Airtable → Confluence → OneDrive → Dropbox Sign document signing is best built as a controlled, no-code pipeline where an Airtable record becomes the “source of truth,” OneDrive hosts the canonical file, Confluence provides the process context, and Dropbox Sign executes signatures with trackable status updates. Then, you keep the workflow reliable by using clear statuses, strict permissions, and a single signing trigger that prevents duplicates.
Next, the fastest way to make this automation dependable for Ops teams is to treat it like a production system: define ownership, lock down access, standardize naming, and log every run so anyone can audit what happened without hunting across tools. This turns “send for signature” from a manual chase into predictable automation workflows.
Besides, OneDrive ↔ Dropbox Sign configuration matters more than most teams expect because file access, folder routing, and signed-copy storage determine whether your process is clean or chaotic. When you set the integration properly, you can save completed PDFs back to OneDrive automatically and keep the Airtable record updated with links and timestamps. (help.dropbox.com)
Introduce a new idea: once you understand the core flow, you can design the Airtable base, choose the right trigger, map recipients and roles, and add governance so the workflow scales without custom code—then expand to advanced scenarios like templates, packets, and idempotency.
What is a no-code document signing automation from Airtable to Confluence to OneDrive to Dropbox Sign?
Airtable → Confluence → OneDrive → Dropbox Sign is a no-code document signing automation that turns structured request data into a signature request, stores files in OneDrive, documents the process in Confluence, and writes signing results back to Airtable for tracking and auditability.
To better understand why this chain works, it helps to see it as one “record-led” workflow with four specialized roles: database, knowledge hub, file repository, and signature engine.



What does each app do in the workflow (Airtable vs Confluence vs OneDrive vs Dropbox Sign)?
Each app does one primary job: Airtable tracks the request, Confluence explains and governs the process, OneDrive stores the authoritative file, and Dropbox Sign sends, tracks, and completes signature requests with a formal audit trail.
More specifically, here’s how to keep responsibilities clean so your team doesn’t blur tool boundaries:
- Airtable (System of Record):
- Holds request metadata (document type, requester, due date, signer list, approver, status).
- Stores identifiers (request ID, signature request ID/envelope ID) so reruns don’t double-send.
- Becomes the single dashboard for Ops: “What’s pending, sent, completed, failed?”
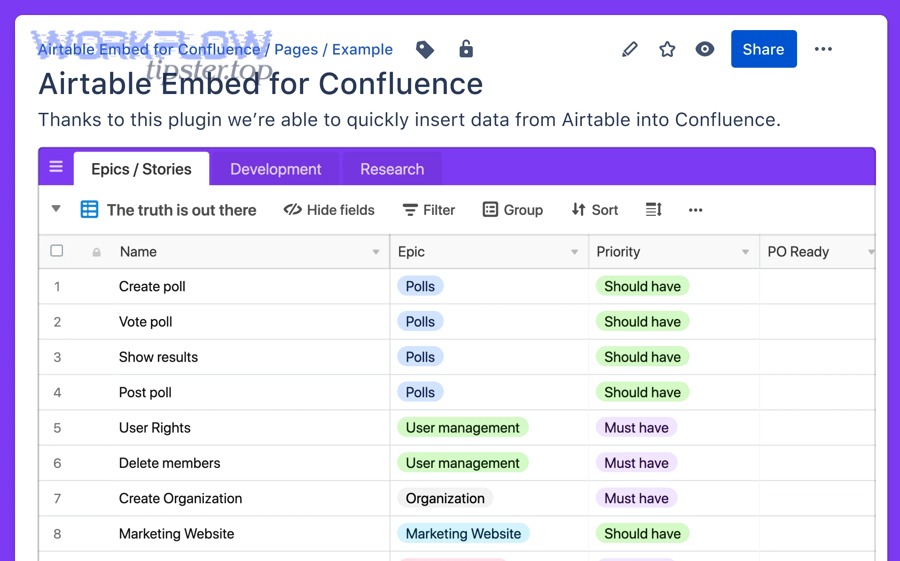
- Confluence (Process Context + Policy):
- Holds SOP pages and templates that explain when to send a document, who approves, and what must be included.
- Links back to Airtable so reviewers see the record context without scattered notes.
- Acts as the training source for new team members.
- OneDrive (Canonical File Storage):
- Stores the source file to be signed (and the final signed PDF).
- Enforces organizational permissions and sharing rules.
- Provides folder structure for governance (e.g., /Contracts/In-Progress vs /Contracts/Signed).
- Dropbox Sign (Execution + Tracking):
- Creates signature requests, assigns recipients, runs signing order, sends reminders, and records completion.
- Stores copies of sent/received documents in OneDrive when integrated, reducing manual file hunting. (help.dropbox.com)
If you keep those roles consistent, every future change becomes easier because you always know which system is responsible for what.
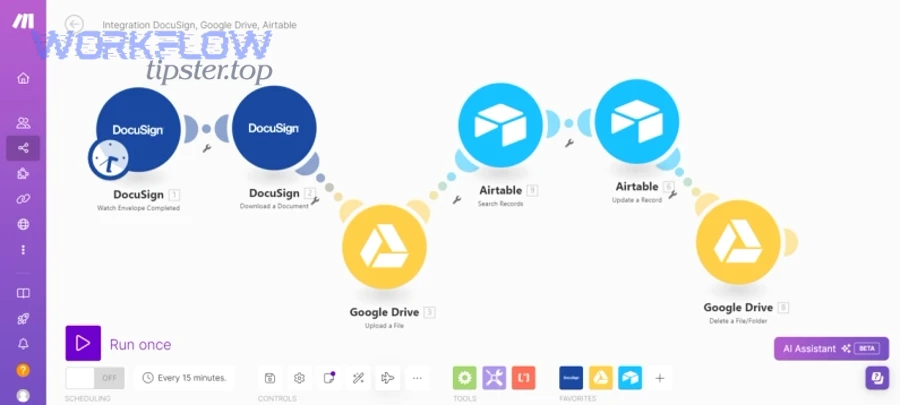
Which integration approach should Ops teams use: Zapier vs Make vs Power Automate?
Zapier wins in speed-to-launch, Make is best for multi-step logic and data shaping, and Power Automate is optimal for Microsoft-centric governance and enterprise controls.
However, the best choice depends on where your “hard requirements” live:
- Choose Zapier when: your priority is quick setup, simple triggers (“status becomes Ready”), and straightforward updates back to Airtable. Zapier’s Airtable + Dropbox Sign ecosystem is built for common automation workflows like “new record → send signature request.” (zapier.com)
- Choose Make when: you need richer branching, iterators for multiple signers, or more complex transformations (like building dynamic signer lists).
- Choose Power Automate when: identity, tenant policies, and Microsoft 365 admin control dominate your requirements (especially if OneDrive permissions and audit expectations are strict).
A practical rule: start with the tool your Ops team will actually monitor—because the best automation is the one someone can troubleshoot at 9 p.m. without panic.
Can you build this workflow without custom code—and is it reliable enough for Ops teams?
Yes—Airtable → Confluence → OneDrive → Dropbox Sign can be reliable without custom code because you can (1) control the trigger with a status gate, (2) enforce permissions and file conventions, and (3) log envelope IDs to prevent duplicate sends.
Next, “reliable enough” isn’t a vibe—it’s an engineering outcome created by operational discipline: consistent inputs, predictable states, and visibility when something fails.

What are the minimum requirements (accounts, permissions, and access levels) to make it work?
There are 4 minimum requirement groups—Airtable access, Confluence access, OneDrive access, and Dropbox Sign sender permissions—based on who must read, who must write, and who must approve.
More specifically, define these roles before building anything:
- Workflow Owner (Ops): can edit Airtable base structure, manage views, and maintain SOPs in Confluence.
- Requesters (Business users): can create Airtable requests and view statuses, but cannot edit system fields (like envelope IDs).
- Approvers (Ops/Legal/Finance): can approve in Airtable or Confluence (depending on your design) and view the OneDrive document.
- Senders (Dropbox Sign): a controlled identity that sends signature requests (ideally a shared service identity), so the audit trail is consistent.
For OneDrive, align file access with the signing reality: signers need access to sign, but they do not need broad access to your storage. Use least-privilege sharing patterns whenever possible.
What are the most common failure points ?
The most common failure points are (1) broken file access, (2) invalid signer data, (3) duplicate triggers, (4) template mismatch, and (5) rate limits/timeouts—so prevention means validating inputs and adding guardrails.
Moreover, here’s a prevention checklist that consistently reduces failures:
- File access failures (OneDrive):
- Store a canonical OneDrive file link in Airtable, not a copied link from email.
- Ensure the sending identity can access the file.
- Avoid “anyone with the link” sharing when governance matters.
- Signer data failures (Dropbox Sign):
- Validate emails before “Ready.”
- Require signer role labels (Approver, Signer, CC) and signing order fields when needed.
- Duplicate sends (Automation):
- Only send when
Status = ReadyANDEnvelopeID is empty. - Immediately write
EnvelopeIDback to Airtable after sending.
- Only send when
- Template mismatch:
- Map document type → template ID in Airtable so the workflow never guesses.
- Operational blind spots:
- Log an “Error message” + “Run ID” field so someone can fix one record without halting everything.
According to a 2020 case report by San Francisco State University’s Quality Assurance team, electronic signatures reduced average turnaround time by 73% versus the manual process across six selected cases, and 78% of transactions were completed in less than one week—showing how reliability + adoption can compound into real throughput gains. (calstate.edu)
How do you design the Airtable base so document signing is trackable and automated?
Design the Airtable base by creating a request table with controlled statuses, a signer structure, and audit fields so the automation can read “Ready,” send once, and write back envelope IDs and signed-file URLs for traceable execution.
Then, the key is to separate human-editable fields (request details) from system fields (envelope ID, timestamps, run logs) so nobody accidentally breaks the workflow.

Which fields should you create for a signing workflow (status, signer, file link, envelope ID)?
There are 12 core fields you should create for a signing workflow—based on what you must validate before sending and what you must store after sending.
Specifically, build a “Signing Requests” table with:
- Request ID (formula or autonumber)
- Requester (collaborator or text)
- Document Type (single select: NDA, MSA, Offer Letter, Policy Acknowledgement, etc.)
- Confluence Page URL (URL) — SOP or approval context
- OneDrive File URL (URL) — canonical file to sign
- Signer 1 Email (email)
- Signer 1 Role (single select: Signer/Approver/CC)
- Signing Order (number) — optional for sequential signing
- Status (single select: Draft → Ready → Sent → Completed → Failed)
- Envelope ID / Signature Request ID (single line text) — system field
- Signed File URL (OneDrive) (URL) — system field
- Sent At / Completed At / Last Error / Run ID (dates + long text)
To keep the base “Ops-safe,” lock system fields with permissions, and create views like Ready to Send, In Progress, Needs Fix, and Completed.
How should you structure statuses to avoid duplicate sends (Draft → Ready → Sent → Completed)?
A single controlled status field wins in clarity, a multi-field gating model is best for complex approvals, and a hybrid approach is optimal for Ops teams who want both simplicity and safety.
More specifically, compare the options:
- Single-status model (best for most teams):
- Draft: incomplete details
- Ready: validated and approved
- Sent: envelope ID exists
- Completed: signed file stored + links written
- Failed: needs Ops intervention
Why it works: the automation trigger is obvious and easy to audit.
- Multi-field gating (best for regulated flows):
Approved = YesandFile Verified = YesandSigner Verified = Yes
Why it works: allows granular accountability but can confuse requesters.
- Hybrid (recommended):
- Use Status for state, plus two checkbox gates:
Signer Verified,File Verified.
Why it works: you get clarity + control without creating a “checkbox jungle.”
- Use Status for state, plus two checkbox gates:
In practice, the “no duplicates” rule is simple: Only send when Status = Ready and Envelope ID is blank. Everything else is a nice-to-have.
How do you set up the end-to-end automation step by step?
Use one main method with 7 steps—design trigger gating, validate inputs, fetch the OneDrive file, send via Dropbox Sign, write envelope IDs back, store signed copies in OneDrive, and update Airtable statuses—so the workflow produces a measurable “Sent → Completed” outcome.
Below, the step-by-step build keeps the hook chain tight: you start with Airtable control, then connect storage and signing, then close the loop with status and links.
What is the best trigger for starting signing: new record, status change, or approval complete?
Status change wins for control, new record is best for ultra-simple intake, and approval complete is optimal when governance must precede signing.
More importantly, here’s how to choose:
- New record trigger: fast but risky because users often create records before fields are complete.
- Status change to Ready: best default because it forces validation before signing.
- Approval complete: best for high-stakes docs where compliance requires a formal approval step.
For Ops teams, “Status → Ready” usually becomes the cleanest operational contract: when you mark it Ready, the system sends it—once.
How do you map data to the signature request (recipients, roles, signing order, message)?
Map Airtable fields to Dropbox Sign request parameters by using consistent recipient roles, validated emails, and a deterministic signing order so the signature request always mirrors the record.
Specifically, use this mapping pattern:
- Subject line:
{{Document Type}} for {{Company/Client}} — Request {{Request ID}} - Message body: short instructions + due date + “reply to Ops if changes needed”
- Recipients:
- Signer emails from Airtable
- Role labels (Signer/Approver)
- Order number when sequential signing matters
- CCs: internal stakeholders who need visibility but not signing action
- Reminders: set reminders in Dropbox Sign where available, so Ops isn’t chasing manually
If you want the workflow to “feel human,” add a short, consistent message template so signers understand the action in one glance.
How do you route the signed document back to OneDrive and update Airtable automatically?
Route the signed file back by storing completed copies in a dedicated OneDrive folder and writing the final OneDrive URL into Airtable, then move the request status to Completed after Dropbox Sign reports completion.
To illustrate the cleanest loop, follow this order:
- Send signature request
- Write Envelope ID back to Airtable immediately
- Wait for completion event (or poll status)
- Save signed PDF to OneDrive (e.g.,
/Signed/{{Year}}/{{Document Type}}/) - Write signed file URL to Airtable
- Set Status = Completed
- Notify stakeholders (email/Teams/Slack)
Dropbox Sign’s OneDrive integration is designed to sync documents into OneDrive via a Dropbox Sign folder, which reduces manual downloads and re-uploads when you activate the integration properly. (help.dropbox.com)
How do you use Confluence correctly in a signing workflow (without turning it into a bottleneck)?
Use Confluence as a “process and policy layer” that standardizes document types, approvals, and checklists—while Airtable remains the execution dashboard—so Confluence supports signing instead of slowing it down.
In addition, Confluence becomes your quality multiplier when it reduces ambiguity: fewer back-and-forth edits, fewer wrong templates, fewer “who approves this?” delays.

How do you standardize templates and SOP pages to reduce signing errors?
Standardize SOP pages by using Confluence templates that define required inputs, approval rules, and file conventions, so every Airtable request follows the same checklist before it becomes Ready.
For example, create one Confluence template per document type:
- Purpose: what the document is for
- Required fields: signer list, legal entity, effective date, attachments
- Approval policy: who approves and when
- OneDrive file standard: where the canonical file must live
- Naming convention:
{{Client}}_{{DocType}}_{{YYYY-MM-DD}}_v{{#}} - Common failure prevention: “verify link access,” “verify signer email,” “confirm signing order”
Then link the SOP page into Airtable so requesters and approvers always have the same source of truth.
Should Confluence hold approvals or should Airtable?
Airtable wins for operational approvals, Confluence is best for policy-driven review context, and a hybrid approach is optimal when approvals need both execution tracking and documented rationale.
Specifically:
- Airtable approvals:
- Best when the approval is a gate to automation (e.g., checkbox “Approved”).
- Keeps state in one place, easy for Ops to filter.
- Confluence approvals:
- Best when the approval requires narrative context, policy references, or structured review notes.
- Great for “why this exception was approved.”
- Hybrid (recommended):
- Confluence holds the “why” (notes, policy references), Airtable holds the “go/no-go” gate.
This hybrid keeps the workflow fast without sacrificing governance.
What security, compliance, and governance practices keep this workflow safe?
There are 6 governance practices that keep Airtable → Confluence → OneDrive → Dropbox Sign safe: least-privilege access, controlled send identities, protected system fields, consistent storage, audit logging, and monitored failures.
Especially for Ops teams, safety is not only about security—it’s also about preventing process drift when the workflow scales.
What are safe defaults for OneDrive sharing links and access (least privilege)?
Safe defaults are: restricted sharing, short-lived links when possible, “need-to-know” access, and separated folders for in-progress vs signed files.
More specifically, implement these defaults:
- Use restricted links (specific people) instead of public links whenever possible.
- Separate storage zones:
/In-Progress/for files being prepared/To-Sign/for files ready to send/Signed/for completed documents
- Keep signed documents immutable: treat Signed as an archive; edits create a new version in a new location.
- Control folder permissions: signers rarely need folder access; they only need signing access through the request.
What should you log for auditability (timestamps, sender, envelope ID, signed file URL)?
You should log envelope IDs, status transitions, timestamps, sender identity, signer list, and file URLs so anyone can reconstruct the “who/what/when” without contacting five people.
To sum up the minimal audit schema in Airtable:
Envelope IDSent At,Completed AtSent By(service identity)Signer Emails(snapshot field)Source OneDrive File URLSigned OneDrive File URLLast Error+Run ID(for debugging)
According to a 2025 Stanford Institute for Human-Centered AI article summarizing research by MIT economist David Autor, 64.5% of removed tasks were routine while 75.6% of added tasks were abstract in task changes analyzed between 1977 and 2018—supporting the idea that automation tends to eliminate repetitive work and shift teams toward higher-value work when designed with the right guardrails. (hai.stanford.edu)
Before you leave the governance layer, document these decisions in Confluence so the workflow is repeatable: who can send, who can approve, how links are created, and what constitutes a valid “Ready” record.
Also, if your team is already automating adjacent processes—like google forms to hubspot to google sheets to microsoft teams lead capture or freshdesk ticket to asana task to google chat support triage—reuse the same governance patterns (least privilege, status gating, and logging) so all automation workflows share one operational standard. And if you publish internal guidance, you can brand your playbook voice as Workflow Tipster so teammates recognize the canonical “how we automate” rules across projects.
How do you optimize advanced signing scenarios in Airtable → Confluence → OneDrive → Dropbox Sign workflows?
Optimize advanced scenarios with 4 upgrades—choose template vs file-send intentionally, handle document packets cleanly, prevent duplicates with idempotency controls, and define a clear boundary where no-code ends and custom-code begins—so the workflow scales without fragility.
Below, these micro-level optimizations make the difference between “it works” and “it works every day.”

Should you send a OneDrive file directly or use a Dropbox Sign template—and when?
Direct file-send wins for ad hoc documents, templates are best for standardized forms, and a hybrid approach is optimal when you need both flexibility and consistency.
More specifically, use this decision matrix:
- Use direct file-send when:
- The document is authored in Word/PDF and changes frequently.
- The signing fields are not standardized across versions.
- You need speed and minimal setup.
- Use templates when:
- The document structure is stable (same fields, same signature placements).
- You want fewer errors and consistent role assignment.
- Ops needs to enforce compliance text and signer positions.
- Use hybrid when:
- Templates exist for standard docs (NDA), while complex contracts use file-send.
This is also where you can extend your process library: if you already run airtable to microsoft word to onedrive to pandadoc document signing for a different department, you can compare it to Dropbox Sign and decide which system performs better for templates vs bespoke documents (without rewriting your entire Airtable base).
How do you handle multiple documents in one signature request (packets) without confusion?
Handle multi-document packets by using consistent naming, deterministic ordering, and a packet manifest in Airtable so signers know exactly what they are signing and Ops can store the outputs cleanly.
Specifically, implement these packet rules:
- Packet ID:
PKT-{{Request ID}} - Document list: a linked table “Packet Documents” with: Doc Name, OneDrive URL, Version, Order
- Signer instructions: “This request contains 3 documents. Please review in order.”
- Storage strategy: save signed outputs into
/Signed/{{Packet ID}}/with one file per document (or one combined PDF if supported).
A short Airtable table can prevent long email threads. Include context when you add a table: the table below shows a clean packet manifest structure that makes packet automation predictable.
| Field | Purpose | Example |
|---|---|---|
| Packet ID | Groups related documents | PKT-1042 |
| Doc Order | Controls signing review order | 1, 2, 3 |
| OneDrive URL | Canonical source file link | https://… |
| Signed URL | Final storage link | https://… |
| Version | Prevents signing wrong draft | v3 |
How do you prevent duplicates when automations rerun (idempotency + run logs)?
Prevent duplicates by using envelope IDs as a hard lock, adding a run log identifier, and requiring a single “Ready” transition so replays cannot send the same request twice.
However, duplicates can still happen if you don’t design for them—because no-code tools will retry on transient errors.
Use these idempotency controls:
- Envelope ID lock: if Envelope ID exists, do not send.
- Run ID: write a unique run identifier each time the automation starts.
- Atomic transition: when sending succeeds, immediately set Status = Sent and store Envelope ID.
- Retries: allow retries only when Status = Failed and Envelope ID is blank.
- Human override: add a field
Force Resend = Yes(rarely used) that requires Ops-only permission.
This is the antonym logic that keeps no-code safe: automate by default, intervene by exception—not the other way around.
When should Ops teams choose no-code over custom code for signing automation?
No-code wins in speed and maintainability, custom code is best for deep customization and extreme scale, and a hybrid approach is optimal when you need a stable core with a few coded extensions.
In short, choose no-code when:
- The workflow can be expressed as triggers, actions, and field mappings.
- Your team can monitor failures and fix records without engineers.
- You need to iterate quickly and prove ROI.
Choose custom code when:
- You must implement complex document assembly, dynamic field placement, or unusual identity flows.
- You need guaranteed throughput at very high volume with strict SLAs.
- Your compliance posture requires bespoke logging, encryption, or policy enforcement beyond tool settings.
For most Ops teams, the real unlock is operational: build the robust no-code version first, then only “graduate” to code when you can clearly name the capability gap—because “custom code” without a clear gap often becomes a maintenance trap.

