STEP 1 — Title & outline analysis (for consistency)
– Main keyword (keyword focus): airtable to confluence to dropbox to dropbox sign document signing
– Predicate (main action): Automate
– Relations Lexical used: Antonym → paperless vs paper-based
– Search intent type detected from the outline: primarily How-to, supported by Definition, Boolean, Grouping, and Comparison.
Airtable → Confluence → Dropbox → Dropbox Sign document signing is a paperless eSignature workflow that moves a request from a structured record to a contextual wiki page, then to file storage, then to a legally trackable signing event—without retyping the same information twice.
Next, you’ll learn how to make that workflow reliable without turning it into a brittle chain of “if this, then that” rules—so operations teams can trust it for real contracts, approvals, and onboarding packets.
Then, you’ll get a practical blueprint: field design, folder structure, template roles, status syncing, and the key automation decisions that prevent missing signatures and lost PDFs.
Introduce a new idea: once the core workflow is stable, you can extend it into a truly paperless system that improves turnaround time, auditability, and collaboration—not just “digital files instead of paper.”
What is an Airtable → Confluence → Dropbox → Dropbox Sign paperless eSignature workflow?
An Airtable → Confluence → Dropbox → Dropbox Sign paperless eSignature workflow is a document signing automation pattern where a record generates a document context, stores the file in a controlled folder, and sends it for eSignature—then writes signing results back to the record and the knowledge page.
To better understand why this chain works, think of it as four layers that reduce manual work while increasing traceability: database → context → storage → signature event.

In practice, each tool plays a distinct role:
- Airtable = system of record (who, what, when, which template, which signer set, what status)
- Confluence = system of context (why this document exists, background notes, links, approvals)
- Dropbox = system of storage (versioned files, canonical paths, permissions, retention)
- Dropbox Sign = system of signature (templates, roles, audit trails, completion events)
Your workflow becomes “paperless” when it does more than email a PDF—it controls creation, routing, signing, filing, and reporting in one consistent lifecycle. And if you’re wondering whether e-signatures are generally recognized, many providers describe them as secure and legally enforceable in most industrialized countries. (adobe.com)
Can you automate this workflow without code (and still keep it reliable)?
Yes—you can automate Airtable → Confluence → Dropbox → Dropbox Sign document signing without code and keep it reliable because (1) you can design strong data constraints in Airtable, (2) you can standardize document generation and folder rules, and (3) you can build event-based status syncing that detects failures early.

More importantly, “no code” doesn’t mean “no engineering”; it means you shift engineering effort into structure: clean fields, strict naming, predictable triggers, and clear fallbacks.
Reliability comes from three operational safeguards:
- Strong inputs: required fields, controlled select lists, validated email domains, and “ready to send” gating.
- Deterministic outputs: consistent file naming, stable Dropbox paths, and templates that don’t depend on optional fields unless handled gracefully.
- Observable state: status fields, timestamps, retry counters, and a single place to see what happened.
A helpful mental model is the same one that research on e-signature adoption often points to: success depends on user involvement, adequate resources, coordination with vendors, and policy alignment—not just the technology. (pmc.ncbi.nlm.nih.gov)
If you build those safeguards, no-code automation can be dependable enough for operations, HR, procurement, and partner agreements—especially when you treat signing as a monitored process, not a one-time action.
What is the best step-by-step workflow blueprint from record creation to signed PDF archiving?
The best blueprint is a 7-step lifecycle: (1) validate record → (2) generate document context → (3) generate draft file → (4) archive draft → (5) send signature request → (6) store signed PDF + audit trail → (7) sync back statuses and links.

Then, the key is to make each step produce a “receipt” (IDs, URLs, timestamps) so you can trace and recover.
Here’s a practical, operations-friendly flow you can implement with most automation tools:
- Airtable intake (Record Created / Updated):
- Required fields completed (template type, counterparty name, signer emails, due date)
- Status = “Ready to Generate”
- Confluence context page:
- Create (or update) a page that includes key metadata + links to files and signing status
- Draft generation:
- Generate a PDF (or DOCX) using a template system (could be a doc-gen tool, a standard PDF template, or a “fill fields then export” approach)
- Dropbox storage (Drafts):
- Save draft to
/Drafts/and record the file URL + path in Airtable
- Save draft to
- Dropbox Sign send:
- Create signature request from a template (or upload the draft) and assign roles/signing order
- Dropbox storage (Signed):
- On “completed”, store signed PDF + audit trail to
/Signed/and lock naming
- On “completed”, store signed PDF + audit trail to
- Sync back:
- Airtable status updates + signed link + completed timestamp
- Confluence page updated with final links and outcomes
Evidence: DocuSign’s higher-education brief reports 54% of agreements completed in under 6 hours (and 74% of those under 1 hour) after adopting e-signature workflows—showing why lifecycle automation can materially improve turnaround. (docusign.com)
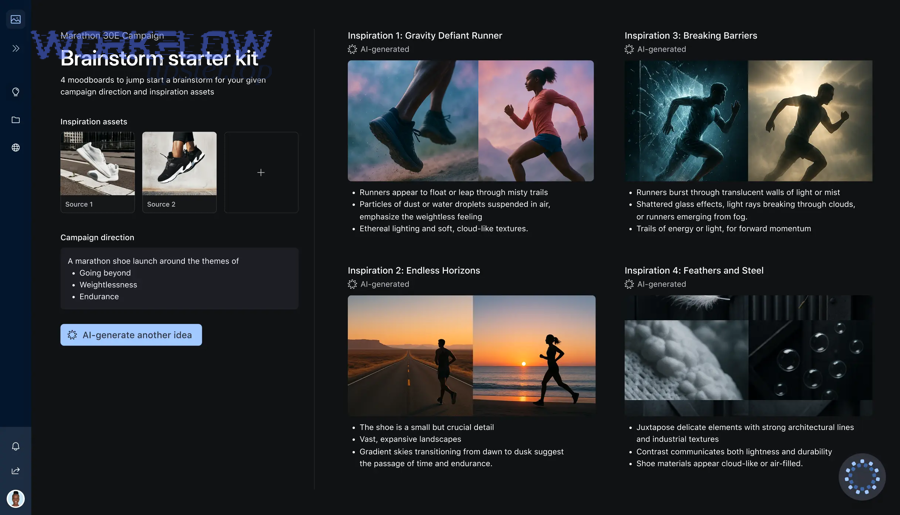
How do you design Airtable fields and Confluence context so documents generate correctly?
You design Airtable fields and Confluence context correctly by (1) separating “inputs” from “outputs,” (2) enforcing validation before generation, and (3) writing document-ready values (clean names, normalized dates, consistent addresses) into a dedicated “document payload.”
Next, you’ll want a single “source of truth” mapping that controls what gets printed and where it appears—so your document generator isn’t guessing.
![]()
How should you structure Airtable for clean document inputs?
Your Airtable base should treat document signing like a state machine, not a spreadsheet.
- Intake fields (human-entered): requester, department, counterparty, signer emails, due date, template type
- Derived fields (system-calculated): doc title, doc ID, canonical folder path, record URL
- Output fields (automation-written): Confluence page URL, Dropbox draft URL, signature request ID, signed PDF URL, audit trail URL, completion timestamp
Add a “Ready to Send” checkbox or a single select with controlled states:
Draft → Ready to Generate → Draft Generated → Ready to Send → Sent → Partially Signed → Completed → Archived → Failed
What should go on the Confluence context page?
Confluence should answer “what is this document and why does it exist?” without forcing anyone to open the PDF.
- Summary: document type, purpose, requester, counterparty
- Links: Airtable record, Dropbox draft, signing request, signed PDF
- Signing status: current stage, who is next, last event time
- Approvals: optional notes, decision history, policy references
A compact mapping table helps teams keep this consistent. The table below shows a practical field-to-document mapping that reduces broken templates and missing values.
| Airtable Field | Purpose in Document | Formatting Rule | Fallback if Missing |
|---|---|---|---|
| Counterparty Legal Name | Signature block + header | UPPERCASE for header, Title Case elsewhere | Block sending |
| Effective Date | Agreement date | ISO input → “Month DD, YYYY” | Leave blank + highlight |
| Signer Email(s) | Signing routing | Validate domain + remove spaces | Block sending |
| Document ID | Filing + audit | Prefix + incremental ID | Auto-generate |
Evidence: A study published in Decision Support Systems by National Chung Cheng University (Department of Information Management) and collaborators highlights that adoption success is shaped by organizational and environmental factors (like resources and policy), not just technology—reinforcing why structured inputs and governance matter. (pmc.ncbi.nlm.nih.gov)
How should you structure Dropbox folders and naming to keep drafts and signed documents organized?
You should structure Dropbox folders and naming by (1) separating Drafts vs Signed, (2) using an ID-first naming convention, and (3) designing paths that reflect how your business retrieves documents (by team, vendor/customer, and time).
Then, you reduce chaos by making the path deterministic: the workflow can always compute “where this file goes” from Airtable fields.
![]()
A practical structure that scales:
/Agreements/{Department}/{Counterparty}/{Year}/Drafts//Agreements/{Department}/{Counterparty}/{Year}/Signed//Agreements/{Department}/{Counterparty}/{Year}/Audit/
Naming convention (simple but strict):
{DocID} - {DocType} - {Counterparty} - {YYYY-MM-DD} - {STATUS}.pdf
Examples:
AGR-02481 - NDA - Acme Co - 2026-02-02 - DRAFT.pdf
AGR-02481 - NDA - Acme Co - 2026-02-02 - SIGNED.pdf
Rules that prevent “where did the file go?” problems:
- Never rename after signing (signed files should be immutable).
- Keep drafts separate (people will upload “v2_final_FINAL.pdf”; your system should not).
- Store the canonical URL in Airtable (don’t rely on people browsing folders).
- Write back the folder path (so you can re-archive without re-deriving).
How do Dropbox Sign templates, roles, and signing order affect automation?
Dropbox Sign templates, roles, and signing order affect automation by determining who must sign, in what sequence, and what data must be provided before the request can be created—which directly impacts how you validate Airtable inputs and how you manage partial completion states.
Next, you’ll want to design templates so the automation fills only what it can guarantee, and humans review only what requires judgment.
What is a template-driven vs upload-driven signing flow?
- Template-driven: you predefine fields and signer roles; automation passes role assignments + merge data
- Upload-driven: you generate the PDF elsewhere and upload it; you still define signers, but field placement may be less standardized
Template-driven is usually more reliable when you have repeatable documents (NDA, SOW, onboarding, approvals).
How do roles change your Airtable data model?
If your template has roles like Company Signer, Counterparty Signer, Witness, you need Airtable fields for each role—not a generic “signer email” list.
Recommended Airtable pattern:
Role: Company Signer → Name, Email, TitleRole: Counterparty Signer → Name, Email, TitleRole: Approver (optional) → EmailSigning Order → 1, 2, 3...
What does signing order do to workflow logic?
Signing order transforms your workflow from “sent → completed” into a multi-event process:
- Sent
- Viewed
- Signed by signer 1
- Waiting on signer 2
- Completed
- Declined / Expired / Canceled
So your automation must support intermediate statuses and reminders—not just “send once and pray.”
What should you sync back to Airtable and Confluence after sending and after signing?
You should sync back (1) identifiers, (2) links, (3) timestamps, and (4) state transitions—so Airtable remains the control center and Confluence remains the narrative record.

Besides keeping humans informed, syncing is what makes troubleshooting fast: you can see exactly which step failed and what was last successful.
What should be written back right after sending?
- Signature request ID
- Request status = “Sent”
- Sent timestamp
- Signer list snapshot (names + emails at send time)
- Draft Dropbox URL (locked as the “sent version”)
- Confluence page update: “Sent on X, waiting on Y”
What should be written back after completion?
- Signed PDF URL
- Audit trail URL (or equivalent receipt)
- Completion timestamp
- Final signers + completion order
- Status = “Completed” + “Archived” after filing finishes
- Confluence update: final links + outcome summary (completed/declined/expired)
Evidence: A case-study listing from Internet2 highlights implementations that report “thousands of hours in time savings annually” after standardizing e-signature workflows—sync-back is one of the mechanisms that makes those gains durable because teams stop re-checking status manually. (internet2.edu)
How do you choose an automation approach for this workflow (Zapier vs Make vs native integrations)?
Zapier wins for speed-to-launch and broad app coverage, Make is best for complex branching and data shaping, and native integrations are optimal for long-term stability when the vendor supports your exact signing and storage events.

Next, the “right” choice depends on whether your workflow is simple routing or true lifecycle orchestration.
What criteria should decide the platform?
Use these criteria (in order):
- Event coverage: can you detect “sent”, “viewed”, “signed”, “declined”, “expired”?
- Idempotency controls: can you prevent duplicates if a trigger fires twice?
- Data shaping: can you map role-based signer objects cleanly?
- Error handling: can you retry, alert, and pause safely?
- Governance: can you manage secrets, access, audit logs, and change control?
When does Zapier make the most sense?
- Your team wants to ship fast and iterate
- You can keep the flow mostly linear
- You rely on standard triggers/actions and minimal custom logic
This is a natural place to think in terms of automation workflows that can be cloned, documented, and handed off across teams.
When does Make make the most sense?
- You need complex branching (multi-party signing, conditional routing)
- You want stronger data transformation and scenario visualization
- You plan for more “systems orchestration” than “single Zap”
When do native integrations win?
- Your compliance demands direct vendor-to-vendor hooks
- You need fewer moving parts (less vendor chaining)
- You want long-term stability and fewer platform dependencies
And if you’re building parallel alerting flows (for engineering or IT), keep them separate from contract signing—e.g., github to jira to microsoft teams devops alerts or GitHub to Jira to Microsoft Teams notifications—so your signing automation doesn’t inherit noisy incident logic.
Is the workflow secure and compliant enough for business documents?
Yes—the workflow can be secure and compliance-ready because (1) e-signature platforms typically provide audit trails and tamper-evident records, (2) Dropbox storage can be permissioned and monitored, and (3) you can enforce least-privilege access and retention policies across the lifecycle.
More specifically, security depends on how you configure identity, access, and evidence—not which apps you picked.
![]()
Your security checklist should include:
- Identity & access
- SSO where available
- Role-based access (who can send vs who can view vs who can admin)
- Separate service accounts for automation with limited scopes
- Data controls
- Restricted folders for Drafts and Signed
- Retention rules (e.g., signed docs retained X years)
- Controlled sharing (disable public links for Signed)
- Auditability
- Store signature request IDs + audit trail links
- Timestamp every state transition
- Log automation runs and errors
Evidence: Adobe’s higher-ed guide describes e-signatures as secure, legally valid, trusted, and enforceable in “almost every industrialized country,” and also emphasizes tracking, reminders, cancellations, and audit trails as core workflow controls. (adobe.com)
If your documents involve regulated data (PII, HR, health, finance), treat this as a governance project: define roles, data classification, and documented procedures before scaling.
What are the most common failure points—and how do you troubleshoot them fast?
There are 6 common failure points in this workflow—(1) bad Airtable inputs, (2) broken document generation, (3) wrong Dropbox path/permissions, (4) signature request mapping errors, (5) webhook/event gaps, and (6) duplicate runs—and you troubleshoot fastest by checking state receipts in order.

Then, instead of searching logs blindly, follow the lifecycle: record → context → storage → signing → sync-back.
A practical “fast triage” sequence:
- Confirm the Airtable record state
- Is status truly “Ready to Send”?
- Are required fields populated?
- Is signer email valid and role-mapped?
- Confirm the Confluence context
- Did the page get created/updated?
- Does it reference the correct record ID?
- Confirm Dropbox draft storage
- Does the draft file exist at the expected path?
- Are permissions correct for the automation account?
- Confirm signature request creation
- Do you have a request ID stored?
- Did roles and signing order match the template?
- Confirm completion event
- Did the “completed” event fire?
- Did the signed PDF get stored in
/Signed/?
- Confirm sync-back
- Are signed URL and timestamps written to Airtable?
- Is the Confluence page updated?
Where many teams get stuck is mixing unrelated automations into the same alert channel. Keep your signing alerts separated from devops routing like github to monday to microsoft teams devops alerts (where monday.com drives a different operational cadence), and keep document-signing alerts tightly scoped to stakeholders who can actually fix mapping or signer data.
Evidence: The same Decision Support Systems study notes adoption is not “just purchasing hardware/software” but also a social and organizational process—so troubleshooting should include process checks like ownership, policy, and user involvement, not only technical fixes. (pmc.ncbi.nlm.nih.gov)
Contextual Border: At this point, you have the macro workflow that satisfies the primary intent: an end-to-end, reliable Airtable → Confluence → Dropbox → Dropbox Sign signing lifecycle. Next, we shift into micro semantics—advanced patterns that make the workflow truly paperless and operationally superior, not merely “digital.”
What advanced patterns make this workflow truly “paperless” instead of just “digital”?
A workflow becomes truly paperless when it adds automation depth: it enforces governance, reduces cycle time, improves retrieval, and produces audit-grade evidence—so the organization stops treating signing as an email task and starts treating it as a managed process.

In addition, the biggest difference between “digital” and “paperless” is whether you can operate without humans chasing documents.
How do you handle multi-party signing, conditional routing, and exceptions?
Use a rules layer in Airtable:
- If
DocType = SOWandAmount > threshold, add an internal approver step - If
Counterparty = VendorandCountry = X, enforce additional identity verification - If
SignerCount > 2, enforce signing order and send reminders
This is where you keep complexity inside data and rules, not scattered across disconnected automations.
How can you generate documents from structured content, not manual copy/paste?
Treat Airtable as the data schema and Confluence as narrative context:
- Airtable feeds structured values (legal name, address, dates, pricing, terms flags)
- Confluence holds justification and collaboration history
- The generated document is the contract artifact—not the place where truth lives
If you want a comparable architecture in another doc-signing chain, patterns like airtable to google slides to box to docusign document signing can work similarly: structured data → template generation → controlled storage → signing. (Here, Google Slides and Box replace Confluence/Dropbox, while DocuSign replaces Dropbox Sign.)
What does “audit-ready” look like in daily operations?
Audit-ready means anyone can answer these questions in under 2 minutes:
- Which version was sent?
- Who signed, and when?
- What was the approval basis?
- Where is the signed PDF and receipt?
- What exceptions occurred (declined/expired), and what happened next?
This is also where a consistent “WorkflowTipster” style operating playbook helps: one page that defines states, folder rules, retry policies, and alert routing—so the workflow survives team changes and scale.
Evidence: DocuSign’s higher-ed brief includes examples like eliminating large volumes of paper annually and saving 1–5 hours per completed document in case studies, illustrating how governance + automation can translate into measurable operational gains when the workflow is standardized end-to-end. (docusign.com)

