If you want a workflow that turns structured Airtable records into a signable document, stores it correctly, and gets it signed without manual chasing, the Airtable → Microsoft Excel → Dropbox → Dropbox Sign chain is one of the most reliable patterns for Ops teams managing repeating agreements.
Next, once the workflow chain is clear, the biggest success factor becomes data readiness: Airtable must contain the exact fields and validations needed to generate the right Excel output every time—because a signing workflow is only as clean as the record that triggers it.
Besides, you also need the storage and signing layer to behave predictably: Dropbox must hold the “single source of file truth,” and Dropbox Sign must send the right file to the right people with a trackable status that your team can trust.
Introduce a new idea: when you connect these layers into one of your automation workflows, you’re not just “sending documents for signature”—you’re building an operational system that reduces rework, prevents duplicates, and creates an audit-friendly trail from record → file → signature outcome.
What is an Airtable → Excel → Dropbox → Dropbox Sign document signing workflow?
An Airtable → Excel → Dropbox → Dropbox Sign document signing workflow is an end-to-end, no-code process that turns Airtable records into an Excel document, stores it in Dropbox, and routes it through Dropbox Sign for legally binding eSignatures with trackable status updates.
Then, to make that definition practical, it helps to see the workflow as a single chain with four connected outcomes:
- Airtable (System of record): holds the source data (customer, pricing, dates, signer details, approval flags).
- Microsoft Excel (Document artifact): generates a structured file that reflects the record at the moment of sending.
- Dropbox (File system of record): stores the file with consistent naming, versions, and permissions.
- Dropbox Sign (Signature execution): sends the request, collects signatures, and returns completion evidence.


To illustrate why this chain matters, compare it to the common “email attachments + reminders” approach: the manual method usually creates multiple file versions, unclear ownership, and missing evidence when you need to prove what was sent and when. In contrast, a well-designed workflow chain creates a repeatable system where each link strengthens the next one—data quality improves the file, the file structure improves the signing request, and the signing status improves follow-up.
According to a study by Université de Montréal (Centre Hospitalier de l’Université de Montréal), Département de Radiologie, in 2003, electronic signature reduced median time from transcription to final signature from 11 days to 3 days for abdominal ultrasound reports and from 10 days to 5 days for chest radiographs.
What data do you need in Airtable to generate a signable Excel document reliably?
You need six core data groups in Airtable—Signer, Document, Business Terms, Workflow Control, Storage Metadata, and Audit Metadata—because each group maps to a required step in Excel generation, Dropbox storage, and Dropbox Sign execution.
Next, the goal is not “more fields”—the goal is predictable outputs. A signing workflow breaks when Airtable allows incomplete or inconsistent records to trigger automation.
Here is a practical grouping that keeps your pipeline stable:
Which Airtable fields are mandatory for creating the Excel file?
Yes—your Airtable record can generate a reliable signable Excel file if it includes mandatory document and signer fields, because (1) Excel generation needs complete inputs, (2) Dropbox storage needs stable identifiers, and (3) Dropbox Sign needs valid recipients and roles.
Then, to keep the workflow chain consistent, treat these as “must not be blank” fields:
1) Signer identity fields (required for sending)
- Signer full name
- Signer email
- Signer role (e.g., Client, Manager, Legal)
- Signing order (if sequential routing)
2) Document identity fields (required for naming + traceability)
- Document type (e.g., NDA, SOW, Offer Letter)
- Record/Deal/Contract ID (unique)
- Customer/Company name
- Effective date (or sent date)
3) Business terms fields (required for content accuracy)
- Pricing / totals (currency)
- Term length
- Start/end dates
- Line items (if applicable)
4) Excel template mapping fields (required for consistent formatting)
- Template ID or template version
- Output language (if you localize)
- Optional: “Locked version” checkbox (more on versioning later)
5) Dropbox storage fields (required for folder routing)
- Dropbox folder path or folder key
- File naming token(s) (Customer + DocType + RecordID)
- Optional: “Signed folder path” (separate destination)
6) Workflow control fields (required to prevent chaos)
- Workflow status (Draft → Ready → Sent → Signed)
- “Ready to send” boolean (or approval checkbox)
- Signature Request ID (blank until created)
- Last sent timestamp
More specifically, the fastest way to remove failures is to use Airtable validations: required fields, single select enums for status, and formula checks that show a “Missing Requirements” warning.
How should you structure records to avoid missing or duplicated signing requests?
You should structure Airtable records around a single “send gate” and a single “identity key” because it prevents accidental re-runs, ensures idempotency, and makes status syncing back from Dropbox Sign unambiguous.
Next, adopt a structure that makes duplicates hard to create:
- One trigger condition: Status changes to “Ready to Send” (or a checkbox is turned on).
- One identity key: A unique Contract ID or Record ID that never changes.
- One request tracker: Signature Request ID field that is written once and then used for all updates.
To illustrate, a clean base often includes:
- Table A (Agreements): core agreement record, signer links, totals, status
- Table B (Contacts): normalized signer info
- Table C (Line Items): repeating pricing rows (optional)
When you link those tables, your Excel generation becomes stable: the workflow reads the agreement record, expands line items into rows, and produces the same spreadsheet structure every time.
How do you automate exporting Airtable data into a Microsoft Excel file?
Automate Airtable-to-Excel generation using a 5-step method—validate the record, select a template, map fields, generate the XLSX, and log the output—so you consistently produce a signable Excel file that matches the Airtable record at send time.
Then, the most important principle is this: Excel should be an artifact, not the source of truth. Airtable remains the system of record; Excel is the generated “snapshot.”

Here’s a practical no-code approach used in many automation workflows:
- Validate record readiness
- Confirm required fields exist (name, email, totals, ID)
- Confirm status is “Ready to Send”
- Confirm no Signature Request ID exists yet
- Select an Excel template
- Choose a fixed template file (stored in Dropbox or template repository)
- Decide the mapping model (cell-based, table-based)
- Map Airtable fields into the template
- Map header values (customer name, dates, totals)
- Map table rows (line items)
- Apply formatting rules
- Generate the Excel file
- Output XLSX (not CSV) when formatting matters
- Confirm row counts and totals
- Write back output metadata
- Store Dropbox file path/link
- Store generated file name
- Store generation timestamp and template version
What is the best way to create an Excel template for repeatable document signing?
The best way is to create a template with stable headers, controlled input zones, and predictable tables because automation tools can map data reliably only when the spreadsheet structure does not change unexpectedly.
Then, design your template with these practical rules:
- Keep headers fixed (don’t rename columns once automation is live)
- Use one “Data” sheet that automation fills
- Use protected formulas in a separate “Summary” sheet
- Use consistent number/date formats (currency, ISO dates when possible)
- Reserve a “Metadata block” (RecordID, TemplateVersion, GeneratedTimestamp)
To better understand why this matters, imagine a template where someone inserts a new column “just to help.” That change can shift every mapped field and silently create wrong values—which is the worst failure mode in document signing.
What are the common formatting issues when generating Excel files from Airtable data?
The most common issues are broken dates, currency formatting errors, leading-zero loss in IDs, and line-item row overflow—because automation layers often treat values as plain text until formatting rules are explicitly enforced.
Next, address these issues before production:
- Dates: Use a consistent output format (e.g., YYYY-MM-DD) unless the template forces a local format.
- Currency: Ensure numeric values are sent as numbers, not strings; lock currency symbol in the template.
- IDs: Store certain IDs as text in Excel to prevent leading zeros from disappearing.
- Long text fields: Set cell wrapping; define max lengths if needed.
- Line items: If you can have 100+ items, design the table to expand (or create a second sheet for overflow).
According to a study by Université de Montréal (Centre Hospitalier de l’Université de Montréal), Département de Radiologie, in 2003, electronic signature increased the proportion of finalized abdominal ultrasound reports at 3 days from 8.8% to 44.8% after implementation, showing how workflow design choices can materially change completion speed.
How do you store the Excel document in Dropbox so it stays organized and traceable?
Store the generated Excel document in Dropbox using a 3-layer structure—a consistent folder taxonomy, a deterministic file naming standard, and controlled permissions—so every file can be found, verified, and reused as evidence.
Then, to keep the workflow chain tight, treat Dropbox as your file system of record, not “just a place to upload.”

When you store files inconsistently, you create operational debt: the team wastes time searching, duplicates files, and cannot confidently answer, “Which version did we send for signature?”
Which Dropbox folder structure works best for Ops teams managing many contracts?
A client-first folder structure works best for most Ops teams because it mirrors how teams search in real life and allows clean separation of drafts, sent files, and signed evidence.
Next, use a structure like this (adapt to your business model):
- /Contracts/{ClientName}/Drafts/
- /Contracts/{ClientName}/Sent/
- /Contracts/{ClientName}/Signed/
- /Contracts/{ClientName}/Evidence/ (audit trail, completion certificates, logs)
If your business is project-based, add one more layer:
- /Contracts/{ClientName}/{ProjectOrDealID}/Sent/
- /Contracts/{ClientName}/{ProjectOrDealID}/Signed/
More importantly, ensure the automation writes the Dropbox path back to Airtable so Airtable can always point back to the file location (and not rely on memory or inbox hunting).
How should you name files to prevent version confusion during signing?
You should name files using a deterministic naming formula because it prevents collisions, supports quick identification, and enables clean versioning when the record changes.
Then, use a naming convention like:
{ClientName} – {DocType} – {RecordID} – {YYYY-MM-DD} – v{Version}.xlsx
Examples:
- Acme – SOW – SOW-1042 – 2026-02-02 – v1.xlsx
- Acme – SOW – SOW-1042 – 2026-02-03 – v2.xlsx
To illustrate why versioning must be explicit: signing the wrong version is not just embarrassing—it can create real risk if terms changed. The naming convention becomes the first safety layer, and the workflow status logic becomes the second safety layer.
How do you send the Dropbox file to Dropbox Sign for document signing?
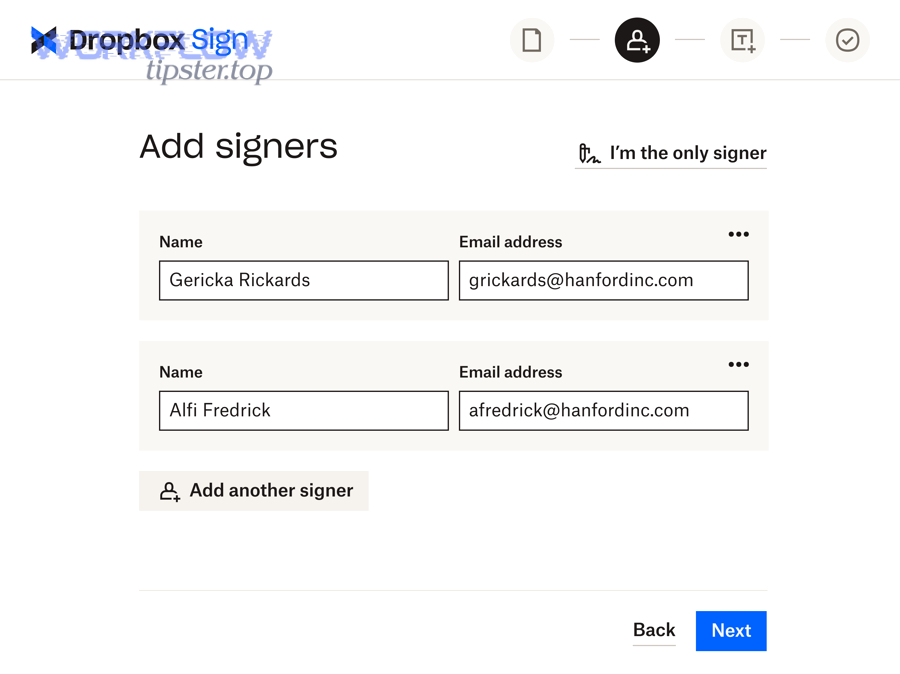
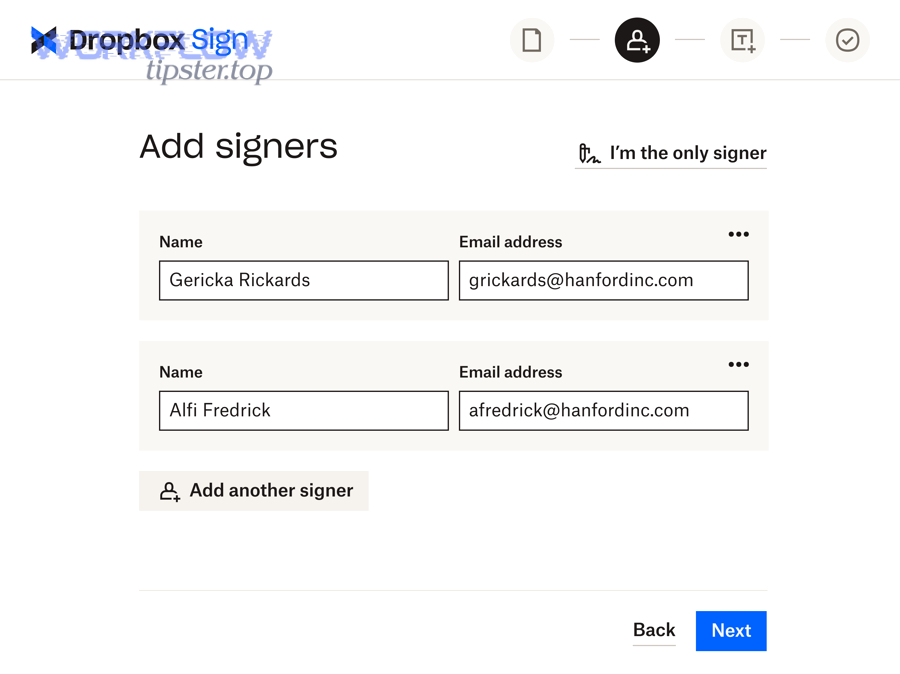
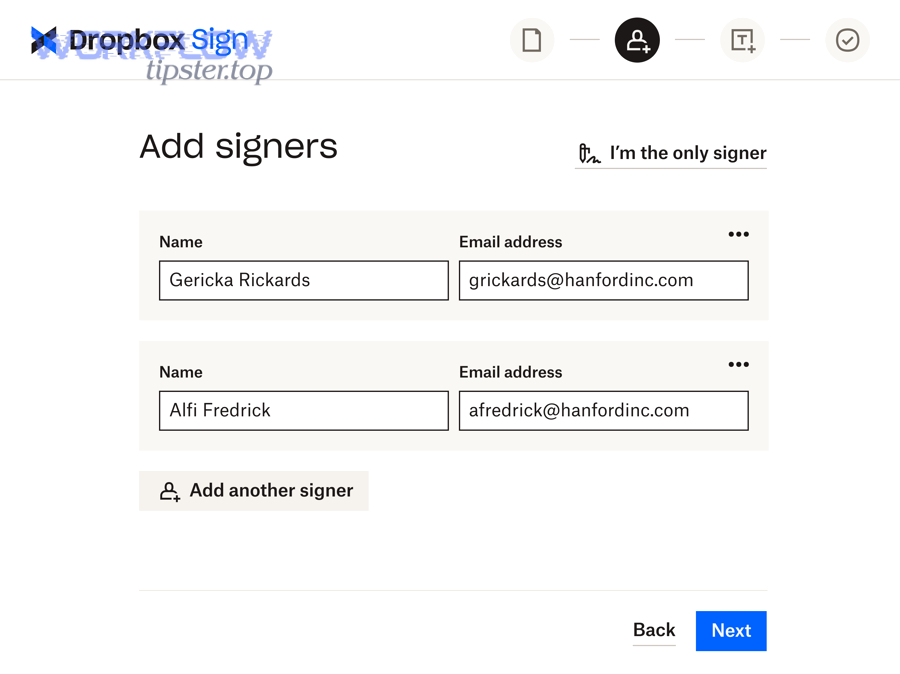
Send the Dropbox file to Dropbox Sign using a 4-step method—prepare the file, assign roles and recipients, configure signing order and reminders, and send the signature request—so the right document reaches the right signer with trackable progress.
Then, your success depends on one operational question: Are you sending a controlled document version with controlled recipient logic? If yes, the rest becomes manageable.

To better understand the sending mechanics, it helps to see the request as a structured object:
- File (the Excel document, or a converted PDF if needed)
- Recipients (emails + names)
- Roles (who signs vs who receives a copy)
- Routing (sequential vs parallel)
- Notifications (reminders, expiration)
Here’s one helpful reference on the mechanics of sending signature requests.
Should you use a Dropbox Sign template or upload the generated Excel file each time?
A Dropbox Sign template wins for consistency, while file upload is best for flexibility, and native “convert-to-PDF first” is optimal when signer experience and field placement must be perfect across devices.
Then, choose based on the stability of your document:
Use a template when:
- The document structure is stable
- You rely on consistent signature fields and roles
- You want fewer mapping errors over time
Upload the generated file when:
- The spreadsheet is truly unique per record
- You embed all values directly into the sheet
- You accept that field placement may need careful handling
Convert to PDF before sending when:
- You want the signer to see a fixed layout
- You need predictable field positioning
- You want fewer “Excel rendering” differences on devices
This is also where your “alternate workflow phrases” can be applied naturally: if your organization already runs airtable to microsoft excel to onedrive to pandadoc document signing, the same decision logic applies—template stability vs file uniqueness—just with different storage and signature endpoints.
How do you map Airtable fields to Dropbox Sign fields without breaking the template?
You map Airtable fields to Dropbox Sign fields by enforcing a stable field schema (names, types, required rules) and testing with representative records, because template-based signing breaks when a required field is missing or a field type changes silently.
Next, apply a safe mapping workflow:
- Define a field contract
- Required fields must exist
- Types must remain stable (date, number, text)
- Enumerations must remain in allowed values
- Map fields intentionally
- Map signer name/email into recipient roles
- Map text fields into template variables
- Map totals/dates into visible fields (or into document content)
- Test across edge cases
- Long names
- Missing optional line items
- International number formats
- Multiple signers
- Create a rollback plan
- If mapping fails, set Airtable status to “Error”
- Notify Ops owner with a clear error reason
- Do not send partial/incorrect documents
How do you track signing status and write results back to Airtable?
Track signing status by storing the Signature Request ID in Airtable, updating status via event callbacks or scheduled checks, and writing back the signed file link and timestamps so Ops can manage follow-up from a single dashboard instead of inbox threads.
Then, to reconnect the workflow chain, remember the purpose: Airtable must remain the operational cockpit where the team can answer, “What’s signed, what’s stuck, and what needs attention?”
This “closed-loop” approach typically includes:
- Request created → Airtable stores Request ID
- Request sent → Airtable status changes to Sent
- Viewed/Signed/Declined/Expired → Airtable updates status and timestamps
- Signed output stored → Airtable stores Dropbox link(s)
What signing statuses should you track in Airtable for full visibility?
There are seven core signing statuses you should track—Draft, Ready, Sent, Viewed, Signed, Declined, and Expired—based on the operational question “what should Ops do next?”
Next, make each status actionable by adding supporting fields:
- Draft: record not approved; missing requirements list
- Ready: approved and valid; waiting to send
- Sent: request created; store Request ID + sent timestamp
- Viewed: signer opened; optional “last viewed” timestamp
- Signed: completed; store signed file link + completion timestamp
- Declined: store decline reason; route to “Fix & resend”
- Expired: store expiration date; route to “Renew & resend”
To illustrate how this reduces chaos: instead of “Where is that contract?”, your team sees a single row that answers it immediately.
How do you store signed files and evidence so audits are easy?
You store signed files and evidence by saving (1) the final signed document, (2) the audit trail or completion certificate, and (3) the request metadata in predictable Dropbox folders, because audits require proof of who signed what, when, and under what version.
Next, store outputs like this:
- Signed document → /Signed/
- Evidence packet / audit trail → /Evidence/
- Optional: JSON/event log exports → /Evidence/Logs/
In practice, write back to Airtable:
- Signed file Dropbox link
- Evidence packet Dropbox link
- Completion timestamp
- Request ID
- Final version number
According to a report by the University of South Carolina Faculty & Staff IT Advisory Committee, in 2017, the university highlighted e-signature as effective for improving efficiency and reducing costs in business processes, emphasizing the operational value of digitized signing and workflow capabilities.
How do you choose between Zapier and Make for this workflow?
Zapier wins in speed-to-launch and simplicity, Make is best for complex branching and robust data shaping, and native integrations are optimal when you need deep control and custom reliability at higher volumes.
Then, to keep your decision grounded, use your workflow chain requirements as the evaluation criteria: data transformations, file generation, branching, retries, and observability.

A practical comparison table helps—this table summarizes what each tool is typically best at in document signing automation workflows:
| Criterion | Zapier | Make | Native / custom |
|---|---|---|---|
| Setup speed | Very fast | Fast–moderate | Slow |
| Complex branching | Moderate | Strong | Strongest |
| Data shaping | Basic–moderate | Strong | Strongest |
| Error handling | Good | Very good | Customizable |
| Scale control | Moderate | Better control | Best control |
| Maintenance effort | Low | Moderate | Higher |
Is Zapier or Make better for multi-step document signing automation workflows?
Zapier is better when the workflow is mostly linear and the team values speed, while Make is better when you need branching, multi-record mapping, and stronger control over complex document generation paths.
Next, use these decision cues:
Choose Zapier if:
- You have a straightforward chain (one record → one file → one request)
- You want quick iteration and low maintenance
- You prefer fewer moving parts
Choose Make if:
- You need conditional routing (different signers by record fields)
- You need advanced mapping (line items, loops, aggregations)
- You want more explicit scenario design and logging
This is where it’s natural to connect to your other operational chains: for example, teams that already run airtable to microsoft word to google drive to pandadoc document signing often prefer Make when they need advanced document assembly logic, while Zapier is often chosen for faster deployment and simpler handoffs.
What are the most common failure points and how do you prevent them?
Yes—most Airtable → Excel → Dropbox → Dropbox Sign failures are preventable because they usually come from (1) missing required data, (2) file generation errors, and (3) permission or duplication issues, and each has a clear mitigation pattern.
Then, prevent failures by designing guardrails into the workflow chain:
Failure point 1: Missing or invalid signer details
- Prevention: validation checks before sending
- Mitigation: set status to “Error – Missing signer”
Failure point 2: Excel generation produces blank or misformatted outputs
- Prevention: template contract + test records + formatting rules
- Mitigation: log the generated file and stop before sending
Failure point 3: Dropbox permission errors
- Prevention: service account access, folder-level permissions, predictable paths
- Mitigation: retry with backoff, notify Ops owner
Failure point 4: Duplicate requests
- Prevention: store and check Signature Request ID
- Mitigation: idempotency rules (block repeats)
Failure point 5: Status never updates
- Prevention: scheduled polling + event callbacks where possible
- Mitigation: alert if status unchanged after X hours
Besides, remember that not all automation workflows are “document workflows.” If your team also runs github to jira to google chat devops alerts, you already understand the same principle: reliability comes from strong triggers, clean IDs, and observable status changes—not from manual checking.
According to a study by Université de Montréal (Centre Hospitalier de l’Université de Montréal), Département de Radiologie, in 2003, electronic signature shifted report finalization toward the first two days after transcription, demonstrating how small workflow design changes can materially accelerate completion and reduce operational lag.
What advanced patterns make Airtable → Excel → Dropbox → Dropbox Sign workflows more reliable at scale?
There are four advanced reliability patterns—idempotency, version control, conditional routing, and governance/audit design—based on the criterion of “what breaks first when volume, complexity, and compliance requirements increase.”
Next, these patterns matter because scaling doesn’t just mean “more documents.” Scaling usually means:
- More signers
- More exceptions
- More re-sends
- More audits
- More handoffs across teams

How can you prevent duplicate signature requests (idempotency) when automations re-run?
You prevent duplicate signature requests by enforcing a single “request creation lock” using a unique Request ID and a status transition rule, because idempotency ensures the same record cannot create two signature requests accidentally.
Then, apply this pattern:
- Before creating a request: check if Signature Request ID is blank
- If blank: create request → write Request ID immediately
- If not blank: skip creation → only update status or resend intentionally
To illustrate, treat the Request ID as the “receipt” that proves the request exists. Without it, your workflow can re-fire from retries, edits, or human toggles.
What is the best way to handle document versioning when Airtable data changes after sending?
The best way is to treat sent documents as immutable and create a new version when terms change, because “mutable vs immutable” is the key antonym pair that protects you from signing the wrong content.
Next, implement version control like this:
- If status is Sent and a critical field changes (price, term, scope):
- Set status to Needs Reissue
- Create v2 Excel file
- Cancel or expire the prior signature request (process depends on your controls)
- Send a new request linked to the new version
- Preserve the old version in /Sent/ for traceability
This makes your audit story clean: each version has a timestamp, a file, and a signature outcome.
How do you handle multi-signer and conditional routing scenarios for different contract types?
You handle multi-signer and conditional routing by using role-based recipient logic and explicit signing order rules, because “one-size-fits-all” routing breaks as soon as a document type requires different approvals.
Next, scale routing with these patterns:
- Role-based mapping: Assign recipients by role (Client, Internal Approver, Legal)
- Conditional logic: If DealSize > X → add Finance Approver
- Sequential vs parallel:
- Sequential for approvals that must happen in order
- Parallel when signers can sign independently
A practical Ops-friendly approach is to store routing in Airtable as fields:
- Approver 1 email
- Approver 2 email (optional)
- Signing order values (1, 2, 3)
What governance and audit trail practices should Ops teams follow for eSignature evidence?
Ops teams should follow governance practices that ensure (1) integrity of the signed version, (2) controlled access to evidence, and (3) retention policies aligned with business and legal needs, because audit readiness is built before you need it—not after.
Then, apply these governance standards:
- Access control: limit who can edit /Sent/ and /Evidence/
- Separation of concerns: store drafts separately from signed outcomes
- Retention rules: define how long to keep evidence packets and logs
- Traceability fields in Airtable: Request ID, version, timestamps, links
- Periodic audits: sample a set of signed agreements and verify evidence completeness
If you want a concrete model, the University of Colorado Boulder case study reported measurable outcomes from digitizing agreement workflows, including cost reductions and faster completion of document-based requests, illustrating how governance plus process redesign can produce scalable operational benefits.

