If you want documents signed faster without chasing people, the most reliable approach is to automate a single “hook chain” workflow: capture structured inputs in Airtable, publish context in Confluence, store the canonical file in OneDrive, and send that file through DocuSign for eSignature—then sync status and links back to Airtable.
Next, this guide shows whether Ops teams can run that Airtable → Confluence → OneDrive → DocuSign eSignature workflow without custom code, including the exact prerequisites and the common blockers that make teams fall back to manual steps.
Then, you’ll get a practical, step-by-step blueprint that covers Airtable data design, Confluence publishing patterns, OneDrive naming and folder rules, DocuSign envelope routing, and status tracking—so the workflow stays consistent even when multiple people touch the process.
Introduce a new idea: once the core workflow works end to end, you can choose the best automation tool (Zapier vs Make vs n8n) and harden the workflow for reliability, security, and auditability—so it scales beyond one document type and one team.
MAIN CONTENT
What is an Airtable → Confluence → OneDrive → DocuSign eSignature workflow (and what does “automate” mean here)?
An Airtable → Confluence → OneDrive → DocuSign eSignature workflow is an end-to-end document signing system that turns a structured record into a shareable file, routes it for signatures, and writes the signed outcome back to the same record with traceable links.
To better understand why this workflow removes busywork, you need to separate data, context, files, and signatures—because each tool is strongest at one job.
How the workflow behaves from start to finish (macro view)
In practice, the workflow acts like a conveyor belt with one clear source of truth at each stage:
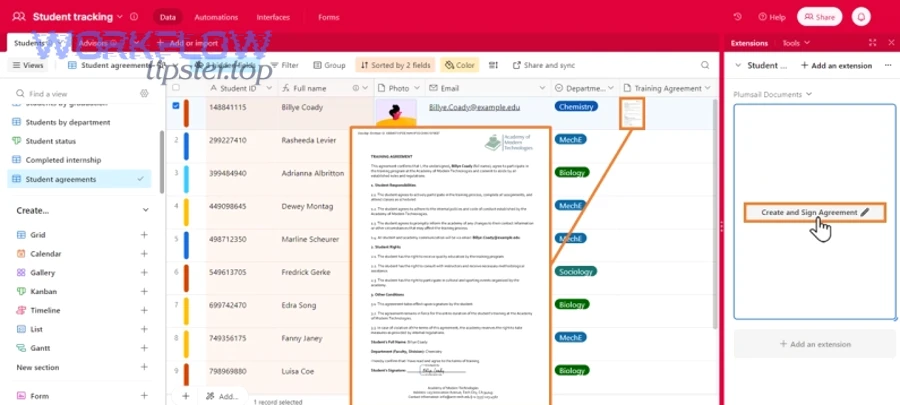
- Airtable = the data source of truth. Airtable holds structured inputs (who signs, what they sign, due dates, doc type) and outputs (envelope ID, signed link, status timestamps). Ops teams use it to control the process, not to store messy versions of documents.
- Confluence = the context layer. Confluence provides the narrative: the “why,” the policy context, the checklist, the instructions, and the stakeholder visibility. It’s where you publish a “living page” that stays updated as the Airtable record progresses.
- OneDrive = the file system of record. OneDrive is where the canonical PDF/DOCX lives with consistent naming, folder rules, and access control. That matters because signatures depend on file integrity and consistent sharing.
- DocuSign = the signing and audit engine. DocuSign handles recipients, routing order, reminders, authentication options, completion certificates, and signature events. It also produces a signed copy and the proof trail your compliance team will ask for.
What “automate (not manual)” means in operational terms
Automation here is not a buzzword. It means you remove repetitive actions that humans do inconsistently:
- No manual copying and pasting record data into templates.
- No manual creating or updating Confluence pages for status changes.
- No manual uploading and renaming files into “random” OneDrive folders.
- No manual emailing PDFs and asking for “please sign.”
- No manual tracking of who signed what and when.
Instead, you use one triggered workflow to generate, publish, store, send, and sync—so every record follows the same path and produces the same outputs.
Where this workflow fits (and where it doesn’t)
This workflow is ideal when you need repeatable agreements (NDAs, vendor onboarding forms, approvals, SOP acknowledgments, policy sign-offs) and you need visibility across teams.
It is not ideal when your documents are one-off negotiations with heavy redlining across multiple parties, because those flows often require a drafting loop before the signature loop.
According to a study by Université de Montréal from the Département de Radiologie, in 2003, the median time from transcription to final signature decreased from 11 days to 3 days after introducing electronic signature in one clinical workflow. (pmc.ncbi.nlm.nih.gov)
Can Ops teams automate Airtable → Confluence → OneDrive → DocuSign without custom code?
Yes—Ops teams can automate the Airtable → Confluence → OneDrive → DocuSign eSignature workflow without custom code for three reasons: no-code connectors cover common trigger/action steps, file routing is standardizable in OneDrive, and DocuSign workflows expose repeatable envelope and status patterns.
Below, the key is to design a workflow that stays simple at the start, then gets more powerful only after it is stable.
What prerequisites (accounts, access, permissions, and licenses) do you need before you start?
There are 5 main prerequisite groups for this workflow: app access, authentication, workspace permissions, file permissions, and DocuSign sending rights—based on where data moves and who must be able to see or change it.
To begin, treat prerequisites as part of the workflow design, not a “setup detail,” because missing permissions create silent failures that look like “automation bugs.”
1) Airtable prerequisites
- A base that contains the workflow table(s) and fields you need (inputs + outputs).
- A dedicated automation user or service account (recommended for stability).
- Permission to read the view you use as a trigger and to write back status fields.
2) Confluence prerequisites
- Permission to create/update pages in the target space.
- A page template or consistent structure you want automation to populate.
- Agreement on how pages are organized (space → parent page → child pages).
3) OneDrive prerequisites
- A defined “system folder” (or SharePoint-backed OneDrive for Business structure) where canonical files will live.
- Permission for the automation identity to create folders, upload files, and generate share links.
- A naming convention that keeps files sortable and searchable.
4) DocuSign prerequisites
- A sender account with permission to send envelopes.
- Template access (if you standardize envelopes/templates).
- Agreement on roles (Signer, Approver, CC) and routing order.
5) Automation platform prerequisites
- A connector that can authenticate to each app (OAuth/keys).
- Access to file-handling actions (upload, download, convert, attach).
- Access to webhooks or polling steps for status updates if you want near real-time tracking.
What are the most common blockers that make the workflow “not fully automatable”?
There are 6 common blockers that prevent full automation: missing file creation, unclear ownership, locked-down sharing policies, inconsistent signer data, envelope complexity, and lack of a reliable status callback—based on where the workflow depends on “human judgment.”
Next, use this list as a pre-flight check before you blame the tools.
- No stable document source
If nobody can say where the “real document” is generated (Confluence page? Word template? Google Doc?), the automation can’t consistently produce a signable file. - Unclear canonical file rule
If teams keep multiple “final” versions in different folders, DocuSign might sign the wrong file, and OneDrive links break the audit chain. - Strict OneDrive sharing restrictions
Some organizations prevent external sharing or block anonymous links, which can break signer access depending on your model. - Signer identity is incomplete or inconsistent
If Airtable records don’t reliably contain signer emails, names, roles, and routing order, DocuSign cannot run without manual fixes. - Envelope rules are too dynamic too early
Complex routing (conditional signers, multiple documents, approvals + signatures) is automatable—but only after you prove a simple version works. - No reliable status feedback loop
If you can’t get “sent/signed/declined” events back into Airtable, Ops teams revert to manual chasing because visibility disappears.
Zapier supports no-code Airtable triggers and Confluence actions like creating Confluence pages from Airtable records, which is a common foundation for this workflow’s first half. (zapier.com)
How do you set up the workflow step-by-step from Airtable to signed document?
Use one end-to-end method with 10 steps—trigger, validate, generate, publish, store, send, confirm, sync, notify, and audit—to produce a signed DocuSign file that stays linked to the Airtable record and visible in Confluence.
Then, implement it in a “thin slice” first (one document type, one signing path), because stability beats complexity when you want repeatable automation workflows.
Step blueprint (macro flow you can reuse)
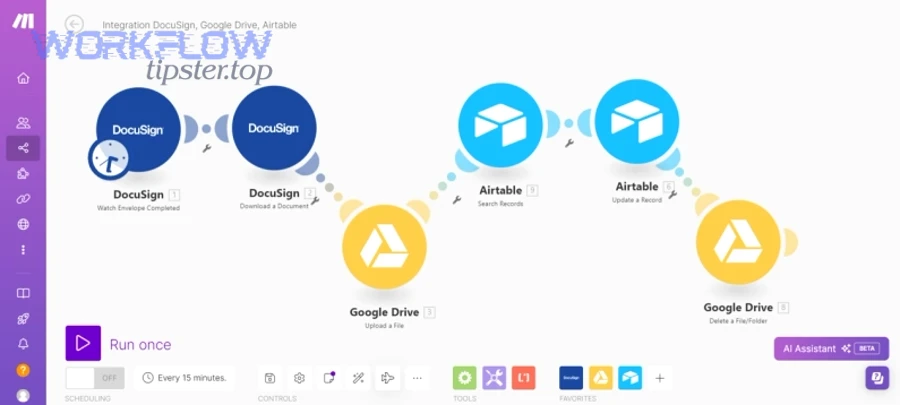
Here is the practical blueprint you can adapt to Zapier, Make, or n8n:
- Trigger: A record in Airtable enters a “Ready to Send” status (or is created in a specific view).
- Validate: Check required fields (doc type, signer emails, routing order, due date).
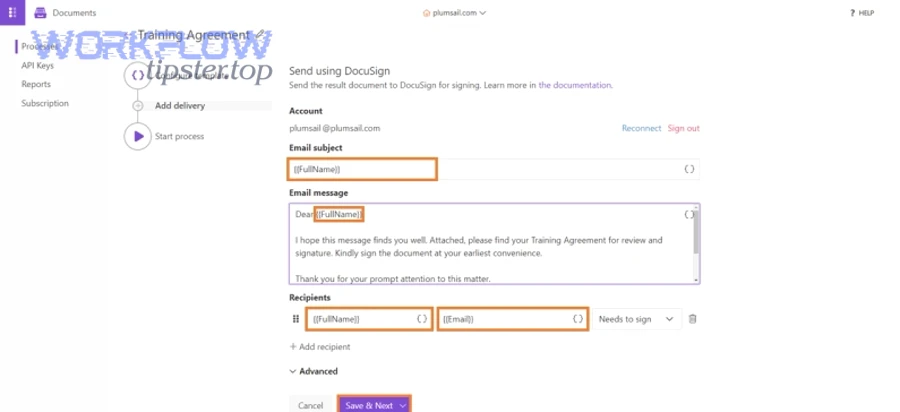
- Generate document: Create a PDF/DOCX from a template or content source.
- Publish context: Create/update a Confluence page that mirrors key metadata and links.
- Store canonical file: Upload to OneDrive in the right folder with the right name.
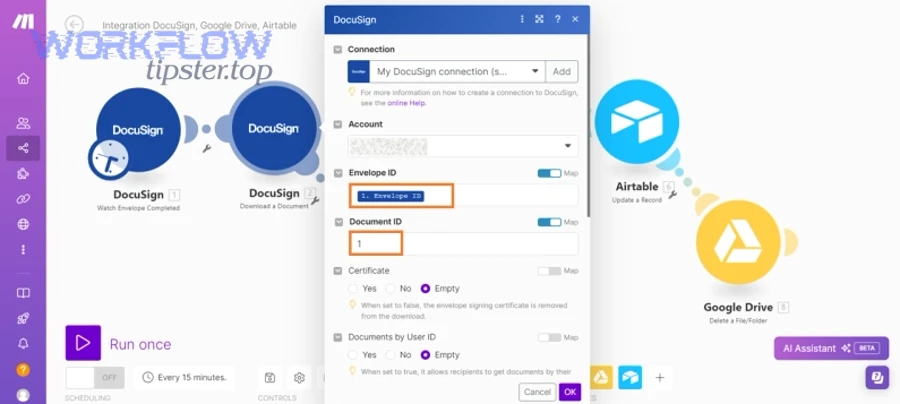
- Create envelope: Send the OneDrive file via DocuSign with recipients/roles.
- Write back tracking keys: Store envelope ID + send timestamp in Airtable.
- Monitor status: Listen for completion events (webhook) or poll until complete.
- Store signed outputs: Save the signed copy (and certificate) to OneDrive.
- Sync and notify: Update Airtable + Confluence with signed link; notify stakeholders.
The rest of this section explains how to design steps 1–10 so they stay predictable.
How do you structure Airtable to store inputs, signer roles, and signing status?
There are 3 main Airtable structures you can use—single-table, two-table (records + signers), and relational (records + signers + documents)—based on how many signer roles and document types you need.
Next, choose the structure that matches your workflow maturity.
Option A: Single-table (fastest to ship)
- Best when each record has 1–2 signers and 1 document.
- Key fields (recommended):
- Record ID (or use Airtable’s internal ID)
- Document Type
- Template Name / Template ID
- Signer 1 Email, Signer 1 Name, Signer 1 Role
- Signer 2 Email (optional), Signer 2 Role (optional)
- Routing Order (simple numeric or “Signer then Approver”)
- Status (Draft → Ready → Sent → Signed/Declined/Expired)
- Envelope ID
- Sent At, Signed At
- OneDrive File Link
- Signed File Link
- Confluence Page Link
- Error Log (long text)
Option B: Two-table (records + signers)
- Best when records can have variable signer counts.
- Tables:
- Agreements (one row per agreement)
- Signers (one row per person; linked to an agreement)
- Benefits:
- Dynamic routing order
- Easier reassignment and escalation
- Clear audit of who was supposed to sign
Option C: Relational (records + signers + documents)
- Best when one agreement includes multiple documents or attachments.
- Tables:
- Agreements, Signers, Documents
- Benefits:
- Multi-doc envelopes
- Better for compliance-heavy processes
- Easy reporting by document type
Practical rule: If your team argues about “where to store the signer list,” you already need Option B.
How do you generate the document and publish it to Confluence correctly?
Confluence wins for visibility and governance, while the file generation method depends on whether you start from a template or from rich content—so the best approach is to generate the signable file first, then publish the Confluence page with stable links.
Below, treat the Confluence page as the human-readable contract hub, not the file itself.
Recommended pattern: “Page as hub, file as artifact”
- Confluence page contains:
- Agreement metadata (doc type, owner, due date, signer list)
- Status banner (Draft/Sent/Signed)
- Links to:
- Canonical file in OneDrive
- Signed copy in OneDrive
- Airtable record
- OneDrive contains:
- The canonical PDF/DOCX used for signing
- The signed copy and certificate
Create vs update Confluence pages
- Create a new page when each agreement should have its own permalink and history.
- Update an existing page when you track recurring agreements under one controlled “registry” page.
How to keep Confluence content consistent
- Use a Confluence page template with placeholders the automation fills.
- Use one standard “Status” block so people know where to look.
- Use one standard “Links” block so your hook chain never breaks.
How do you save the file to OneDrive with the right naming and folder rules?
There are 4 main OneDrive storage rules that keep this workflow stable: one canonical folder path, deterministic filenames, strict permissions, and a signed-copy convention—based on how humans search and how auditors verify.
Then, apply these rules before you automate the DocuSign send, because file chaos becomes signature chaos.
1) Folder taxonomy (simple but scalable)
- /Agreements/{Department}/{DocumentType}/{Year}/
- Example: /Agreements/Ops/Vendor_Onboarding/2026/
2) Deterministic naming convention
Use a name that avoids duplicates and supports sorting:
- {DocType}_{CompanyOrPerson}_{AirtableRecordID}_{YYYY-MM-DD}.pdf
- Example: NDA_AcmeCo_recA1B2_2026-02-02.pdf
3) Permission design
- Automation identity: edit permission in the system folders.
- Team members: read or edit depending on role.
- External signers: avoid giving OneDrive access directly unless your org requires it; let DocuSign handle signing access.
4) Signed-copy convention
- Signed copy name: append _SIGNED (and keep the original intact).
- Example: NDA_AcmeCo_recA1B2_2026-02-02_SIGNED.pdf
This single rule prevents the “someone overwrote the canonical file” nightmare.
How do you send the OneDrive file through DocuSign and track completion?
DocuSign sending works best when you treat every envelope as a trackable transaction: you attach the canonical file, define roles and routing order, store the envelope ID in Airtable, and update status from completion events.
Next, focus on tracking—because sending is easy, but visibility is what Ops teams depend on.
Sending: the operational minimum
- Envelope recipients:
- One or more Signers
- Optional Approver (if your process requires approval before signature)
- Optional CC (for visibility)
- Envelope controls:
- Reminder schedule (e.g., every 2 days)
- Expiration (e.g., 14 days)
- Message text that references the Confluence page (context)
Tracking: the non-negotiables
Write these back to Airtable immediately after sending:
- Envelope ID
- Sent At
- Envelope Status (Sent)
- Signer Summary (optional)
Then update on completion:
- Signed At
- Signed File Link (OneDrive)
- Envelope Status (Completed/Declined/Expired)
One optional video walkthrough (for the OneDrive ↔ DocuSign piece)
According to DocuSign’s OneDrive Connect documentation, prerequisites like having a OneDrive account, sharing folders/documents with users, and ensuring Connect is enabled on the DocuSign account directly impact whether autosave-style flows work. (support.docusign.com)
Which automation approach is best: Zapier vs Make vs n8n for this workflow?
Zapier wins in speed-to-launch, Make is best for visual branching and data shaping, and n8n is optimal for technical teams that need control, extensibility, and self-hosting—so the “best” choice depends on how complex your DocuSign routing and file handling must become.
Meanwhile, you should choose tools based on the workflow’s hard parts: multi-step branching, file conversions, retries, and long-running signature tracking.
A quick comparison table
The table below compares Zapier, Make, and n8n across criteria that matter specifically for Airtable → Confluence → OneDrive → DocuSign eSignature automation workflows.
| Criterion | Zapier | Make | n8n |
|---|---|---|---|
| Best for | Fast deployment + simple flows | Complex routers + transformations | Custom logic + control |
| Setup effort | Low | Medium | Medium–High |
| Branching/routers | Good (paths) | Strong (routers) | Strong (logic nodes) |
| Data shaping | Good | Strong | Strong (code + nodes) |
| File handling | Good for common cases | Strong for multi-step scenarios | Strong if you can configure nodes |
| Long-running tracking | Works (polling/webhooks via steps) | Works (scenarios + scheduling) | Works (webhooks + queues) |
| Ops maintainability | High (easy UI) | High (visual) | Depends on team maturity |
Use it like this: if you need predictable maintainability for Ops, start with the simplest tool that can complete the end-to-end hook chain without hacks.
What is the simplest “minimum viable” automation workflow for teams starting today?
There are 3 main MVP versions of this workflow—single-signer, two-step (approver+signer), and multi-signer sequential—based on how many recipients and decisions you need on day one.
To begin, ship single-signer first because it proves file generation, storage, and status syncing without complex routing.
MVP 1: Single-signer, one document (recommended first release)
- Airtable trigger: record becomes “Ready”
- Confluence: create page from template
- OneDrive: upload canonical PDF
- DocuSign: send envelope to one signer
- Airtable: write back envelope ID + status
- Notification: email/Teams/Slack message to owner
MVP 2: Approver then signer (adds governance)
- Add a human checkpoint before sending
- Approver can flip Airtable status from “Review” → “Ready”
- This reduces “oops we sent the wrong doc” incidents
MVP 3: Multi-signer sequential (adds realism)
- Uses routing order logic
- Requires strong signer data design in Airtable
- Adds more failure modes—so only do this after MVP 1 works
Operational tip: If you also run “github to linear to microsoft teams devops alerts” elsewhere, treat this signing flow the same way: a small, reliable MVP is better than a “perfect” automation that fails silently.
What is the most scalable version of this workflow for multiple doc types and teams?
There are 4 scaling patterns—template library, modular sub-flows, centralized logging, and environment separation—based on how you prevent your automations from turning into an unmaintainable maze.
More specifically, scaling is less about “more steps” and more about “reusable components.”
1) Template library (documents + envelopes)
- Standardize:
- Document templates by doc type
- DocuSign envelope templates by doc type
- Store template IDs in Airtable so the workflow selects the right one automatically.
2) Modular sub-flows
- Sub-flow A: “Generate & store file in OneDrive”
- Sub-flow B: “Create/update Confluence page”
- Sub-flow C: “Send DocuSign envelope & track status”
This makes changes safer because you don’t rewrite everything when one step changes.
3) Centralized logging
- Create a dedicated Airtable table (or base) called
Automation Runs - Write:
- Run ID, record ID, timestamp
- Step name
- Success/failure
- Error detail
This turns debugging into searching and filtering, not guesswork.
4) Test vs production environments
- Separate credentials and folders:
- /Agreements_TEST/ vs /Agreements/
- Separate Airtable views:
- “Ready (Test)” vs “Ready (Prod)”
- Separate DocuSign environments if available (sandbox vs production)
Workflow expansion note: If you already use “google forms to hubspot to google sheets to slack lead capture,” the same scaling principle applies: standardize the schema first, then automate the handoffs.
How do you make the workflow reliable, secure, and auditable (not brittle)?
A reliable, secure, and auditable Airtable → Confluence → OneDrive → DocuSign eSignature workflow is one that prevents duplicates, enforces least-privilege access, logs every key status change, and stays idempotent—so reruns don’t create chaos.
Besides building the steps, you must engineer failure behavior—because production workflows fail, and Ops teams need predictable recovery.
The reliability checklist (macro safeguards you should implement)
Use this checklist to harden the workflow:
- Idempotency key: one unique key per agreement (Airtable Record ID + Doc Type).
- Single canonical file rule: one “current” file to sign; signed copies never overwrite it.
- Deterministic naming: identical inputs generate identical naming rules.
- Permission boundaries: automation identity can do what users cannot, but only where needed.
- Audit trail fields: envelope ID, timestamps, signer list snapshot, file link snapshot.
- Alerts: notify humans when automation cannot proceed safely.
How do you prevent duplicates, version conflicts, and broken links across the four apps?
DocuSign prevents signature tampering, but your process must prevent duplicate sends and version drift—so the most effective strategy is to enforce one canonical file path, one envelope per record state, and one stable link strategy across Confluence and Airtable.
However, you also need rules that hold up under human behavior.
1) Prevent duplicate sends (idempotency in practice)
- Before sending, check if Airtable already has:
- Envelope ID and Status = Sent
- If yes, stop the workflow and notify the owner instead of sending again.
2) Prevent version conflicts (canonical file model)
- Canonical file:
- Stored in OneDrive
- Name stays stable for the agreement’s lifecycle
- Signed copy:
- Stored as a separate file with _SIGNED
- Confluence page links:
- Link to canonical file and signed copy once available
- Airtable record:
- Stores both links so the Confluence page can be regenerated without loss
3) Prevent broken links (link strategy)
Choose one link strategy and stick to it:
- Prefer file permalink URLs rather than “temporary share links” if your org rotates sharing settings.
- If you must use share links, generate them from a dedicated system folder with stable permissions.
4) Prevent the “someone updated the doc after sending” issue
- When status becomes “Sent,” lock down editing:
- Either set permissions to read-only
- Or store an immutable PDF copy for signing and keep the editable source separate
How do you handle errors, timeouts, and partial failures without losing track of signatures?
There are 4 main error-handling patterns—retry with backoff, dead-letter logging, human escalation, and safe re-run rules—based on whether failures are transient, permanent, or data-related.
In addition, you should treat signature workflows as long-running processes, not instant transactions.
1) Retry with backoff (for transient failures)
Use retries for:
- Temporary API timeouts
- Rate limits
- Brief permission glitches after admin changes
But cap retries. If a step fails 3 times, stop and log the run.
2) Dead-letter logging (for permanent failures)
When something fails, write back to Airtable:
- Status = Error
- Error Step = Upload to OneDrive (example)
- Error Detail = Permission denied (example)
Then route the record into an “Ops Queue” view so humans can triage consistently.
3) Human escalation (for risky failures)
Send an alert to a shared channel:
- Microsoft Teams / Slack / email
- Include:
- Airtable record link
- Error step
- Suggested fix
This is how you keep the hook chain intact when automation breaks.
4) Safe re-run rules (for partial completion)
Define what “safe rerun” means:
- If file upload succeeded but DocuSign send failed, rerun from “send” step only.
- If DocuSign send succeeded but status sync failed, rerun only the “status monitor” step.
- If you can’t guarantee step boundaries, rerun nothing automatically—require a human checkpoint.
Reliability is not only “less downtime.” It is “fewer invisible errors,” because invisible errors create manual chasing, which recreates the very “Not Manual” problem the workflow was meant to solve.
SUPPLEMENTARY CONTENT
What advanced patterns make this eSignature workflow faster, safer, and less manual over time?
There are 4 advanced patterns that improve this workflow—dynamic signer routing, Confluence-as-hub design, compliance-grade audit trails, and deliberate manual checkpoints—based on how you reduce operational friction without sacrificing control.
To illustrate, these patterns turn a working workflow into a durable system your org can trust.
How can you build dynamic signer routing (role-based, conditional, or multi-step approvals) from Airtable?
There are 3 main ways to build dynamic signer routing from Airtable: rules by record type, rules by department/region, and rules by amount/risk—so the workflow assigns recipients automatically without guessing.
Next, use routing only when your Airtable data is clean enough to support it.
Pattern 1: Role-based routing (most common)
- Airtable stores roles (Legal Approver, Finance Approver, Signer)
- Automation selects email addresses based on roles linked to the record
- Benefits:
- Easy reassignment
- No hard-coded emails in automation steps
Pattern 2: Conditional routing (adds intelligence)
- If Doc Type = Vendor and Region = EU, add a compliance approver
- If Amount > $50,000, require Finance approval before signature
- Benefits:
- Governance without manual intervention
Pattern 3: Multi-step approvals (adds safety)
- Airtable status moves: Draft → Review → Approved → Ready → Sent
- Automation only sends DocuSign when Approved is true
- Benefits:
- Prevents accidental sends
- Creates an audit-friendly decision trail
What’s the best way to use Confluence as the “policy hub” while OneDrive remains the file system of record?
Confluence is best as the policy hub for explanation and visibility, while OneDrive is best as the system of record for canonical files—so the strongest pattern is “Confluence page = context + links” and “OneDrive folder = artifacts + versions.”
More importantly, this pattern keeps collaboration from corrupting the signature chain.
How to structure the Confluence hub
- A consistent page template that includes:
- “Purpose” section (why this doc exists)
- “Inputs” section (key Airtable metadata)
- “Process” section (what happens next)
- “Artifacts” section (OneDrive canonical + signed link)
- “Audit” section (envelope ID, timestamps, signer list)
Why this works
- People read Confluence to understand what and why
- People use OneDrive to manage files
- The automation ensures the links stay updated as the record changes
How do you implement compliance-grade audit trails and retention (without over-collecting data)?
Compliance-grade audit trails require you to capture the minimum proof needed—who initiated, who signed, what was signed, and when—while controlling access and retention so sensitive data does not spread across tools.
Then, build auditability into Airtable and OneDrive rather than stuffing everything into Confluence.
Minimum audit fields to store in Airtable
- Envelope ID
- Send timestamp + completion timestamp
- Signer list snapshot (names/emails/roles at send time)
- Canonical file link snapshot
- Signed file link snapshot
- Error log (if any)
Retention and access strategy
- OneDrive:
- Store signed copies in a restricted folder
- Apply retention policies where your org requires them
- Confluence:
- Store links and metadata, not the signed file itself (unless policy demands)
- Automation platform:
- Avoid storing sensitive payloads in long-term logs
- Redact where possible
Micro-optimization: If compliance needs stronger controls, store a hash of the canonical file at send time so you can later prove the file did not change.
When should you avoid automation and keep a manual checkpoint (and why)?
Yes—you should keep a manual checkpoint when the risk of sending the wrong document is high, when legal review is mandatory, or when signer identity requires human verification, because these scenarios benefit more from correctness than speed.
In short, “Not Manual” does not mean “No Humans”; it means humans intervene only where judgment matters.
Best moments for a manual checkpoint
- Before sending DocuSign for:
- High-value agreements
- Regulated documents
- First-time vendor onboarding
- After document generation but before upload:
- When templates are new or frequently updated
- When signer identity is uncertain:
- Role-based routing rules are still maturing
How to keep the checkpoint efficient
- Make the checkpoint a single Airtable status change: “Review” → “Approved”
- Keep the reviewer’s job clear:
- Verify the canonical file link
- Verify signer list
- Verify due date / routing order
- Let automation handle everything else
According to a study by Université de Montréal from the Département de Radiologie, in 2003, introducing electronic signature reduced median turnaround times (e.g., 11 days to 3 days in one measured workflow), which supports the idea that automating signing steps removes delay—provided governance prevents incorrect sends. (pmc.ncbi.nlm.nih.gov)

