Automating eSignature document signing across Airtable, Microsoft Word, Box, and Dropbox Sign is the fastest way for Ops teams to turn a “ready-to-send” record into a signed agreement with consistent files, traceable statuses, and fewer manual handoffs. Introduce a new idea: once you treat the Airtable record as the “single source of truth,” every downstream step becomes predictable.
Next, many teams also want a clean path for using Dropbox Sign with Microsoft Word—because Word is where contracts and templates often start, and the Word-to-signing experience influences speed and error rates. To better understand that connection, we’ll show when Word is a creation tool, when it’s a sending tool, and how both approaches can coexist.
In addition, the workflow only stays reliable when Box storage is intentional: consistent foldering, naming, permissions, version control, and a clear “final signed artifact” location. More importantly, Box is not just “where the file lives”—it’s the backbone for access, governance, and audit readiness.
Introduce a new idea: beyond “getting it to sign,” the real win is designing automation workflows that prevent duplicates, capture status changes back into Airtable, and create a repeatable Ops pipeline that scales with volume.
What is an Airtable → Microsoft Word → Box → Dropbox Sign document signing workflow?
An Airtable → Microsoft Word → Box → Dropbox Sign workflow is an automated document lifecycle that turns structured Airtable data into a generated Word agreement, stores it in Box with predictable governance, and sends it via Dropbox Sign for electronic signatures while syncing status back to Airtable.
Specifically, this workflow works best when you treat the Airtable record as the “control panel” and everything else as an execution layer. That mindset reduces confusion because each tool plays one job: Airtable decides, Word produces, Box stores, Dropbox Sign signs, and the automation connects the chain.
What data should live in Airtable to power document signing automation?
Your Airtable base should hold the data that controls timing, templates, recipients, and proof—not the entire contract text—so your automation stays stable and easy to audit.
A practical “signing-ready” table usually includes:
- Record identity & routing
- Unique Record ID (or Airtable record ID mirror)
- Document type (NDA, MSA, offer letter, vendor form)
- Region/jurisdiction (if it changes clauses or signer order)
- Owner (Ops, Legal Ops, Sales Ops)
- Trigger & readiness fields
- Status (Draft → Review → Approved → Ready to Send → Sent → Signed)
- Approval checkbox or approver field
- “Send on” timestamp or due date
- Recipient fields
- Primary signer name/email
- Secondary signer(s) name/email (optional)
- CC recipients
- Signing order (sequential vs parallel)
- Template + document generation fields
- Template selector (Word template name or template ID)
- Merge fields (company name, address, pricing, start date, etc.)
- Box + Dropbox Sign tracking fields
- Box folder path or folder ID
- Generated document filename
- Box file link (source to sign)
- Dropbox Sign request ID
- Signing status + timestamps (sent/viewed/signed/declined/expired)
- Final signed file link (Box link)
- Audit/certificate link (if available)
Then, to keep your base clean, store “long content” (the actual Word file, signed PDF, certificate) in Box and store only the references in Airtable. That separation makes it much easier to scale and to troubleshoot because you can see whether the workflow failed at data readiness, generation, storage, or signing.
Is “eSignature” the same as “electronic signature” in this workflow?
Yes—eSignature and electronic signature are synonyms in most Ops documentation, and treating them as the same term improves clarity while still matching the language used by signing platforms.
However, the important operational nuance is not the wording but the intent capture and auditability: the workflow should reliably record who signed, when they signed, and which document version they signed. When you keep that concept consistent across Airtable, Box, and Dropbox Sign, the terminology stays stable and your internal stakeholders stop debating labels.
Can you automate eSignature document signing from Airtable without coding?
Yes, you can automate Airtable → Microsoft Word → Box → Dropbox Sign document signing without coding because (1) Airtable can trigger on record changes, (2) no-code tools can generate documents from templates, and (3) signing tools accept standardized file inputs and return status updates.
To better understand why “no-code” works here, focus on the shape of the data: if your Airtable fields are clean, your template placeholders are consistent, and your storage rules are predictable, the automation becomes configuration—not programming.

Which step is the best trigger point in Airtable for sending a signature request?
Status-change triggers win for reliability, “record enters view” is best for quick prototypes, and “manual button/approval field” is optimal for high-risk documents that need human control.
Here’s how to choose:
- Best overall (Ops scale): Status changes to “Ready to Send”
This is explicit, easy to audit, and prevents accidental sends. - Best for controlled risk: Approval field becomes true
Great when Legal Ops or Finance must approve before signature. - Best for batching: Scheduled job checks “Ready to Send” queue
Useful when you want to send at specific times or throttle volume. - Best for fast prototypes: Record enters view “To Send”
Quick to implement, but views can change accidentally.
Your “best” trigger is the one that reduces ambiguity. If a stakeholder can point to one field and say, “This is why it sent,” you’ve chosen well.
What are the minimum integrations required to make the workflow work end-to-end?
There are five core building blocks required to make the workflow function end-to-end: Airtable trigger, document template engine, file storage in Box, Dropbox Sign request creation, and status sync back to Airtable.
- Trigger: Airtable record becomes eligible (status/approval)
- Generate: Create a Word document (or convert to PDF if required by your process)
- Store: Upload the generated file to Box; return a stable file link/ID
- Send: Create the signature request in Dropbox Sign using that file
- Track: Write the request ID and status back into Airtable; update as events happen
Once those five pieces are in place, everything else (reminders, routing, approvals, retries) becomes an optimization layer rather than a requirement.
How do you build the workflow step-by-step for Ops teams?
Build the workflow using a “single-source Airtable record” method in 8 steps to produce a generated agreement, store it in Box, send it for signature in Dropbox Sign, and synchronize outcomes back into Airtable.
Then, instead of trying to automate everything at once, design your workflow like a checklist: validate input, generate output, store output, send output, and track output. That progression makes failures obvious and keeps Ops ownership clear.

How do you generate a Microsoft Word document from Airtable data?
To generate a Microsoft Word document from Airtable data, use a template-first approach: create a Word template with placeholders, map Airtable fields to those placeholders, then output a new document named with a consistent convention.
Start with the template because it creates stability:
- Template strategy
- Keep one “master template” per document type.
- Avoid manual formatting in placeholder areas; let the template handle layout.
- Create a clear naming scheme:
DocType_Company_YYYY-MM-DD_RecordID.docx.
- Field mapping strategy
- Map only fields that are truly variable (names, dates, amounts, addresses).
- Use safe defaults (blank strings) for optional fields.
- Validate “must-have” fields before generation (no signer email = no generate).
- Quality guardrails
- Include a “Preview URL” or “Generated Document Link” field in Airtable.
- Add a “Template Version” field so you can trace which template produced which file.
- Keep a “Generation timestamp” for troubleshooting.
This is where many teams also link parallel automation patterns in their organization. For example, the same discipline that makes document generation reliable is what makes calendly to google calendar to microsoft teams to basecamp scheduling work smoothly: consistent inputs, stable naming, and clear ownership across steps.
How do you store the generated Word file in Box in a consistent way?
To store the generated Word file in Box consistently, upload it to a dedicated folder structure that matches your Airtable record taxonomy and returns a permanent file ID or link back to Airtable.
A clean Box strategy includes:
- Folder structure:
/Agreements/<Year>/<DocType>/<Client or Vendor>/<RecordID>/ - Filename convention:
NDA_AcmeCo_2026-02-02_AT-2381_v1.docx - Permissions rule:
Only the automation identity and the Ops/legal group should have write access; others should be view-only.
Version control matters because contracts change. If your team uploads multiple iterations, Box versions can preserve that history. For instance, Cornell’s Box guidance notes that Box keeps the most recent 100 versions of each file in their environment, which is a useful mental model for version governance even if your enterprise settings differ.
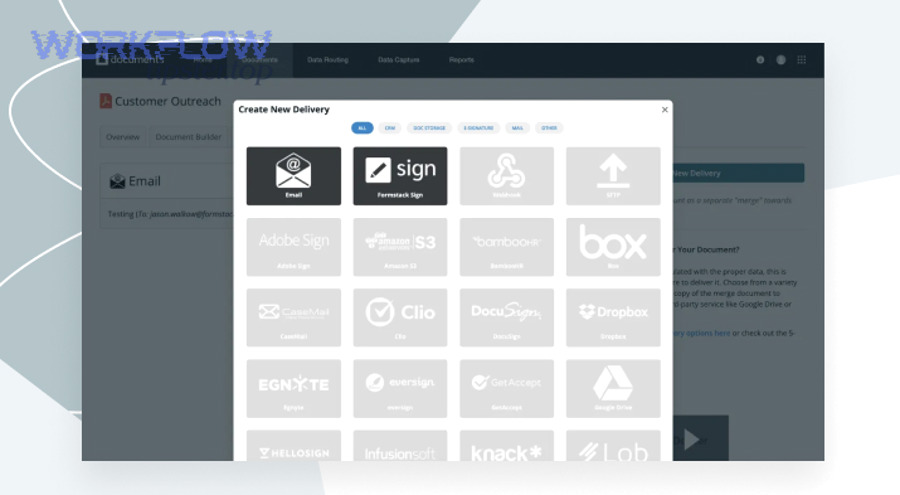
How do you send a Dropbox Sign signature request using the Box-stored document?
To send a Dropbox Sign signature request using the Box-stored document, you upload or reference the stored file, assign signer roles and fields, set signing order, and send the request while saving the request ID back to Airtable for tracking.
At the operational level, you want the signing request to be as “self-driving” as possible:
- Clear subject line: includes doc type + company + reference ID
- Short message: tells signers what to do and when it’s due
- Roles: signer, approver, CC recipients
- Reminders: automated nudges, not manual follow-up
If your team uses the Microsoft Word add-in as part of the sending experience, Dropbox’s help documentation describes the Word add-in workflow and options like Self-Sign and Send for Signature.
According to a study by Pepperdine University from the Information Technology division, in 2016, users sent more than 275 documents with an average turnaround time of 19 minutes after adopting automated e-signature workflows.
What are the key signer roles and fields you must map to Dropbox Sign?
There are three main role-and-field groups you must map to Dropbox Sign—signers, document fields, and delivery controls—based on who must sign, what they must fill, and how the request should be routed and tracked.
Next, mapping becomes much easier when you treat it as a contract “interface” layer: your Airtable record defines the roles and values, and Dropbox Sign enforces completion and timestamps.

What should you include in a signing request to reduce delays and rework?
To reduce delays and rework, include a signer-ready payload that removes uncertainty, prevents missing fields, and makes the next step obvious.
A strong request includes:
- Signer clarity
- Exact legal name (as it should appear on the agreement)
- Email address verified (no aliases unless your org supports them)
- Signer title (optional but helpful for business agreements)
- Document clarity
- Doc type + reference ID in the subject line
- Due date (or an internal SLA)
- Short instructions: “Please review Section 3 and sign by Friday.”
- Field completeness
- Required signature fields
- Date fields (auto-populated when possible)
- Text fields mapped from Airtable (company name, address, pricing)
- Operational controls
- CC legal ops or records mailbox (if your policy requires it)
- Reminders (e.g., day 2 and day 5)
- Expiration policy (if applicable)
This is also where you can draw consistency from other automation playbooks in your organization. If your team already runs freshdesk ticket to linear task to discord support triage, you know the pattern: clear owner, clear payload, clear next action—so nothing gets stuck waiting for a human to interpret intent.
How do you handle multiple signers vs single signer flows?
Single-signer flows win in speed, multi-signer sequential flows are best for compliance and clarity, and multi-signer parallel flows are optimal when independent approvals can happen at the same time.
In practice:
- Single signer
- Fastest turnaround
- Simplest mapping
- Least operational overhead
- Multiple signers (sequential)
- Best when signing order matters (e.g., internal approver signs before external signer)
- Reduces conflict (“who signs first?”)
- Can extend timeline if one signer delays
- Multiple signers (parallel)
- Best when signatures are independent
- Improves speed for multi-party agreements
- Requires clearer messaging (“Please sign; others are signing too.”)
Ops teams usually choose sequential signing when risk is higher and parallel signing when speed is the priority.
How do you track Dropbox Sign status back into Airtable?
To track Dropbox Sign status back into Airtable, capture the signature request ID, listen for status changes (sent/viewed/signed/declined/expired), and write those events into Airtable fields so the record becomes the live dashboard for the agreement lifecycle.
Specifically, status tracking is what turns a “send step” into an “Ops process.” If you only send and never track, you force manual follow-up. If you track and timestamp, you can measure cycle time and improve it.
Which Airtable status model works best for a signing pipeline?
A “stage + substatus” model wins for visibility, a “simple status” model is best for lightweight workflows, and a “stage + SLA timestamps” model is optimal for mature Ops teams that manage throughput.
Compare them like this:
- Simple status model
- Fields: Draft → Ready → Sent → Signed
- Best for low volume, low compliance risk
- Limits troubleshooting detail
- Stage + substatus model
- Fields: Sent + (Viewed / Waiting on Signer / Waiting on Internal)
- Best for mid-to-high volume
- Improves follow-up precision
- Stage + SLA timestamps
- Fields: SentAt, ViewedAt, SignedAt, LastReminderAt
- Best for teams who measure throughput and enforce timelines
- Enables analytics like “average time to sign by doc type”
The best model is the one that matches your decision-making rhythm: if you need to know “what’s blocking signing today,” you need substatus or timestamps.
What artifacts should be stored after signing is complete?
There are five artifacts you should store after signing is complete: the final signed document, the audit/certificate trail, the final Box link, the signer metadata, and the completion timestamps—so you can prove what happened without rebuilding the story later.
A practical post-signing checklist:
- Signed PDF saved to Box in the same record folder
- Audit trail / certificate stored next to the signed PDF
- Airtable links updated:
SignedFileURL,CompletedAt,SignerEmails - Record locked (optional): prevent edits that create mismatch after signing
- Notifications sent to stakeholders (Ops, requester, legal ops)
This is also the moment to standardize language in the base: keep “Signed,” “Completed,” and “Executed” aligned so your reporting doesn’t split one outcome into three labels.
What are the most common failure points in this workflow and how do you fix them?
There are six common failure points in Airtable → Word → Box → Dropbox Sign automation—missing fields, template mismatches, file access issues, broken links, duplicate triggers, and status sync gaps—and each can be fixed by adding validation, stable IDs, and run-once logic.
Next, think like an Ops debugger: every failure should map to one layer—data, document, storage, signing, or tracking—so you can isolate issues in minutes instead of hours.
Why do signing requests fail because of file access or permissions?
Signing requests fail because of file access or permissions when the automation identity can’t read the Box file, the shared link expires or is restricted, or the file lives in a folder with mismatched access controls between teams.
Fix this with a permissions “golden rule”:
- The automation identity must have read access to the exact file it sends.
- The signing process must use a stable file reference (ID or permanent link), not a temporary URL.
- The Ops/Legal group should control folder permissions so individual users can’t break access accidentally.
How do you prevent duplicate signature requests from the same Airtable record?
Prevent duplicates by using an idempotent “send-once” design: only send when the record has no request ID, lock the record after sending, and block reruns unless a human explicitly resets the state.
A robust duplicate-prevention pattern includes:
- Before sending
- If
DropboxSignRequestIDis not empty → do not send - If
Statusis not “Ready to Send” → do not send - If required fields are missing → do not send, write error back to Airtable
- If
- After sending
- Write
DropboxSignRequestID - Set
Status = Sent - Set
SentAt = now() - Optionally set
SendLock = true
- Write
- Reset process
- Only a human can clear
DropboxSignRequestID - Require a reason field (“Why resending?”)
- Store prior request IDs in a history field
- Only a human can clear
This same “send-once” pattern is why parallel document flows remain stable, including airtable to microsoft excel to dropbox to dropbox sign document signing—because the core risk is identical: triggers fire twice unless you enforce state.
Is this workflow secure enough for contracts and internal approvals?
Yes, this workflow can be secure enough for contracts and internal approvals because (1) access can be restricted by least privilege across Airtable, Box, and Dropbox Sign, (2) signing events can be audited with timestamps and artifacts, and (3) storage governance can preserve integrity and traceability.
Besides security settings, the most important part is operational: you must ensure the signer receives the correct file and you retain proof of what was signed. That is what makes the workflow defensible when stakeholders ask for evidence.
What permissions should Ops teams set in Airtable, Box, and Dropbox Sign?
There are three permission layers Ops teams should set—record permissions, file permissions, and signing permissions—based on who can trigger, who can edit, and who can access signed artifacts.
- Airtable permissions
- Ops: edit status and recipient fields
- Legal/Approvers: approve fields only (or controlled views)
- Viewers: read-only access to status and links
- Box permissions
- Automation identity: uploader and reader (minimum necessary)
- Ops/Legal: editor access in agreement folders
- Broad stakeholders: viewer access only
- External parties: avoid giving Box access unless required; use signing platform delivery
- Dropbox Sign permissions
- Limit who can create/send requests (team roles)
- Restrict template editing to admins (if using templates)
- Enforce authentication or access controls where appropriate
The best permission model is the one that prevents accidental edits at the moment the contract becomes “signing-ready.”
When should you use approval gates before sending to signature?
Approval gates win when risk is high, auto-send wins when speed is the priority, and a hybrid gate is optimal when you want speed with a lightweight control.
Use approval gates when:
- Contract value is high
- Terms vary per deal
- Compliance requires documented internal approval
- Signer list changes frequently
Use auto-send when:
- Document is standardized (template)
- Terms do not change
- Speed drives value (e.g., onboarding forms)
Use a hybrid gate when:
- Most contracts are standard, but some need review (e.g., gate only triggers when “Non-standard terms = Yes”)
What advanced variations and alternatives improve Airtable → Word → Box → Dropbox Sign automation?
There are four advanced variations that improve this automation—Word add-in sending, conditional routing, version-locking in Box, and embedded signing—based on whether you optimize for speed, governance, or completion rate.
Next, these upgrades matter because they let you handle real-world complexity without breaking the core workflow: a contract isn’t just “generated and signed,” it’s routed, governed, and proven.
Should Ops teams use the Dropbox Sign Microsoft Word add-in instead of an automated Word generation step?
Automated generation wins in scalability, the Word add-in is best for ad-hoc documents, and a hybrid approach is optimal when Ops needs both templated speed and occasional human-crafted contracts.
- Choose automated generation when:
- You need consistent documents at scale
- Data already lives in Airtable
- You want predictable filenames, folders, and statuses
- Choose the Word add-in when:
- A person writes or heavily edits the document manually
- The contract is unique and not template-friendly
- The sender wants to stay inside Word for speed
In a mature Ops environment, both approaches can coexist: automated generation handles standardized agreements, while the Word add-in supports exceptions that still need a fast “send-for-signature” path.
How can you route documents by type, region, or signer order without breaking the workflow?
Route documents safely by using a controlled routing matrix that maps document type + region + risk level to template choice, Box folder rules, and signer order rules.
A simple routing matrix might include:
- DocType → TemplateID
- Region → Clause set or appendix
- RiskLevel → Approval gate required?
- Signer order → Sequential vs parallel
- Box destination → Folder path format
To keep it stable:
- Store routing rules in a dedicated Airtable “Config” table
- Reference rules by ID (not free-text)
- Default to a safe path (e.g., “Needs Review”) when rules don’t match
This turns complexity into structured configuration—and keeps the workflow explainable.
What is the best way to version-lock the document in Box so the signed file matches what was sent?
Version-locking is best achieved by storing the exact Box file ID/version reference at send time, preventing edits after sending, and saving the signed output as a separate final file in the same record folder.
A strong version-lock pattern:
- Upload generated doc to Box → get FileID
- Save FileID to Airtable
- Send for signature using that FileID (or a stable export)
- Set record to “Sent” and restrict edits to generation fields
- Save signed PDF as Final_Signed.pdf (new file) to Box
- Store final file link back to Airtable
When should you use embedded signing instead of email-based signing?
Email-based signing wins for simplicity, embedded signing is best for controlled user experiences (portals and internal apps), and a hybrid approach is optimal when internal users sign in-app while external users sign by email.
Use embedded signing when:
- You have an authenticated portal
- You want higher completion rates with fewer context switches
- You need tighter control over the signing journey
Use email signing when:
- External parties are involved
- You want the lowest friction setup
- You don’t control the signer’s environment
The “best” choice depends on where you already run work. If your organization is building central hubs for operations, embedded signing may fit naturally; if your contracts are mostly external, email-based signing keeps adoption smooth.

