Connecting Freshdesk to Jira for two-way ticket sync means you create a single, traceable workflow where a Freshdesk ticket can become (or link to) a Jira work item, and key updates—like status and notes—stay aligned across both tools so neither team loses context.
Next, you’ll see how to choose the right Jira destination (Jira Software vs Jira Service Management) based on whether your workflow is engineering backlog-first or ITSM/operations-first, because the “best” setup depends on where ownership and SLAs actually live.
Then, you’ll learn the practical configuration that makes two-way syncing safe: prerequisites, field/status mapping, and the guardrails that prevent duplicate updates, permission errors, or accidental sharing of internal information.
Introduce a new idea: to keep this guide semantically clear, the main keyword focus is freshdesk to jira, the predicate is connect, the relations lexical is Hyponym (two-way ticket sync is a specific type of integration), and the outline intent mix is mainly How-to with supporting Definition, Comparison, Grouping, and Boolean questions.
What does “connecting Freshdesk to Jira for two-way ticket sync” actually mean?
Connecting Freshdesk to Jira for two-way ticket sync is an integration method that links tickets and work items so ticket-side activity (like notes and closures) and Jira-side actions (like adding notes or closing) can reflect back across systems with controlled visibility and mapping.
To better understand what you’re actually building, it helps to separate linking from syncing and define exactly which updates flow where.

What is the difference between “linking” a ticket to an issue and “syncing” them?
Linking means Freshdesk and Jira reference each other, while syncing means the integration actively transfers defined updates (like status, comments, or fields) between them on rules you control.
Next, once you know whether you need link-only or real sync, you can choose the minimum data set that prevents “copy-paste escalation” without creating noise.
A link-only setup is often enough when:
- Support only needs a Jira URL and a “current state” snapshot.
- Engineering only needs the customer context once (repro steps, environment, impact).
- The teams already communicate in a shared channel for updates.
A sync setup is usually required when:
- Support must notify customers based on Jira progress (triage → in progress → fixed → released).
- Engineering needs new evidence from ongoing customer replies (screenshots, logs, steps to reproduce).
- You want an auditable escalation trail without manual re-entry.
In practice, most mature teams do both: they link for traceability and sync a limited, high-value subset (status + key notes + priority/severity alignment) to protect signal-to-noise.
Does two-way sync always mean “everything syncs both ways”?
No, two-way sync for Freshdesk to Jira is only effective when it syncs selectively—at least three reasons are control (to prevent data leaks), reliability (to avoid conflicts/loops), and clarity (so each team keeps ownership of its workflow).
Then, once you accept that “two-way” should be curated, you can define boundaries like public vs internal notes and which system owns which fields.
A healthy definition of “two-way” typically looks like this:
- Support → Engineering (Freshdesk → Jira): customer impact, reproduction steps, attachments/logs, urgency signals, and follow-up findings.
- Engineering → Support (Jira → Freshdesk): progress/status updates, resolution notes that are customer-safe, fix/version references, and requests for more information.
A risky “sync everything” approach creates common failure modes:
- Accidental disclosure: internal Jira comments landing in customer-visible replies.
- Conflicting updates: both sides editing the same field with different meaning.
- Noise loops: a synced comment triggers a webhook that creates another comment.
If you remember one rule: two-way sync works best when each side owns specific fields, and the integration only carries what the other side truly needs.
Which Jira product should you integrate with: Jira Software or Jira Service Management?
Jira Software wins for engineering backlog workflows, Jira Service Management is best for ITSM-style alerting/on-call workflows, and a hybrid approach is optimal when support escalates to engineering but operations still needs structured incident/alert handling.
Next, you’ll choose the Jira “landing zone” based on whether your Freshdesk items become engineering work or service operations signals.

When should support teams prefer Jira Service Management for Freshdesk integration?
Yes—support teams should prefer Jira Service Management for Freshdesk integration when you need at least three things: structured alert handling, escalation/on-call workflows, and bidirectional operational updates that map cleanly back to ticket notes.
Below, this choice becomes obvious when your workflow includes incident-style routing, escalations, and rotations tied to operational response.
Jira Service Management (JSM) is a strong fit when:
- Freshdesk tickets represent incidents or operational issues requiring response ownership.
- You need escalations and on-call rotations, not just a dev backlog queue.
- You want two-way behavior where Freshdesk ticket notes flow to JSM and JSM actions (ack/close/note) can reflect back as private notes.
If your goal is “every important ticket becomes an operational alert with rules,” JSM is usually the cleanest semantic match.
When is Jira Software enough for Freshdesk → engineering escalation workflows?
Yes—Jira Software is enough when your Freshdesk to Jira workflow mainly needs at least three outcomes: create dev work items, keep progress visible to support, and avoid ITSM overhead that doesn’t map to engineering delivery.
Then, once you confirm the destination is engineering, you can design mappings around issue types, components, and sprint-ready fields.
Jira Software is a good fit when:
- Support escalates bugs, feature requests, and tasks into a product backlog.
- Engineering owns the workflow from triage to done in scrum/kanban.
- You primarily need: ticket → issue creation, link-back, status updates, and controlled comment sync.
A practical pattern is: Freshdesk remains the customer communication layer, while Jira Software remains the delivery layer—connected by a thin sync that prevents context loss.
What prerequisites must be in place before you start the Freshdesk–Jira setup?
There are 6 core prerequisites for a reliable Freshdesk to Jira setup: correct permissions, integration authentication, a clearly chosen Jira target project, a field/status map draft, a test/sandbox workflow, and a rollout plan with monitoring.
To begin, you should treat prerequisites as “integration design,” not “admin chores,” because most failures come from mismatched expectations rather than tooling.
What permissions do you need in Freshdesk and Jira to create and update records?
You need admin-level access (or delegated integration permissions) in both Freshdesk and Jira to create items, read/write the mapped fields, and post notes/comments according to your visibility rules.
Next, once permissions are correct, you can enforce least privilege so the integration can do its job without becoming a security backdoor.
Use this checklist mindset:
- Freshdesk: ability to read ticket content, create notes, and (if applicable) access ticket fields needed for rules/triggers.
- Jira: ability to create issues in the target project, update fields you map, and add comments (or transition status if you sync status).
Practical tip: create a dedicated “integration user” with only the project permissions required for the integration, not a human admin account.
Which fields should you standardize first to avoid sync failures?
You should standardize a small set of “must-not-break” fields first: ticket/issue title format, priority/severity mapping, status mapping, product/component tags, and a consistent customer-impact summary.
Then, once these are stable, you can safely add custom fields without turning your sync into fragile glue.
Start with these field standards:
- Title/summary template: include customer, product area, and short symptom.
- Description template: reproduction steps + environment + expected vs actual + impact.
- Priority/severity: define meaning (customer urgency vs engineering severity).
- Tags/components: align taxonomy (e.g., “billing”, “mobile”, “login”, “API”).
- Visibility rules: what counts as internal-only vs customer-safe.
The goal is not perfection—it’s to ensure that any ticket escalated to Jira has enough context to be triaged without a back-and-forth.
Should you create a sandbox/test project before syncing live tickets?
Yes—creating a sandbox/test project before syncing live tickets is the safest Freshdesk to Jira approach for at least three reasons: it prevents irreversible bad mappings, it allows realistic end-to-end testing, and it gives you a rollback path before customers are impacted.
Next, once you have a sandbox, you can simulate real ticket types and confirm every rule behaves as intended.
A simple sandbox plan:
- Create a test Jira project (or a test board within a project if your governance allows).
- Create 10–20 sample Freshdesk tickets representing common scenarios .
- Test: creation, linking, comment sync, status transitions, and attachment handling.
- Document “expected behavior” so stakeholders agree before you flip production on.
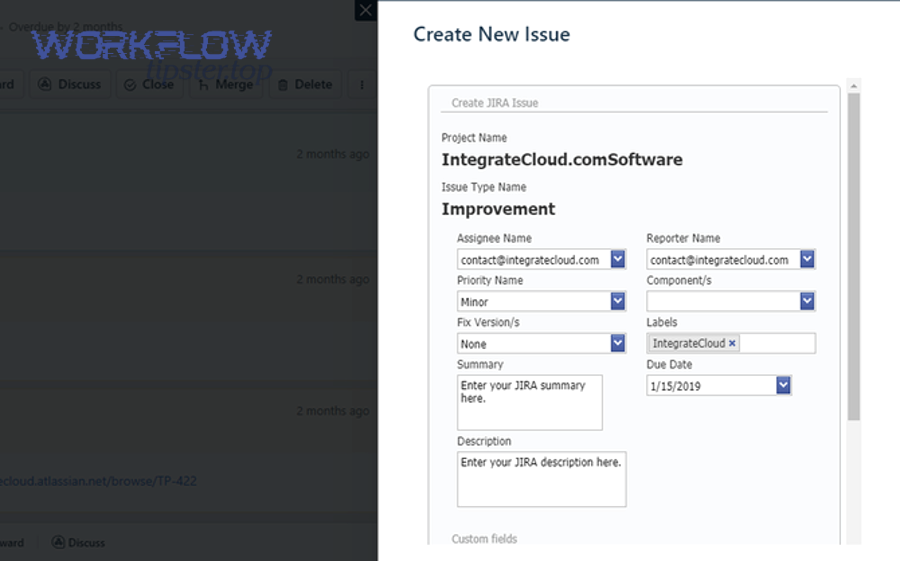
How do you set up Freshdesk → Jira issue creation step-by-step?
The most reliable method is a 6-step setup: choose your integration approach, authenticate, define the target Jira project/issue types, map required fields, enable link-back, and run controlled tests before rollout so Freshdesk tickets reliably create Jira issues.
Below, you’ll build the “create from ticket” pipeline first, because two-way sync is easier once creation is stable.
How do you connect accounts and authorize access securely?
Secure authorization means using OAuth/API keys in a dedicated integration account, limiting scopes/permissions, and rotating credentials on a schedule rather than sharing personal admin tokens.
Then, once authorization is stable, you can treat every sync failure as a rules/mapping issue instead of an access mystery.
Even if you use a different connector, the security principle stays the same:
- Prefer dedicated integration credentials
- Apply least privilege
- Maintain auditability (who changed what and when)
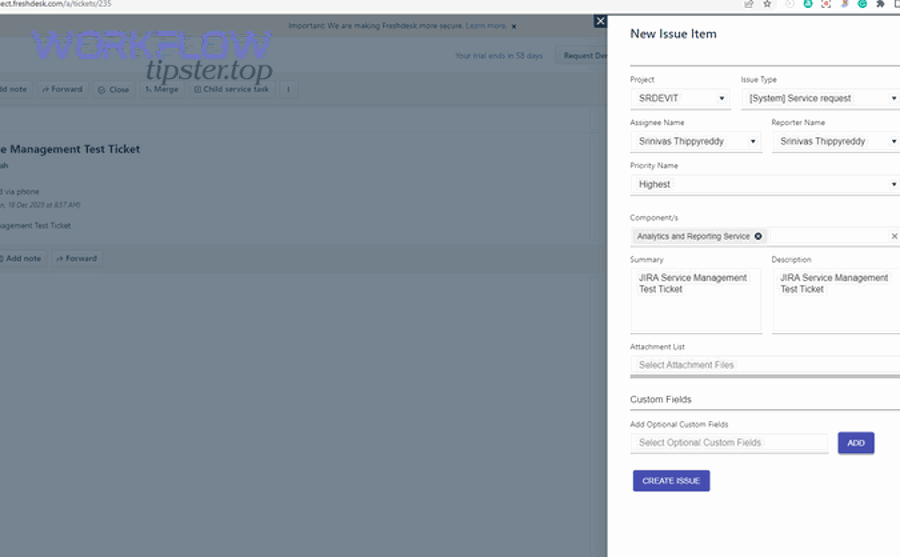
How do you map Freshdesk ticket fields to Jira issue fields during creation?
There are 5 core mapping groups for Freshdesk to Jira creation: identity fields, context fields, classification fields, routing fields, and communication fields.
Next, once you map by groups, you avoid the classic mistake of “mapping everything” before you even know what engineering truly needs.
1) Identity fields (traceability)
- Freshdesk ticket ID + URL → Jira custom field or description footer
- Jira issue key → Freshdesk ticket link field or private note
2) Context fields (triage-ready)
- Subject → Summary
- Description → Description (use a template with headers)
- Customer impact → a structured field or top-of-description block
3) Classification fields (meaning)
- Ticket type/category → Issue type/component
- Tags → Labels/components
4) Routing fields (ownership)
- Product area → Jira project or component
- Priority/severity → Jira priority (with clear mapping rules)
5) Communication fields (signal)
- Latest public reply (careful!) → optionally include as customer context
- Internal notes → keep internal unless explicitly needed
A good description template creates fast triage:
- Customer / Account
- Impact
- Steps to reproduce
- Expected vs actual
- Environment
- Attachments / logs link
- Freshdesk ticket link
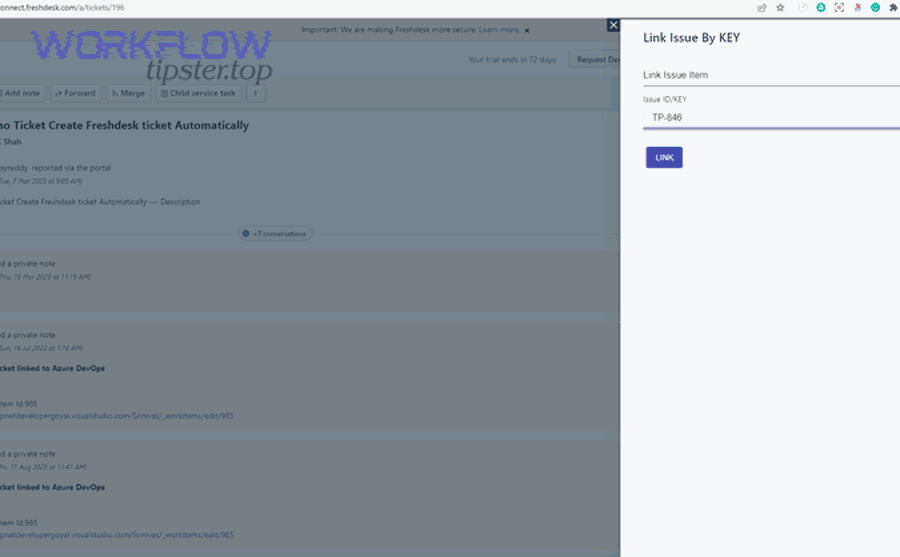
How do you ensure the Jira issue link is written back into the Freshdesk ticket?
Yes—you should write back the Jira issue link into the Freshdesk ticket for at least three reasons: support gains instant visibility, engineering reduces duplicate escalations, and managers can audit the full lifecycle without hunting across tools.
Then, once link-back exists, you can safely automate status updates without losing the “single thread” of truth.
Common link-back methods:
- Add a private note to the Freshdesk ticket containing the Jira key + URL.
- Store the Jira key in a custom field on the ticket for reporting/filters.
- Add a tag like jira-linked to drive downstream automation (e.g., SLA handling, escalation queues).
Optional (but powerful): enforce a rule that only tickets with jira-linked can move into certain support statuses like “Escalated” or “Engineering in progress,” which keeps operations clean.
How do you enable two-way sync between Freshdesk and Jira without breaking workflows?
The safest two-way sync approach is to sync only 4 classes of updates—status signals, customer-safe progress notes, high-value fields, and essential attachments—while assigning field ownership to one system per attribute to avoid conflicts and loops.
Next, once you define “what must sync,” you can also define “what must never sync,” which is what keeps workflows stable.
Which updates should flow from Jira back to Freshdesk to keep customers informed?
There are 6 high-value Jira → Freshdesk update types: status, resolution, customer-safe summary notes, requests for information, fix/version references, and ownership signals (assignee/team) when it affects response expectations.
Then, once you limit updates to these types, support can communicate confidently without exposing internal engineering chatter.
Practical examples:
- Jira moves to “In Progress” → Freshdesk adds private note: “Engineering investigating.”
- Jira adds resolution “Fixed” + fix version → Freshdesk adds a customer-safe note with next steps.
- Jira comment requesting logs → Freshdesk creates a public reply asking the customer for logs.
Keep the customer-facing layer intentional: support should translate dev language into customer language, even when the integration carries the raw status.
Should internal Jira comments sync into Freshdesk public replies?
No—internal Jira comments should not sync into Freshdesk public replies for at least three reasons: they can leak sensitive details, they can confuse customers with jargon or uncertainty, and they can create compliance risk if internal data crosses into customer-visible channels.
Moreover, once you block internal-to-public leakage, you can still sync customer-safe summaries via a deliberate field or a curated comment rule.
A clean policy is:
- Jira internal comments → Freshdesk private notes only (if synced at all)
- Jira customer-safe update field (or labeled comments) → Freshdesk public reply candidate
This is exactly where “two-way” needs boundaries: sync should support collaboration, not replace communication discipline.
How do you handle attachments and large files across both systems?
Attachment handling works best when you choose one of two models: “copy attachments both ways for small files” or “sync links only for large/sensitive files,” because bandwidth, storage limits, and permission models differ across platforms.
Next, once you select an attachment model, you can prevent broken links and avoid duplicating sensitive data into the wrong system.
Recommended rules:
- Small files (screenshots, short logs): copy if both sides need them for triage.
- Large files (videos, dumps): store in a controlled repository and sync a link.
- Sensitive files: never auto-sync; require manual approval or a secure upload workflow.
If you do copy attachments, test edge cases: inline images, multiple attachments per reply, and attachment removal/expiry.
What field and status mapping rules make a Freshdesk–Jira sync reliable at scale?
There are 3 reliability layers for mapping rules: a status mapping matrix, a priority/severity translation model, and routing rules that land work in the right Jira project/issue type based on ticket classification.
Specifically, once these three layers are stable, you can scale the integration without turning every new field into a production risk.

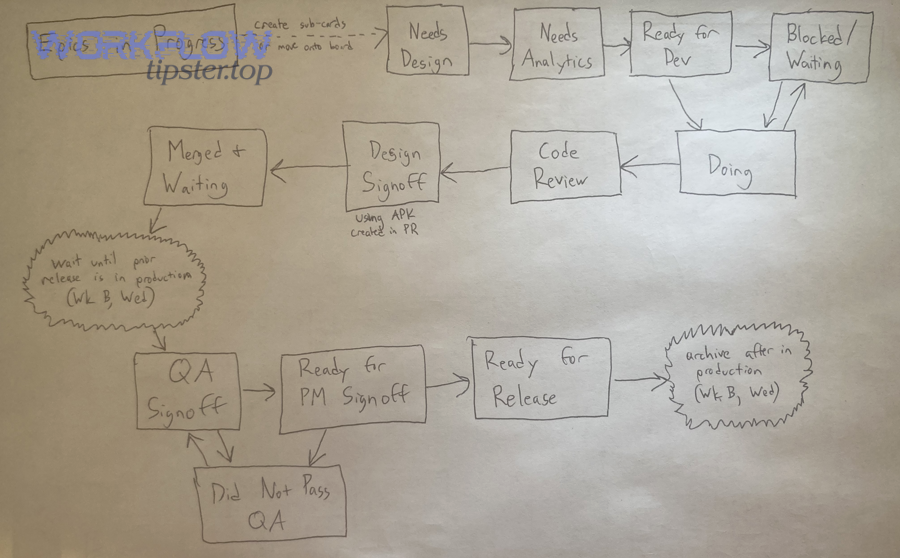
How do you create a status mapping that matches both team workflows?
A strong status mapping aligns Freshdesk customer-facing states with Jira delivery states by defining a small set of canonical phases and mapping each platform’s statuses into them.
Then, once you map into canonical phases, you avoid the trap of trying to make two different workflows identical.
This table contains a practical status mapping example to help support and engineering share meaning without forcing the same status names:
| Canonical phase | Freshdesk example | Jira example |
|---|---|---|
| Intake | New / Open | To Do / Backlog |
| Triage | In Progress (Support) | Selected for Development / Triage |
| Waiting | Pending on Customer / Pending on Third Party | Blocked / Waiting |
| Delivery | Escalated / Engineering Working | In Progress |
| Resolution | Resolved | Done / Fixed |
| Closure | Closed | Done + Released (or Closed) |
Key rules that keep this reliable:
- Decide which system owns the canonical phase transitions.
- Only sync status when a mapped transition occurs (not on every minor change).
- Keep a “manual override” path for edge cases.
How should you map priorities between customer urgency and engineering severity?
Freshdesk urgency wins for response-time decisions, Jira severity is best for engineering risk, and a combined matrix is optimal when you need both customer impact and technical impact to determine true priority.
However, once you separate urgency from severity, you can stop arguing about “P1” meaning different things in different teams.
This table contains a simple urgency × severity matrix to help translate Freshdesk signals into Jira priorities consistently:
| Customer urgency (Freshdesk) | Engineering severity (Jira) | Recommended Jira priority |
|---|---|---|
| High (VIP outage) | High (data loss / security) | Highest |
| High | Medium | High |
| Medium | High | High |
| Medium | Medium | Medium |
| Low | High | Medium |
| Low | Low | Low |
Operational guardrail: define escalation thresholds (e.g., “VIP + revenue impact” always creates a Jira issue and notifies an on-call rotation if you use JSM).
What routing rules should you use to send tickets to the right Jira project?
There are 4 main routing rule types for Freshdesk to Jira: product-based, component/tag-based, customer-tier-based, and channel/source-based routing.
Next, once routing is deterministic, your backlog stays clean and you don’t waste time reassigning issues across projects.
Examples:
- Product-based: “Mobile app” tickets → Jira project MOB; “API” tickets → API.
- Component-based: ticket tag billing → component Billing; tag login → component Auth.
- Customer-tier-based: VIP accounts → a dedicated Jira queue/project or a higher default priority.
- Channel-based: Phone escalations → higher urgency; Community posts → lower urgency unless tagged.
Keep routing rules transparent: document them in one place and update them when product ownership changes.
How do you test, monitor, and troubleshoot the integration after launch?
A strong post-launch plan uses 3 pillars—test coverage, monitoring metrics, and a troubleshooting playbook—so Freshdesk to Jira syncing stays trustworthy as workflows evolve and permissions, fields, or projects change.
Then, once you can detect failures quickly, you can fix them before they become customer-impacting delays.
What are the must-run test cases before enabling sync for all tickets?
There are 8 must-run Freshdesk to Jira test cases: ticket creation, link-back, status sync both directions, public reply vs private note handling, comment sync rules, attachment sync, permission failure handling, and duplicate prevention.
To illustrate, if any one of these fails in staging, you should treat production launch as a reliability risk.
Run tests like a checklist:
- Create a Freshdesk ticket → confirm Jira issue created in correct project/type.
- Confirm Jira key/URL appears back in Freshdesk ticket (field or private note).
- Change Freshdesk status → confirm Jira status mapping behavior (if enabled).
- Change Jira status → confirm Freshdesk update behavior (if enabled).
- Add a Freshdesk public reply → confirm Jira comment policy.
- Add a Freshdesk private note → confirm Jira comment policy.
- Attach a file → confirm copy vs link behavior.
- Trigger a permission error (remove access temporarily) → confirm graceful failure + alerting.
What are the most common sync failures and how do you fix them?
There are 7 common Freshdesk to Jira sync failures: missing required fields, mismatched field values, permission denied, project/key changes, status mapping gaps, attachment limits, and loop/duplicate triggers.
Moreover, once you categorize failures, you stop “randomly toggling settings” and start fixing the root cause.
Fast fixes by category:
- Required field missing: set defaults or map a Freshdesk field into the required Jira field.
- Value mismatch: align dropdown options (e.g., priority labels differ) or use translation rules.
- Permission denied: ensure integration user has project permission + field edit rights.
- Project moved/renamed: update routing rules and stored project keys.
- Status mapping gap: update the mapping matrix; define “unknown” handling.
- Attachment issues: switch large files to link-only; enforce size/type policies.
- Loops/duplicates: add loop prevention tags/markers; restrict which events trigger sync.
How can you monitor sync health and prevent silent failures?
Monitoring requires at least four signals: sync success rate, sync lag time, error rate by category, and backlog of queued/retried events—because “it seems fine” is not an operational metric.
In addition, once you define thresholds, you can page the right owner before customers notice.
A simple monitoring dashboard checklist:
- Success rate: % of events synced without errors (target: near 100%).
- Lag time: time from update in system A to reflection in system B.
- Error taxonomy: permissions vs field mapping vs rate limiting.
- Queue depth: number of pending retries.
- Top failing rule: the specific mapping or automation causing most errors.
Operational practice: assign an integration owner (support ops, IT ops, or platform team) with a weekly review of error patterns.
Is your Freshdesk–Jira integration secure and compliant for support & dev teams?
Yes—your Freshdesk to Jira integration can be secure and compliant when you apply at least three controls: least-privilege access, data minimization (sync only what’s necessary), and auditable change management for tokens/rules so sensitive information doesn’t cross boundaries accidentally.
Next, once security is designed into the sync, you can scale collaboration without increasing risk.
Should you restrict which fields sync to avoid leaking sensitive data?
Yes—you should restrict synced fields for at least three reasons: it reduces the chance of PII exposure, it prevents internal engineering notes from becoming customer-visible, and it improves reliability by limiting fragile mappings.
Then, once you restrict fields, you can still give engineering what it needs through structured summaries instead of raw data dumps.
Examples of fields that should usually not auto-sync:
- Payment details, ID documents, sensitive personal identifiers
- Security incident details or vulnerability reports (unless handled by a dedicated secure process)
- Internal-only operational notes that do not belong in customer communication
A safer pattern is: sync a sanitized customer-impact summary plus reproduction details, and keep sensitive artifacts in controlled systems with permissioned links.
How do you manage access, audits, and token rotation over time?
Access and audit hygiene requires a 5-part routine: dedicated integration accounts, least-privilege project permissions, documented rule changes, periodic access reviews, and scheduled credential rotation with rollback steps.
In short, once you treat the integration like production infrastructure, it stays safe even as staff and workflows change.
Practical governance:
- Use a named integration owner and a change log for mapping edits.
- Rotate credentials on a schedule (and immediately after staff changes).
- Review synced fields quarterly to confirm they still match policy and need.
- Keep an emergency “disable sync” switch documented and tested.
Evidence: According to a study by the University of California, Irvine from the Department of Informatics, in 2008, interrupted work made people compensate by working faster but resulted in more stress and higher frustration, which is why secure, reliable automation that reduces needless back-and-forth can protect both quality and team wellbeing.
Contextual Border: Up to this point, you’ve covered the core “how-to” for a stable Freshdesk ↔ Jira two-way sync. Next, you’ll move beyond the baseline into advanced edge cases, conflict control, and when manual handoff is the safer antonym to automation.
How can you handle advanced workflows and edge cases in a Freshdesk–Jira integration?
Advanced Freshdesk to Jira integrations succeed when you implement 4 edge-case controls—loop prevention, conflict resolution, scalable routing governance, and a deliberate “manual handoff” rule—so automation accelerates work instead of multiplying noise.
Below, you’ll tighten micro-level behavior that becomes critical once volume grows and multiple teams share the same integration.
How do you prevent “sync loops” and duplicate updates between Freshdesk and Jira?
Preventing loops requires at least three tactics: add an origin marker to synced updates, ignore updates that originated from the integration itself, and restrict sync triggers to meaningful state changes rather than every edit.
Then, once you eliminate loops, you can safely enable richer two-way behavior like selective comment sync.
Concrete loop-prevention patterns:
- Origin marker: add a hidden tag/flag like synced_from_jira or a custom field “Last updated by integration.”
- Ignore rule: if origin marker is present, do not re-trigger the outbound sync.
- Event filtering: sync only on status change, labeled comment types, or mapped field changes.
Duplication prevention patterns:
- Require a “unique key” mapping (Freshdesk ticket ID stored on Jira issue).
- On new creation requests, check if a Jira issue already exists for that ticket ID.
- Use deterministic routing so the same ticket can’t create issues in two projects.
What’s the best strategy for conflict resolution when both sides edit the same field?
The best strategy is field ownership: Freshdesk owns customer-facing fields (requester info, ticket status meaning), Jira owns delivery fields (fix version, sprint, technical resolution), and shared fields use precedence rules or write-protection to avoid last-write-wins chaos.
Moreover, once ownership is explicit, conflict resolution becomes predictable instead of political.
A practical conflict policy:
- Single-owner fields: only one system can update; the other can read.
- Shared fields with precedence: define “Jira wins” or “Freshdesk wins” per field.
- Human override: allow a manual override path for rare cases, logged as an audit note.
Example: “Priority” might be shared, but updates could be restricted to a single owner role (support ops or engineering triage lead) to avoid flip-flopping.
How do you route tickets across multiple Jira projects (or multiple Freshdesk brands) with clean governance?
Clean governance means using a decision tree that is simple enough to maintain: brand/product → project, component/tag → component, customer tier → priority, and region/regulatory → special handling—while keeping routing rules documented and versioned.
Next, once routing is governed, scale stops breaking your backlog hygiene.
Maintainable routing strategies:
- Use a single routing document (source of truth) and update it with ownership changes.
- Prefer a few high-signal fields over dozens of brittle rules.
- Build rules that are explainable: “If product=Mobile and tag=login, route to MOB/Auth.”
If you operate multiple Freshdesk brands:
- Normalize brand identifiers into a shared field so Jira can filter/report easily.
- Route “regulated” brands into projects with stricter permission models.
When should you avoid automation and use a manual escalation handoff instead?
You should avoid automation and use manual handoff when at least three conditions apply: the case involves sensitive/security/legal content, the ticket requires judgment-based triage, or the workflow crosses strict compliance boundaries where an automated sync could expose data or trigger the wrong response path.
In short, automation is powerful—but manual handoff is the necessary antonym when risk outweighs speed.
Typical manual-only scenarios:
- Security incidents and vulnerability disclosures
- Legal requests, subpoenas, or regulated data handling
- High-risk VIP escalations where messaging must be controlled tightly
- Ambiguous issues where the “right team” is unclear and misrouting would harm trust
If you do this well, the integration becomes a force multiplier for routine work, while humans stay responsible for edge cases that demand care.
Linked phrases used in the body: Automation Integrations, airtable to google forms, google docs to loom, Workflow Tipster.

