If you’re seeing “Invalid JSON payload received” from a Google Chat incoming webhook, the fix is almost always the same: send valid JSON that also matches Google Chat’s accepted message schema (starting with a minimal {"text":"..."} body) and then expand safely from there. ([developers.google.com](https://developers.google.com/workspace/chat/quickstart/webhooks?))
Next, you’ll learn how to tell whether the failure is caused by malformed JSON syntax (quotes, commas, invisible control characters) or by schema mismatch (unsupported keys that trigger “Unknown name … Cannot find field”). ([support.atlassian.com](https://support.atlassian.com/jira/kb/fix-400-errors-with-json-payloads-in-google-chat-webhooks-via-jira-cloud/?))
Then, you’ll get a repeatable debugging workflow using curl, Postman, and automation logs, plus a practical approach to transforming third-party alert payloads (Jira/Prometheus-style) into a Google Chat message payload that succeeds. ([developers.google.com](https://developers.google.com/workspace/chat/quickstart/webhooks?))
Introduce a new idea: once your core webhook request is stable, you can prevent “it worked yesterday” regressions by adding validation, controlling escaping, and recognizing nearby errors like rate limits and other non-JSON failures before they look like a payload problem. ([developers.google.com](https://developers.google.com/workspace/chat/quickstart/webhooks?))
What does “Google Chat Invalid JSON payload” mean, and what triggers webhook 400?
Google Chat “Invalid JSON payload” is a webhook/API response that means your request body is either not valid JSON or valid JSON that doesn’t match the message schema, so Chat rejects it with an HTTP 400. ([developers.google.com](https://developers.google.com/workspace/chat/quickstart/webhooks?))
To better understand the issue, start by separating two failure families: syntax failures (the JSON parser cannot read the body) versus schema failures (the JSON is readable, but the fields are not allowed in a Chat message). This single distinction prevents hours of “guess-and-post” debugging.
In practice, Google Chat webhooks are strict about what they accept. Incoming webhook examples and Google’s workflow guidance consistently treat the message as a structured object and show a simple, predictable pattern for valid requests. ([developers.google.com](https://developers.google.com/workspace/chat/quickstart/webhooks?))
What is the difference between “malformed JSON” and “unsupported fields” in Google Chat payloads?
Malformed JSON is a syntax problem where the payload can’t be parsed (for example, an unescaped newline or a missing quote), while unsupported fields means the JSON parses fine but includes keys Chat doesn’t recognize (often shown as “Unknown name … Cannot find field”). ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
Specifically, malformed JSON errors are triggered by characters and structure:
- Unescaped double quotes inside strings
- Trailing commas in objects/arrays
- Mismatched braces/brackets
- Hidden control characters (like Windows
\r) inside a JSON string
Unsupported-field errors are triggered by the shape of the payload:
- Fields copied from other chat platforms (for example, Slack-like keys such as
usernameorattachments) - Tool-native alert payload keys that don’t belong in a Chat message (for example,
alert,source, or callback fields) - Wrong nesting (placing keys under the wrong object or level)
The fastest diagnostic is to read the exact error string: “Closing quote expected” points to syntax; “Unknown name … Cannot find field” points to schema mismatch. ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
Does Google Chat accept any generic webhook JSON format by default?
No—Google Chat does not accept arbitrary “generic webhook JSON”; it requires a message payload that matches Chat’s supported request format, and unknown fields will be rejected. ([developers.google.com](https://developers.google.com/workspace/chat/quickstart/webhooks?))
More importantly, this is why “copy my alert JSON and paste it into the webhook” fails so often: generic webhook templates tend to send large, nested objects with keys that make sense for the tool that produced them, not for Google Chat’s message contract.
Thus, the correct mindset is: transform into a Chat message, don’t “forward the payload.” This is the core of effective google chat troubleshooting when you’re integrating external systems into Chat notifications.
![]()
What are the most common causes of Invalid JSON payload in Google Chat webhooks?
There are two main groups of causes of Google Chat invalid JSON payload errors: (1) JSON syntax breaks and (2) schema mismatch fields, and most fixes come from identifying which group you’re in before changing anything else. ([support.atlassian.com](https://support.atlassian.com/jira/kb/fix-400-errors-with-json-payloads-in-google-chat-webhooks-via-jira-cloud/?))
Then, you can make progress quickly by matching your symptom to a small set of high-probability root causes instead of rewriting the whole payload.
Which malformed JSON mistakes break payload syntax most often?
There are seven common malformed JSON mistakes that repeatedly break Google Chat webhook payloads: unescaped quotes, stray CR characters, raw newlines, trailing commas, mismatched braces, invalid escaping, and mixed quoting rules in shell scripts. ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
Specifically, these are the failures developers hit most:
- Unescaped quote inside a JSON string: Your message text contains
"and you didn’t escape it. - Windows line endings / hidden control characters: A string includes
\r(carriage return) and JSON rejects it as a control character. - Raw newline inside a JSON string: You built the payload with multiline text but didn’t encode newlines correctly.
- Trailing comma: Common when you hand-edit JSON or use templating.
- Mismatched braces/brackets: Often caused by partial string concatenation.
- Incorrect escaping in curl/bash: Shell quoting ends early and injects unexpected characters.
- Wrong Content-Type or body encoding assumptions: Rarely the sole cause, but it makes debugging harder because the server interprets differently.
When you see errors like “Closing quote expected,” treat it as a sign that the payload never became valid JSON in the first place. ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
According to a study by Rochester Institute of Technology from the Department of Computer Science, in 2021, researchers analyzed 47,610 JSON files and reported that approximately 7.07% of collected JSON Schemas were invalid due to invalid syntax, showing that syntax-level mistakes remain a measurable, recurring class of failure. ([cs.rit.edu](https://cs.rit.edu/~dataunitylab/uploads/publications/Alsulami2021.pdf))
Which “schema mismatch” mistakes cause “Unknown name … Cannot find field”?
There are three common schema-mismatch patterns that cause “Unknown name … Cannot find field”: sending tool-native alert fields, sending Slack-like message fields, and nesting fields under the wrong object level for Google Chat. ([support.atlassian.com](https://support.atlassian.com/jira/kb/fix-400-errors-with-json-payloads-in-google-chat-webhooks-via-jira-cloud/?))
More specifically, schema mismatch happens when:
- You forward a whole alert payload: Fields like
alert,source,receiver,alerts, or callback URLs appear where Chat expects a message. ([support.atlassian.com](https://support.atlassian.com/jira/kb/fix-400-errors-with-json-payloads-in-google-chat-webhooks-via-jira-cloud/?)) - You reuse a Slack template: Keys such as
usernameorattachmentsare rejected because they aren’t recognized in the Chat message payload. ([github.com](https://github.com/pydantic/logfire/issues/1540?)) - You guess the structure: You place a field under
messageor another wrapper incorrectly and Chat flags it as unknown.
The “Unknown name …” detail is actually good news: it tells you exactly which key to remove or remap first.

How do you fix the payload fast using a minimal “known-good” Google Chat webhook body?
You can fix Google Chat invalid JSON payload issues fastest by using a 4-step method: start with a minimal known-good payload, confirm a clean 200 response, add fields one at a time, and stop at the first failing change to identify the exact breaking character or field. ([developers.google.com](https://developers.google.com/workspace/chat/quickstart/webhooks?))
Below, this approach turns a frustrating “random 400” into a controlled experiment where every change has a visible effect.
Is a minimal { "text": "..." } payload the best baseline for debugging?
Yes—a minimal {"text":"..."} payload is the best baseline because it isolates the core contract, removes unsupported fields, and makes it easy to prove your webhook URL and network path are correct before you add complexity. ([docs.cloud.google.com](https://docs.cloud.google.com/workflows/docs/notify-google-chat?))
Specifically, the baseline gives you three major benefits:
- Fast validation: You confirm the webhook is reachable and accepts your request shape.
- Clean diffing: Every failure after the baseline is caused by what you changed, not by the environment.
- Portable reproduction: You can replay the same request from curl, Postman, CI, or a no-code tool.
Once the baseline works, your real job is to preserve JSON validity while expanding the message—either with safe formatting in text or with structured message elements (like cards) only after the simplest message succeeds.
What step-by-step checklist should you follow before re-testing the webhook?
There are nine checklist steps you should follow before re-testing: verify the endpoint, ensure POST, validate JSON, normalize line endings, set headers, remove unknown keys, keep the body small, re-test with the baseline, and only then reintroduce automation fields gradually. ([developers.google.com](https://developers.google.com/workspace/chat/quickstart/webhooks?))
To illustrate, use this checklist every time you edit a payload:
- 1) Confirm the webhook URL is correct: Don’t test with a truncated or copied-wrong token.
- 2) Use HTTP POST: Webhooks expect a POST body, not query-parameter JSON.
- 3) Validate JSON: Use a JSON validator or parse it locally before sending.
- 4) Remove hidden control characters: Normalize Windows CRLF when the message comes from files. ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
- 5) Set
Content-Type: application/json; charset=UTF-8: Make intent explicit. - 6) Strip unknown keys: Remove anything that is not a Chat message field. ([support.atlassian.com](https://support.atlassian.com/jira/kb/fix-400-errors-with-json-payloads-in-google-chat-webhooks-via-jira-cloud/?))
- 7) Keep payload small: Long nested objects increase risk of schema mismatch and truncation.
- 8) Re-test with
{"text":"hello"}: Ensure baseline success. - 9) Add one change at a time: Stop at first failure and keep the smallest failing diff.
How do you debug Invalid JSON payload using curl vs Postman vs your automation tool logs?
curl wins for reproducible raw requests, Postman is best for quick iteration and visual inspection, and automation logs are essential when the payload is being templated or transformed—so the best debugging is often to start in Postman and then lock the final request in curl. ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
Meanwhile, the key to stopping repeat failures is to always capture the exact raw body that reached Google Chat—because what you “intended” to send is not always what the tool actually sent.
Why does the same payload “work in Postman” but fail in curl/bash?
Postman often succeeds where curl/bash fails because Postman sends the exact JSON you typed, while shells can rewrite quotes, expand variables, and inject control characters when you build JSON with string concatenation or mismatched quoting. ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
For example, curl calls often fail due to:
- Single-quote vs double-quote confusion: The shell ends the string early and splits JSON into arguments.
- Variable expansion surprises: A variable containing quotes or newlines breaks JSON structure.
- CRLF in file-loaded content: A copied Windows line ending introduces
\rin the string. ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
On the other hand, Postman can hide the escaping complexity—so once it works, export the exact body and headers and replicate them in curl to ensure your production environment behaves the same way.
What should you log to pinpoint the exact breaking character or field?
There are six things you should log to pinpoint the failure: the raw request body, the raw response body, headers, status code, a payload hash/version, and the “smallest failing diff” between the last good payload and the first bad payload. ([community.fabric.microsoft.com](https://community.fabric.microsoft.com/t5/Data-Pipeline/Notification-from-Webhook-activity-to-Google-Chat/td-p/4312570?))
More specifically, good logs include:
- Raw body as bytes/text: Not a pretty-printed object—capture what was sent over the wire.
- Response JSON: Keep the full “Unknown name …” details when present. ([community.fabric.microsoft.com](https://community.fabric.microsoft.com/t5/Data-Pipeline/Notification-from-Webhook-activity-to-Google-Chat/td-p/4312570?))
- Headers: Especially Content-Type, and any proxy-added headers.
- Request ID / timestamp: So you can correlate retries and tool runs.
- Template version: Which automation template produced this payload.
- Minimal reproduction: A copy/paste curl command that fails reliably.
This is also where people confuse unrelated issues with JSON: a workflow might have a different bug like google chat pagination missing records, but your logs will show that “missing records” is not the same category as an HTTP 400 payload rejection.
This table contains a quick interpretation guide that helps you map the error message pattern to the most likely root cause and the first fix to try.
| Error pattern | Likely cause | First fix to try |
|---|---|---|
| Invalid JSON payload received. Closing quote expected… | Malformed JSON (escaping / control chars) | Validate JSON; remove CRLF; escape quotes/newlines |
| Invalid JSON payload received. Unknown name “X” at ‘message’: Cannot find field. | Schema mismatch (unsupported field) | Remove/remap field X into supported message structure |
| 401 / 403 Unauthorized / Forbidden | Auth / policy issue (not JSON validity) | Check webhook configuration and access rules |
| 429 Too Many Requests | Rate limiting | Backoff, queue, reduce message frequency |
How do you correct payloads coming from third-party systems (Jira/Alertmanager/Looker/HubSpot) to Google Chat?
There are three effective ways to correct third-party payloads for Google Chat: flatten to text, template a small summary object, or transform into a structured card message, and the best choice depends on how much reliability you need versus how rich the message must be. ([support.atlassian.com](https://support.atlassian.com/jira/kb/fix-400-errors-with-json-payloads-in-google-chat-webhooks-via-jira-cloud/?))
In addition, the most important principle is to stop forwarding tool-native JSON. Instead, treat the tool output as input data and render a Chat message from it.
What fields should you keep vs remove when converting a generic alert payload to Google Chat?
There are four groups of fields you should keep—title, severity, key metrics, and action links—and you should remove everything else that is tool-specific or deeply nested, because those fields commonly trigger “Unknown name … Cannot find field” in Google Chat. ([support.atlassian.com](https://support.atlassian.com/jira/kb/fix-400-errors-with-json-payloads-in-google-chat-webhooks-via-jira-cloud/?))
To begin, keep only what a human needs to act:
- Keep: short title, severity/priority, what changed, affected service, and a direct link to investigate.
- Keep: 3–8 key-value facts (host, environment, incident ID, time).
- Remove: raw arrays of alerts, nested metadata trees, receiver/group label structures, callback URLs, and internal IDs unless you render them into a simple text line.
- Remove: Slack-like decoration fields and any keys not documented for Chat messages. ([github.com](https://github.com/pydantic/logfire/issues/1540?))
This is why some automation setups report google chat field mapping failed: the mapping step often tries to “map everything,” creating a payload full of keys Chat doesn’t accept. Your mapping should be intentionally small.
Should you send plain text or a structured card message for alerts?
Plain text wins for speed and reliability, while structured cards are best for readable, action-oriented alerts once your baseline payload is stable and you can maintain a stricter schema over time. ([developers.google.com](https://developers.google.com/workspace/chat/api/reference/rest/v1/cards?))
However, choose based on these criteria:
- Choose plain text when: you need the fewest moving parts, you’re under time pressure, or your alerts must always deliver.
- Choose cards when: you need consistent formatting, multiple sections, buttons, or richer layouts for on-call workflows. ([developers.google.com](https://developers.google.com/workspace/chat/api/reference/rest/v1/cards?))
A practical strategy is to start with text, prove stability, then add a card version later as an enhancement. This also makes it easier to notice unrelated issues like google chat api limit exceeded, because you’ve reduced payload complexity and can clearly attribute failures to rate limits instead of message formatting. ([developers.google.com](https://developers.google.com/workspace/chat/quickstart/webhooks?))

Is the error always your JSON, or can Google Chat/Network issues cause it too?
No—the “Invalid JSON payload” message is not always “just your JSON,” because proxies, middleware, truncation, and upstream tools can mutate the body in transit, and nearby failures (rate limits, auth, policies) can look similar until you check the status code and response details. ([community.fabric.microsoft.com](https://community.fabric.microsoft.com/t5/Data-Pipeline/Notification-from-Webhook-activity-to-Google-Chat/td-p/4312570?))
More importantly, this is why debugging must include the raw request body that actually reached Google Chat. If a proxy rewrites your JSON, the fix belongs in the gateway or automation configuration—not in the message template alone.
In short, treat the payload as “guilty until proven innocent,” but also treat the network path as “capable of changing evidence.” That mindset is how developers prevent repeat incidents on production automations—especially when multiple tools are chained together, including content libraries such as WorkflowTipster.top.
How do you differentiate Invalid JSON payload (400) from 401/403/429/5xx problems?
Invalid JSON payload is a 400 client-format failure, 401/403 indicate access/auth policy failures, 429 is rate limiting, and 5xx indicates server-side or upstream instability—so the correct fix is determined first by status code, then by the detailed message text. ([developers.google.com](https://developers.google.com/workspace/chat/quickstart/webhooks?))
To illustrate, follow this order:
- Step 1: Read the status code (400 vs 401/403 vs 429 vs 5xx).
- Step 2: If 400, read whether the message mentions parsing (“closing quote”) or schema (“unknown name”). ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
- Step 3: If 429, implement backoff/queueing; do not rewrite JSON first.
- Step 4: If 401/403, check webhook permissions/settings and organizational controls.
- Step 5: If 5xx, retry with jitter and confirm service health before making payload changes.
Contextual Border: Now that you can reliably fix the core webhook 400 “Invalid JSON payload” issue using minimal payloads, strict field control, and reproducible debugging, the next section covers advanced edge cases and related problems that appear in real integrations.
Advanced edge cases: What rare issues still cause Google Chat payload failures even when your JSON looks correct?
There are four rare-but-real classes of failures that can break Google Chat webhook delivery even when your JSON looks correct: encoding/characters, payload truncation, error-type confusion, and proxy/WAF mutation, and each requires a different validation step. ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
Especially in production pipelines, “looks correct” is not enough; you need to confirm the exact bytes that reached the webhook endpoint.
What encoding and character issues (emoji, smart quotes, non-UTF-8) can corrupt payloads?
There are five encoding issues that commonly corrupt “correct-looking” JSON: smart quotes, non-UTF-8 text, invisible control characters, mixed normalization forms, and copy/paste artifacts from rich editors. ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
Specifically, protect your payload by:
- Replacing smart quotes (“ ”) with standard JSON quotes (“) in templates.
- Ensuring your pipeline uses UTF-8 end-to-end (including logs and template storage).
- Stripping control characters from variables before templating.
- Converting CRLF to LF when loading message text from files. ([stackoverflow.com](https://stackoverflow.com/questions/68762312/google-chat-invalid-json-payload-received-closing-quote-expected-in-string-n?))
- Testing with a minimal ASCII message to isolate encoding from schema issues.
What payload size, truncation, or line-break issues happen in CI/CD and webhook relays?
There are four common truncation/line-break issues in CI/CD and webhook relays: log-driven truncation, template field length limits, multiline environment variables, and relay services that rewrite whitespace—each of which can cut off a closing brace and instantly turn valid JSON into malformed JSON. ([community.fabric.microsoft.com](https://community.fabric.microsoft.com/t5/Data-Pipeline/Notification-from-Webhook-activity-to-Google-Chat/td-p/4312570?))
More specifically, prevent truncation by:
- Keeping messages concise and linking to details instead of embedding full payloads.
- Limiting nested structures when using templates in no-code tools.
- Encoding multiline content explicitly (or converting to single-line summaries).
- Storing the “final rendered payload” as an artifact for debugging.
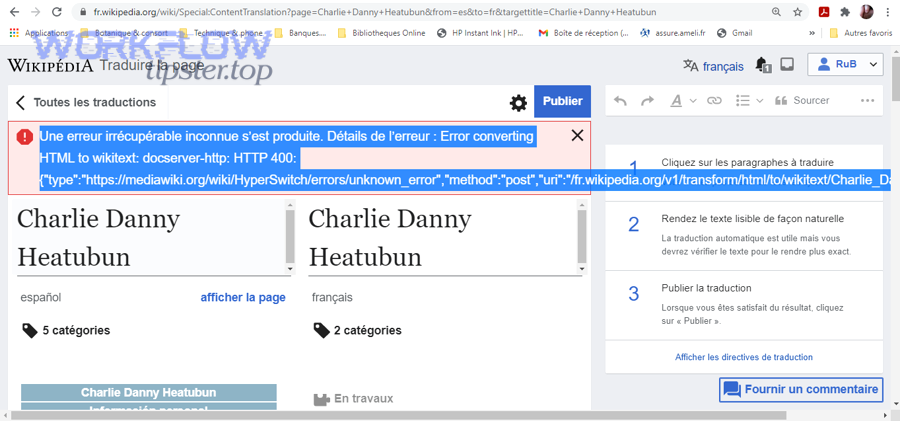
How does Google Chat “Invalid JSON payload” differ from “Invalid argument” or “Unknown name” errors?
Invalid JSON payload points to parsing or message-format rejection, while Unknown name is a schema mismatch that identifies the exact unsupported field—and both are typically categorized as INVALID_ARGUMENT in the structured response, so you should fix fields first when a field name is given. ([community.fabric.microsoft.com](https://community.fabric.microsoft.com/t5/Data-Pipeline/Notification-from-Webhook-activity-to-Google-Chat/td-p/4312570?))
However, the practical difference is your first action:
- If parsing-style: validate JSON and eliminate control characters/escaping issues.
- If unknown-field-style: delete or remap the named field, then retry with the smallest possible payload. ([support.atlassian.com](https://support.atlassian.com/jira/kb/fix-400-errors-with-json-payloads-in-google-chat-webhooks-via-jira-cloud/?))
What security/proxy/WAF behaviors can rewrite your JSON and how do you confirm it?
There are three proxy/WAF behaviors that can rewrite JSON: request normalization, body inspection/redaction, and header-driven transformations—and you confirm them by comparing the payload before the proxy, after the proxy, and at the final destination using an identical request ID. ([community.fabric.microsoft.com](https://community.fabric.microsoft.com/t5/Data-Pipeline/Notification-from-Webhook-activity-to-Google-Chat/td-p/4312570?))
To begin, confirm mutation with a clean experiment:
- Send directly to the webhook from a controlled machine and record the exact body.
- Send through the full pipeline and capture the raw body from logs at each hop.
- Diff the two bodies to identify rewriting (missing braces, changed quotes, stripped characters).
Once you know where the JSON changes, you can fix the correct layer—template, relay, or gateway—without endlessly adjusting the message content itself.

