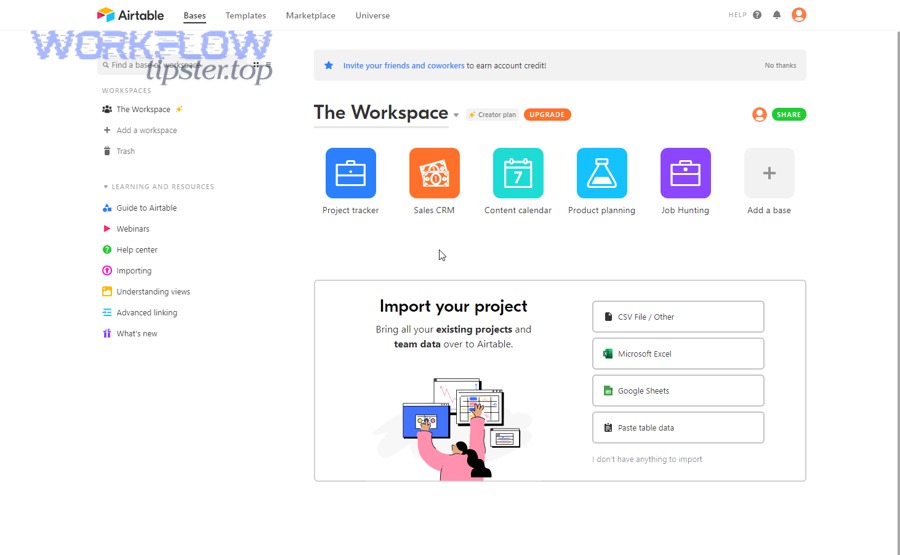
An airtable to bitbucket integration helps development and product teams connect planning data in Airtable with code activity in Bitbucket so work stays aligned, statuses stay accurate, and handoffs happen faster without manual copying.
Next, you’ll see what this integration really means in practice—what gets connected, what “sync” actually looks like, and which parts of your workflow benefit most (issues, pull requests, deployments, or release tracking).
Then, we’ll break down the most common connection methods—no-code connectors, webhook-driven automations, and custom API workflows—so you can pick the approach that fits your team’s size, governance, and budget.
Introduce a new idea: once you choose a method, the real win comes from mapping fields, handling edge cases, and building reliability (retries, rate limits, permissions, and security) so your integration doesn’t quietly drift out of sync.
What does an Airtable to Bitbucket integration mean for DevOps and product teams?
An Airtable to Bitbucket integration is a workflow bridge that connects Airtable records (requirements, tasks, bugs, releases) to Bitbucket repository events (commits, pull requests, builds) so updates can move automatically between planning and delivery systems.
To better understand why this matters, think of Airtable as your “work catalog” and Bitbucket as your “change log.” When they’re integrated, you stop treating them like separate worlds and start using them as two views of the same delivery system.

In practical terms, an integration usually aims to do at least one of these:
- Link work items to code: attach a Bitbucket PR URL or commit hash to an Airtable record so anyone can trace delivery.
- Automate status changes: move an Airtable “In Review” field when a pull request is opened, approved, or merged.
- Generate consistent artifacts: create branches, PR templates, or checklist steps when a record reaches a “Ready” milestone.
- Create reporting that matches reality: align roadmap views with what is actually happening in repos.
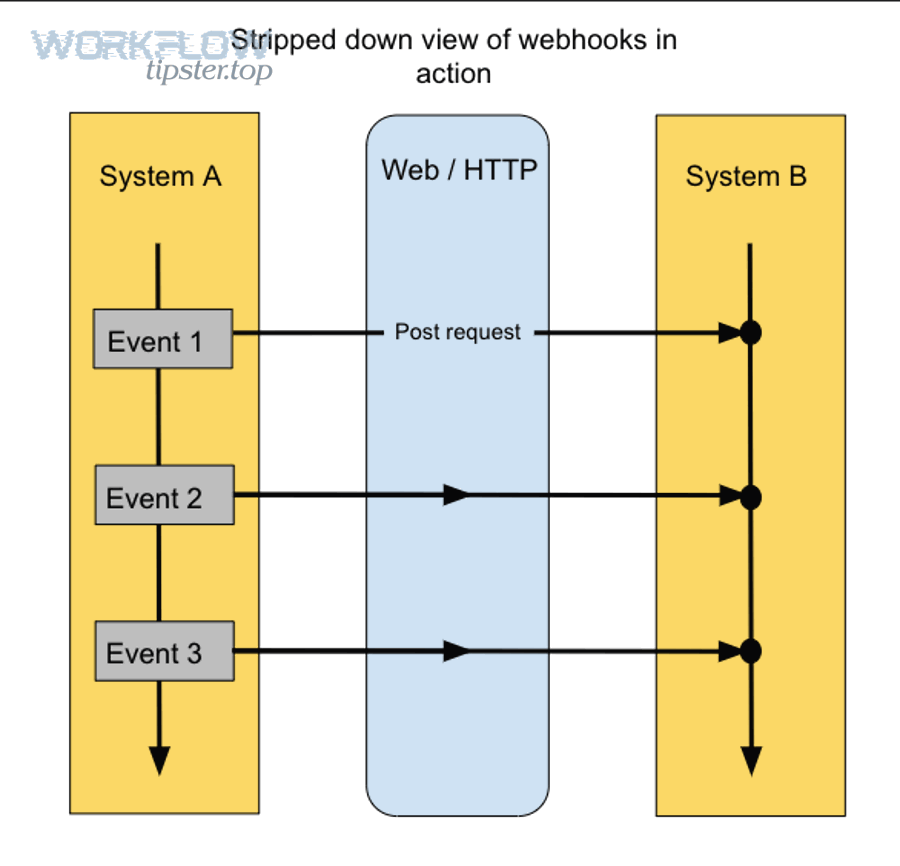
Bitbucket supports webhook-driven event delivery (it can send requests to your service when events occur).
Do you need an Airtable to Bitbucket integration for your workflow?
Yes—you likely need an airtable to bitbucket integration if (1) your team manually copies statuses between tools, (2) you lose time chasing “what’s the latest?” and (3) your releases depend on accurate handoffs between product, engineering, and QA.

More importantly, the value shows up when integration removes “micro-friction” that steals focus. If your workflow requires constant switching between planning and code tools, your team pays a compounding cost in delays and mistakes.
Here are the three most reliable signals that integration will pay off quickly:
- Status pain: roadmap statuses lag behind Bitbucket activity by days, so stakeholders stop trusting dashboards.
- Traceability pain: “Which PR delivered this requirement?” becomes a recurring question that costs meeting time.
- Handoff pain: QA and release managers rely on ad-hoc updates instead of event-driven automation.
When interruptions and tool switching are frequent, regaining focus takes real time. According to a study by University of California, Irvine from the Department of Informatics, in 2008, knowledge workers needed significant time to recover after interruptions, showing measurable productivity costs from fragmented attention.
That’s why teams that already invest in Automation Integrations across other workflows often see Airtable ↔ Bitbucket as a natural next step—similar to how teams automate handoffs in pipelines like freshdesk to jira for support-to-engineering, or operational notifications like google docs to google chat for approvals, or even outbound messaging like google docs to sendgrid for templated communications.
What are the best ways to connect Airtable to Bitbucket?
There are three main types of Airtable to Bitbucket connections: (1) no-code automation platforms, (2) two-way sync connectors, and (3) custom integrations using APIs and webhooks, chosen based on complexity, reliability needs, and governance.
Next, let’s break down each type so you can match the tool to the job instead of forcing a single approach onto every workflow.
No-code automation platforms
No-code platforms are best when you need fast setup, clear triggers/actions, and minimal engineering overhead—especially for one-way updates like “when PR merged, update Airtable status.”
- Strength: speed to launch and easy iteration.
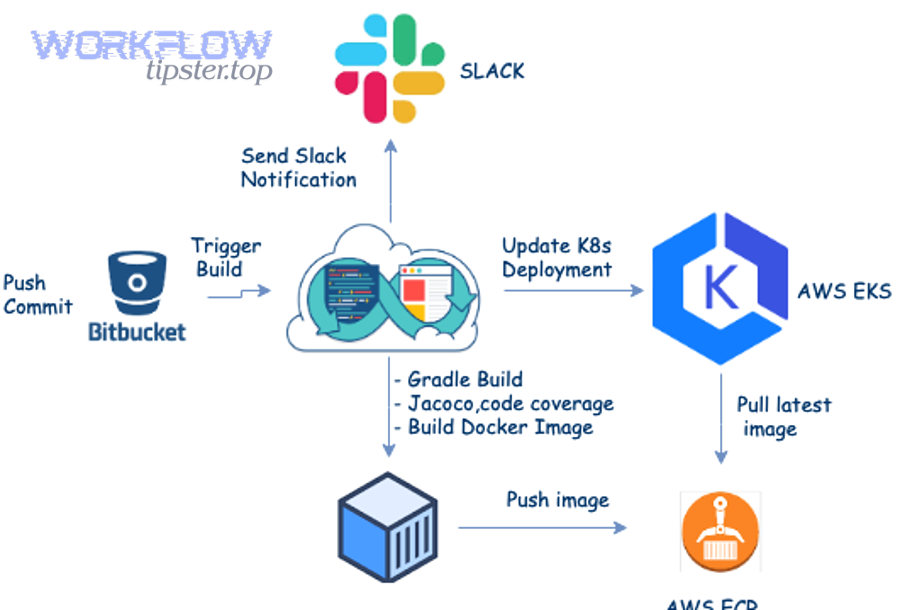
- Typical triggers: Bitbucket webhook event → automation step(s) → Airtable record update.
- Typical risks: limited custom logic, brittle mapping if your schema changes, and less control over retries/idempotency.
Two-way sync tools
Two-way sync tools focus on keeping data consistent in both systems—useful when multiple teams update different fields and you want “single source of truth” behavior.
Some vendors position dedicated Airtable↔Bitbucket sync offerings explicitly as “two-way” configurations for work tracking and engineering signals.
- Strength: consistency across multiple teams and views.
- Typical use: product ops updates Airtable fields; engineering updates delivery metadata; both stay aligned.
- Typical risks: conflict resolution rules can be non-obvious; you must define “ownership” per field.
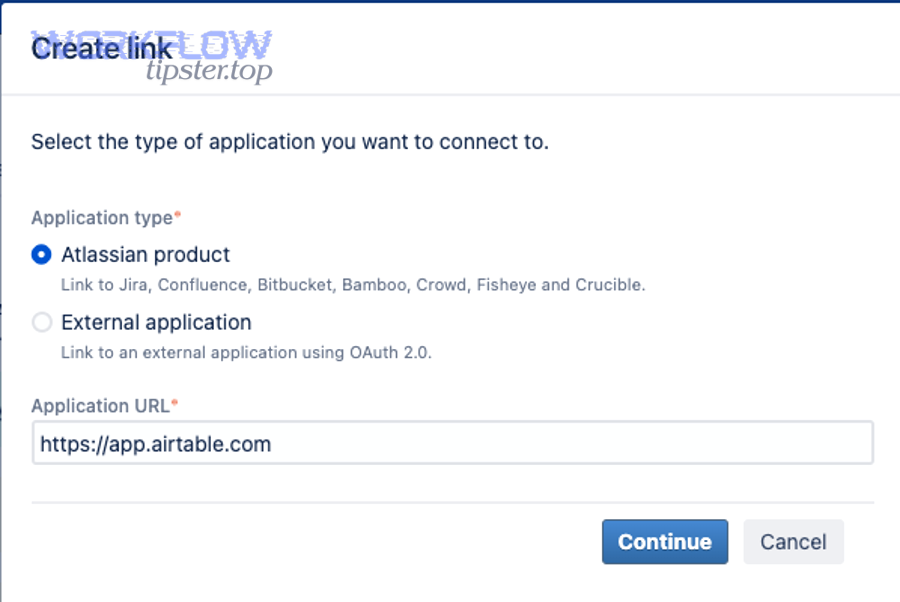
Custom integration with APIs & webhooks
Custom integrations are best when you need strict control (security, compliance, observability), complex transformations, or domain-specific rules like “map PR approvals to a weighted confidence score.”
- Strength: maximum flexibility and reliability engineering (retries, queues, dead-letter handling).
- Typical inputs: Bitbucket Cloud webhooks and payloads, plus Airtable Webhooks API notifications.
- Typical risks: engineering time, ongoing maintenance, and dependency management.
How do you set up an Airtable to Bitbucket integration step by step?
The most reliable setup method is a 4-step workflow: define the data model, choose triggers, configure actions, and validate with test events—so your Airtable to Bitbucket integration produces the same outcome every time.
To begin, treat setup like system design, not a quick “connect and hope” button, because most integration failures come from unclear ownership and unstable mapping rather than tooling.
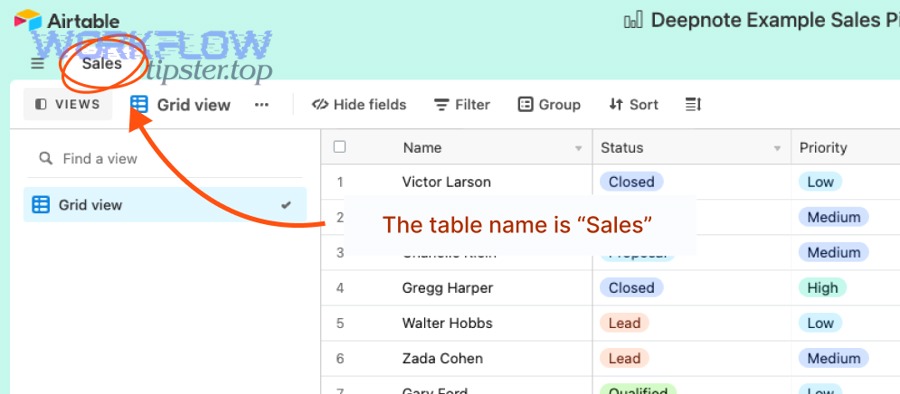
Define your use case and data model
Start by writing one sentence: “When X happens in Bitbucket, update Y in Airtable (and optionally notify Z).” Then create a mapping sheet before building anything.
- Choose your core Airtable table: Features, Bugs, Releases, or Sprint Items.
- Choose a stable unique key: an Airtable Record ID, plus a Bitbucket PR URL or Issue Key field.
- Define ownership: which system “owns” each field (Airtable owns priority; Bitbucket owns merge status, etc.).
Create triggers in Airtable
If your integration starts in Airtable, pick a trigger that reflects real workflow commitment (e.g., “Ready for Dev”) rather than early drafts.
- Good triggers: status changes, checkbox “Approved,” record enters a view, due date reached.
- Stability tip: trigger on a dedicated “automation flag” field so edits to descriptive text don’t spam your pipeline.
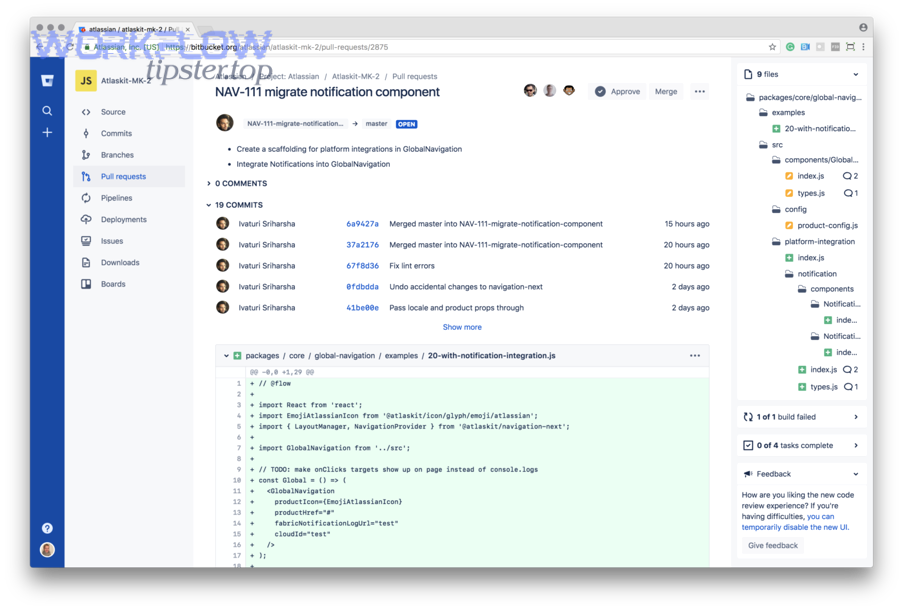
Configure Bitbucket actions
If your integration pushes into Bitbucket, keep actions minimal and deterministic so you don’t create accidental repo noise.
- Common actions: create a branch name from Airtable fields, create a PR checklist, post a comment to a PR, or update a linked issue tracker field.
- Naming conventions: use a predictable slug like feature/<airtableRecordId>-<shortTitle>.
Test and monitor
Testing should include success cases, duplicates, and failures—because webhooks and APIs are designed for delivery, not perfection.
- Use real events: open a PR, push a commit, merge with/without approvals, and verify Airtable updates.
- Test duplicates: resend the same webhook payload to ensure idempotency.
- Log outcomes: store integration run IDs in Airtable so you can audit what changed and why.
How should you map Airtable fields to Bitbucket issues, pull requests, and commits?
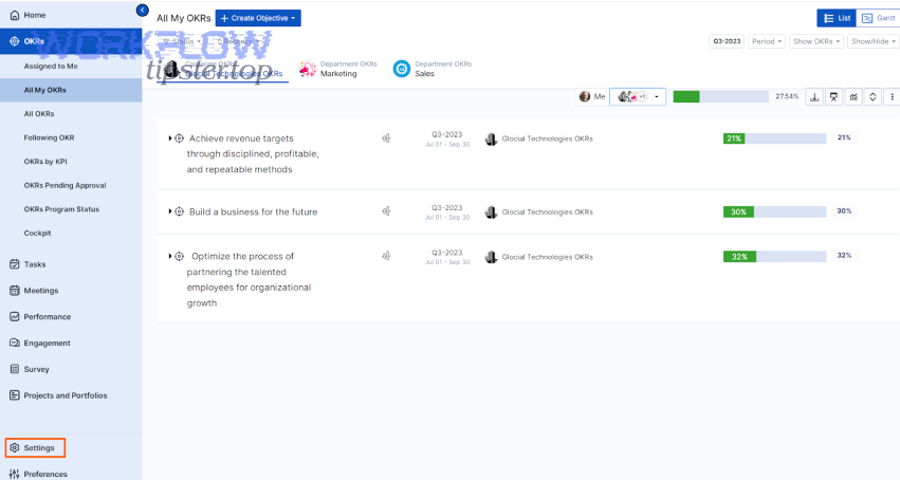
You should map Airtable fields to Bitbucket entities by using one primary linkage field (stable ID/URL) plus three functional groups—status, ownership, and delivery metadata—so anyone can trace work from “planned” to “shipped” without ambiguity.
Specifically, mapping becomes reliable when you separate “what humans decide” (priority, scope) from “what systems observe” (PR merged, build passed).
Field mapping for issues/requests
Even if you don’t use Bitbucket Issues, you can still treat “issue-like” items as a structured object in Airtable that references a repo and target branch.
- Airtable fields (recommended): Repo, Component, Priority, Target Release, Owner, Acceptance Criteria.
- Bitbucket linkage field: repository slug + branch name or PR URL.
- Rule: never “infer” repo identity from free text—use a controlled select field.
Status mapping and ownership
Status mapping works best when you define a small set of states and lock down which system is allowed to move each transition.
- Example state model: Planned → Ready → In Progress → In Review → Merged → Released.
- Ownership suggestion:
- Airtable moves Planned/Ready (product decision).
- Bitbucket events move In Review/Merged (engineering reality).
- Release tooling moves Released (deployment reality).
Linking records to repository entities
Linking becomes effortless when every PR title or branch name carries the Airtable record ID, and Airtable stores the canonical PR URL.
- Branch naming: feature/recXXXXXXXXXXXX
- PR title prefix: [Airtable: recXXXXXXXXXXXX]
- Airtable back-link: store PR URL, PR state, last commit hash, and merge timestamp.
Once your linking convention is stable, you can build views in Airtable that act like “engineering dashboards” without requiring everyone to live inside Bitbucket all day.
What webhooks and API components do you need for a reliable Airtable to Bitbucket connection?
You need three core components for reliability: Airtable webhook notifications, Bitbucket webhook events/payloads, and a processing layer that authenticates, retries, and applies idempotent updates.
More specifically, webhooks are the backbone because they push changes immediately, which is usually superior to polling if you care about timely status accuracy.
Airtable Webhooks API essentials
Airtable’s Webhooks API exists to notify you about changes in a base that you care about—like created records, updated fields, or records moving into/out of a view.
- Design tip: subscribe only to the tables/views you need to reduce noise.
- Schema tip: version your field mapping so field renames don’t silently break your logic.
- Operational tip: keep a “last processed cursor” so you can recover cleanly after downtime.
Bitbucket Cloud webhooks and payloads
Bitbucket Cloud webhooks let you configure events that trigger outgoing requests to your service whenever repository activity happens.
- Start with a small event set: PR created, PR merged, build status changes.
- Filter early: ignore events that don’t include your Airtable record ID convention.
- Normalize payloads: map all event types into a common internal schema before updating Airtable.
Authentication, retries, and idempotency
Your processing layer should assume duplicate and late deliveries, then protect Airtable from inconsistent writes.
- Authentication: verify webhook signatures or shared secrets where supported; never trust source IP alone.
- Retries: exponential backoff for transient failures (timeouts, 429s).
- Idempotency: store an event ID hash; if you’ve processed it, ignore repeats.
- Queueing: if you expect bursts (many commits), buffer events before updating Airtable.
What are the most common Airtable to Bitbucket integration errors and how do you fix them?
The most common Airtable to Bitbucket integration errors fall into four groups—delivery failures, rate limits, permission issues, and schema drift—and you fix them by adding verification, backoff, least-privilege tokens, and mapping version controls.
However, the key is to debug in the right order: confirm the event arrived, confirm you can parse it, confirm you can write to Airtable, and only then blame “the tool.”
Webhook delivery failures
Webhook failures usually happen because the receiving endpoint is down, slow, or rejecting payloads due to authentication errors.
- Fix: return a fast 2xx response and push heavy processing into a queue.
- Fix: log the raw payload and headers for replay.
- Fix: add a “webhook health” check that alerts when deliveries drop.
Rate limits and pagination
Rate limits show up when you update too many Airtable records per minute or you make repeated Bitbucket API reads during bursts.
- Fix: batch updates (group changes per record).
- Fix: cache repo metadata (default branch, workspace ID) instead of fetching repeatedly.
- Fix: degrade gracefully (update critical fields first, enrich later).
Permission and token issues
Permission errors happen when tokens expire, scopes are insufficient, or a workspace policy changes without updating your integration.
- Fix: use service accounts where possible and rotate secrets on a schedule.
- Fix: implement “permission tests” during deployment (a simple read + write validation).
- Fix: store error context in Airtable so non-engineers can report exact failures.
Data validation and schema drift
Schema drift happens when fields are renamed, data types change, or a “required” field becomes optional (or vice versa).
- Fix: enforce a mapping contract: field name + field ID + expected type.
- Fix: add a staging view in Airtable where changes are validated before promotion.
- Fix: write integration tests that run when Airtable schema changes.
Which approach is best: Airtable automations, third-party connectors, or custom code?
Airtable automations win for speed and simplicity, third-party connectors are best for configurable cross-tool workflows, and custom code is optimal when you need strict control over security, reliability, and complex transformations.
Meanwhile, the “best” choice is rarely permanent—many teams start with no-code, then move high-impact paths into custom code once requirements stabilize.
This table contains a practical comparison of the three approaches so you can match your constraints (speed, governance, reliability) to the right build path.
| Approach | Best for | Pros | Cons |
|---|---|---|---|
| Airtable Automations | Simple triggers and updates | Fast setup, low overhead, easy iteration | Limited branching logic, weaker observability at scale |
| Third-party connectors | Multi-step workflows across apps | Flexible recipes, faster than custom, good for ops teams | Connector limits, cost scaling, harder deep customization |
| Custom code | High reliability and governance | Full control, strong security patterns, scalable architecture | Build/maintain effort, needs engineering ownership |
When Airtable Automations wins
Airtable Automations wins when your workflow is mostly “record-based” and you only need a small number of deterministic actions, like setting a status field when a related event is confirmed.
- Use it when: you have a single base, a stable schema, and low event volume.
- Avoid it when: you need complex retries, event deduplication, or deep payload parsing.
When connectors win
Connectors win when multiple systems must participate and you want a visual builder with operational ownership outside engineering.
- Use it when: you need multi-step routing (notify, update, create, log) and quick changes.
- Avoid it when: strict compliance requires full control over runtime, logs, and data retention.
When custom code wins
Custom code wins when the integration is business-critical and failure has a measurable cost (bad release signals, missed compliance steps, incorrect reporting).
- Use it when: you need queues, replay, audit logs, and strong secret management.
- Avoid it when: your process is still changing weekly and you can’t afford maintenance.
Evidence supports that well-designed “assistance layers” can improve throughput in real work settings. According to a study by Stanford University from the Stanford Digital Economy Lab, in 2023, access to an AI assistance tool increased productivity in a customer-support setting by roughly 14% on average, demonstrating how structured assistance and automation can boost output when applied to repeatable workflows.
In other words, if your Airtable↔Bitbucket workflow is repeatable and rule-based, automation is a productivity lever—but you still need correctness, governance, and observability to keep it trustworthy long-term.
— Contextual Border —
How do you harden an Airtable to Bitbucket integration for security and compliance?
You harden an Airtable to Bitbucket integration by applying four controls—secret management, least privilege, data minimization, and incident-ready logging—so your automation is safe to operate under real governance constraints.
Besides reliability, security is what separates a “cool workflow” from a production-grade system that your organization can trust.
Secret management
Store API tokens and webhook secrets in a dedicated secrets manager, not inside Airtable fields or automation step notes.
- Rotation: rotate on a schedule and immediately on staff changes.
- Scoping: separate tokens by environment (dev/stage/prod) to reduce blast radius.
- Access: restrict read access to secrets to the runtime only, not all admins.
Least privilege and audit trails
Give the integration only the minimum permissions needed: update the specific base/table and read the specific repo/workspace events required.
- Principle: the integration should not have human-like “full admin” access.
- Audit trail: log who/what triggered changes and store a run ID on each updated Airtable record.
- Change control: treat mapping edits like code—review, approve, and document them.
PII and data residency
Minimize what you synchronize: store links and IDs instead of copying sensitive text, and avoid pushing personally identifiable information into repos or webhook logs.
- Data minimization: sync only what’s required to operate the workflow.
- Retention: define how long you keep payload logs and when you purge them.
- Residency: ensure your integration runtime location aligns with your organization’s policies.
Incident response checklist
Build a simple response plan so you can pause automation safely and recover without data corruption.
- Kill switch: one toggle that stops writes to Airtable during incidents.
- Replay plan: store events so you can replay from a known checkpoint.
- Rollback plan: keep “before values” for critical fields or maintain a change journal table.
- Verification: after recovery, reconcile a sample set of records against Bitbucket event history.
Because both Airtable and Bitbucket can drive workflows through webhooks, your security posture should assume inbound event traffic and enforce strict validation and logging at that boundary.

