If you want faster deal cycles, fewer handoffs, and cleaner compliance, you can automate an Airtable → DocSend → Dropbox → Dropbox Sign document signing flow by designing a stable Airtable data model, standardizing document versions in Dropbox, using DocSend for controlled sharing + engagement signals, and routing signatures through Dropbox Sign with write-backs to Airtable.
Next, you’ll need to understand what each tool is responsible for in the chain—Airtable as the system of record, DocSend as the controlled delivery + analytics layer, Dropbox as the file source of truth, and Dropbox Sign as the legally-binding signing engine—so your automation doesn’t collapse when one link changes.
Then, you’ll want to implement the workflow step-by-step with a predictable trigger (for example, a record enters a “Ready to Send” view), deterministic document selection, safe recipient mapping, and a signed-file return path so Airtable always reflects the current signing status. (support.airtable.com)
Introduce a new idea: once the “happy path” works, the real win comes from measuring engagement and tightening security without adding friction—so you can scale from “semi-automated” to “fully automated” without turning the process into a brittle Rube Goldberg machine.
Can you fully automate Airtable to DocSend to Dropbox to Dropbox Sign document signing?
Yes—you can fully automate Airtable to DocSend to Dropbox to Dropbox Sign document signing because it reduces manual handoffs, increases deal visibility through engagement signals, and enforces a consistent compliance trail.
To begin, the reason most teams ask this question is simple: “Can we stop chasing PDFs and still stay in control?” The answer is “yes,” but only if you treat the flow like a system—not a string of one-off zaps.
At a high level, “full automation” means:
- Airtable decides when a document should be sent and to whom (rules + fields).
- Dropbox stores the correct, approved version of the document (single source of truth).
- DocSend distributes a controlled link and captures engagement signals (views, time spent, completion).
- Dropbox Sign sends signature requests, routes signers in order, and returns a signed, auditable artifact.
- Airtable receives status updates + signed file links so no one has to “check the portal.”
What are the biggest benefits of automating this workflow?
Automating this workflow delivers the highest ROI when you’re trying to reduce cycle time and remove uncertainty from follow-ups.
1) You compress “time-to-send” and “time-to-sign.”
Manual flows tend to stall between “approved” and “sent.” Automation makes “Ready to Send” an action, not a reminder. In parallel, electronic signature systems have repeatedly shown faster completion compared to paper-based routing in real operational contexts. For example, a study by the Centre Hospitalier de l’Université de Montréal (Department of Radiology), published in 2003, reported median transcription-to-final-signature time dropping from 11 days to 3 days after introducing electronic signature for one workflow. (pubmed.ncbi.nlm.nih.gov)
2) You standardize the experience (and stop shipping the wrong version).
When Dropbox is your canonical file store and Airtable selects documents by versioned rules, you reduce “oops, wrong attachment” errors—especially across teams.
3) You replace guesswork with engagement signals.
DocSend isn’t just “sharing.” It’s “controlled access + analytics,” so your team can act on meaningful signals like page-level attention instead of “Did you see my email?” (help.docsend.com)
4) You build a clean audit trail without extra admin work.
Dropbox Sign’s audit trail is designed to record and timestamp transaction details and make tampering detectable (including the use of hashing and identifiers to look up logs). (help.dropbox.com)
What are the common limitations or edge cases you should plan for?
Even in strong automation workflows, these are the failure modes that show up most often:
- Trigger instability (views/filters changed): If your automation triggers when a record enters a view, changes to filters can cause accidental runs—so Airtable recommends pairing the trigger with locked views/fields. (support.airtable.com)
- Recipient ambiguity (multiple signers, role swaps): If the “Signer” is not a stable, mapped entity (name + email + role + signing order), your signature request can be valid but wrong.
- Document version drift (template updated mid-deal): If you overwrite files instead of creating versioned artifacts, you lose traceability.
- Link forwarding risk (DocSend link shared outside intended audience): You need access controls and “require email to view” style gates, or you’ll optimize for speed at the cost of confidentiality. (help.docsend.com)
- Expiration + “closed request” confusion: If a signing link expires or a request closes due to decline/cancel, recipients may see a “closed” message and your pipeline silently stalls unless you capture that state. (developers.hellosign.com)
What does “Airtable to DocSend to Dropbox to Dropbox Sign document signing” mean in practice?
“Airtable to DocSend to Dropbox to Dropbox Sign document signing” is a multi-step revenue workflow where Airtable governs the business state, Dropbox stores approved documents, DocSend controls sharing and captures engagement, and Dropbox Sign executes the legally-binding signature request and returns signed outputs.
Next, the key to making this flow reliable is assigning one job to each tool—and refusing to let tools overlap without a clear reason.

What role does Airtable play in the workflow?
Airtable is your system of record and workflow controller. In practice, Airtable should hold:
- Deal (or request) identity: who, what, and why this document exists
- Signing configuration: recipients, roles, signing order, fallback contacts
- Document selection logic: which template/version to use for this deal type
- State machine: Draft → Ready to Send → Sent → Viewed → Signing → Completed (or Declined/Expired)
- Integration identifiers: DocSend link ID, Dropbox file path, Dropbox Sign signature request ID
Most automation failures happen when Airtable is used like a spreadsheet instead of a state machine. If “Ready to Send” isn’t a deterministic state, your automation can’t be deterministic either.
What role does DocSend play in the workflow?
DocSend is your controlled distribution and engagement intelligence layer.
It provides two operational superpowers:
- Access control: requiring email identification, limiting downloads, enabling link-level settings.
- Engagement analytics: visibility into how recipients interact with the document, including page-level attention and visit duration metrics surfaced in activity views. (help.docsend.com)
A practical nuance: DocSend’s “time spent” is not just a raw timer; it is designed to track active viewing by pausing when the visitor navigates away, improving interpretability for follow-up decisions.

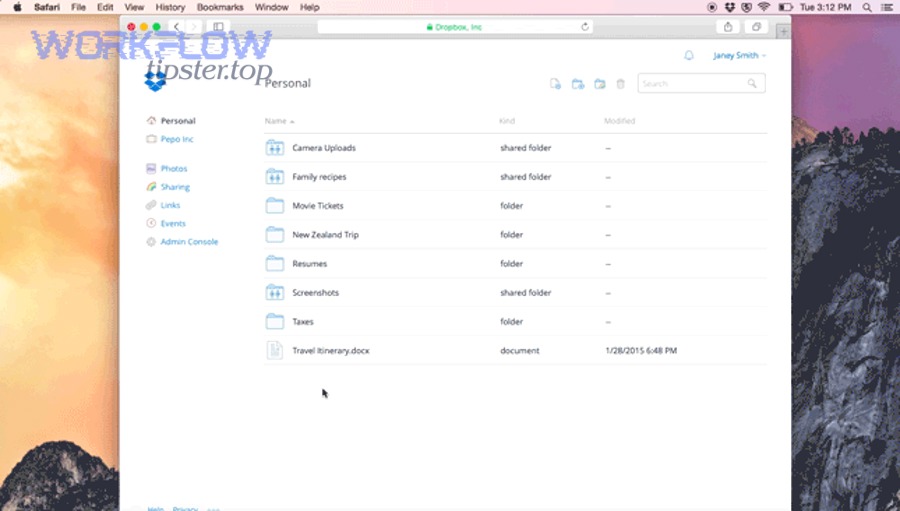
What role does Dropbox play in the workflow?
Dropbox is your file source of truth.
In a mature setup, Dropbox holds:
- A template library (approved, versioned)
- Deal-specific generated files (a copy created per deal)
- A “signed” folder with completed documents + audit artifacts
- Permissioned team access so edits are controlled and traceable
Dropbox is the anchor that prevents “where is the PDF?” chaos. Airtable should reference Dropbox via stable file paths or shared links—never by “it’s in someone’s Downloads.”
What role does Dropbox Sign play in the workflow?
Dropbox Sign is your signature execution and proof layer:
- Sends signature requests (embedded or email-based)
- Tracks signing states (awaiting signature, signed, declined, expired, etc.)
- Generates signed outputs plus audit trails that can be used to verify integrity and events
The audit trail matters because it isn’t just “nice to have”—it’s part of how you defend validity. Dropbox Sign describes audit trails as a comprehensive, timestamped transaction trail and notes hashing-based tamper detection. (help.dropbox.com)
How do you design the right data model in Airtable for document signing workflows?
You design the right Airtable data model by separating deals, documents, recipients, and signature events into normalized tables—then mapping them with stable IDs so every automation step can read and write without ambiguity.
Then, when automation scales, the base stays stable because it’s structured around entities instead of “one giant table with 200 columns.”
Which Airtable tables and fields should you create?
Below is a practical schema blueprint. The table is included to show what each entity contains and how it connects, so your automation can pass clean tokens from step to step.
| Table | Purpose | Must-have fields (examples) |
|---|---|---|
| Deals (or Requests) | Core record that triggers signing | Deal ID, Stage, Owner, Primary Contact, Deal Type, Ready to Send (bool), SLA date |
| Documents | Versioned templates + deal copies | Doc Type, Version, Dropbox Path, Output Filename Pattern, Requires NDA (bool) |
| Recipients | People who sign or receive | Name, Email, Role (Signer/CC), Signing Order, Auth Method (if any) |
| Signature Requests | One request per deal/doc | Dropbox Sign Request ID, Status, Expires At, Completed At, Audit Trail Link |
| DocSend Links | Tracking layer | DocSend Link URL, Require email to view (bool), Last Viewed At, Total Time Spent |
| Events (optional) | Timeline & troubleshooting | Event Type, Timestamp, Source (Airtable/DocSend/Sign), Raw Payload |
Key design rule: don’t store signer details only as free-text fields on Deals. Store signers as records so you can handle multi-signer routing and changes safely.
How do you map records to documents, recipients, and signature status?
Use explicit mapping fields so you never rely on “matching by name.” Recommended mapping patterns:
- Deals ↔ Documents: link to a “Selected Document” record (or selection rules that produce one)
- Deals ↔ Recipients: linked recipients list filtered by role/order
- Signature Requests ↔ Deals: a single linked record plus the external request ID
- DocSend Links ↔ Deals: a single link record per doc share instance
Practical tip: treat external IDs as sacred:
dropbox_file_path(or shared link)docsend_link_url(or link ID)signature_request_id
Once those are stored, you can rebuild state even if a webhook event was missed.
What views, filters, and permissions keep the base scalable?
Your automation is only as stable as your views.
- Create a locked “Ready to Send” view that only shows records meeting strict conditions (complete fields, valid recipients, approved document). Airtable explicitly recommends pairing “record enters view” triggers with locked views/fields to prevent accidental runs caused by filter changes. (support.airtable.com)
- Create an “Exceptions” view for incomplete data so humans can fix records without touching production triggers.
- Use permissioning so only admins can edit the trigger view and the “status machine” fields.
This approach preserves your system even as new deal types, templates, and signing routes appear.
How do you build the automation workflow step by step?
Build the automation by chaining five steps—trigger, document creation, controlled sharing, signature routing, and write-back—so the outcome is a signed document stored in Dropbox with status and links written back to Airtable.

Let’s explore the exact sequence in a way that stays robust when you scale to hundreds or thousands of deals.
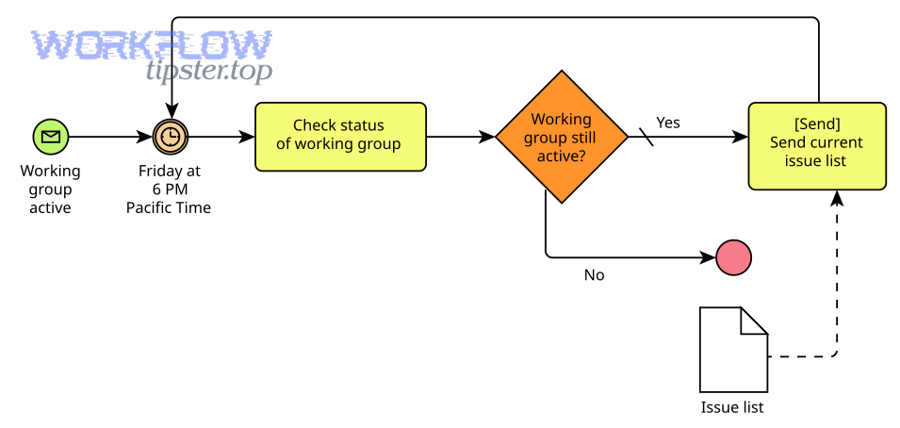
Step 1: Trigger from Airtable when a deal reaches “Ready to Send”
Use a deterministic trigger—typically one of these:
- “Record enters view” (best when you want a condition-based workflow) (support.airtable.com)
- “Record matches conditions” (if you prefer rule logic over a view)
Implementation checklist:
- Confirm required fields are present (document type, recipients, signing order)
- Lock the view/fields that govern the trigger
- Store a “Workflow Run ID” (timestamp or UUID) so re-runs are detectable
This prevents accidental duplicates and gives you traceability.
Step 2: Generate or attach the correct document version and upload to Dropbox
Your goal is a deal-specific file that never changes after it’s sent.
Best practice:
- Start from a versioned template in Dropbox
- Create a copy into a deal folder (e.g.,
/Deals/2026/Deal-123/) - Name it deterministically (
Deal-123-MSA-v3.pdf)
If you generate documents dynamically, you can still upload the final artifact to Dropbox—just ensure the final file is immutable once the signing request is created.
Step 3: Share through DocSend with tracking and access controls
DocSend is where “sending” becomes “measured delivery.”
Configuration priorities:
- Enable identification gates when appropriate (for example, requiring email to view so your analytics has a real identity) (help.docsend.com)
- Decide whether downloads are allowed (download-only content changes tracking behavior, so use intentionally)
- Set link settings aligned with your sales motion (expiration, access toggles, controlled distribution)
This is also where you can unify your broader automation workflows mindset—just like “calendly to google calendar to google meet to linear scheduling” turns meetings into trackable events, DocSend turns document delivery into trackable buyer behavior.
Step 4: Send to Dropbox Sign and route recipients correctly
This is the point of no return—so validate inputs before sending.
Routing checklist:
- Verify signer emails (format + domain sanity checks)
- Confirm role-to-signer mapping is correct (no swapped buyer/legal contacts)
- Set expiration policy if needed (and store it in Airtable)
On expiration, Dropbox Sign considers the request expired only when expires_at is explicitly set, and it provides status codes like expired in signatures when the time passes. (developers.hellosign.com)
Step 5: Write back signing status and signed files to Airtable
The write-back is what makes your system self-healing.
Minimum write-backs to Airtable:
signature_request_id- current status (awaiting_signature / signed / declined / expired)
- signed document Dropbox link
- audit trail link (or indicator it exists)
Also, store failure states. If a recipient sees “signature request has been closed,” Dropbox lists common causes like already signed, declined, or canceled—those should map to Airtable statuses and trigger follow-up automations. (help.dropbox.com)
How do you track, measure, and optimize performance with DocSend + Dropbox Sign?
You track and optimize performance by combining DocSend engagement signals with Dropbox Sign status signals (awaiting, signed, declined, expired) to predict readiness, prevent stalls, and test improvements safely.

More specifically, this is where your workflow becomes a growth system instead of a “document conveyor belt.”
Which DocSend engagement metrics actually predict signing readiness?
Not all analytics are equal. The predictive signals usually fall into three tiers:
Tier 1 (high intent):
- Repeat visits by the same identified viewer
- High completion percentage (most of the doc viewed)
- High time spent on pricing/legal pages (page-level attention)
DocSend’s Activity tab is explicitly designed to surface page-by-page analytics, visit duration, and document-view completion signals in one place. (help.docsend.com)
Tier 2 (moderate intent):
- Single visit + meaningful time spent
- Engagement clustered in a short time window (e.g., “review meeting” behavior)
DocSend’s time measurement is intended to track active viewing (pausing when the viewer navigates away), which makes “time spent” more actionable than a naive timer.
Tier 3 (weak intent):
- Link opened with very low time spent
- Low completion and no revisit
Operationally, you can create an Airtable “Engagement Score” field that rolls up these signals to guide follow-up sequences.
Which Dropbox Sign status signals help you prevent deal stalls?
The stall-prevention playbook is about detecting final vs non-final states and responding automatically.
Common “what to do next” patterns:
awaiting_signaturefor too long → send reminder sequence + notify ownerdeclined→ open a “Deal Risk” task and capture reasonexpired→ create a new request or route to legal for decision
Dropbox Sign’s developer documentation explains that expired requests become non-signable and show status codes like expired, and it treats expired as a final state similar to declined/completed. (developers.hellosign.com)
Also, the platform provides structured response objects that include a status_code per signature (e.g., awaiting_signature). (developers.hellosign.com)
How do you run A/B tests on document versions without breaking the workflow?
A/B tests fail when the workflow can’t tell version A from version B.
Safe A/B testing approach:
- Create two template versions in Dropbox (immutable)
- Store both as Document records in Airtable with explicit version tags
- Randomize selection before DocSend and Dropbox Sign steps
- Keep recipient mapping identical across variants
- Compare outcomes:
- DocSend engagement (time spent on key pages)
- Dropbox Sign completion time and completion rate
Important: don’t A/B test mid-flight (changing the doc after sending). Instead, test on new deals entering “Ready to Send.”
Evidence that process-level improvements matter: a feasibility study involving the University of California, Los Angeles (David Geffen School of Medicine, Department of Obstetrics and Gynecology) reported 19% labor savings with digital signatures and faster completion versus paper-based processes in its measured context. (pmc.ncbi.nlm.nih.gov)
In revenue workflows, even “moderate” operational savings often translate into meaningful pipeline velocity.
How do you secure and comply with sensitive documents in this workflow?
You secure and comply by enforcing least-privilege access in Dropbox, using DocSend controls to reduce unauthorized sharing, relying on Dropbox Sign’s audit trail for integrity, and selecting the stack that best balances compliance with buyer friction.

Besides speed, this is the section that separates “automation” from “trusted automation.”
What access controls and audit trails matter most in Dropbox and Dropbox Sign?
The minimum security posture for sensitive documents usually includes:
- Controlled file permissions in Dropbox (team folders, restricted editing)
- Document integrity proof after signing
- Audit trail availability for disputes
Dropbox Sign explains that it tracks and timestamps transaction information (including IP address), appends an audit trail identifier, and uses hashing so tampering of the transaction log is detectable. (help.dropbox.com)
So, in practice, your Airtable record should always store:
- signed file link (Dropbox)
- audit trail link or indicator (Dropbox Sign)
- completion timestamp + signer metadata
How do you prevent unauthorized forwarding while keeping signing friction low?
This is a balancing act: the stricter you are, the more friction you create.
Low-friction controls (good default):
- Require email identification for DocSend links (so “who viewed” is real) (help.docsend.com)
- Use DocSend link settings that support your motion (access toggles, controlled distribution)
- Keep signer experience straightforward—avoid extra steps unless risk demands it
Higher-control options (use when sensitivity is high):
- Watermarking
- NDA gating
- Expiration and rapid link revocation
Remember: if you over-tighten early-stage sales documents, you may reduce conversions. Instead, raise controls as the deal moves to legal/procurement.
How does this compare to other stacks like Airtable → Google Docs → Google Drive → DocuSign?
In terms of function, these stacks are similar:
- Airtable: orchestrates data + states
- Google Docs/Drive or Dropbox: stores drafts and final PDFs
- DocuSign or Dropbox Sign: executes signatures
- DocSend: adds controlled sharing + engagement analytics (some stacks substitute other link-tracking tools)
Where the comparison becomes real is in:
- Analytics depth (DocSend is purpose-built for document engagement tracking) (help.docsend.com)
- Audit trail approach (Dropbox Sign emphasizes comprehensive trails + hashing) (help.dropbox.com)
- Integration shape (Google-native vs Dropbox-native ecosystems)
Operationally, teams often evaluate variants like “airtable to google docs to google drive to docusign document signing” or “airtable to docsend to google drive to docusign document signing” when they want stronger collaboration in drafting or different compliance tooling—while keeping the same core state machine in Airtable.
How do you make this “Not Manual” (and what is the opposite of automation in this flow)?
You make this “Not Manual” by identifying the handoff points humans repeat (copying files, emailing links, chasing signatures), replacing them with deterministic triggers and write-backs, and treating “manual” as the antonym of “automated” that you progressively eliminate.

Next, think of “manual” as a tax you pay every time a process relies on memory instead of state.
What manual steps usually break first, and why?
The first manual steps to fail are the ones that depend on “someone remembering”:
- Attaching the right version (wrong PDF sent)
- Copy-pasting recipient emails (typos, outdated contacts)
- Following up without signals (pings at the wrong time)
- Checking signature portals (status unknown until someone looks)
- Saving signed copies back to the right folder (lost audit trail, messy compliance)
Once you map these to fields + triggers + write-backs, they stop being failure points.
What lightweight automation workflows can you start with if you’re not ready to fully automate?
If “fully automated” is too big for week one, start with partials that still move the needle:
Level 1: Airtable status + checklist automation
- Airtable view shows “Ready to Send”
- A task/comment is created for the owner with prefilled recipients + doc link
Level 2: DocSend link creation + tracking
- Automatically create a DocSend link when a record enters view
- Write the link + first-view timestamp back to Airtable
Level 3: Signature routing automation
- Trigger Dropbox Sign when DocSend engagement crosses a threshold (e.g., high completion)
- Store request ID + status codes in Airtable
This incremental path matches how most teams adopt automation workflows: you don’t jump to “perfect,” you jump to “measurably better,” then tighten.
What troubleshooting checklist catches 80% of failures?
Use this checklist whenever a workflow run looks “stuck”:
- Trigger check (Airtable): Did the record actually enter the trigger view, and is the view locked/unchanged? (support.airtable.com)
- Data completeness: Are recipients present with correct emails + signing order?
- Document path validity (Dropbox): Does the referenced file exist, and is it the correct version?
- DocSend identity: Is “Require email to view” enabled if you expect named analytics? (help.docsend.com)
- Time-spent interpretation: Are you interpreting time spent correctly (active viewing vs tab switching)?
- Signature state: Is it awaiting, declined, expired, or closed—and is your automation handling each final state? (developers.hellosign.com)
- Audit trail expectation: Are you expecting an audit trail in a flow that doesn’t generate one (e.g., self-signed “Just Me” cases)? (help.dropbox.com)
Once these are stable, you can confidently expand into more complex variants—like “airtable to docsend to google drive to docusign document signing”—without losing control of the core state machine.

