows become.
The “Yes, use DocSend” reasons (3+)
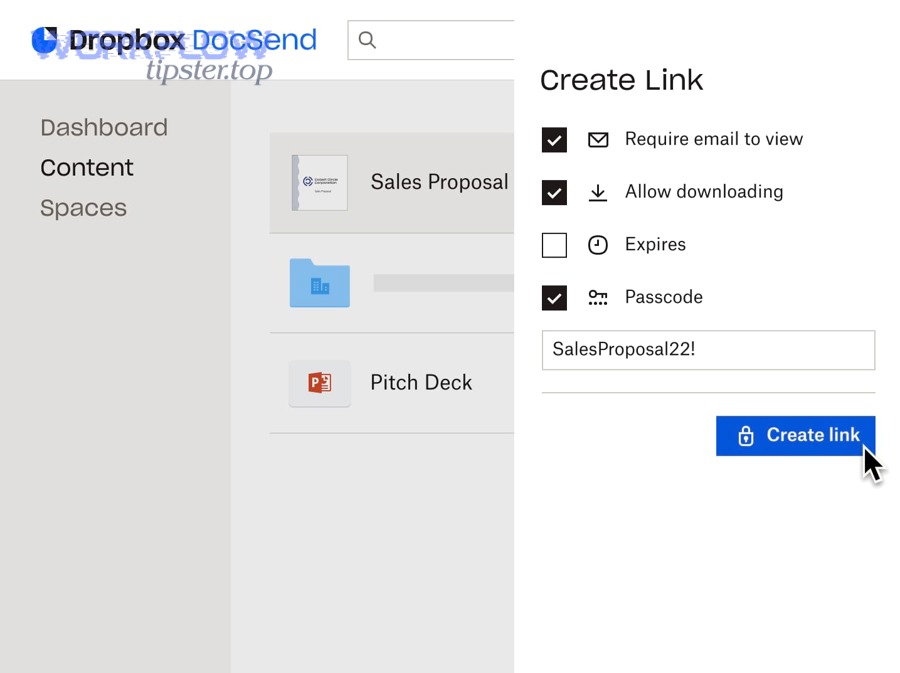
- You need a controlled document front door. DocSend-style sharing can standardize how recipients access the document, so you’re not relying on ad-hoc file links.
- You want engagement context. Even basic signals like whether someone opened a link can help Operations time reminders and escalation (without guessing).
- You need consistent packaging for many document types. If multiple teams send contracts, forms, and policy documents, DocSend becomes a single “presentation layer.”
The “No, you can sign directly from OneDrive” reasons (3+)
- You want fewer systems to maintain. Fewer connectors can mean fewer permission points and fewer failure modes.
- Your documents already live in governed OneDrive folders. If OneDrive is your single source of truth, you can keep the lifecycle there and just call Dropbox Sign.
- Your recipients only need signing, not a managed viewing experience. If “open → sign → done” is enough, DocSend might be optional.
Practically, many Ops teams start simple (OneDrive → Dropbox Sign) and add DocSend only when they need better packaging or when multiple upstream sources create inconsistent document links.
Which components and data do you need before you automate document signing?
There are 6 core components you must have before you automate document signing: Airtable intake fields, a reliable document reference, signer identity data, a clear routing model, a storage location in OneDrive, and a status-tracking model that closes the loop after signing.
Then, once those exist, you can automate confidently because your workflow is built on stable inputs—not guesswork.
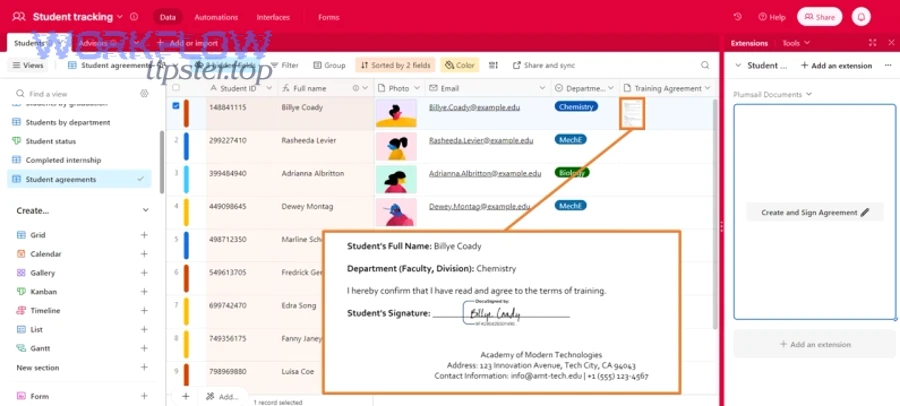
Which Airtable fields should you standardize for signers, documents, and status?
There are 10 foundational Airtable field groups you should standardize—based on the criterion of “minimum viable data to send, track, and audit a signature request.”
To begin, here’s a pragmatic field blueprint Operations teams can copy:
A) Signer identity (required)
- Signer full name
- Signer email
- Signer role (e.g., Customer, Vendor, Approver)
- Signing order (1, 2, 3…) if sequential
B) Document reference (required)
- Document source type (DocSend link vs OneDrive file)
- Document URL (share link) or file ID/path
- Document version or checksum (optional but powerful)
C) Request governance (required)
- Record owner (who is accountable)
- Due date / expiration date
- Priority (Normal / Urgent)
D) Workflow state (required)
- Status (Queued, Ready, Sent, Viewed, Signed, Declined, Failed, Needs Review)
- sent_at timestamp
- last_status_at timestamp
E) External IDs (strongly recommended)
- Dropbox Sign request ID
- DocSend asset/link ID (if used)
- OneDrive file ID/path
F) Audit notes (recommended)
- Exception reason (if Failed/Needs Review)
- Retry count
- Manual override flag
Airtable becomes your “truth table” only when these fields stay consistent across every request. The moment different teams invent different status labels or different signer field formats, your automation workflow turns into a patchwork of special cases.
What permissions and access controls must be in place across Airtable, OneDrive, DocSend, and Dropbox Sign?
Permissions must be in place across all four tools so that the automation account can read the intake data, access the document, store the canonical file, and send the signature request without over-sharing sensitive content.
Next, use this mental model: each handoff requires “read here” + “write there.” If any handoff fails, signing stops.
A reliable baseline approach for Operations:
- Airtable: automation user can read required tables/views and write back status fields. Limit write scope to status + IDs.
- DocSend: automation user can create/share the signable experience (if applicable) and retrieve the correct link/asset ID.
- OneDrive: automation user can write to a governed folder and read the document file that will be signed.
- Dropbox Sign: automation user can create signature requests and receive event updates (via webhook or polling).
Security-wise, aim for least privilege with clear ownership:
- One “service” identity for automations (not a personal account).
- Folder-level permissions in OneDrive (not scattered per-file sharing).
- A documented “break glass” manual process for urgent sends.
This setup is what prevents the classic Ops failure: a workflow that works perfectly for one person’s account—and breaks the moment ownership changes.
How do you design the workflow stages from intake to completed signature?
A strong design uses 7 stages—Queue, Validate, Prepare, Store, Send, Track, Archive—so each stage has one job and one clear output, which makes failures diagnosable and progress measurable.
Below, you’ll see why stage design is the main difference between “automation that scales” and “automation that creates new chaos.”
A stage-based pipeline also creates a natural place for controls:
- Validation before sending
- A human checkpoint for exceptions
- Clean rollback when a signer changes
- Predictable audit logs
What is the recommended status pipeline in Airtable to prevent stuck or duplicate requests?
There are 8 recommended statuses—based on the criterion of “one status per lifecycle milestone”—that keep records moving and prevent duplicates.
Then, implement them as a single-select field so reporting stays consistent.
Recommended statuses (with purpose):
- Queued — record exists but not ready for sending
- Ready — validated and approved to send
- Preparing — building DocSend asset or verifying document reference
- Stored — OneDrive file path confirmed and canonical storage set
- Sent — Dropbox Sign request created (store request ID)
- Viewed — recipient opened the document (if available)
- Signed — completed; final PDF archived; lock the record
- Declined / Failed / Needs Review — terminal exceptions with reason codes
What prevents “stuck” requests is the rule: every status change must have a timestamp, and every exception status must capture a reason.
What prevents duplicates is the rule: the “Sent” transition can happen only once unless a manual override is explicitly set.
How do you prevent duplicate signature requests when the same record updates multiple times?
You prevent duplicates by using an idempotency strategy: a “send lock,” a unique request key, and a rule that record edits do not re-trigger the send stage unless the lock is cleared intentionally.
Next, implement these three tactics together:
- Send lock (sent_at)
- When you send, write
sent_at = now()and never clear it automatically.
- When you send, write
- Unique request key
- Create a key like
record_id + signer_email + doc_versionand store it.
- Create a key like
- Change detection
- If signer email or doc version changes after sending, route to Needs Review instead of automatically re-sending.
This is the same reliability pattern you’d use in other automation workflows. For example, when a support team automates a freshdesk ticket to jira task to slack support triage, they still need a “create-once” rule to prevent duplicate Jira issues when the ticket updates. The same logic applies if you run a freshdesk ticket to clickup task to slack support triage—idempotency keeps the workflow sane when upstream data changes.
How do you connect Airtable to DocSend, OneDrive, and Dropbox Sign step-by-step?
Connect Airtable to DocSend, OneDrive, and Dropbox Sign by following 6 steps—authorize accounts, choose intake views, confirm document sources, set OneDrive storage rules, configure Dropbox Sign sending, and run a controlled test—so the expected outcome is a single record that reliably produces one signature request and one archived signed file.
Let’s explore the sequence, because the order matters: permissions and storage should be solved before you turn on sending.
Step 1: Define the intake view in Airtable
- Create a view like “Ready to Send” filtered by Status = Ready.
- Ensure required fields are present and validated.
Step 2: Authenticate your automation identity
- Use a service identity wherever possible.
- Record which account owns each connection (Ops documentation, not tribal knowledge).
Step 3: Decide your document source path
- Option A: Airtable holds a DocSend link reference (DocSend-first).
- Option B: Airtable holds a OneDrive file reference (OneDrive-first).
Step 4: Create OneDrive storage rules
- Choose a root folder (e.g.,
/Contracts/Sent/and/Contracts/Signed/). - Define naming conventions (ClientName-DocType-Date-RecordID).
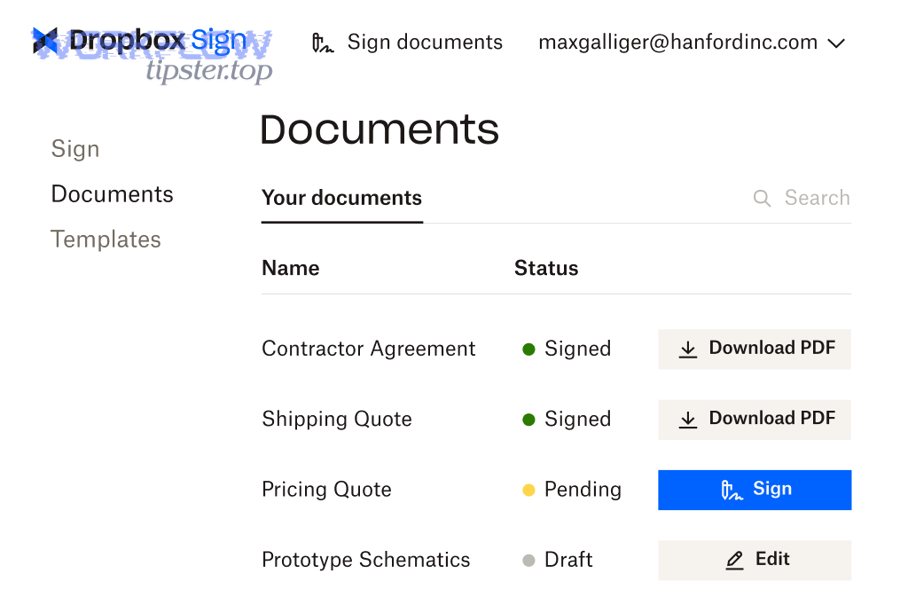
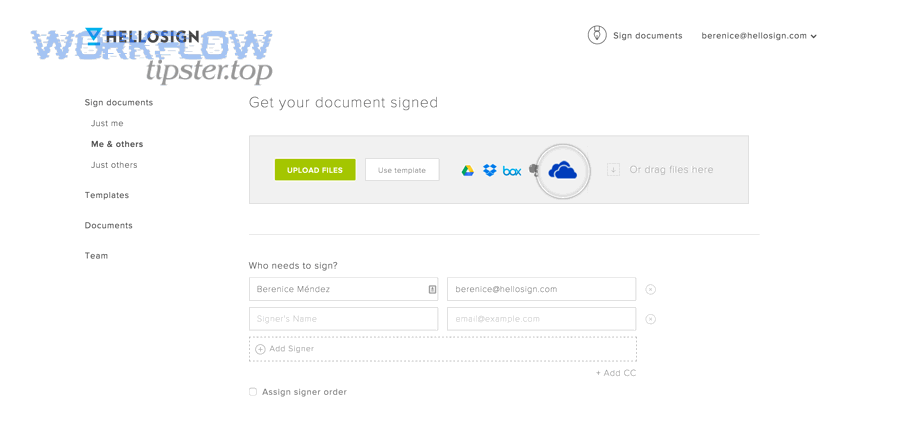
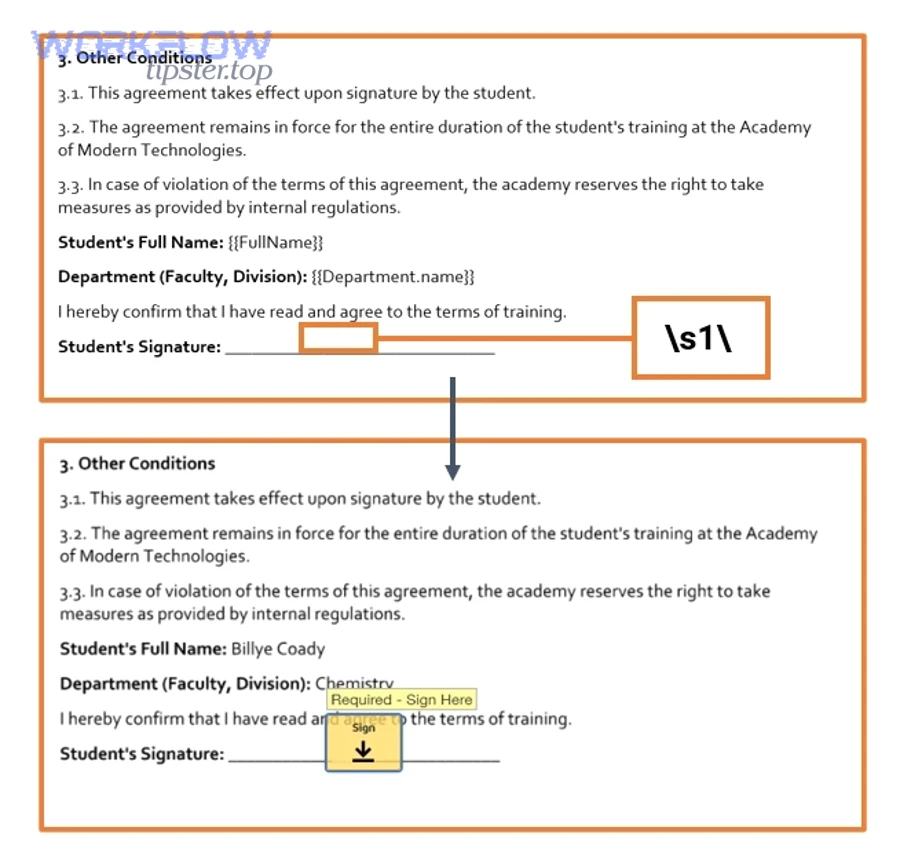
Step 5: Configure Dropbox Sign sending
- Choose template-based or upload-and-send.
- Define signer roles, order, reminders, expiration.
Step 6: Run a controlled end-to-end test
- Use one internal signer and one test document.
- Confirm: created request ID, status updates, and final signed PDF placement.
The single biggest “gotcha” here is enabling sending before storage and permissions are stable. If your automation can’t reliably read the document and write the final artifact, you’ll end up with signed files scattered across personal drives and partial audit trails.
How do you map Airtable data to a Dropbox Sign request correctly?
You map Airtable data to a Dropbox Sign request by defining a stable field-to-role contract, validating required fields before sending, and writing external IDs back to Airtable—so the expected outcome is a request that routes to the right people with the right document and can be tracked from start to finish.
More specifically, mapping is where Ops teams win or lose reliability: it’s easy to “send a request,” but hard to guarantee it’s always the correct request.
A clean mapping model includes:
- Record → Request
- Airtable Record ID becomes the external reference for the signature request.
- Signer fields → Recipient objects
- Name/email map to recipient; role maps to template role.
- Doc reference → File or template
- OneDrive/DocSend reference determines which document gets signed.
- Operational controls
- Due date → expiration; priority → reminder frequency; owner → internal notifications.
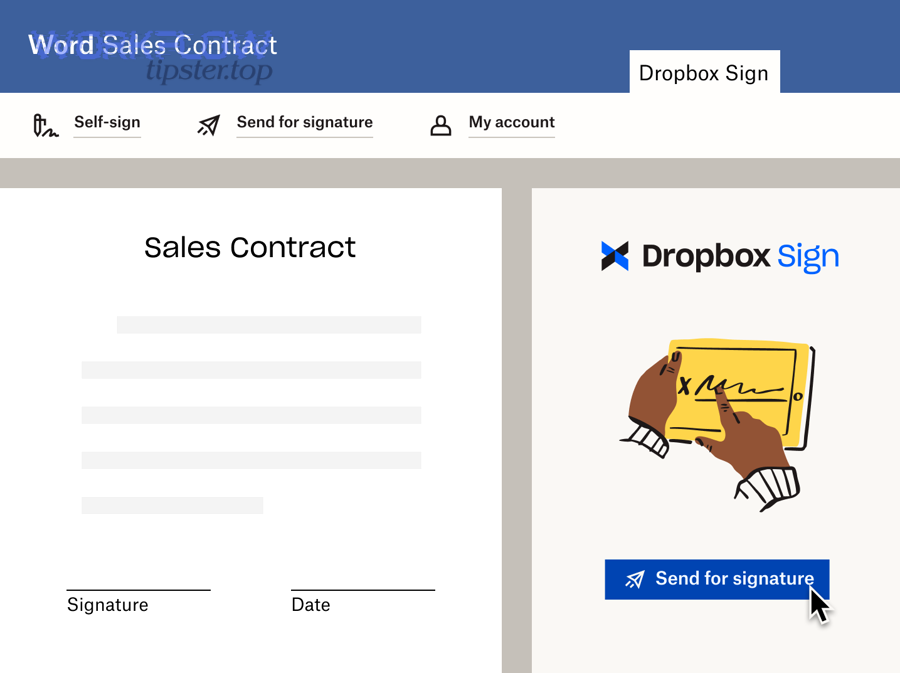
Which Dropbox Sign sending model should you use: template-based or upload-and-send?
Template-based wins in consistency, upload-and-send is best for flexibility, and hybrid is optimal when you need both standardized fields and occasional one-off documents.
Then, use these criteria:
Template-based (best for scale)
- You have repeatable documents (MSA, SOW, NDA).
- You want consistent fields and signer roles every time.
- You want fewer mapping errors because the template defines structure.
Upload-and-send (best for variability)
- Every document is unique (custom redlines, vendor-provided PDFs).
- You prioritize speed of sending over standardization.
- You accept higher diligence requirements in validation.
Hybrid (common for Ops)
- Use templates for 80% of requests.
- Use upload-and-send for exception cases, but enforce strict review gates.
The real cost difference is not “template vs no template”—it’s how many times your team must intervene to fix a mismatch between the document and the signer roles.
How do you handle multi-signer workflows (sequential vs parallel) without breaking the process?
Sequential signing is best for controlled legal routing, parallel signing is best for speed, and mixed routing is optimal when one signer must approve before others can acknowledge.
Next, decide based on what must be true before the document can be considered valid:
Sequential (A → B → C)
- Use when signer B depends on signer A’s completion.
- Store signing order explicitly in Airtable.
- Expect longer cycle times, but clearer governance.
Parallel (A + B + C)
- Use when signatures are independent acknowledgements.
- Improve turnaround, but require better tracking and reminders.
Mixed
- Approver signs first; recipients sign in parallel afterward.
- Requires strong mapping to roles and careful event handling.
From an automation standpoint, multi-signer workflows succeed when your data model treats each signer as an object with status, not just a comma-separated list in one Airtable field.
What should the OneDrive folder structure and file lifecycle look like for signed documents?
Your OneDrive folder structure should be predictable and your file lifecycle should be explicit—so every document has one canonical location, one naming rule, and one “final signed” archive path that the team can audit without hunting.
In addition, the storage design is what keeps your signing process compliant and searchable as volume grows.
A practical OneDrive structure for Operations:
Root folders
/Agreements/Outbound/(pre-sign documents prepared for sending)/Agreements/Signed/(final signed PDFs)/Agreements/Exceptions/(failed/declined with notes)/Agreements/Templates/(if you keep canonical templates internally)
Naming convention (example)
ClientName_DocType_YYYY-MM-DD_AirtableRecordID.pdf
Lifecycle rules
- Prepare (Outbound): create or verify document
- Send: create signature request; store request ID
- Complete (Signed): archive the final PDF and lock editing
- Retain: apply retention policy, access reviews, and periodic audits
This is also where you can enforce “one source of truth.” If DocSend is used for the experience layer, OneDrive still holds the canonical file and the final artifact—so the organization does not become dependent on a single share link for long-term retention.
How do you track progress and push real-time status updates back into Airtable?
You track progress and push updates back into Airtable by recording the signature request ID, capturing key lifecycle events (sent/viewed/signed/declined), and updating a single status field plus timestamps—so the expected outcome is that any Ops teammate can open Airtable and know exactly what’s happening.
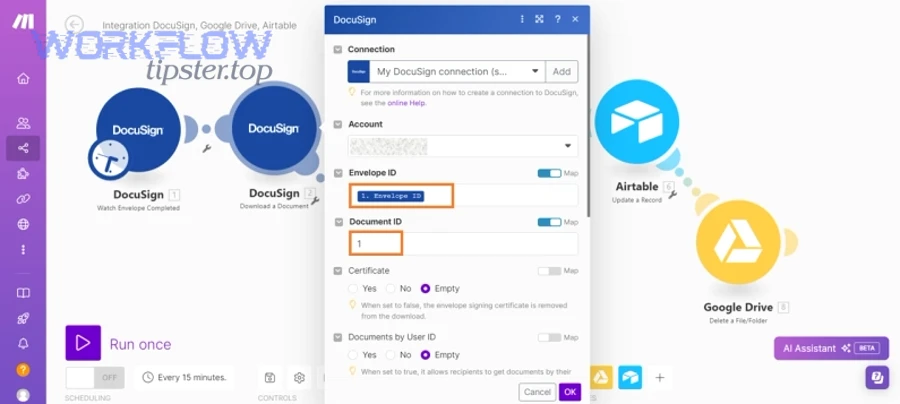
Then, choose between two tracking patterns: polling or events.
Pattern A: Polling (simpler)
- Every X minutes, check status for requests in “Sent.”
- Update Airtable when a status changes.
- Pros: easy to implement.
- Cons: slower and may hit rate limits at scale.
Pattern B: Webhooks/events (more real-time)
- Receive a callback when status changes.
- Update Airtable immediately with event timestamps.
- Pros: fast and scalable.
- Cons: requires robust error handling and idempotency.
What you should store in Airtable for tracking:
- Request ID
- Current status
- sent_at / viewed_at / signed_at timestamps (where available)
- Final file path in OneDrive
- Exception reason + retry count
According to a study by Kungliga Tekniska Högskolan (KTH Royal Institute of Technology) from the Division of Media Technology and Interaction Design, in 2023, personalized email reminders increased the probability of participants being on time by 14 percentage points compared with general reminders—supporting the idea that smart reminders improve completion behavior in deadline-driven workflows. (formative.jmir.org)
What are the most common failure points and how do you troubleshoot them fast?
There are 6 common failure points—authentication, permissions, missing/invalid document references, signer data quality, template/role mismatches, and rate limits—and you troubleshoot fastest by isolating which stage failed and checking the one dependency that stage relies on.
Next, treat troubleshooting like a stage audit: every stage has one expected output, so you check outputs in order.
Failure point 1: Authentication expired
- Symptoms: sudden failures across many records
- Fix: refresh token / reconnect integration; use service account governance
Failure point 2: Permissions misconfigured
- Symptoms: “file not accessible,” “forbidden,” “cannot write to folder”
- Fix: validate OneDrive folder permissions and DocSend access scope
Failure point 3: Document reference is wrong
- Symptoms: request created without correct file, or send fails at “prepare”
- Fix: validate URL format, file ID/path, and that the file exists
Failure point 4: Signer data quality
- Symptoms: bounced emails, invalid recipient, missing role assignment
- Fix: enforce validation rules at “Ready” stage
Failure point 5: Template/role mismatch
- Symptoms: fields don’t populate; signer role not found
- Fix: align Airtable “role” values to the exact template role names
Failure point 6: Rate limits or timeouts
- Symptoms: sporadic failures during peak volume
- Fix: queue requests, use backoff retries, and batch updates to Airtable
Which errors come from permissions vs data quality, and how can you tell the difference?
Permission errors usually fail consistently at the same integration boundary, while data quality errors vary record-by-record; permission errors block access, data quality errors block correctness.
To illustrate, use this quick diagnostic checklist:
Permission error signals
- Many records fail at once
- Same error message across requests
- Failure occurs when reading OneDrive file or writing to a folder
Data quality error signals
- Only certain records fail
- Failures correlate with missing signer email, malformed links, or wrong role values
- Fixing a field resolves the issue without changing permissions
This is why a “Validate” stage is not optional. It’s the cheapest place to catch errors before you create signature requests that embarrass the team—or confuse the customer.
How do you secure and govern the workflow for an Operations team at scale?
You secure and govern the workflow by applying least-privilege access, standardizing ownership, enforcing audit-ready storage, and creating an exception-handling process—so your Operations team can scale volume without scaling risk.
More importantly, governance is what makes the workflow durable when people leave, org charts change, or compliance asks “show me the trail.”
A scalable governance framework includes:
1) Identity and ownership
- Use service identities for automations
- Document who owns each integration connection and where credentials are managed
- Run periodic access reviews
2) Data minimization
- Store only what you need in Airtable (IDs, timestamps, links), not full sensitive documents
- Avoid copying signed PDFs into multiple systems unnecessarily
3) Audit trail completeness
- Ensure every signature request maps to one Airtable record ID
- Ensure every final document has a OneDrive path recorded back in Airtable
- Capture timestamps for key lifecycle events
4) Exception handling
- Route ambiguous changes to “Needs Review” (e.g., signer swapped after sending)
- Document manual steps for urgent edge cases so the team doesn’t invent new processes under pressure
5) Change control
- Treat templates, folder rules, and status pipelines as “process code”
- Version and document changes the same way you would a critical workflow
Done right, you stop relying on heroics and start relying on a system.
What advanced options and edge cases can improve or break an Airtable → DocSend → OneDrive → Dropbox Sign signing workflow?
Advanced options make the workflow faster and safer when they reduce ambiguity (routing rules, compliance controls, retries), but they break the workflow when they add complexity without tightening inputs (unvalidated branching, uncontrolled re-sends, unmanaged environments).
Next, use these edge cases as a checklist: if you handle them intentionally, your workflow becomes resilient instead of fragile.
When should you automate approvals vs keep a manual review step before sending to Dropbox Sign?
Automation is best for low-risk, repeatable documents, while manual review is best for high-risk, high-variance agreements; a hybrid gate is optimal when speed matters but exceptions are costly.
Use these decision rules:
Automate approvals when
- Document type is standardized (e.g., NDA template)
- Signer roles are consistent
- The cost of a wrong send is low
Manual review when
- Large contract value or regulatory exposure exists
- Signer identity changes frequently
- Documents include customized redlines
A practical hybrid model:
- Auto-approve if fields pass validation and document type is “standard.”
- Route to review if doc type is “custom,” signer changes after Ready, or a high-value flag is set.
How do you handle compliance, retention, and audit trails for signed documents stored in OneDrive?
You handle compliance by defining retention rules, enforcing immutable archives for final signed PDFs, and restricting access based on role—so audits can trace who sent what, when it was signed, and where the final artifact lives.
Key micro-controls:
- Retention policy aligned to document type
- Final signed folder with restricted write access
- Consistent naming and metadata that includes record ID
- Periodic access reviews and reporting
If you ever need to answer: “Show me every signed agreement for Vendor X last quarter,” your folder structure and Airtable metadata are what make that question easy instead of painful.
What rate limits, webhook behaviors, and retry patterns matter for high-volume signing?
At high volume, rate limits and event ordering matter most; you stabilize the system with queueing, exponential backoff, idempotent updates, and a dead-letter path for failures so your workflow doesn’t collapse under burst traffic.
Key patterns that keep things stable:
- Backoff retries for transient failures (timeouts, temporary API errors)
- Idempotent writes back to Airtable (update by request ID + event type)
- Event de-duplication (ignore repeated “sent” or “viewed” events)
- Dead-letter handling (route to a table/view for human intervention)
How do you test the workflow safely in sandbox vs production environments?
Sandbox is best for validating logic without risk, production is best for proving real permissions and real stakeholder behavior; a staged rollout is optimal when you need both confidence and accuracy.
A safe testing approach:
- Create a sandbox base/table (or separate workspace) with test records
- Use test signers and non-sensitive documents
- Mirror OneDrive folder structure in a test area
- Run end-to-end tests that confirm:
- One request per record
- Correct role mapping
- Status updates are accurate
- Final signed PDF lands in the expected OneDrive folder
- Roll out to production with:
- limited document types first
- monitoring for failure rate spikes
- a documented rollback plan
When you combine sandbox discipline with production-grade permissions testing, your automation workflows stop being “hope-based” and become “proof-based”—which is exactly what Operations needs.

